Old electronics are not scrap. They are retired business assets that still carry data, regulatory exposure, and brand risk long after users stop touching them.
Most companies do not get into trouble because they meant to mishandle ewaste. They get into trouble because old laptops sit in closets, drives stay in storage cages, and a well-meaning facilities cleanup turns into an undocumented disposal event. That is where a routine refresh becomes a legal and operational problem.
The Growing Mountain of Corporate Ewaste
In 2022, the world generated a record 62 million metric tons of e-waste, an 82% increase from 2010. This waste stream is growing 2-3 times faster than the global population, but only 22.3% was formally collected and recycled, leaving millions of tons of data and hazardous materials improperly managed, according to global ewaste reporting summarized here.

For an IT director, that number matters for a different reason than it does for a sustainability team. A decommissioned server is not just waste. A laptop pulled from service is not just surplus. Each asset can contain customer data, employee records, credentials, network configurations, licensed software, and internal documents.
Why businesses misread the problem
Many organizations still classify ewaste as a facilities issue. That is too narrow.
Exposure often spans several teams:
- IT owns the asset history
- Security owns the data risk
- Legal and compliance own defensibility
- Facilities often control the physical removal
- Procurement and finance care about residual value
If those groups do not work from one process, assets fall through gaps.
The practical reframing
A retired device moves through three states. It may be suitable for reuse, suitable for parts and commodity recovery, or suitable only for destruction. Each state requires documented handling.
Treat ewaste as a controlled business process, not a cleanup task.
That is also why the environmental side cannot be separated from governance. When devices leave your custody without inventory, sanitization records, and downstream accountability, you lose more than recoverable material. You lose proof. For teams building internal policy, Beyond Surplus has a useful background page on the environmental impact of electronic waste, but the bigger business lesson is custody. If you cannot show what left, how it was processed, and who handled it, you are relying on trust where documentation is required.
Navigating the Business Risks of Improper Ewaste Disposal
The fastest way to underestimate ewaste is to focus only on haul-away logistics. Significant losses happen after a device leaves a desk and before anyone can prove what happened to it.
Data risk sits inside the hardware
An old endpoint can still hold active risk. Hard drives, SSDs, mobile devices, copiers, and network gear often retain information long after the user account is disabled.
That is why “we removed it from service” is not the same as “the data is gone.”
If your team cannot answer these questions, the process is weak:
- What media is inside the asset
- Whether wiping or physical destruction is required
- Who verified completion
- What record ties the serial number to the destruction event
For companies handling regulated data, the disposal process becomes inseparable from information security at this point. Secure workflows usually require documented sanitization or shredding, plus a defensible chain of custody. The operational baseline is straightforward: if a device held sensitive data, you need proof of what happened next. Teams reviewing options can compare controls against services for secure destruction of data.
Hidden barriers inside the company
The most disruptive ewaste problem is often internal behavior. Not policy. Not pickup access. Behavior.
Key barriers to enterprise e-waste compliance go beyond logistics. They include deep-seated fears over data privacy on old devices and internal hoarding behaviors. This often leads to clandestine disposal, creating contaminated sites and leaving companies exposed to liability, as noted in this discussion of enterprise barriers to e-waste recycling.
A few patterns show up repeatedly:
Device hoarding
Staff keep retired equipment “just in case.” IT keeps backup units with no formal review cycle. Departments store old phones and laptops because no one trusts that data will be destroyed properly.
Informal cleanouts
Office moves, warehouse resets, and data center projects create pressure to clear space fast. That is when undocumented pickups and mixed scrap loads appear.
Split ownership
Facilities arranges removal. IT assumes drives were handled. Compliance assumes both teams documented it. Nobody owns the complete record.
The risk is rarely one bad decision. It is usually several reasonable decisions made without one accountable process owner.
Brand and compliance exposure
A company name on a device in the wrong place creates a preventable public problem. So does an internal audit that finds missing equipment with no destruction records.
Improper ewaste disposal can trigger questions your team should never have to answer under pressure:
| Risk area | What goes wrong |
|---|---|
| Data security | Storage media leaves the organization without verified sanitization |
| Compliance | Required records do not exist, are incomplete, or cannot be matched to specific assets |
| Reputation | Branded equipment appears in landfills, informal channels, or unapproved resale streams |
The fix is not complicated. Make disposal formal, serial-based, documented, and auditable.
Decoding Ewaste Categories for Corporate IT
Corporate ewaste is not one stream. It is several streams with different handling rules, value profiles, and risks.
A facilities vendor that treats everything as mixed scrap will miss those differences. Consequently, companies lose resale value, mishandle hazardous components, or apply the wrong data destruction method to the wrong asset class.
User devices and office IT
This is the largest category most businesses see day to day. Laptops, desktops, monitors, docks, tablets, phones, printers, and small network devices move through refresh cycles constantly.
These assets look simple, but they are not low risk. User devices often contain the most direct concentration of business data because they were used by employees every day.
Focus on three decisions:
- Reuse or retire
- Wipe or shred
- Resell, donate, or recycle
If the asset is still functional, refurbishment may be a better path than immediate material recovery. If it is damaged or too old for controlled reuse, move it into the recycling stream with media handled separately where needed.
Data center and infrastructure equipment
Servers, blades, storage arrays, switches, UPS units, rack PDUs, and telecom hardware require a different playbook. The issue is not just data. It is logistics, weight, access controls, de-install sequencing, and chain of custody during removal.
A rushed server room cleanout usually creates avoidable mistakes. Rails, drives, loose media, and staged pallets get separated. Asset records stop matching what shipped.
For data center gear, inventory discipline matters as much as destruction discipline.
Specialized and regulated equipment
Healthcare, labs, manufacturing, and field operations all generate electronic waste that should never be treated like general office surplus.
Examples include:
- Medical electronics that may contain patient-related data or specialized components
- Lab equipment with embedded storage, proprietary software, or contamination concerns
- Industrial devices that include batteries, boards, sensors, and mixed materials
- Print and imaging equipment with internal drives and memory
In this category, classification needs to connect with environmental handling rules. Many business assets also intersect with broader waste categories involving batteries, lamps, and other controlled materials. For teams mapping asset classes to proper handling, this overview of the universal waste definition helps separate standard IT recycling from regulated waste streams that need additional controls.
A simple internal sorting model
Use this at intake:
- Data-bearing assets
- High-value reusable assets
- Hazardous or regulated components
- Low-value mixed electronics
- Equipment needing special de-installation
That classification works better than broad labels like “computer recycling” because it maps directly to action.
The Secure IT Asset Disposition ITAD Process Explained
A sound ITAD process is observable. You can watch it happen, inspect the records, and tie every result back to a specific asset list.
If a vendor cannot explain the chain of custody from pickup through final documentation, you do not have a process. You have a promise.
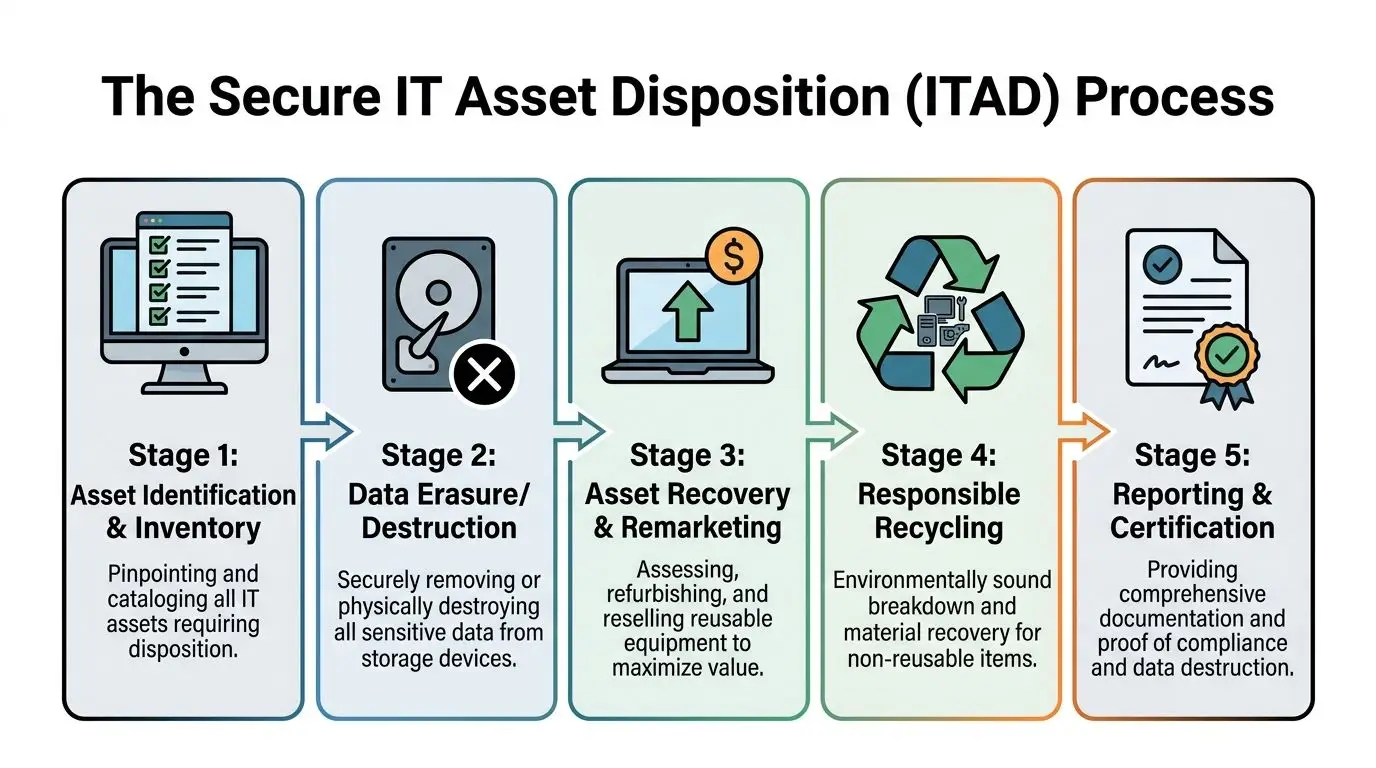
A certified ITAD process involves multiple stages: sorting to segregate hazardous items like batteries, shredding equipment into small pieces, and using advanced mechanical separation such as magnets, eddy currents, and infrared to liberate materials for recovery, all while providing chain-of-custody documentation like Certificates of Destruction, as described in this overview of the e-waste recycling process.
Intake and inventory control
The process starts before anything leaves the building. Assets should be identified, counted, and tied to a pickup scope. For higher-control projects, that includes serial capture or at least a documented equipment manifest by class and quantity.
What works:
- Pre-pickup review with IT and facilities
- Separation of data-bearing from non-data-bearing equipment
- Controlled staging area
- Named handoff points
What does not work:
- Mixed loading from multiple departments
- Last-minute additions with no record
- Loose drives in open bins
- Pickup tickets that only say “electronics”
Data destruction choices
Not every asset needs the same destruction method. The decision depends on the media type, asset condition, reuse intent, and your internal policy.
When wiping fits
Certified data wiping makes sense when the asset is suitable for remarketing or redeployment and the media can be sanitized to policy.
When shredding fits
Physical destruction is often the cleaner answer for failed drives, damaged devices, heavily regulated environments, or any case where resale is off the table and proof matters more than recovery.
A mature program does not argue ideology. It chooses the method that fits the asset and the risk.
The wrong question is “Do we wipe or shred everything?” The right question is “Which method is defensible for this asset class?”
Value recovery and reuse
A proper ITAD workflow tries to preserve value before it destroys it. Functional business hardware can often be tested, graded, and remarketed if policy permits and data has been handled correctly.
That matters because disposal cost is only one side of the equation. The other side is whether the organization captures residual value from newer assets instead of treating everything as scrap.
Recycling and downstream processing
For equipment that cannot be reused, the next step is responsible breakdown and material recovery. Hazardous components should be removed early. Then mechanical separation and downstream metallurgical processes handle the recovery stream. Vendor quality becomes visible at this stage. Serious operators can explain how materials move after shredding, which streams go to approved downstream processors, and what records support that path.
Reporting and final documentation
The process is not finished when the truck leaves or when the shredder runs. It is finished when your compliance team has records it can use.
At minimum, expect documentation that addresses:
- Pickup details
- Asset scope
- Data destruction outcome
- Recycling outcome
- Chain of custody
If you are comparing providers, start with their explanation of what is IT asset disposition and then press for operational specifics. Ask to see sample reporting. Ask how exceptions are handled. Ask what happens when serial counts do not match.
Such questions often reveal the weaknesses of vendors.
How to Choose a Certified Ewaste and ITAD Partner
Most mistakes in vendor selection happen because buyers evaluate on convenience first and controls second. That order should be reversed.
A pickup truck and a weight ticket do not make an ITAD partner. You are selecting a custodian for retired assets that may still contain sensitive data and recoverable value.

With global e-waste recycling rates failing to keep pace with generation, with a projected rate of only 20% by 2030, choosing an ITAD partner with certifications like R2 or e-Stewards is critical to ensure your assets are recycled and not illegally exported or landfilled, which transfers liability away from your organization, according to the Global E-waste Monitor reference cited here.
Non-negotiables to verify
Start with process evidence, not marketing language.
Certifications and scope
R2 and e-Stewards matter because they signal structured environmental and operational controls. Still, the certificate alone is not enough. Verify the scope and ask what locations and activities it covers.
Data handling methods
Ask how the provider handles wiping, shredding, failed media, mobile devices, and embedded storage. Good vendors answer clearly. Weak ones stay generic.
Chain of custody
You want to hear who takes possession, how shipments are secured, how loads are documented, and how exceptions are reported.
Questions worth asking in the first call
- Who handles downstream materials after your facility?
- How do you document data destruction?
- Can you support de-installation, packing, and logistics for multi-site projects?
- What happens to reusable equipment?
- What proof do you provide when the project closes?
Signals that should slow you down
Some red flags appear early:
| Warning sign | Why it matters |
|---|---|
| Vague answers about downstream vendors | You may be buying blind on final disposition |
| No sample certificate or report | Documentation may be weak or inconsistent |
| Only commodity language | Scrap handling is not the same as controlled ITAD |
| No discussion of data-bearing assets | They may not understand your main risk |
If a vendor cannot explain its controls in plain language, your legal team will not be able to defend them later.
A practical review process helps. This vendor due diligence checklist is a useful framework for separating actual ITAD capability from basic hauling.
Beyond Surplus Ewaste Solutions for Your Business
The right operating model combines secure pickup, data destruction, reuse screening, recycling, and final reporting under one chain of custody. Many businesses do not fail because they lack intent. They fail because they split those tasks across too many vendors.

Advanced ITAD providers use advanced techniques like hydrometallurgy and pyrometallurgy to recover high-purity metals from shredded e-waste. This commitment to technology ensures maximum value recovery and environmental compliance, supported by certificates that transfer liability under regulations like the FTC Disposal Rule, as outlined in these global e-waste statistics and processing notes.
For business users, the practical takeaway is simple. Your provider should support the whole disposition decision tree, not just the recycling leg.
What an enterprise-ready solution looks like
A workable service model usually includes:
- Pickup coordination for offices, warehouses, and technical sites
- On-site or off-site data destruction based on policy and asset type
- IT buyback and remarketing where equipment still has market value
- Recycling with documentation for non-reusable hardware
- Project support for relocations, closures, and decommissions
Beyond Surplus is one example of that model. The company handles business electronics recycling, secure data destruction, IT buyback, and nationwide pickup coordination for organizations that need one documented workflow rather than separate service providers.
Where value recovery fits
Not every retired device belongs in a shred stream. Some assets should be refurbished or remarketed after approved data sanitization. That is especially relevant for phones and mobile fleets, where timing and condition heavily affect returns. If your team is evaluating secondary market options, this guide on how to maximize your used phone value is a useful companion to an ITAD review because it shows how resale outcomes depend on condition, preparation, and timing.
The most expensive disposal decision is destroying assets that should have been remarketed, or remarketing assets that should have been destroyed.
The discipline is in deciding correctly, asset by asset.
Building Your Company's Ewaste Management Policy
A defensible ewaste policy does not need to be complicated. It needs to be specific, enforced, and owned.
Too many companies rely on tribal knowledge. Someone in IT knows who to call. Someone in facilities knows where old monitors go. Someone in security assumes drives are shredded. That is not policy. That is dependency on memory.
The policy components that matter
Write the document so an auditor, project manager, or new IT lead could follow it without verbal context.
Include these elements:
Asset scope
Define what equipment falls under the policy. Cover endpoints, servers, storage, phones, peripherals, network gear, printers, and embedded media.Disposition paths
State when assets are reused, remarketed, donated, recycled, or destroyed.Data sanitization standard
Identify which asset classes require wiping, which require shredding, and who approves exceptions.Chain of custody rules
Require documented handoffs, controlled staging, and approved transportation methods.Vendor approval
Specify how providers are vetted, what certifications or documentation are required, and who signs off.
Operational controls that keep the policy alive
Policy without routine controls becomes shelfware.
Build in:
- Quarterly cleanouts for hoarded equipment
- Simple intake forms for every pickup or internal transfer
- Serial-based tracking where risk justifies it
- Employee instructions for where retired devices go and where they do not go
- Closure reports for major refreshes, relocations, and decommissions
A useful ownership model
The cleanest structure is shared execution with single accountability.
| Function | Core responsibility |
|---|---|
| IT | Asset identification and technical review |
| Security or compliance | Data handling requirements and audit standards |
| Facilities | Access, staging, and site logistics |
| Procurement or finance | Value recovery and disposition approval |
Assign one accountable owner for the final record. Without that, gaps survive because every team assumes another team has the evidence.
Good ewaste policy removes improvisation from office cleanouts, hardware refreshes, and data center shutdowns.
The result is not just cleaner recycling. It is lower risk, better documentation, and more disciplined recovery of value from retired technology.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. If your organization needs pickup coordination, data destruction, IT buyback, or documented ewaste handling for offices, medical environments, labs, or data centers, start with a review of your current process and close the gaps before the next refresh cycle.