For healthcare organizations and medical facilities across Georgia, disposing of outdated IT equipment is not just an operational task—it's a critical compliance mandate governed by federal law. HIPAA regulations extend beyond your digital network; they apply to every single device that has ever stored or transmitted electronic Protected Health Information (ePHI), from the moment it's decommissioned to its final destruction. A single misstep in this process can result in substantial fines, severe reputational damage, and an irreparable loss of patient trust.
The High Stakes of E-Waste Management in Georgia's Healthcare Sector
When a computer, server, medical device, or even an office multifunction printer in a Georgia healthcare facility reaches its end-of-life, it cannot be discarded like ordinary office equipment. These assets are often repositories of sensitive ePHI, containing everything from patient records and billing information to diagnostic images and laboratory results. Improper disposal is a direct violation of federal law and carries significant penalties. This is a critical concern for Georgia's healthcare sector, a major economic driver that relies on secure IT asset disposal to protect patient data amid rapid technological turnover.

The HIPAA Security Rule (45 CFR §164.312) is explicit: covered entities and their business associates must implement and document policies for the final disposition of electronic devices and media. Fines for non-compliance are severe, with penalties frequently ranging from $10,000 to $50,000 per violation, and can escalate into multi-million-dollar settlements as evidenced by numerous enforcement actions by the Department of Health and Human Services (HHS).
Understanding the Regulatory Landscape
Adhering to HIPAA regulations for e-waste is a non-negotiable component of broader Data Security Best Practices. The law requires that ePHI be rendered "unusable, unreadable, or indecipherable to unauthorized individuals." Simply deleting files or reformatting a hard drive is insufficient and fails to meet this standard. The responsibility lies squarely with the healthcare organization to ensure a secure, unbroken chain of custody from the moment a device is taken offline until its data is verifiably destroyed.
Engaging a certified IT asset disposal vendor is the only effective way to manage these risks.
HIPAA E-Waste Disposal Risks vs. Certified Solutions
| Compliance Risk | Consequence of Improper Disposal | Certified Vendor Solution (e.g., Beyond Surplus) |
|---|---|---|
| Data Breach | Exposure of patient ePHI, leading to identity theft, fraud, and loss of institutional trust. | Guarantees data destruction using NIST-compliant methods, including physical shredding and certified data erasure. |
| HIPAA Violations | Fines from $10,000 to $50,000+ per violation, with the potential for million-dollar settlements. | Provides a signed Business Associate Agreement (BAA), contractually accepting direct liability for ePHI protection. |
| Lack of Audit Trail | Inability to demonstrate compliance during an HHS audit, resulting in automatic penalties. | Delivers auditable documentation, including Certificates of Destruction, serialized reports, and chain-of-custody logs. |
| Reputational Damage | Negative media coverage, loss of patient confidence, and long-term damage to the organization's brand. | Ensures a secure, transparent, and legally compliant process that safeguards your professional reputation. |
| Environmental Fines | Improperly dumping e-waste can violate state and federal environmental laws, leading to fines. | Adheres to R2v3 and other environmental certifications for responsible and legal electronics recycling. |
Partnering with a certified electronics recycling vendor who specializes in these requirements is the only way to effectively mitigate risk. A qualified commercial partner will:
- Execute a Business Associate Agreement (BAA): This legally binding contract makes the vendor equally liable for protecting your ePHI.
- Provide an Auditable Paper Trail: This includes Certificates of Data Destruction and Recycling, serialized asset reports, and complete chain-of-custody logs.
- Utilize Compliant Destruction Methods: Their processes must align with federal standards, such as those published by the National Institute of Standards and Technology (NIST).
This guide provides Georgia-based businesses with the essential information for secure, compliant electronics recycling, helping turn a regulatory obligation into a streamlined component of your data security strategy.
What HIPAA Mandates for Electronics Disposal
When disposing of electronics containing patient data—officially termed ePHI—the rules are strict. HIPAA’s Security Rule, specifically section §164.310(d)(2)(i), requires that you render this data completely unusable, unreadable, and indecipherable.
For an old server in your data center or decommissioned laptops, this is the cornerstone of HIPAA compliant electronics recycling in Georgia. The data must be permanently eliminated, with no possibility of recovery. The Department of Health and Human Services (HHS) defers to the National Institute of Standards and Technology (NIST) for defining the appropriate methods to achieve this.
The Three Methods of Data Sanitization
NIST Special Publication 800-88 outlines a clear framework with three methods for data sanitization. Understanding these is the first step toward developing a compliant disposal plan for your Georgia-based healthcare facility.
Consider the disposal of a sensitive paper document:
Clearing: This is analogous to using software or hardware to overwrite existing data. It is effective against simple recovery attempts but may not withstand advanced forensic analysis.
Purging: This is a more robust method, like using a cross-cut shredder. Techniques like degaussing (for magnetic media) or advanced cryptographic erasure make data recovery practically impossible, even with specialized laboratory equipment.
Destroying: This is the most definitive option—akin to incineration. The physical media is shredded, pulverized, or melted, ensuring there is nothing left to recover data from.
For any healthcare organization committed to compliance, purging and destroying are the only acceptable options for media containing ePHI. For a deeper dive, review our frequently asked questions about HIPAA-compliant IT equipment disposal.
Data Security Is Only Half the Equation
While protecting patient data is paramount under HIPAA, environmental compliance cannot be overlooked. The same electronic devices contain hazardous materials such as lead, mercury, and cadmium. If landfilled, these substances can cause significant environmental harm.
A comprehensive IT asset disposal strategy must integrate stringent data security with environmental stewardship. Neglecting either aspect not only risks non-compliance with environmental regulations but also undermines a healthcare provider's commitment to public health and corporate social responsibility.
This dual focus is essential. Beyond HIPAA, healthcare organizations must adhere to principles of safe and responsible hazardous waste disposal. A certified recycling partner ensures that after data is verifiably destroyed, the remaining materials are processed responsibly in accordance with state and federal laws, with a zero-landfill policy.
When selecting a vendor, confirm they provide both a Certificate of Data Destruction and a Certificate of Recycling. These documents create a complete, defensible audit trail, proving you have fulfilled your duties to protect patient data and meet environmental obligations. This holistic approach defines a true partner in HIPAA compliant electronics recycling in Georgia.
Choosing Your Method for Certified Data Destruction
Understanding the need to make ePHI unrecoverable is the first step; mastering the how is what ensures compliance. For healthcare data in Georgia, using proven, certified methods for data destruction is non-negotiable. The sole objective is permanent, irreversible data elimination.
The industry gold standards are three primary approaches. The appropriate choice depends on your organization's security protocols, the media type, and whether the retired equipment has potential for remarketing.
Data Wiping to NIST 800-88 Standards
Data wiping (also known as clearing or overwriting) involves using specialized software to write patterns of random data over the entire drive, effectively sanitizing the original information and making it forensically unrecoverable.
The crucial element is ensuring the process meets the NIST 800-88 "Purge" standard. This is the benchmark that guarantees data cannot be reconstructed. It is the ideal solution for newer, functional hard drives intended for resale, as it preserves the hardware's value while securing the data.
Degaussing for Magnetic Media
For traditional magnetic storage like hard disk drives (HDDs) and legacy backup tapes, degaussing is a powerful and efficient solution. A degausser generates a powerful magnetic field that instantly randomizes the magnetic domains on a drive's platters, where data is stored.
The data is permanently erased in seconds, and the drive itself is rendered inoperable. Degaussing is reserved for end-of-life media destined for physical recycling. If you are interested in the technology, you can learn more about how a degausser works.
Physical Shredding: The Ultimate Destruction
For absolute, verifiable proof of destruction, nothing surpasses physical shredding. Industrial-grade shredders tear through hard drives, solid-state drives (SSDs), and other storage media, reducing them to small, unrecoverable fragments of metal and plastic.
Physical shredding is the most visually verifiable and definitive method of data destruction. It provides absolute certainty that the data can never be reconstructed, making it the preferred choice for healthcare facilities with the most stringent security requirements.
It is also the only guaranteed method for destroying data on SSDs and other flash-based media, which are not susceptible to magnetic degaussing.
To assist in your decision, here is a comparison of these methods:
Comparison of Data Destruction Methods for HIPAA Compliance
This table outlines the primary methods for electronic data destruction, detailing their processes, compliance standards, and ideal use cases within a commercial healthcare environment.
| Destruction Method | Description & Process | Compliance Standard Met | Best Use Case |
|---|---|---|---|
| Software Wiping (NIST 800-88 Purge) | Uses specialized software to overwrite existing data with random characters across the entire drive, making original data unrecoverable. | NIST 800-88 "Purge" | Functional hard drives (HDDs & SSDs) intended for reuse or resale. |
| Degaussing | Exposes magnetic media (HDDs, tapes) to a powerful magnetic field, instantly scrambling and erasing the stored data. The drive is rendered inoperable. | NIST 800-88 "Purge" | End-of-life magnetic hard drives (HDDs) and backup tapes not suitable for reuse. |
| Physical Shredding | An industrial shredder grinds the storage device into small, unrecognizable fragments, making data reconstruction physically impossible. | NIST 800-88 "Destroy" | All media types, especially damaged drives, SSDs, and for maximum, verifiable security. |
On-Site vs. Off-Site Destruction: A Key Logistical Choice
After selecting a destruction method, you must decide where it will occur.
- On-Site Destruction: A mobile shredding truck or degaussing unit is brought to your Georgia facility, allowing your team to witness the entire process. This provides an unbroken chain of custody and immediate verification, making it the preferred choice for hospitals and clinics managing highly sensitive ePHI.
- Off-Site Destruction: Your equipment is securely transported in a locked, GPS-tracked vehicle to our certified facility. The process is documented with detailed chain-of-custody logs, offering an efficient and compliant solution for routine IT asset disposals.
Both options, when executed by a certified vendor like Beyond Surplus, are fully HIPAA compliant. Since Georgia lacks state-mandated e-waste laws, healthcare providers must proactively partner with certified experts. Improperly disposing of a single server or laptop can lead to a data breach, with HIPAA fines reaching up to $1.5 million per violation category.
Beyond Surplus provides NIST 800-88 certified data wiping and on-site hard drive shredding, complete with Certificates of Data Destruction and Recycling. This documentation creates a defensible audit trail, proving you have met the media disposal requirements of HIPAA Security Rule §164.310(d)(2)(i).
Building Your Unbreakable Audit Trail
In the context of HIPAA, an undocumented action is considered an action that never occurred. This principle is especially critical for electronics disposal. The final and most crucial step in HIPAA compliant electronics recycling in Georgia is creating a complete, defensible audit trail.
This documentation serves as your proof of compliance. It is the evidence you will need to present to government regulators in the event of an audit. A certified recycling partner provides the essential documents that demonstrate you have adhered to all applicable regulations. This paper trail is your legal defense, showing a transparent and secure process from start to finish.
The Core Components of a Defensible Audit Trail
A complete audit trail is a collection of documents that tells the full story of an asset's journey from your Georgia facility to its secure end-of-life. Each document serves a specific purpose in proving due diligence.
The key documents you must obtain from your vendor include:
- Signed Business Associate Agreement (BAA): This is the legal foundation of your partnership. It must be executed before any ePHI leaves your control, legally binding your vendor to the same HIPAA standards you follow.
- Serialized Asset Tracking Reports: A detailed inventory list that includes the make, model, and serial number of every device being processed, ensuring full accountability.
- Secure Chain-of-Custody Logs: This document tracks the asset at every touchpoint—from pickup at your location, during secure transit, and upon arrival at the processing facility.
These initial documents establish a secure and accountable handover. The final documents certify that the data destruction and recycling were completed according to regulations.
Certificates: The Final Proof of Compliance
The two most critical documents you will receive are the certificates that formally close the loop on your compliance obligations. These are non-negotiable and serve as definitive proof that the service was completed correctly.
A Certificate of Data Destruction is the cornerstone of your audit trail. This document formally attests that all data on specified assets has been permanently destroyed using a compliant method, such as physical shredding or NIST 800-88 certified wiping. You can see what this entails in our detailed explanation of a Certificate of Destruction.
Simultaneously, a Certificate of Recycling confirms that the physical hardware was processed in an environmentally responsible manner, in accordance with all federal and state regulations. This proves you have met your environmental duties alongside your data security obligations.
This image illustrates the core data destruction methods that support a compliant audit trail.
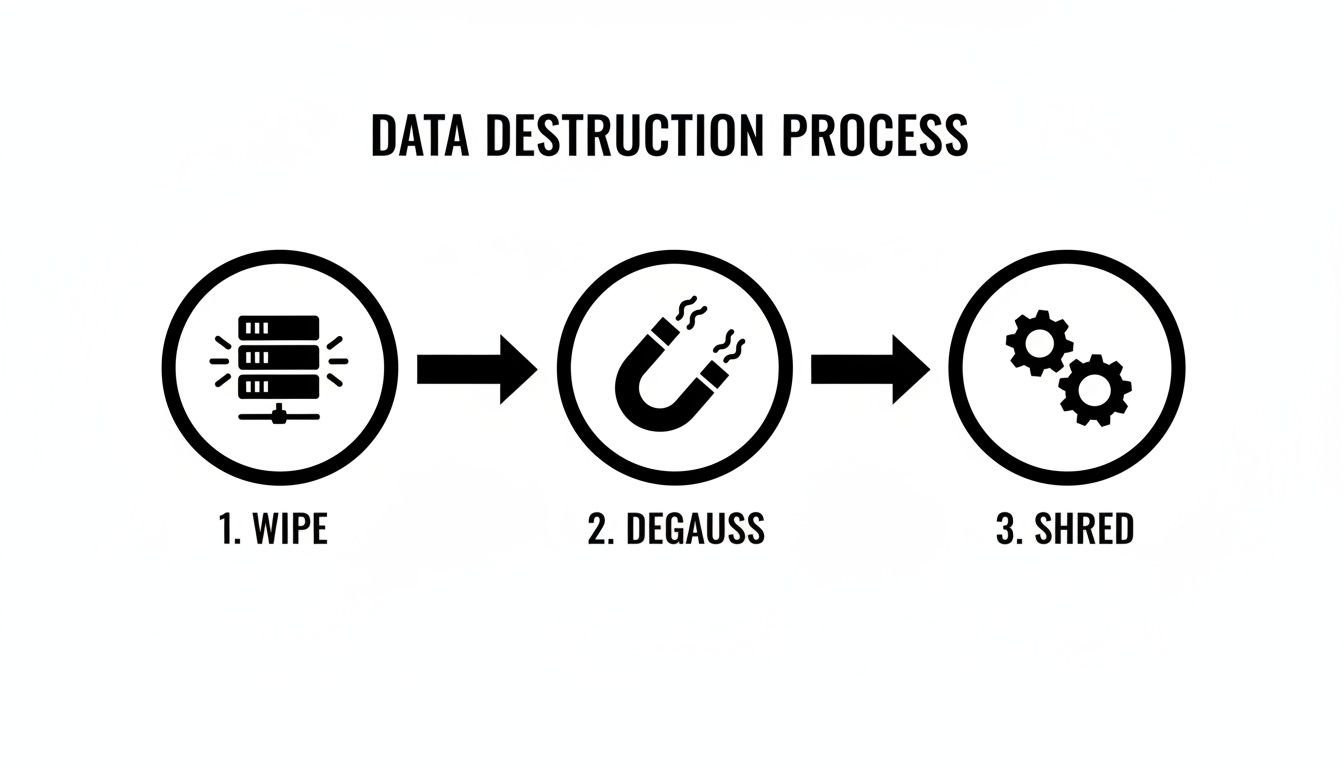
It highlights the progression from software-based erasure to the finality of physical shredding—each a valid and critical step in a secure disposal workflow.
In an audit, documentation is everything. A complete file containing a BAA, chain-of-custody logs, serialized reports, and final certificates for both data destruction and recycling creates a powerful, defensible record that leaves no room for doubt about your organization's commitment to HIPAA compliance.
By demanding this level of thorough documentation, you are not merely checking a box. You are actively transferring liability and building a robust defense that protects your organization, its reputation, and the sensitive patient data you are entrusted to secure.
How to Select Your ITAD Partner in Georgia
Choosing the right IT Asset Disposition (ITAD) partner in Georgia is a critical decision that directly impacts your organization's security, compliance, and reputation. For commercial healthcare entities, your partner is a Business Associate entrusted with your most sensitive data.
This requires due diligence beyond a simple web search. You need a partner who can substantiate their compliance claims with certifications, transparent processes, and comprehensive documentation. This vetting process is your first line of defense against a data breach or a costly HIPAA violation.

Core Vendor Qualifications
Before discussing services, verify these foundational credentials. These non-negotiable qualifications separate professional ITAD providers from scrap haulers.
Your initial screening should focus on three critical areas:
- Industry Certifications: Insist on active R2v3 or e-Stewards certifications. These are the leading standards in the electronics recycling industry, guaranteeing adherence to stringent environmental, health, safety, and data security protocols.
- HIPAA Compliance Readiness: The vendor must be willing and able to execute a Business Associate Agreement (BAA). This contract legally obligates them to protect your ePHI and holds them directly liable for breaches.
- Data Destruction Standards: Verify their data destruction methods align with NIST 800-88 guidelines. Whether using certified wiping, degaussing, or physical shredding, the outcome must be forensically unrecoverable data.
Your Practical Vendor Evaluation Checklist
Once a vendor meets these prerequisites, delve into their operational procedures. The answers to these questions will reveal their true commitment to security and professionalism, helping you select the best partner for HIPAA compliant electronics recycling in Georgia.
Data Security and Process Verification
- Chain of Custody: How do you document and secure our assets from our facility to final processing? Request a sample of their chain-of-custody logs.
- Facility Security: What security measures are in place at your facility? Look for controlled access, 24/7 video surveillance, and employee background checks.
- On-Site Services: Do you offer on-site hard drive shredding? If so, can our staff witness the process?
- Downstream Auditing: How do you vet and audit your downstream partners? This is a key requirement of R2 and e-Stewards certifications.
Documentation and Reporting
- Certificate of Destruction: Request a sample Certificate of Data Destruction. It should list serial numbers and the specific destruction method used for each asset.
- Serialized Reporting: Do you provide a detailed inventory report listing every asset processed by serial number?
- Reporting Timelines: What is the turnaround time for receiving all final documentation for our audit trail?
Logistics and Capabilities
- Secure Transportation: Do you use your own vehicles or a third party? Are the vehicles locked and GPS-tracked?
- Insurance Coverage: What are your liability insurance limits, particularly for data breach incidents? Request a certificate of insurance.
- Asset Value Recovery: Do you offer programs for IT asset value recovery or remarketing for our newer, functional equipment?
Choosing an ITAD vendor is fundamentally a risk management decision. Your goal is to find a partner whose security procedures are just as strong—if not stronger—than your own. When ePHI is on the line, a transparent, certified, and meticulously documented process is the only standard that matters.
By using this structured approach, your healthcare organization can make an informed, defensible choice. Partnering with a company like Beyond Surplus means selecting a vendor fully equipped to deliver the security, documentation, and peace of mind that HIPAA compliance demands. Explore our complete range of ITAD services in Georgia.
More Than Compliance: Turning ITAD into a Strategic Advantage
For healthcare organizations in Georgia, meeting HIPAA standards in electronics disposal is the baseline, not the ultimate goal. A strategic IT Asset Disposition (ITAD) program does more than prevent fines—it strengthens the bottom line and aligns with broader corporate objectives.
Partnering with a premier ITAD provider transforms a regulatory burden into a value-generating activity. It becomes an opportunity to enhance your brand, meet environmental goals, and improve financial performance.
Weave ITAD into Your Corporate ESG Goals
Responsible electronics recycling is a direct and measurable way to advance your organization’s Environmental, Social, and Governance (ESG) targets. Every server, laptop, and medical device you responsibly recycle is a tangible contribution to your sustainability initiatives.
When you partner with a certified expert for HIPAA compliant electronics recycling in Georgia, you ensure:
- Environmental Stewardship: Hazardous materials like lead and mercury are kept out of local landfills, protecting Georgia's environment.
- Resource Conservation: Valuable commodities—including copper, aluminum, and precious metals—are recovered and returned to the supply chain.
- Reduced Carbon Footprint: Recycling electronics consumes significantly less energy than mining and processing virgin materials.
This entire process is documented, providing verifiable data for your annual ESG and corporate social responsibility reports. It is a clear demonstration that your commitment to public health extends to environmental protection.
Uncover Hidden Revenue in Retired IT Equipment
Do not assume retired IT assets are worthless. Many devices, particularly those only a few years old, retain significant residual value. A strategic ITAD partner can help you access this hidden revenue through a structured IT buyback program.
It is a common misconception that all end-of-life electronics are a disposal liability. In fact, a significant portion of a retired IT inventory can be securely refurbished and resold, converting a potential cost into a new revenue stream for your facility.
The process includes:
- Asset Evaluation: Your ITAD partner assesses your retired equipment to identify items with resale potential.
- Secure Data Destruction: Every device undergoes a certified, NIST 800-88 compliant data sanitization process to ensure complete ePHI removal.
- Remarketing: The vendor leverages its global sales channels to resell the refurbished equipment, sharing the proceeds with your organization.
This transforms retired technology from a liability into a financial asset. The revenue generated can help offset the cost of new equipment or be reinvested into other operational areas, all while maintaining absolute data security.
Common Questions About HIPAA E-Waste Recycling
Navigating the requirements of HIPAA-compliant electronics disposal can raise numerous questions for healthcare organizations in Georgia. To provide clarity, here are answers to the most frequently asked questions, helping you build your e-waste program with confidence.
What Documentation Should I Expect From a Vendor in Georgia?
When you transfer retired IT assets, you are also transferring significant legal responsibility. A reputable recycling partner must provide a complete audit trail to prove they have handled your data in a compliant manner.
This documentation package should include:
- A signed Business Associate Agreement (BAA) executed before any devices containing ePHI are handled.
- Detailed chain-of-custody records tracking each asset from your location to final disposition.
- A Certificate of Data Destruction specifying the method of destruction (e.g., physical shredding, a NIST 800-88 compliant wipe).
- A Certificate of Recycling confirming that all materials were processed in an environmentally responsible manner.
At Beyond Surplus, providing this complete documentation is a standard part of our service to ensure our commercial clients are always protected and audit-ready.
Does HIPAA Require On-Site Hard Drive Shredding?
This is a frequent point of inquiry. While the HIPAA Security Rule mandates that ePHI be rendered unreadable and indecipherable, it does not prescribe on-site shredding as the only compliant method.
However, on-site shredding is considered a best practice because it offers the highest level of security and transparency. It allows your staff to witness the physical destruction of media before it leaves your facility, eliminating any potential chain-of-custody risks. To provide maximum flexibility, Beyond Surplus offers both on-site and secure off-site shredding services across Georgia to align with your organization's specific security policies.
Under the HIPAA Omnibus Rule, Business Associates are directly liable for their own non-compliance and any breaches they cause. A properly executed Business Associate Agreement (BAA) legally obligates the vendor to safeguard your ePHI, transferring significant risk away from your organization.
What Happens If a Business Associate Causes a Data Breach?
This is precisely why vendor selection is so critical. If a data breach occurs due to your vendor’s negligence, the liability, including fines, notification costs, and reputational damage, falls directly on them as the Business Associate.
This is why partnering with an insured, certified, and BAA-ready vendor like Beyond Surplus is a foundational component of your HIPAA compliant electronics recycling Georgia strategy. It is about risk transference and ensuring full accountability.
For a partner that provides certified security and a complete, auditable trail for your healthcare facility's IT assets, contact Beyond Surplus today. Visit our website to schedule a pickup or learn more about our secure HIPAA compliant electronics recycling services.