For any business in Georgia, managing technology from procurement to retirement is more than an IT chore—it's a core component of your business strategy. A solid plan for IT lifecycle management in Georgia is not an expense; it’s a strategic imperative for staying competitive in the state's dynamic tech landscape. This guide provides a framework for maximizing the value of every technology dollar while protecting your enterprise from significant financial and reputational risks.
Why IT Lifecycle Management Is a Strategic Advantage in Georgia
In Georgia's thriving tech, finance, and healthcare sectors, every piece of hardware—from servers and laptops to specialized medical devices—represents both a critical investment and a potential liability. IT Lifecycle Management (ITLM) is the comprehensive process of managing this technology through its entire journey, ensuring every stage is optimized for value, security, and compliance.
Viewing this process as merely "getting rid of old computers" is a critical error that can have substantial financial repercussions. An effective ITLM strategy directly impacts your bottom line and strengthens your security posture. It provides your Georgia business with a clear roadmap for planning technology refreshes, controlling costs, and mitigating the risks associated with data breaches and environmental non-compliance. For a deeper dive into building a full strategy, explore our guide to IT asset lifecycle management.
The Four Core Phases of ITLM
A robust ITLM plan is not a one-time project but a continuous, cyclical process. Each phase presents an opportunity to enhance efficiency and reduce risk. This diagram illustrates how the process works, walking through the four key stages of an asset's life.
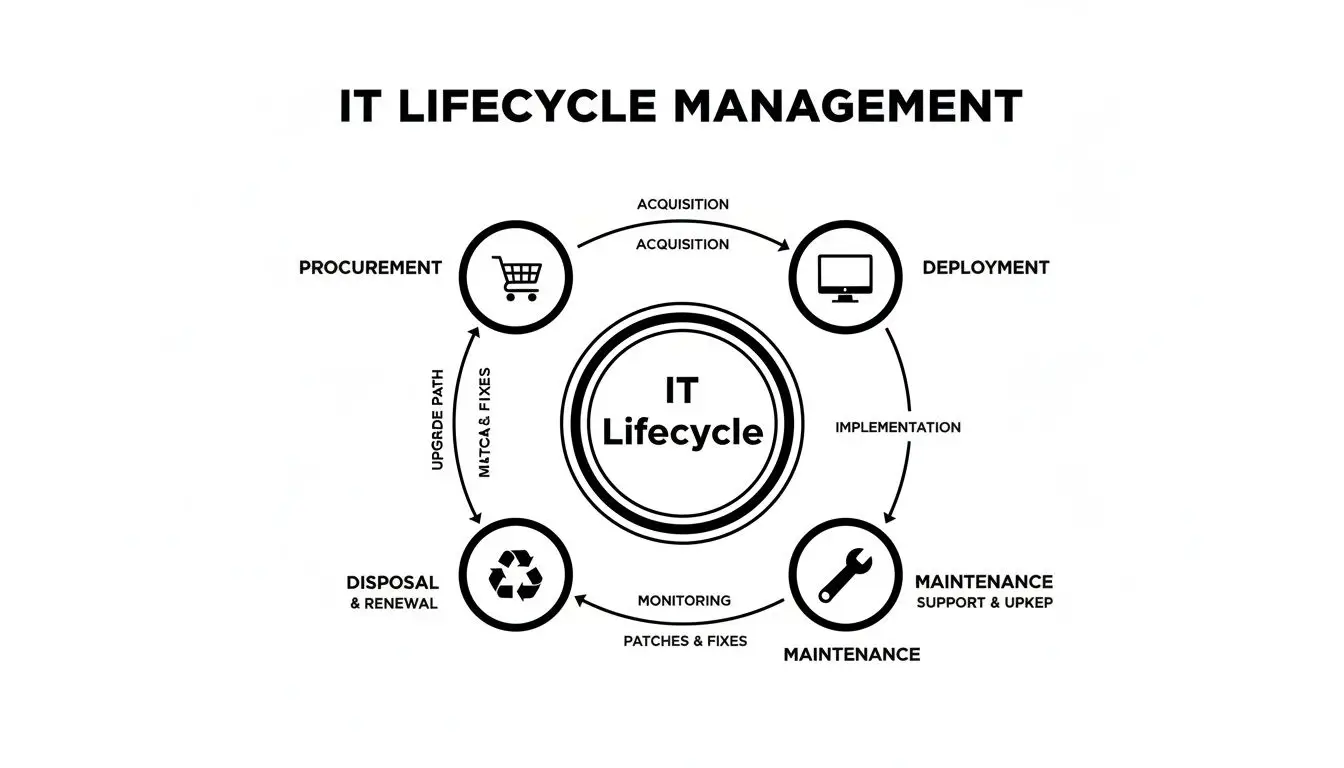
This visual breaks the process into four distinct, manageable stages. It highlights how a structured approach ensures nothing is overlooked, from the moment a device is procured to the day it is retired. This cycle is self-funding, as capital recovered from disposed assets can be reinvested into new technology.
The following table outlines the activities and primary goals for businesses at each stage.
The Four Stages of IT Asset Lifecycle Management
| Lifecycle Stage | Key Activities | Primary Goal for Georgia Businesses |
|---|---|---|
| Procurement | Acquiring new technology based on business needs, total cost of ownership (TCO), and future requirements. | Acquire optimal tools at the best value, avoiding overspending and ensuring long-term compatibility. |
| Deployment | Configuring new assets, installing software, integrating into the network, and onboarding users. | Achieve secure and rapid productivity from new hardware with minimal operational disruption. |
| Maintenance | Performing ongoing support, software updates, and hardware repairs to ensure optimal asset performance. | Maximize the operational lifespan of hardware, reduce downtime, and defer capital replacement costs. |
| Disposal | Securely decommissioning assets, performing certified data destruction, and responsibly recycling or remarketing them. | Protect sensitive corporate data, recover residual financial value, and ensure full compliance with all disposal regulations. |
Mastering these four phases transforms technology from a mere operational expense into a strategic asset. A well-executed ITLM program ensures you extract maximum value from hardware investments while neutralizing risks before they can materialize.
Protecting Your Business with Secure Data Destruction
When corporate IT hardware reaches its end-of-life, its journey is far from complete. For businesses in Georgia, the most critical and high-risk phase begins: ensuring every bit of sensitive data is verifiably and permanently destroyed.
From Atlanta to Augusta, this is not a suggestion—it is a legal and financial imperative, particularly for enterprises in heavily regulated industries like healthcare, finance, and government.
Simple "delete" commands or factory resets are dangerously insufficient. This is analogous to crumpling a confidential document; it can be smoothed out and read. Certified data destruction is the equivalent of feeding that document through a professional cross-cut shredder, turning it into indecipherable confetti.

Why Compliance Demands More Than Deletion
Federal and state laws mandate the protection of customer and patient data, even on retired equipment. The penalties for non-compliance are severe, in addition to reputational damage and loss of client trust.
HIPAA (Health Insurance Portability and Accountability Act): For healthcare organizations, HIPAA is non-negotiable. It requires Protected Health Information (PHI) to be rendered unreadable and impossible to reconstruct before a device leaves your control.
FTC Disposal Rule: This federal regulation applies to nearly every business, mandating "reasonable measures" to protect consumer information during disposal, making certified destruction a cornerstone of compliance.
State-Level Data Privacy Laws: Georgia businesses must also navigate state regulations governing the handling of Personally Identifiable Information (PII).
These regulations require a deliberate, documented process that proves legal obligations have been met. This is where professional data destruction is essential. Secure data destruction is foundational to effective IT lifecycle management, as retired assets are often overlooked vulnerabilities. According to a recent industry report, the average cost of a data breach has reached new highs, making the sanitization of end-of-life assets a critical security control. You can explore market trends in this detailed industry report from marketsandmarkets.com.
Choosing Your Method: NIST Wiping vs. Physical Shredding
To meet these strict standards, Georgia businesses have two primary, highly effective options for data sanitization. The appropriate choice depends on media type, age, and internal security policies.
NIST 800-88 Compliant Data Wiping: A software-based method using specialized programs to overwrite an entire hard drive with random data in multiple passes, making the original data forensically unrecoverable. This is ideal for newer, functional drives intended for resale to recover value.
On-Site or Off-Site Physical Shredding: For older, non-functional, or highly sensitive drives, physical destruction is the definitive solution. Mobile shredding trucks can be dispatched to your facility, allowing you to witness the destruction firsthand as drives are ground into unsalvageable metal fragments.
Your Ultimate Proof of Compliance: The Certificate of Data Destruction
Following data sanitization, your ITAD partner must provide a serialized Certificate of Data Destruction. This legal document serves as your official record, listing the serial numbers of every destroyed drive. It is your ultimate proof of due diligence and transfers liability, protecting your business from future claims.
Properly managing this final stage is non-negotiable for any organization serious about IT lifecycle management in Georgia. Partnering with a certified expert provides assurance that your data is irretrievably destroyed and your company is protected. Review your options with our complete overview of certified data destruction services in Georgia.
Handling the Logistics of Your IT Asset Disposition
Decommissioning and removing end-of-life IT equipment from an office or data center presents significant logistical challenges that most businesses are ill-equipped to handle. For companies across Georgia, this final stage of IT lifecycle management is fraught with hidden operational risks.
A do-it-yourself (DIY) approach, while seemingly cost-effective, is laden with peril. Tasking IT staff with hauling heavy servers, racks, and pallets of old desktops creates a risk of workplace injuries. Furthermore, any equipment in transit without a secure chain of custody exposes your company to data theft and severe compliance violations. A single misplaced hard drive can become a catastrophic liability.
The Pitfalls of a DIY Approach
Handling IT asset disposition internally may appear to save money, but the potential costs can escalate rapidly. This approach places the entire burden on internal teams who lack the specialized training and equipment for these high-risk tasks.
Common problems include:
- Employee Injury: IT professionals are not logistics experts. Moving heavy, awkward equipment without proper training or tools can lead to serious injuries and workers' compensation claims.
- Data Exposure: Transporting assets without a secure, documented chain of custody creates a significant security vulnerability. A lost device containing sensitive data can have devastating consequences.
- Improper Documentation: Without formal asset tracking and a Certificate of Disposal, there is no legal proof of responsible handling, leaving you exposed during an audit.
- Resource Drain: The time of IT professionals is better spent on strategic initiatives that drive business value, not on packing boxes and coordinating freight.
Professional Logistics: The Secure Alternative
Engaging a professional ITAD vendor transforms a high-risk logistical challenge into a secure, managed operation. An experienced partner handles every detail from start to finish, guaranteeing safety, security, and compliance. Effective project management is critical for a smooth disposition, which is why experts who are Project Management Professional (PMP) certified excel at overseeing these complex projects.
A professional ITAD provider operates its own fleet of vehicles and employs trained, background-checked logistics personnel who are experts in handling sensitive electronics. This ensures your assets are securely packed, palletized, and transported under a strict, documented chain of custody from your facility to the processing center.
This professional approach delivers true peace of mind. Your IT team can focus on core responsibilities, while your organization is shielded by a fully documented, secure, and compliant disposal process. Georgia businesses seeking reliable removal services can learn more about our process by exploring our guide on professional IT equipment pickup in Georgia.
Turning Retired IT Assets into Revenue
End-of-life IT equipment occupying valuable storage space is not just clutter—it is a potential source of revenue. For businesses across Georgia, the final stage of IT lifecycle management presents a significant financial opportunity. An IT asset buyback program allows you to recover tangible cash value for used laptops, servers, and networking gear, converting depreciated hardware into fresh capital.
This process, also known as asset recovery or IT value recovery, is an integral component of a modern ITAD strategy. It helps unlock the residual value in your retired equipment, which can then be allocated toward your next technology refresh, transforming a cost center into a revenue generator.
How Is Asset Value Determined?
The value of a retired IT asset is calculated based on clear factors that reflect its current market worth. Understanding this calculation helps set realistic expectations for your return.
A professional ITAD partner will evaluate each piece of equipment based on these key criteria:
- Age and Model: Newer equipment from top-tier brands like Dell, HP, or Cisco consistently holds more value. Technology evolves rapidly, and devices older than 4-5 years typically have minimal to no resale value.
- Condition: Both functional and cosmetic condition are assessed. Assets that are fully operational, free from major cosmetic damage, and complete with all original components (e.g., RAM, power cords) command the highest prices.
- Current Market Demand: The value of used IT equipment fluctuates with market supply and demand. The demand for specific server models, laptops, or network switches can change quickly.
A general understanding of asset types and their potential value can be a helpful guide.
Potential Value Recovery by IT Asset Type
This breakdown illustrates how different IT asset types typically perform in the buyback market. These are general guidelines; a detailed audit will determine the final value.
| Asset Type | Average Age for Buyback | Value Potential (High/Medium/Low) | Key Value Factors |
|---|---|---|---|
| Laptops | 1-4 Years | High | CPU generation, RAM, storage (SSD vs. HDD), brand |
| Servers | 2-5 Years | High | Processor model, RAM capacity, storage config |
| Networking Gear | 2-6 Years | Medium | Brand (e.g., Cisco), port speed, model series |
| Desktops | 2-4 Years | Medium | All-in-Ones, small form factors, CPU, RAM |
| Smartphones/Tablets | 1-3 Years | Low | Model, cosmetic condition, carrier lock status |
Ultimately, newer, high-specification equipment in good condition from major brands will always yield the best return on investment.
Security First, Value Second
It is critical to understand that value recovery occurs only after security has been addressed. An asset possesses zero resale value until all data has been completely and verifiably destroyed. No reputable ITAD partner will ever attempt to sell a device before it has been professionally sanitized.
This security-first principle is non-negotiable. It guarantees that sensitive corporate data is protected long before an asset enters the secondary market. This underscores a key point: a secure ITAD process not only protects your Georgia business but also enables the financial return. You can learn more about our process in this overview of our asset recovery services in Georgia.
The global IT Asset Disposition (ITAD) market is expanding rapidly as more companies seek to recover value from their retired assets. In Georgia, partnering with local ITAD experts helps businesses manage security risks while supporting the circular economy. You can discover more insights about the ITAD market on gminsights.com.
From Liability to Liquidity: The Buyback Process
The process is straightforward. Once your assets are securely transported to a processing facility, all data is destroyed. Each item is then tested, graded, and evaluated for its fair market value. You receive a detailed report and payment for the total recovered value.
This approach to end-of-life management means you are not just disposing of hardware but actively managing it as a financial asset. It closes the lifecycle loop, providing a budget-friendly way to fund new technology while ensuring security and compliance from start to finish.
Meeting Your ESG Goals with Sustainable E-Waste Recycling
The disposition of end-of-life electronics is no longer an afterthought—it is a core element of corporate responsibility. For companies across Georgia, the disposal phase of IT lifecycle management is a powerful statement about your commitment to corporate citizenship and brand integrity.
This represents a choice between a linear path, where old equipment becomes a long-term environmental liability in a landfill, and a circular approach, where retired assets are treated as a source of valuable materials for new technology.

The Hidden Environmental Cost of E-Waste
Modern electronics contain a complex mixture of precious metals and hazardous materials. Improper disposal can lead to the leaching of toxic substances like lead, mercury, and cadmium into soil and groundwater, causing significant environmental damage and health risks.
- Lead: Found in older CRT monitors and solder, lead is a potent neurotoxin.
- Mercury: Used in flat-screen displays and some batteries, mercury can cause severe kidney and nervous system damage.
- Cadmium: Commonly used in semiconductors and rechargeable batteries, it is a known carcinogen.
The scale of the e-waste problem is immense. Globally, e-waste generation is projected to reach 82 million tons by 2030. In Georgia alone, the annual generation of electronic waste contributes significantly to this total, underscoring the need for responsible action. To better understand these trends, you can read a detailed analysis of ITAD security and sustainability on itadusa.com.
Aligning Disposal with Your Corporate Values
For Georgia businesses pursuing Environmental, Social, and Governance (ESG) or Corporate Social Responsibility (CSR) goals, the choice of an ITAD partner is critical. Vague promises are insufficient; you require a partner with policies that provide verifiable proof of responsible recycling.
Zero-Landfill and Zero-Export Policies: The Gold Standard
For any company serious about sustainability, choosing a certified e-waste recycler with strict zero-landfill and zero-export policies is non-negotiable. This guarantees your assets are never dumped in local landfills or exported to developing nations, where they can contribute to unsafe labor practices and environmental degradation.
Working with a certified recycler ensures every component is managed correctly. Valuable commodities like gold, silver, copper, and aluminum are extracted and reintroduced into the manufacturing supply chain. Plastics are sorted for processing, and all hazardous materials are safely isolated and disposed of according to strict environmental regulations.
This level of diligence provides tangible proof of your commitment to ESG goals, creating an auditable record that demonstrates your company is actively reducing its environmental footprint, conserving natural resources, and preventing pollution. By making sustainable recycling a mandatory part of your IT lifecycle management Georgia strategy, you are not only protecting the environment but also strengthening your brand's reputation as a leader in corporate responsibility.
How to Choose the Right ITAD Partner in Georgia
Selecting an IT Asset Disposition (ITAD) partner is one of the most critical decisions in your corporate IT strategy. The right vendor acts as a true partner, shielding your business from risk, while the wrong one can expose you to data breaches, compliance penalties, and environmental fines.
This decision transcends merely finding a hauler for old equipment. You are entrusting a provider with your sensitive data, legal compliance, and brand reputation. To assist Georgia businesses in making an informed choice, we have compiled an essential checklist of questions to ask any potential partner.
Verifying Certifications and Security
Begin by scrutinizing a vendor’s certifications. These are not merely website logos; they are proof of rigorous, third-party audits that validate a company's processes for security, environmental responsibility, and safety.
Key questions to ask:
- What industry certifications do you hold? Look for top-tier credentials such as R2v3 (Responsible Recycling) or e-Stewards. These are the gold standards in the ITAD industry.
- Are you NAID AAA Certified? This certification is specific to data destruction and signals adherence to the strictest protocols for secure data sanitization.
- Can you provide a copy of your certifications? A reputable partner will readily share their current certificates for verification.
Evaluating the Chain of Custody
A secure chain of custody is paramount. It is the unbroken, documented trail that follows your assets from your facility to their final disposition. Any gap in this chain creates a significant security risk.
Ask direct questions about their process:
- How do you document the chain of custody? The answer should include serialized asset tags, signed transfer of liability forms at pickup, and secure, GPS-tracked transportation.
- Do you use your own trucks and employees? A vendor with its own fleet and background-checked team maintains far greater control over security than one that subcontracts logistics.
- Can I get a detailed, serialized report for every asset? The final report must list every item by serial number, confirming its disposition (e.g., data destroyed, recycled, or resold).
Understanding Data Destruction and Value Recovery
Finally, demand complete clarity on how a vendor handles data security and financial return. These two outcomes are intrinsically linked, and the process must be transparent. For a comprehensive look at how these services should integrate, explore our guide on comprehensive ITAD services in Georgia.
Critical Questions for Transparency
A trustworthy ITAD partner will provide clear, straightforward answers to these questions: "What is your exact process for NIST 800-88 compliant data wiping versus physical shredding?" "How do you determine the fair market value of our assets for a buyback?" and "What will our value recovery report look like, and when will we receive it?"
Securing answers to these questions empowers IT managers across Georgia to vet vendors with confidence, cutting through marketing claims to find a partner that delivers proven security, verifiable compliance, and transparent financial returns.
Common Questions About IT Lifecycle Management Answered
If you're exploring IT lifecycle management in Georgia, practical questions are a natural part of the process. To provide clarity, we have compiled answers to the most common inquiries from businesses across the state. Consider this your quick-start guide.
What Does It Cost to Recycle Our Old IT Equipment?
The cost depends on the composition of your retired assets. For many corporate clients, the service is free of charge, and some even receive payment for their equipment.
Valuable Assets: If your retired equipment includes recent-generation laptops, servers, or networking hardware, our IT asset buyback program may cover all logistics costs and result in a net payment to your company.
Mixed Lots: Most businesses possess a mix of valuable and non-valuable equipment. In such cases, the revenue from remarketing valuable assets often offsets the cost of recycling obsolete items.
Recycling-Only Loads: For equipment with no resale value, a recycling fee may be necessary to cover labor, transport, and responsible processing of hazardous materials. We provide transparent, upfront quotes with no hidden fees.
How Can We Be Sure Our Data Is Actually Destroyed?
Data security is paramount. We provide absolute, auditable proof that your data has been destroyed. We offer documentation confirming every storage device has been sanitized to NIST 800-88 standards or physically shredded.
After every project, you will receive a Certificate of Data Destruction. This legal document lists the serial numbers of all processed hard drives and storage devices. It serves as your official compliance record and transfers liability, providing complete peace of mind.
What Types of Equipment Do You Accept?
Our services are focused exclusively on commercial and enterprise-grade electronics. We do not handle residential items. We are equipped to manage a vast range of business assets.
If it has a plug or a battery, we can likely accept it. This includes, but is not limited to:
- IT Hardware: Laptops, desktops, servers, monitors, networking switches, and routers.
- Data Center Equipment: Server racks, uninterruptible power supplies (UPS), and storage arrays.
- Specialized Electronics: Medical equipment, laboratory instruments, and industrial machinery.
- Office Electronics: Printers, copiers, and telecommunication systems.
If you have unique or specialized equipment, please contact us. Our team possesses the expertise to manage nearly any electronic asset your Georgia business needs to retire.
For a no-obligation quote or to discuss your specific IT lifecycle management Georgia needs, contact Beyond Surplus today. Let our experts provide a secure, compliant, and cost-effective solution for your retired technology. Schedule your business pickup with Beyond Surplus.