Secure destruction of hard drives is the only way for your business in the United States to be 100% sure the data on an old storage device is gone forever. It’s a formal process designed to make corporate information completely unrecoverable, protecting it from unauthorized access during IT asset disposal. For any business owner or IT manager in the United States, simply hitting "delete" or even reformatting a drive is a significant risk. With the right software, determined individuals can often recover that "deleted" data, creating a massive liability for any U.S. enterprise.
Understanding the Stakes: Why Secure Destruction is a Business Imperative
In a commercial setting, failing to properly dispose of retired hard drives is much more than a simple operational oversight—it's a direct threat to your company’s security, reputation, and financial stability. Every legacy computer, server, or storage device holds a piece of your corporate history, including customer lists, financial records, trade secrets, and employee PII. Leaving that data intact on a device you’re disposing of is like leaving the blueprint to your business out in the open. Proper, certified destruction is a fundamental part of any solid Data Loss Prevention strategy. It is the final, non-negotiable step in the lifecycle of your sensitive business data.
Why It Is a Business Necessity
The demand for professional data destruction services across the United States is climbing, driven by a heightened awareness of data security risks and increasingly strict privacy laws. This urgency is reflected in the market. The Data Destruction Service Market was valued at USD 12 billion in 2025 and is projected to explode to USD 39.3 billion by 2035—a compound annual growth rate (CAGR) of 12.6%. North America is set to lead this charge, holding 38% of the market share, driven by tough regulations and the sheer volume of data handled by U.S. businesses. To put it in perspective, data breaches in the U.S. exposed a staggering 353 million records in 2023 alone.
For any modern business in the United States, secure data destruction isn't an optional expense—it's an essential investment in risk management. It is what protects your enterprise from crippling fines, litigation, and the kind of reputational damage that can take years to repair.
Key Reasons To Prioritize Secure Destruction
Implementing a formal process for destroying old hard drives is a core component of a comprehensive IT asset disposition strategy that solves several critical business challenges simultaneously.
Here’s why every organization must make this a priority:
- Protecting Sensitive Corporate Data: This is the primary driver. It prevents confidential company, client, or patient data from being accessed by unauthorized parties.
- Ensuring Regulatory Compliance: Federal and state laws like the FTC Disposal Rule, HIPAA, and GLBA don't just suggest—they mandate—the secure disposal of sensitive information. Non-compliance results in severe financial penalties.
- Safeguarding Brand Reputation: A single public data breach can demolish customer trust that took decades to build. The damage to a company's image can be irreversible.
- Preventing Corporate and Customer Identity Theft: Discarded hard drives containing personally identifiable information (PII) are a primary target for criminals. Proper destruction is a direct action to protect your employees and customers from fraud.
The Core Methods of Hard Drive Destruction
When a corporate hard drive reaches its end-of-life, dragging files to the trash bin is entirely insufficient. To truly secure your business's data, you need a method that renders the information completely unrecoverable. For any enterprise, selecting the right technique depends on the media type (HDD vs. SSD), asset reuse potential, and the sensitivity of the data involved. The three primary methods for secure data destruction are physical shredding, degaussing, and data wiping (sanitization). Each offers a different level of security and serves a distinct business case.
Physical Shredding: The Gold Standard for Businesses
Physical shredding is the most definitive and verifiable method for data destruction. The process is exactly as it sounds: hard drives are fed into powerful, industrial shredders that grind them into small, mangled pieces of metal and plastic. This mechanical destruction is absolute—the drive platters or flash memory chips are physically obliterated, ensuring the data is gone for good.
This method is the only guaranteed solution for Solid-State Drives (SSDs). Unlike traditional Hard Disk Drives (HDDs), SSDs store data on flash memory chips, which are immune to magnetic destruction methods like degaussing. Shredding is the only NIST-approved "Destroy" method for these assets.
For organizations that cannot tolerate any risk, on-site physical shredding offers the ultimate security and peace of mind. Witnessing the destruction at your facility provides a level of transparency that confirms your data is irrevocably destroyed before the assets leave your custody.
Degaussing: Magnetic Data Erasure for HDDs
Degaussing is a highly effective method for purging data from magnetic media, such as traditional HDDs and legacy backup tapes. A degausser subjects the drive to an extremely powerful magnetic field, instantly and completely scrambling the magnetic domains on the drive's platters where data is stored.
Once a drive is degaussed, it is rendered permanently inoperable and cannot be reused. While highly effective for HDDs, it is crucial to remember that degaussing has zero effect on SSDs, flash drives, or other non-magnetic storage media. For a deeper technical overview, review our guide on what degaussing is and how it works.
This flowchart can help your business decide on the right destruction method.
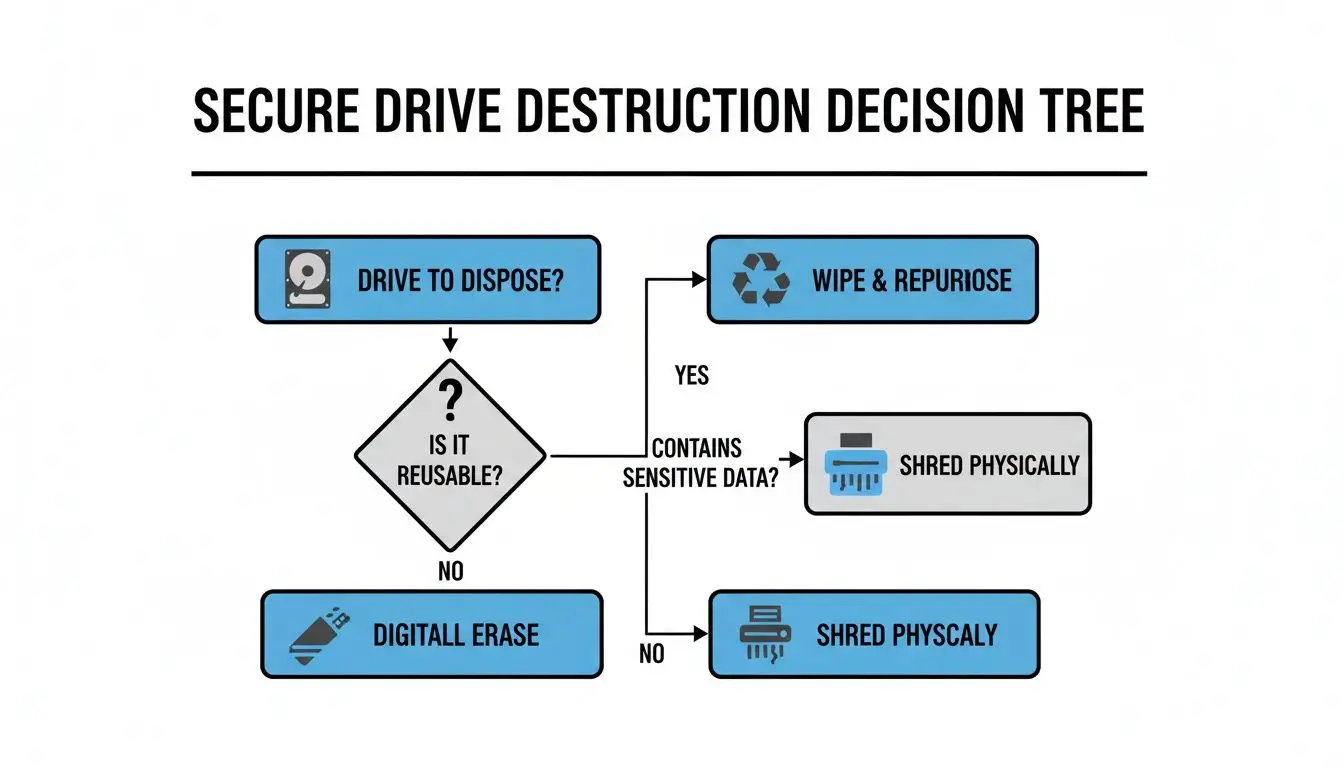
The key takeaway for businesses is that physical shredding is the universal solution, especially for end-of-life media, SSDs, or when data sensitivity demands absolute destruction.
Data Wiping: The Solution for Asset Reuse
Data wiping, or data sanitization, is a software-based method that overwrites every sector of a hard drive with random binary data. This process is repeated multiple times according to established protocols, like the NIST 800-88 "Purge" standard, to ensure the original information is forensically unrecoverable.
The primary business benefit of data wiping is that the hard drive remains functional, allowing it to be safely reused, redeployed within your organization, or resold to recover value. This makes it a cost-effective and environmentally responsible option for viable IT assets. The drawbacks include the time required for the process and the difficulty in verifying success on drives with damaged sectors.
The market trend is increasingly toward physical destruction for its foolproof outcome. North America currently leads the global Hard Drive Shredding Services Market, which hit USD 0.72 billion in 2024 and is projected to climb to USD 1.2 billion by 2033. This is fueled by the fact that 80% of U.S. enterprises now prefer shredding, partly because studies have shown that 42% of drives sanitized with software alone still contained recoverable data.
Maintaining Compliance with U.S. Data Security Regulations
Disposing of old corporate hard drives is not just an IT task; it is a legal and regulatory requirement. Mishandling this process can transform a routine equipment refresh into a legal and financial crisis. For any U.S. business, understanding the nexus between the technical act of destruction and your legal obligations is absolutely critical. Imagine a healthcare system facing a multi-million-dollar fine because retired hard drives containing patient data were improperly disposed of. This is a real-world consequence of inadequate data destruction protocols.
Key Regulations Governing Data Disposal in the U.S.
Several federal and state laws dictate how organizations must destroy sensitive information. Familiarity with these regulations is the first step toward building a compliant IT asset disposal (ITAD) program that protects your business.
- HIPAA (Health Insurance Portability and Accountability Act): This applies to the healthcare sector and its business associates, mandating secure disposal of electronic protected health information (ePHI).
- FACTA (Fair and Accurate Credit Transactions Act): The FTC Disposal Rule under FACTA requires any business handling consumer reports (e.g., credit reports, background checks) to destroy that information to prevent unauthorized access.
- GLBA (Gramm-Leach-Bliley Act): Aimed at financial institutions, this law requires them to protect consumers' private financial data. Its Safeguards Rule mandates a written plan for protecting client information, including secure disposal procedures.
These are legally binding rules with severe penalties for non-compliance. To mitigate this risk, businesses must address the hidden costs of poor data governance by establishing robust policies for the entire data lifecycle.
The NIST 800-88 Framework: The U.S. Standard for Compliance
Most regulations do not prescribe a specific technology. Instead, they point to a set of federal guidelines as the benchmark for compliance: NIST Special Publication 800-88, Guidelines for Media Sanitization. This document is the de facto playbook for data destruction in the United States.
NIST 800-88 defines three levels of media sanitization:
- Clear: Uses software-based overwriting. Appropriate for low-risk scenarios where the drive will be reused within the same secure enterprise environment.
- Purge: Renders data recovery infeasible even with advanced laboratory techniques. Methods include degaussing.
- Destroy: Renders the media completely unusable and the data unrecoverable. Methods include shredding, pulverizing, or incineration.
The "Destroy" method is the only one that provides absolute certainty. It is the gold standard for compliance when dealing with highly sensitive data or when assets reach their final end-of-life, making physical shredding the preferred choice for risk-averse U.S. businesses.
Aligning your hard drive destruction process with NIST guidelines ensures your approach is not only effective but also legally defensible.
On-Site Versus Off-Site Hard Drive Destruction for Your Business

Once your business has selected a destruction method, the next critical decision is where the destruction will take place. You have two primary commercial service options: on-site and off-site destruction. Each offers distinct advantages, and the optimal choice depends on your company’s security policies, compliance requirements, and logistical considerations. This decision is a key part of your overall IT asset disposition (ITAD) plan.
On-Site Destruction: Maximum Security and Transparency
On-site hard drive destruction offers the highest possible level of security and transparency for your business. A specialized, mobile shredding vehicle comes directly to your U.S. facility, and your hard drives are destroyed on the spot under your supervision. This completely eliminates any chain-of-custody risk during transit.
This approach is the standard for organizations handling highly sensitive data or operating under strict regulatory mandates. Industries like healthcare (HIPAA), finance (GLBA), and government contractors often require the "witnessed destruction" that only on-site services can provide.
- Ultimate Security: Your data-bearing assets never leave your premises intact.
- Immediate Verification: Your team can witness the shredding process, providing instant, irrefutable proof of destruction.
- Simplified Audit Trail: The chain of custody is as short as possible, with collection and destruction occurring at the same time and place.
The primary trade-off is typically cost, as mobilizing specialized equipment and personnel to your location is more resource-intensive. However, for many businesses, the enhanced security justifies the premium.
Off-Site Destruction: Secure, Efficient, and Cost-Effective
Off-site destruction is a secure, efficient, and often more economical alternative for U.S. enterprises. In this model, your hard drives are collected, inventoried by serial number, and transported in locked, GPS-tracked vehicles to a secure, access-controlled processing facility. There, the drives are destroyed according to the same rigorous standards as on-site services.
The entire process is governed by a strict chain of custody. Every asset is scanned and tracked at each touchpoint, creating a detailed audit trail from your loading dock to the final shred.
Off-site destruction is built on a foundation of documented trust and verified security protocols. Choosing a certified partner who provides an unbroken and transparent chain of custody is absolutely critical to ensuring this model meets your security and compliance needs.
This model is ideal for businesses requiring a cost-effective solution for large quantities of drives or for those whose risk policies do not mandate witnessed destruction. Demand for both options is driving major market growth. The global Hard Disk Destruction Equipment Market, valued at USD 2.85 billion in 2025, is projected to climb to USD 4.23 billion by 2032. This expansion is powered by a network of certified ITAD providers across the United States. You can review market projections from 360iResearch for more detail.
The Role of Certification and Chain of Custody in Business

When your business outsources hard drive destruction, the physical process is only half the battle. The other critical component is the documented proof that the job was completed correctly. This is where professional certifications and a robust chain of custody come in, providing the auditable evidence needed to protect your business from liability. Without this paper trail, you have no verifiable proof of compliance.
The Certificate of Destruction: Your Legal Proof
Upon completion of any destruction project, a professional ITAD partner will issue a Certificate of Destruction (CoD). This is not a simple receipt; it is a formal legal document that confirms your media has been destroyed in accordance with industry standards, rendering the data unrecoverable. This certificate formally transfers liability for the data from your company to the disposal vendor and serves as your official record for compliance audits.
A proper CoD must include:
- The date and location of destruction.
- A clear description of the materials destroyed, often including serial numbers.
- The specific destruction method used (e.g., shredding to a specific particle size).
- A unique reference number for the job.
- A statement of compliance with relevant laws and standards.
Following the Chain of Custody
A chain of custody is a chronological, documented trail that tracks every single hard drive from the moment it leaves your business's control to its final destruction. This unbroken record is your guarantee that no asset is lost, stolen, or mishandled during the process. For off-site destruction services, a secure chain of custody is non-negotiable.
The process includes:
- Serialized Inventory: Each hard drive is scanned and inventoried by serial number at your location.
- Secure Transport: Drives are moved in locked containers within GPS-tracked vehicles operated by background-checked personnel.
- Facility Check-In: All assets are scanned again upon arrival at the secure facility.
- Final Confirmation: Drives are reconciled against the initial inventory before destruction, and the CoD is issued.
This meticulous, step-by-step tracking creates an auditable record demonstrating complete due diligence. It proves not only that your drives were destroyed, but also documents how they were securely managed throughout the entire process.
Choosing a vendor with a transparent and verifiable chain of custody is fundamental to responsible corporate IT asset disposal.
How to Choose the Right ITAD Partner in the United States
Selecting the right IT Asset Disposition (ITAD) partner is the final, and most critical, step in executing a secure hard drive destruction strategy for your business. This decision is not merely about logistics; it's about entrusting a vendor with your data security, regulatory compliance, and brand reputation. The right partner acts as an extension of your security team, providing a reliable, documented, and compliant process for every IT asset your business retires.
Key Certifications to Look For in a U.S. Vendor
Certifications are third-party verifications that a vendor’s processes meet the highest industry standards for security, safety, and environmental responsibility. They are your primary tool for vetting potential partners.
Look for these essential U.S. certifications:
- NAID AAA Certification: This is the gold standard for the data destruction industry. It ensures a vendor adheres to the most stringent security protocols for shredding, sanitization, and maintaining a secure chain of custody.
- R2 (Responsible Recycling) Certification: This certification focuses on environmentally sound and socially responsible electronics recycling. An R2-certified partner guarantees your non-data-bearing e-waste is managed properly and does not end up in a landfill.
A vendor holding both NAID AAA and R2 certifications demonstrates a comprehensive commitment to both data security and environmental stewardship. This dual qualification should be a primary requirement for any U.S. business.
Essential Questions to Ask Potential Vendors
Before signing a service agreement, conduct thorough due diligence. For an exhaustive guide, use our complete vendor due diligence checklist to ensure you cover all critical areas.
Start your evaluation with these four essential questions:
- Can you provide a detailed, serialized chain of custody report for every job? This document is your auditable proof of secure handling from pickup to destruction.
- Are your destruction methods compliant with NIST 800-88 guidelines? Adherence to this federal standard demonstrates best-practice data sanitization and destruction.
- Do you offer IT asset value recovery or buyback programs? A premier partner can often recover value from retired but functional equipment, turning a disposal cost into a revenue stream for your business.
- Are your employees background-checked and formally trained in data security protocols? The personnel handling your sensitive assets must be trustworthy and competent.
Ultimately, choosing the right ITAD partner comes down to certified trust and proven performance. You need a provider like Beyond Surplus that delivers certified processes, transparent reporting, and a full suite of services to protect your U.S. business from every angle.
Your Business's Hard Drive Destruction Questions, Answered
When it's time for your business to dispose of old hard drives, many practical questions arise. Addressing these concerns is crucial for protecting your corporate data and ensuring compliance. We've answered the most common questions from IT managers and business owners across the United States to help you implement a secure and defensible strategy.
Is It Sufficient to Drill Holes in Our Hard Drives?
It’s a common misconception that drilling holes through a hard drive is an adequate method of data destruction. While better than doing nothing, it is far from a secure or compliant solution for a business. Data recovery specialists can often retrieve data from the undamaged sections of the magnetic platters between the drill holes. For total security, professional shredding is the only guaranteed method. Industrial shredding pulverizes the entire drive and its platters into small metal fragments, making data recovery impossible and ensuring your business is fully protected.
Is Data Wiping Sufficient for Corporate Compliance?
Software-based data wiping can be a compliant method, provided it is performed according to a recognized standard like NIST 800-88 (Purge level). It is a viable option when your business plans to reuse or resell the hardware. However, wiping has limitations. The process can fail on drives with bad sectors, leaving data remnants, and it provides no physical proof of destruction, which can be problematic during a compliance audit. For the highest level of assurance and a clear audit trail, physical destruction is the superior choice.
What Happens to the Shredded Hard Drive Materials?
After your business's hard drives are shredded, the process is not over. The resulting pile of shredded material—mostly aluminum, steel, and circuit boards—is securely transported to a certified recycling facility. There, these commodities are sorted, separated, and processed to be reintroduced into the manufacturing supply chain for new products. This responsible, R2-certified approach prevents hazardous e-waste from entering landfills and helps your company achieve its corporate sustainability goals by participating in the circular economy.
Ready to implement a foolproof, certified data destruction strategy for your U.S. business? Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal with complete, auditable chain-of-custody documentation.