For enterprises in Georgia's dynamic business landscape, managing retired IT assets is a critical component of a sound business strategy, not a mere disposal task. An effective enterprise ITAD Georgia program is about more than clearing out old servers; it’s a strategic process for minimizing risk, controlling costs, and extracting maximum value from obsolete equipment. When executed professionally, IT asset disposition protects sensitive data, ensures regulatory compliance, and can convert old hardware into a significant revenue stream.
Navigating IT Asset Disposition in Georgia's Tech Hub
IT Asset Disposition (ITAD) has evolved from a back-office function to a boardroom-level concern for Georgia businesses. This shift is driven by the state's rapid growth as a technology and data center hub, which creates immense opportunities alongside substantial risks.
The most effective way to approach ITAD is not as "disposal" but as comprehensive end-of-life management for your technology. A professional partner manages the entire lifecycle, from secure data destruction and logistics to responsible recycling and remarketing retired equipment for a financial return.
The Georgia Data Center Boom
The exponential growth of the data center market in Georgia underscores why professional ITAD is no longer optional. The Metro Atlanta area, in particular, is experiencing unprecedented expansion. In 2024, it surpassed all other U.S. markets with an astonishing 705.8 MW of net absorption, while construction activity increased by 76% year-over-year.
This boom, fueled by hyperscalers like AWS and Meta, means companies are constantly upgrading and retiring servers, storage arrays, and networking hardware. This rapid turnover creates a continuous flow of data-bearing assets that must be managed securely and efficiently. Any misstep in this process can expose an organization to significant risk.
Core Objectives of a Georgia ITAD Program
Every enterprise in Georgia should build its ITAD strategy on several fundamental objectives. These goals form the foundation of a program designed to protect the organization from all angles.
- Ironclad Data Security: Ensuring every byte of sensitive corporate, customer, and employee data is forensically destroyed before an asset leaves your facility.
- Regulatory Compliance: Adhering to industry and federal regulations such as HIPAA, GLBA, and the FTC Disposal Rule to avoid severe fines and legal complications.
- Maximum Value Recovery: Recovering the highest possible financial return from retired assets through secure resale and remarketing, which helps offset new technology investments.
- Environmental Responsibility: Guaranteeing that electronics that cannot be reused are processed in an environmentally sound manner, aligning with corporate sustainability initiatives.
To provide a clearer perspective, here is how these components integrate to form a comprehensive ITAD strategy tailored for Georgia businesses.
Key Components of a Strategic ITAD Program for Georgia Businesses
| Component | Business Objective | Key Benefit for Georgia Enterprises |
|---|---|---|
| Secure Data Destruction | Eliminate the risk of a data breach from retired assets. | Protects brand reputation and ensures compliance with data privacy laws like HIPAA. |
| On-Site Logistics | Efficiently de-install and remove equipment with minimal disruption to operations. | Frees up internal IT teams and valuable real estate, especially during office moves. |
| Asset Remarketing | Recover the maximum possible financial value from used but functional hardware. | Generates revenue to offset new equipment costs, improving the overall IT budget. |
| Certified Recycling | Ensure environmentally responsible disposal of non-viable electronics. | Meets corporate social responsibility (CSR) goals and avoids environmental fines. |
| Detailed Reporting | Provide an auditable chain-of-custody for every asset from pickup to final disposition. | Delivers the proof of compliance and data destruction necessary for internal and external audits. |
Ultimately, a well-executed ITAD program is more than a series of tasks; it is a strategic advantage that protects your bottom line, your data, and your reputation.
When planning a major equipment removal, it is also wise to consider the broader context. These projects often coincide with services like professional office decommissioning services. For a detailed overview of local regulations and best practices, consult our complete guide to Georgia electronics recycling services.
Protecting Your Business with Secure Data Destruction
For enterprise ITAD in Georgia, nothing is more critical than the absolute, verifiable destruction of sensitive data. This is not merely a procedural step. A single retired hard drive that is improperly handled can become a significant liability, leading to catastrophic financial penalties, legal disputes, and irreparable damage to your company's reputation.
This is why data destruction is not just part of the process—it is the most crucial element of any ITAD strategy.
Simply deleting files or reformatting a drive provides a false sense of security. Commercially available software can easily recover "deleted" information, leaving your organization exposed. True data security requires professional methods that render data completely unrecoverable.
Navigating Compliance in Georgia
For any enterprise operating in Georgia, navigating the complex web of data privacy regulations is a fundamental aspect of doing business. Several key federal laws dictate how you must handle sensitive information on retired assets, and the consequences for non-compliance are severe.
- FTC Disposal Rule: This rule mandates that businesses take appropriate measures to dispose of sensitive information derived from consumer reports to protect individuals from identity theft.
- HIPAA (Health Insurance Portability and Accountability Act): For healthcare providers across Georgia—from major Atlanta hospitals to regional clinics—HIPAA requires strict protocols for safeguarding protected health information (PHI) on any electronic device.
- GLBA (Gramm-Leach-Bliley Act): Financial institutions, including banks, investment firms, and insurance companies, must comply with GLBA to protect consumers' private financial data.
These are not mere guidelines; they are legally binding requirements. Failure to provide proof of secure data destruction can trigger audits, substantial fines, and significant legal liability.
A robust data destruction plan serves as your primary line of defense. It demonstrates due diligence and provides a clear, auditable trail documenting every measure your organization took to protect sensitive information, shielding you from regulatory scrutiny.
Choosing the Right Data Destruction Method
When it comes to data destruction, you have several options. The optimal method for your Georgia enterprise depends on your security requirements, asset types, and compliance needs. It is about selecting the right tool for a critical task.
On-Site Physical Shredding
This method involves bringing a mobile shredding vehicle directly to your facility in Georgia. Your hard drives, solid-state drives (SSDs), and other storage media are physically destroyed into small, irrecoverable fragments before your eyes.
- Maximum Security: Offers the highest level of assurance, as you can witness the destruction firsthand.
- Immediate Verification: Provides instant confirmation that your data-bearing assets have been permanently destroyed.
- Ideal for: Organizations with highly sensitive data, strict compliance mandates, or policies that prohibit data-bearing assets from leaving the premises intact.
Certified Data Wiping (NIST 800-88)
This software-based approach uses certified processes to overwrite data on a drive multiple times, making the original information impossible to recover with forensic tools. The NIST 800-88 standard is the industry benchmark for data sanitization.
- Preserves Asset Value: Because the drive remains physically intact, it can be refurbished and resold, maximizing your financial return.
- Environmentally Friendly: Promotes asset reuse, aligning with corporate sustainability objectives.
- Ideal for: Leased equipment that must be returned in working order or for assets with significant resale value.
The Certificate of Data Destruction: Your Liability Shield
Regardless of the method chosen, the process is not complete until you receive a Certificate of Data Destruction. This official document serves as your legal proof that the data on your retired assets was securely and permanently destroyed in accordance with all relevant regulations.
This certificate is a non-negotiable deliverable from any reputable ITAD partner. It lists the serial number of every drive that was sanitized or shredded, creating a complete, auditable record that transfers liability from your organization to the vendor. To learn more about these processes, explore our secure data destruction services. This documentation is your most valuable asset during audits and the ultimate proof of your commitment to data security.
Turning Retired IT Assets into Revenue
Imagine if your retired servers, laptops, and networking gear were not a disposal expense but a hidden revenue stream. This is the core principle of IT asset value recovery. A strategic approach to enterprise ITAD in Georgia transforms a cost center into a profit center by realizing the maximum financial return on equipment that no longer meets your operational needs but remains valuable to others.
This is not about simply selling old computers. It is a calculated process where an expert ITAD partner meticulously evaluates each asset to determine its highest potential value on the secondary market. By tapping into this market, Georgia enterprises can directly offset the cost of new technology and enhance their overall IT budget.
The Asset Evaluation Process
The journey from a retired asset to recovered revenue begins with a thorough, expert evaluation. Not all equipment holds the same value, and an experienced partner knows precisely what to look for to maximize your return.
This detailed assessment channels your equipment into three primary avenues for value recovery:
- Remarketing: This is the ideal outcome, typically for newer, high-demand equipment like recent-generation servers, laptops, and networking switches. These items are tested, securely wiped, and sold on the secondary market.
- Refurbishment: Assets with minor cosmetic or functional issues can be professionally refurbished to meet market standards, restoring their value before resale.
- Component Harvesting: Even if a computer is too old to be sold whole, its internal components—such as RAM, CPUs, and power supplies—often retain significant value. These parts are carefully harvested and sold individually.
This multifaceted approach ensures no potential value is overlooked. To gain further insights into this process, learning how to liquidate assets for maximum return can be beneficial.
Demystifying the IT Buyback Process
The IT buyback or asset recovery process should be straightforward and transparent, providing Georgia businesses a clear path from assessment to payment. It transforms a logistical challenge into a simple financial transaction.
Here is a step-by-step overview of the process:
- Initial Inventory Assessment: You provide your ITAD partner with a detailed list of the assets you wish to retire, including make, model, specifications, and quantities.
- Fair Market Valuation: Using real-time market data, your partner delivers a comprehensive quote outlining the expected return for your equipment based on current demand.
- Secure Logistics and Pickup: Upon approval of the quote, the partner arranges for the secure pickup and transport of the assets from your Georgia facility to their processing center.
- Audit and Final Reporting: At the facility, each asset is audited against the initial inventory. Its condition is verified, and all data is securely destroyed. You receive a final report confirming the inventory and data destruction.
- Payment and Finalization: After the audit is complete, you receive payment for the agreed-upon value of your assets, officially converting your old hardware into working capital.
This professional approach aligns with industry trends. The U.S. ITAD market, valued at $2.66 billion in 2022, is projected to reach $4.90 billion by 2032. This growth is driven by data security concerns and continuous technology upgrades, particularly in tech hubs like Georgia.
For more information on how we can help you recover value from your retired IT assets, please see our guide on IT asset recovery services in Georgia.
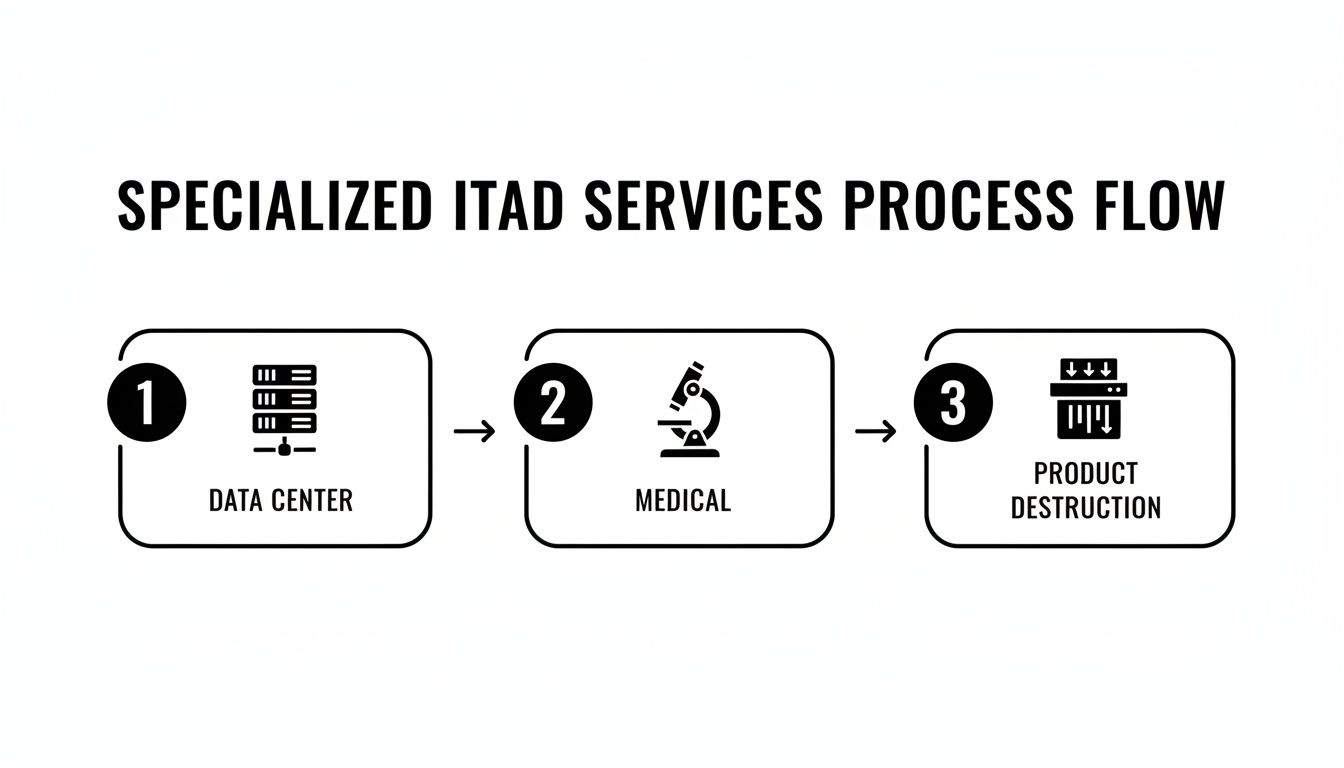
A Closer Look: ITAD for Georgia's Key Industries
A one-size-fits-all approach to retiring old technology is ineffective. Every industry in Georgia faces unique challenges, and your IT asset disposition strategy must reflect these specific needs. True enterprise ITAD in Georgia requires specialized solutions for sectors like data centers, healthcare, and manufacturing.
An ITAD partner with deep industry experience understands the distinction between decommissioning a large-scale data center and securely managing sensitive medical equipment. The process must be tailored to ensure every asset is handled with the appropriate level of security, precision, and care.
Tackling Data Center Decommissioning
Georgia is a major hub for data centers, particularly in the Atlanta metro area. Decommissioning one of these facilities is a monumental undertaking that is far more complex than a typical office IT cleanout. It is a high-stakes project requiring meticulous precision to execute without causing operational disruptions or security vulnerabilities.
A professional data center decommissioning project involves several critical steps:
- Project Management: Meticulous planning and coordination of every detail, from initial inventory to the final asset report.
- On-Site De-installation: Safely de-racking and disconnecting thousands of servers, storage arrays, and networking devices in a systematic manner.
- Asset Tagging and Auditing: Establishing a chain of custody by tagging and inventorying every asset, capturing serial numbers to ensure complete accountability.
- Secure Packing and Transport: Utilizing specialized equipment and secure, GPS-tracked vehicles to move sensitive hardware from your site to a secure processing facility.
This process is not merely about removing old equipment; it is about dismantling a complex, live environment while guaranteeing 100% data security and maintaining a perfect audit trail.
The High Stakes of Laboratory and Medical Equipment Disposal
For healthcare providers and research labs in Georgia, the data they handle is extremely sensitive and protected under strict HIPAA regulations. Disposing of old lab and medical equipment requires specialized expertise. Devices such as patient monitors, MRI machines, and diagnostic tools often contain internal storage with Protected Health Information (PHI).
In healthcare and life sciences, data privacy is paramount. The ITAD process must ensure the forensic destruction of all patient or research data. A rock-solid audit trail is essential to prove HIPAA compliance, as the penalties for a breach are severe and can erode patient trust.
In addition to data security, this equipment often contains hazardous materials that must be handled responsibly to meet environmental regulations. A knowledgeable partner will manage both data security and environmental compliance, providing a complete, defensible solution.
Secure Product Destruction for Brand Protection
For manufacturers, distributors, and retailers in Georgia, managing returned, defective, or overstock inventory presents a significant challenge. Simply discarding these items is not an option. If they are scavenged and resold on the gray market, it can severely damage your brand's reputation or create legal liabilities.
This is where product destruction services become essential. The process is designed to ensure your branded goods are permanently removed from the market.
- Secure Logistics: All products are securely transported from your warehouse to a dedicated destruction facility.
- Witnessed Destruction: For complete peace of mind, you can often witness the destruction process, either in person or via a secure video feed.
- Certificate of Destruction: You receive official documentation confirming that the products were destroyed, which is vital for inventory records, insurance claims, and compliance audits.
By addressing these specialized requirements, a proficient ITAD partner becomes a valuable resource for any challenge, ensuring every unique asset is managed securely, responsibly, and in alignment with your industry's specific needs.
The Critical Role of Secure Logistics and Chain of Custody
The strength of an enterprise ITAD program lies in its logistical framework. While secure data destruction and value recovery are the ultimate goals, the intermediate steps—the physical transport of your assets—are where vulnerabilities can arise. For any enterprise ITAD Georgia strategy, secure logistics is not just a service detail; it is the foundation of trust and compliance.
From the moment a server is removed from a rack in your Atlanta data center or a laptop is packaged at your Savannah office, a strict chain of custody must be established. This is the unbroken, documented trail that tracks every asset from your facility to its final disposition. Without it, you lack verifiable proof of what happened to your equipment, leaving your organization exposed to risk.
Why Chain of Custody is Non-Negotiable
The chain of custody is the central nervous system of your ITAD project. It is the official, auditable record that confirms the location, handling, and processing of every asset. This documentation is your most effective defense against a potential data breach, theft, or a negative compliance audit.
A proper chain of custody provides:
- Accountability: Every asset is scanned and logged at each touchpoint, from pickup to final processing.
- Transparency: You receive a clear, verifiable record of your equipment's journey.
- Proof of Compliance: This documentation is precisely what you need to satisfy internal audits and external regulatory requirements.
This meticulous tracking ensures that a hard drive destined for shredding is not accidentally placed on a pallet for resale. For any IT manager in Georgia, demanding a detailed chain of custody is a fundamental step in protecting the organization.
An ITAD vendor's approach to logistics is a direct reflection of their commitment to security. If their transportation process lacks transparency or rigor, any promises of data destruction are built on a weak foundation.
The Anatomy of Secure Transportation
Securely transporting sensitive IT assets requires more than a standard truck and driver. It demands a coordinated system designed to protect your equipment from the moment it leaves your premises. Professional ITAD logistics incorporate several key features to ensure your assets are never at risk during transit.
This flowchart illustrates how different types of equipment require specialized, secure handling, from data center hardware to medical devices.
As shown, whether dealing with servers, specialized medical equipment, or branded products slated for destruction, a secure and well-documented logistical process is the common thread ensuring integrity.
Key elements of secure transport include:
- Vetted Logistics Professionals: All drivers and technicians undergo extensive background checks and receive specialized training in handling sensitive electronics.
- GPS-Tracked Vehicles: The entire fleet is monitored in real-time, adding a powerful layer of security and accountability.
- Locked and Sealed Transport: Assets are moved in locked, sealed containers or trucks to prevent unauthorized access during transit.
- Seamless Scheduling: A reliable partner works with your schedule to arrange pickups that minimize disruption, whether for a small office or a full data center decommissioning.
These measures provide confidence that your valuable, data-bearing assets are handled with precision and professionalism at every stage. You can learn more about how we manage these complex projects by reviewing our nationwide reverse logistics services. Ultimately, robust logistics ensure your ITAD program is protected from start to finish.
Choosing the Right ITAD Partner in Georgia
Selecting the right vendor for enterprise ITAD in Georgia is one of the most important decisions an IT leader will make. This partnership extends beyond simple equipment disposal; it directly impacts your data security, regulatory compliance, and financial bottom line. The right choice mitigates risk and converts old assets into revenue, while the wrong one can expose your company to significant liabilities.
To make an informed decision, you need a clear evaluation framework. Begin by seeking a partner with deep experience in the Georgia market and a national service footprint capable of supporting your business as it grows. This combination is crucial—it ensures they understand local compliance nuances while having the scale to manage complex, multi-site projects seamlessly.
Key Strengths of a Premier ITAD Provider
When vetting potential vendors, focus on three non-negotiable pillars: proven security, certified sustainability, and a demonstrable track record of asset value recovery. These attributes distinguish a transactional vendor from a true strategic partner.
A top-tier provider delivers a comprehensive, fully documented process from beginning to end.
- Verified Security Protocols: They must offer both on-site physical destruction and certified data wiping compliant with NIST 800-88 standards. You should receive a Certificate of Data Destruction for every data-bearing device, without exception.
- Certified Sustainability: Look for key industry certifications that prove a commitment to responsible recycling. It is essential to understand what R2 Certification is and its importance in ensuring your e-waste is handled ethically and legally.
- National Logistical Capability: Their operations must include secure, GPS-tracked transportation and a documented chain of custody from the moment equipment leaves your Georgia facility.
Aligning with Market Growth and Compliance
The need for a reliable ITAD partner is becoming increasingly urgent due to explosive market growth. The global ITAD market, valued at $20.66 billion in 2025, is projected to reach $31.89 billion by 2029, growing at an 11.5% CAGR. This growth is driven by a massive wave of data center decommissioning, cloud migrations, and stricter e-waste regulations. For IT managers in Atlanta, this trend is a clear signal: strategic ITAD is no longer just about recycling—it's about compliance and revenue.
A partnership with a certified and experienced provider is your best defense against risk. It streamlines operations by offloading complex logistical and compliance burdens, allowing your internal teams to focus on core business objectives while ensuring a positive financial return on retired technology.
Ultimately, the right partner for your Georgia-based enterprise does more than haul away old equipment. They collaborate with you to build a strategic ITAD program tailored to your specific needs, protecting your brand, securing your data, and improving your bottom line.
Common Questions About Enterprise ITAD in Georgia
When it comes to IT Asset Disposition, Georgia enterprises often have practical questions. This is completely normal, as making the right decision is critical for protecting data, ensuring compliance, and recovering value from retired equipment. Let's address some of the most common inquiries from IT leaders.
What Kind of Documentation Should I Expect?
Proper documentation is the backbone of a sound ITAD program. It serves as your official record and proof of compliance.
Any certified partner should provide you with:
- A Detailed Inventory Report: This comprehensive document should detail every asset collected from your facility, itemized by make, model, and unique serial number. It initiates the chain of custody.
- A Certificate of Data Destruction: This document is your legal shield. It confirms that every data-bearing device was sanitized or physically destroyed according to standards like NIST 800-88 and lists the serial number of every processed drive.
- A Certificate of Recycling: This certifies that any equipment unsuitable for resale was managed in an environmentally responsible manner, helping you meet corporate sustainability goals.
Can I Really Get Money Back for My Old Equipment?
Yes, absolutely. This is known as IT asset value recovery, and it is a major benefit of a strategic ITAD program. While not every piece of equipment will have resale value, many assets that are only a few years old remain in high demand on the secondary market.
An expert partner will assess your inventory of servers, laptops, networking gear, and other hardware to determine its fair market value. Any equipment that can be refurbished and resold generates a financial return, which can be used to offset the cost of your next technology refresh.
How Is Data Security Ensured During Transport?
This is a critical concern, and any professional ITAD provider takes it extremely seriously. Secure logistics are non-negotiable to prevent assets from being lost or compromised between your facility and the processing center.
The security of an ITAD program is only as strong as its weakest link. Secure transportation and an unbroken chain of custody are not optional—they are fundamental requirements for mitigating risk.
Security during transit is maintained through several key measures:
- Vetted Personnel: All drivers and technicians handling your assets undergo thorough background checks.
- Secure, GPS-Tracked Vehicles: The entire fleet is monitored in real-time, providing constant visibility of your equipment's location.
- Locked and Sealed Transport: Assets are moved in locked containers or trucks, making unauthorized access virtually impossible.
- Documented Chain of Custody: Each asset is scanned and tracked at every handoff point, creating a complete, auditable trail from your door to its final disposition.
This robust process ensures your sensitive assets are protected every step of the way, providing complete peace of mind.
For a partner that delivers certified security, maximum value recovery, and a transparent process for your Georgia enterprise, contact Beyond Surplus. Discover how our ITAD solutions can protect your organization and enhance your bottom line. Learn more at https://www.beyondsurplus.com.