For IT directors, business owners, and facility managers in Georgia, managing surplus technology is a critical task that extends far beyond simply clearing out old equipment. It’s a complex challenge involving data security, environmental compliance, and the strategic recovery of asset value. Beyond Surplus serves as a professional partner for Beyond Surplus technology reuse in Georgia, transforming retired IT assets from a potential liability into a secure and often profitable opportunity for commercial and enterprise clients.
Navigating IT End-Of-Life Management In Georgia

Managing the end-of-life cycle for your company’s IT equipment is a core business function, not a janitorial task. It directly impacts your data security, regulatory compliance, and financial bottom line. Every server, laptop, and switch contains sensitive corporate data, making secure and certified handling a non-negotiable priority for any modern enterprise.
Improper disposal doesn’t just harm the environment; it exposes your organization to significant operational and financial risks. Data breaches from discarded hard drives can result in severe financial penalties and cause irreparable damage to a brand’s reputation. This is precisely where a professional IT Asset Disposition (ITAD) strategy becomes essential for businesses in Georgia.
The Strategic Value of an ITAD Partner
A true ITAD program is a structured process for managing surplus technology, covering every step from the moment an asset is decommissioned. Partnering with a certified specialist like Beyond Surplus provides Georgia businesses with a distinct competitive advantage.
A dedicated ITAD partner ensures every step is managed with precision, including:
- Secure Data Destruction: We guarantee that all proprietary, employee, and customer data is permanently destroyed, meeting strict compliance standards such as HIPAA, GLBA, and the FTC Disposal Rule.
- Environmental Responsibility: Our certified processes adhere to stringent environmental regulations, preventing hazardous e-waste from entering landfills and supporting your corporate sustainability initiatives.
- Value Recovery: We specialize in identifying assets with remaining market value and remarketing them to generate a return on your initial investment, turning a cost center into a revenue stream.
- Chain-of-Custody Documentation: You receive detailed certificates of data destruction and recycling, which are crucial for audits and legally transfer liability away from your organization.
For Georgia companies, a proactive approach to technology reuse isn’t just good practice—it’s a competitive necessity. Failing to manage IT assets securely at their end-of-life is a direct threat to corporate data integrity and financial stability.
Moving Beyond Simple Disposal
The challenge of managing obsolete IT assets is growing as technology refresh cycles accelerate. This constant upgrading creates an increasing volume of retired equipment that requires secure and responsible handling. Without a defined ITAD plan, these assets quickly become a logistical and security burden. You can learn more about how our structured process helps with IT asset disposition in Georgia and what it can do for your business.
A strategic approach to technology reuse enables Georgia businesses to address these challenges effectively. It ensures every device is processed securely and responsibly, protecting your company while contributing to a sustainable, circular economy. It’s a forward-thinking mindset that transforms a disposal problem into a strategic business opportunity.
How To Prepare Your IT Assets For Disposition
Before any equipment leaves your facility, internal preparation is your first and most effective line of defense against data risks and logistical inefficiencies. A successful technology reuse program begins with a clear, deliberate internal strategy, not when the pickup truck arrives. Neglecting these initial steps can lead to costly errors, from misplaced assets to a critical data breach.
The entire disposition process hinges on one foundational task: creating a comprehensive inventory. You cannot manage what you do not measure. This requires documenting every asset slated for disposal, whether it’s a full rack of servers, a pallet of laptops, or specialized laboratory equipment.
Starting With A Comprehensive Asset Inventory
Your inventory must be more than a simple headcount. For each device, capture key details that will inform every subsequent decision. A detailed spreadsheet or asset management system entry should include:
- Asset Type: (e.g., Laptop, Server, Switch, Medical Device)
- Manufacturer and Model: (e.g., Dell Latitude 7420, Cisco Catalyst 9300)
- Serial Number or Asset Tag: The unique identifier for precise tracking.
- Physical Condition: Note any cosmetic damage or known functional issues.
- Data-Bearing Status: Critically important. Clearly identify if the device contains a hard drive, SSD, or other storage media.
This documentation serves two crucial functions. First, it establishes the initial link in the chain of custody, providing a definitive record of what is leaving your control. Second, it enables accurate sorting, which is essential for determining the appropriate disposition path for each asset. You can dive deeper into this process with our guide on how businesses should prep for IT disposal.
A meticulous inventory isn’t just about logistics; it’s a core component of risk management. Knowing exactly what assets you have and where they are is the first step in protecting the sensitive data they contain.
Categorizing Assets For Maximum Value And Security
Once inventoried, the next step is to categorize your assets. This sorting process separates equipment with potential resale value from items destined for secure recycling. Generally, your assets will fall into two primary categories: those for remarketing and those for recycling.
Newer, functional equipment such as recent-generation laptops, servers, and networking hardware often retains significant market value. Segregating these items ensures they are properly evaluated for our IT buyback program, which can convert a disposal cost into revenue. Conversely, older, damaged, or proprietary equipment should be flagged for secure destruction and recycling.
This proactive sorting aligns directly with your internal data security policies. For example, your policy might mandate that any device containing highly sensitive intellectual property be designated for on-site physical destruction, regardless of its age or condition. Making these determinations before the equipment is moved ensures your security protocols are applied consistently and without exception.
Aligning With State and Federal Regulations
Preparing your assets also means ensuring compliance with a complex web of regulations. Georgia’s electronics recycling landscape is evolving. As 25 US states and D.C. have enacted e-waste laws, the standards for how businesses must manage technology at its end of life have fundamentally changed.
Mishandling e-waste not only exposes sensitive data but can also lead to significant penalties for non-compliance with regulations like the FTC Disposal Rule. For more on Georgia’s role in the national e-waste conversation, check out this piece on reworxrecycling.org. A well-documented preparation process provides the necessary audit trail to prove due diligence and responsible management, protecting your organization from legal and financial repercussions.
Choosing The Right Data Destruction Method
With your assets prepared and inventoried, the most critical decision in the disposition process is selecting the appropriate method for data destruction.
For any business in Georgia, data security is a legal and ethical mandate. Choosing the right data destruction method is paramount to protecting your company, your customers, and your reputation. At Beyond Surplus, we offer several certified options, each designed to meet different security levels, compliance requirements, and equipment types.
Your choice involves balancing the need for absolute data security with the potential to recover value from the hardware. For instance, a high-security server from a financial data center requires a different approach than a pallet of five-year-old office laptops. Understanding the practical differences between physical shredding and certified data wiping is key to making a compliant, secure, and cost-effective decision.
This flowchart illustrates the initial preparation steps that guide you toward the most appropriate destruction method for your equipment.
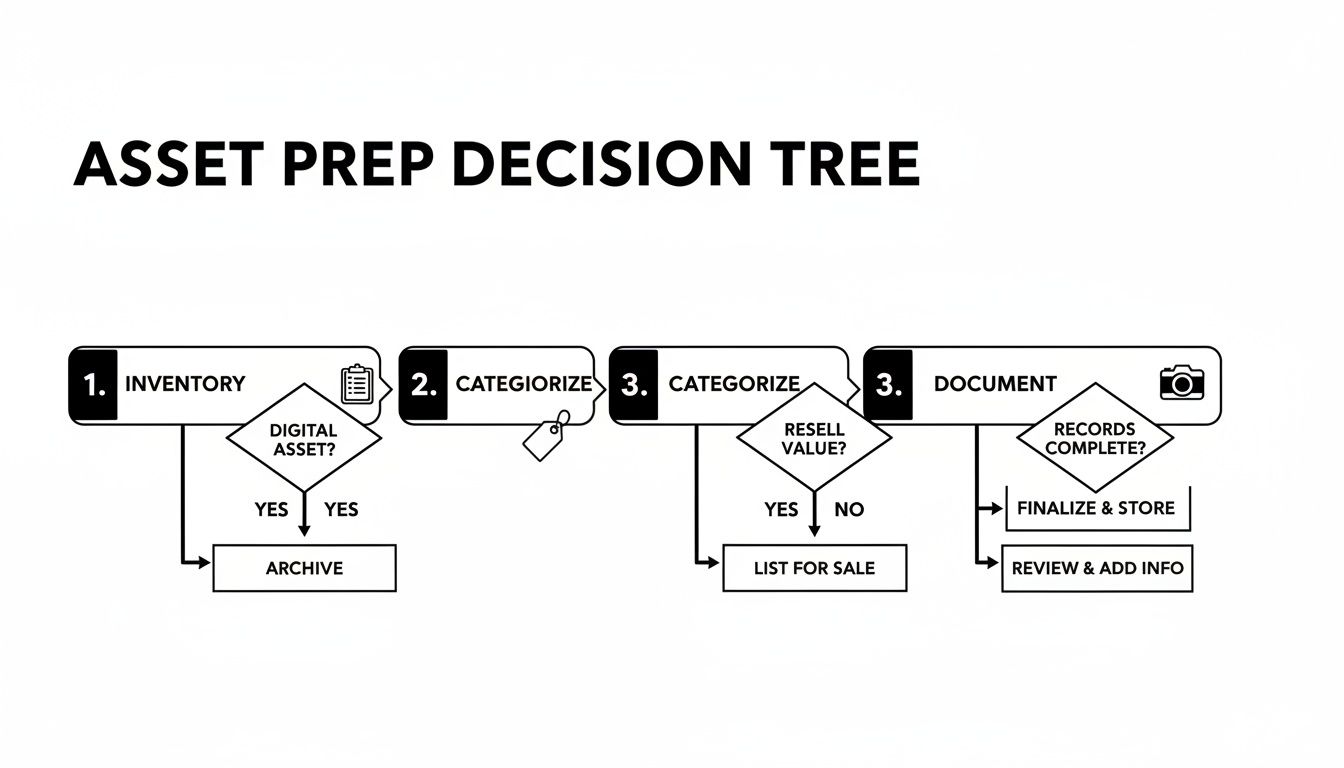
As the chart demonstrates, a methodical approach—inventory, categorization, documentation—is the foundation for choosing the optimal path for your assets.
On-Site Hard Drive Shredding: The Gold Standard for Security
For organizations in highly regulated sectors such as healthcare (HIPAA), finance (GLBA), or government contracting, on-site hard drive shredding is often the required standard. A mobile shredding vehicle is brought directly to your Georgia facility, allowing you and your team to witness the physical destruction of every hard drive, SSD, and data tape.
The process is transparent and final. There is no ambiguity and zero chance of data survival. Each drive is rendered into small, unrecoverable fragments, providing ultimate peace of mind and the strongest possible chain of custody.
This method is ideal for:
- Assets containing sensitive intellectual property or mission-critical corporate data.
- Meeting the strictest compliance mandates where data cannot leave your premises intact.
- Organizations requiring irrefutable, witnessed proof of destruction.
Off-Site Shredding: Secure and Cost-Effective
Off-site shredding provides the same level of complete physical destruction with different logistics. We securely transport your data-bearing devices from your location in locked, tamper-evident containers to our controlled facility in Smyrna, Georgia. Upon arrival, the devices are shredded under continuous video surveillance.
This is a practical and secure option for businesses that require certified physical destruction but do not need or have space for an on-site shredding vehicle. It is a highly efficient method for handling large volumes of retired media. While not witnessed firsthand, you receive a detailed Certificate of Data Destruction that validates the entire process and transfers liability.
Certified Data Wiping: Preserving Value While Ensuring Security
When IT assets retain functional value, physical destruction is not cost-effective. Certified data wiping (data sanitization) is the solution. We use specialized software to overwrite every sector of a storage device, rendering the original data forensically unrecoverable.
This is not a simple “delete” command. Our methods adhere to the rigorous standards of the Department of Defense (DoD 5220.22-M) and the National Institute of Standards and Technology (NIST 800-88). For a deeper technical overview, review our guide to secure data destruction methods.
The primary advantage of certified wiping is that it preserves the hard drive and the entire device for resale. This is our standard method for newer laptops, servers, and networking equipment that qualify for our IT Buyback program, returning value to your budget.
To aid in your decision, here is a comparison of our core data destruction services.
Comparing Data Destruction Services
This table outlines which service is best suited for different business needs, whether your priority is maximum security, cost-effectiveness, or asset value recovery.
| Service | Process | Best For | Key Benefit |
|---|---|---|---|
| On-Site Shredding | Mobile shred truck at your Georgia location physically destroys drives under your supervision. | Highly regulated industries (healthcare, finance); devices with mission-critical data. | Maximum security and absolute peace of mind with witnessed destruction. |
| Off-Site Shredding | Devices are securely transported to our facility and shredded under video surveillance. | Businesses needing certified destruction for large volumes without the need for on-site service. | Secure, cost-effective, and fully documented physical destruction. |
| Certified Wiping | Software-based overwriting of data to DoD & NIST standards, preserving the hardware for reuse. | Newer, functional assets with resale value (laptops, servers, networking gear). | Enables value recovery through remarketing while guaranteeing data erasure. |
Choosing the right partner and method is more than a compliance task; it is a direct contribution to a sustainable solution.
The e-waste crisis in the U.S. highlights the importance of responsible disposal. In 2023, the nation generated an estimated 6.9 million tons of e-waste, with recycling rates at only 11% for mobile phones and 40% for computers. By selecting the appropriate destruction method, Georgia businesses can securely protect their data while ensuring their obsolete technology does not contribute to this environmental problem.
Making the Logistics of Your IT Asset Pickup Effortless
Transporting your obsolete technology from your business location to our secure facility should be a seamless process. Whether you’re in downtown Atlanta or anywhere else in the contiguous U.S., our Beyond Surplus technology reuse Georgia program is designed for complete transparency and efficiency. It begins with clear communication to ensure our team arrives fully prepared for your specific needs.
The process is customized to your environment. A data center decommissioning requires different logistics than collecting laptops from a corporate office. One project might necessitate pallet jacks and server lifts, while another may only require security bins. Providing accurate details upfront ensures a smooth and secure pickup.
Scheduling Your Pickup in Georgia or Nationwide
To initiate the process, provide a general overview of the equipment you need removed. A detailed, serial-number-level inventory is not required at this stage.
Key information we need to get started:
- A General Asset List: e.g., “approximately 50 laptops, 10 servers, and a rack of networking gear.”
- Your Full Location Details: Complete address, including suite numbers, building name, and specific loading dock instructions.
- On-Site Contact Information: The name, email, and phone number of the point of contact for pickup day.
- Any Special Handling Needs: e.g., equipment located on a floor without an elevator access or requiring specialized tools for removal.
This initial information allows our logistics team to dispatch the appropriate vehicle and a sufficient number of technicians to complete the job safely and efficiently.
We Handle Specialized Environments
Logistics in controlled environments like data centers, hospitals, or laboratories require specialized expertise. For a data center decommissioning, we need to know your security protocols, floor protection requirements, and loading dock hours. We arrive with all necessary equipment, such as server lifts and anti-static materials, to de-install and pack your hardware without disrupting your live operations.
Similarly, for medical or lab equipment disposal, we coordinate with your facility managers to ensure our team adheres to all site-specific safety and access protocols. By discussing these needs in advance, we guarantee a seamless process that complies with your internal policies.
Peace of mind comes from a well-documented chain of custody. From the moment our team signs for the assets at your Georgia facility, every item is tracked until its final disposition, giving you a transparent and defensible record of its journey.
Convenient Mail-In and Drop-Off Options
For businesses with a small number of assets or located near our Smyrna, Georgia facility, we offer flexible alternatives to a scheduled pickup. Our mail-in program is a secure way to send devices like laptops, tablets, and mobile phones. We provide clear instructions to ensure your equipment is packed safely.
Local businesses can also drop off equipment directly at our facility. It’s an efficient way to manage IT asset disposal on your schedule. For more information, see our business guide to electronics drop-off locations. Both mail-in and drop-off services include the same secure data destruction and certified recycling processes, ensuring your assets are handled with the highest standards of care.
Turning Surplus IT Into Revenue
What if your end-of-life technology could be a revenue source instead of a cost? For many Georgia businesses, retired IT equipment is often viewed as a liability. However, with a strategic approach to Beyond Surplus technology reuse Georgia, these same assets can unlock significant hidden value.

Our IT Buyback Program is designed to transform the disposition process from an expense into a financial return, rewarding your organization for its technology investments. This is not just recycling; it is about recognizing the market value remaining in well-maintained, functional enterprise equipment.
The circular economy model is gaining momentum because it is a smarter, more sustainable, and financially sound approach to resource management.
Identifying High-Value Assets
The key to a successful buyback is identifying which assets command the highest prices on the secondary market. The most sought-after categories consistently include:
- Recent-Generation Servers: Enterprise-grade servers from manufacturers like Dell, HP, and Cisco that are less than five years old.
- Networking Gear: Switches, routers, and firewalls from brands such as Cisco, Juniper, and Arista.
- Enterprise Laptops and Desktops: Bulk quantities of business-class laptops (e.g., Dell Latitudes, Lenovo ThinkPads) in good working condition.
- Data Center Components: Storage arrays (SANs), memory modules, and high-performance processors.
The value of these assets depends on their age, condition, configuration, and current market demand. By focusing on these categories, your business can achieve the best possible financial return.
The Professional Evaluation Process
Upon receiving your equipment, our technicians conduct a meticulous evaluation to determine its precise value. This is a comprehensive assessment of the hardware’s functionality and specifications.
First, every asset is tested to ensure all components are operational. We run diagnostics on CPUs, memory, storage drives, and network interfaces. Next, we grade the equipment based on its cosmetic condition. Finally, we appraise the asset based on its exact configuration and current secondary market value. This data-driven approach ensures a fair and accurate offer. For more details, explore our IT equipment buy back services.
The goal of our evaluation is to unlock the maximum possible value for you. A thorough, professional appraisal ensures that your return is based on real-world market data, not guesswork.
Maximizing Your Financial Return
Businesses can take practical steps to increase the buyback value of their surplus IT assets. Maintaining equipment in good cosmetic condition throughout its lifecycle makes a significant difference. Providing complete and accurate specifications when requesting a quote allows us to provide a more precise initial offer. Including original accessories like power cords and rack mounts also adds to the overall value.
This proactive approach not only enhances your revenue but also supports a sustainable, circular economy—a win for your budget and the environment.
This model is part of a growing industry. The U.S. electronic goods recycling sector is projected to reach a market size of $27.7 billion in 2025, growing at a 4.8% CAGR. This growth is driven by corporate demand for sustainable IT solutions that mitigate risk, as data breaches from improper disposal cost companies an average of $4.45 million per incident. Discover more insights about the electronics recycling industry at ibisworld.com. By participating in a buyback program, your organization actively contributes to this positive trend.
Common Questions About Technology Reuse In Georgia
When Georgia businesses explore professional IT asset disposition, several common questions arise concerning logistics, data security, compliance, and costs. We have compiled answers to the most frequent inquiries to help you build a secure and effective technology reuse strategy.
What Types Of Business Equipment Does Beyond Surplus Accept?
We specialize in the full range of commercial-grade IT and electronic equipment. Our services are tailored for the demanding needs of modern businesses, not residential electronics.
We routinely handle equipment including:
- Data Center Hardware: Servers, storage area networks (SANs), networking switches, routers, and associated rack infrastructure.
- Corporate IT Equipment: Laptops, desktops, monitors, docking stations, and VoIP phones.
- Specialized Electronics: Medical equipment, laboratory instruments, and telecommunications systems.
For unique or proprietary equipment, please contact us directly to ensure our Beyond Surplus technology reuse Georgia services are the right fit for your needs.
How Do You Guarantee Compliance With Regulations?
Compliance is central to our operations. We utilize a documented, auditable process to ensure your organization meets or exceeds the requirements of regulations like the FTC Disposal Rule and industry mandates such as HIPAA.
Upon project completion, we provide official documentation as proof of compliance, including:
- A Certificate of Data Destruction: This document certifies that every data-bearing device was sanitized or destroyed according to NIST 800-88 and DoD 5220.22-M standards, with serial numbers listed for a complete audit trail.
- A Certificate of Recycling: This confirms that any non-remarketable equipment was processed in an environmentally responsible manner, adhering to all federal, state, and local regulations, and guarantees no hazardous e-waste from your project entered a landfill.
These certificates are vital for your records, legally transferring liability and satisfying any audit requirements.
Choosing a certified ITAD partner is a direct investment in risk management. The documentation we provide is your definitive proof that you performed the necessary due diligence to protect your company’s data and meet your environmental obligations.
What Are The Costs For Your ITAD Services In Georgia?
There is no one-size-fits-all pricing, as each IT disposition project is unique. The final cost depends on the type and volume of equipment, logistics, and selected data destruction services. However, for many businesses, the process can be cost-neutral or even profitable.
If you have valuable, newer IT assets—such as recent-generation servers, networking gear, or laptops—our IT Buyback Program can often offset or exceed the service costs, resulting in a payment to your company. For projects focused solely on recycling and data destruction of older, non-valued assets, service fees may apply.
We provide a transparent, customized quote upfront, so you know exactly what to expect in terms of costs or returns before proceeding.
My Business Has Multiple Locations. Can You Help?
Yes. Headquartered in the Atlanta metro area, our reach is nationwide. Beyond Surplus provides pickup and logistics services for commercial and enterprise clients across the country. Our network is built to manage complex, multi-site projects anywhere in the contiguous United States.
Whether you have a single branch office in Georgia or data centers across multiple states, we coordinate all logistics. Our team arranges for secure, timely pickups from each location and consolidates the assets for processing at our main facility. This ensures consistent security, documentation, and quality of service across your entire organization.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. Learn more about our services at https://www.beyondsurplus.com.



