A successful data center migration is a feat of meticulous planning and flawless execution, not a simple 'lift and shift.' It's an opportunity to optimize, secure, and modernize your infrastructure. However, without a structured approach, it can quickly devolve into a high-stakes puzzle of downtime, data loss, and budget overruns. This definitive data center migration checklist breaks down the entire process into 10 manageable, sequential phases, ensuring no critical step is overlooked.
From initial stakeholder alignment and detailed infrastructure mapping to the final, secure decommissioning of legacy assets, this guide provides the actionable steps needed to navigate the complexity. Whether you are moving to a colocation facility or undertaking a cloud transition, having a clear roadmap is non-negotiable. To lay a strong foundation for your journey, consider consulting a comprehensive guide on how to migrate to cloud for specialized strategies.
Our checklist covers the complete project lifecycle, including:
- Assessment and Planning: Setting clear objectives and defining scope.
- Infrastructure Mapping: Understanding every dependency and connection.
- Execution and Validation: Ensuring a seamless cutover with minimal disruption.
- Post-Migration Support: Finalizing documentation and optimizing performance.
We will explore each phase in-depth, providing critical considerations and expert tips to mitigate risk and ensure your transition is a strategic success rather than an operational headache. This structured plan transforms a monumental task into a clear, achievable project, from initial pilot programs to final IT asset disposition with a certified partner.
1. Phase 1: Comprehensive Assessment and Strategic Planning
A successful data center migration begins long before the first server is unplugged. Phase 1 is the foundational bedrock of the entire project, focusing on a meticulous evaluation of your current environment to build a data-driven strategy. This initial step is non-negotiable for mitigating risks and ensuring the migration aligns perfectly with overarching business goals. The primary objective is to move from assumptions to absolutes by creating a comprehensive inventory and understanding every technical and business requirement.
What This Phase Involves
This phase systematically catalogues every component of your existing infrastructure. It goes beyond a simple hardware list to map out applications, databases, inter-dependencies, and network configurations. By understanding how different elements interact, you can prevent unexpected outages and performance degradation post-migration.
The assessment also establishes crucial baseline performance metrics for servers, storage, and network throughput. These benchmarks are vital for validating success later in the project, providing concrete data to confirm that the new environment meets or exceeds the performance of the old one. This detailed inventory is a critical first step in a larger IT asset management lifecycle, setting the stage for eventual secure disposition.
Implementation and Key Actions
To execute this phase effectively, project managers should:
- Deploy Automated Discovery Tools: Manually cataloging a complex environment is prone to error. Tools like Cloudscape, Turbonomic, or native cloud assessment services (e.g., AWS Migration Evaluator, Azure Migrate) can automate the discovery process, mapping dependencies and gathering performance data with high accuracy.
- Adopt a Migration Framework: Instead of reinventing the wheel, use a proven methodology. Gartner's "6 R's" of migration (Rehost, Replatform, Repurchase, Refactor, Retire, Retain) provides a strategic framework to decide the best path for each application.
- Engage All Stakeholders: A migration is not just an IT project. Involve department heads and business leaders early to understand their critical applications, performance expectations, and acceptable downtime windows. This collaboration ensures the final plan supports business operations, not just technical requirements.
2. Stakeholder Communication and Change Management
A data center migration is as much a people project as it is a technology project. Phase 2 focuses on establishing robust communication channels and a structured change management process. Neglecting this crucial step can lead to resistance, confusion, and misalignment, jeopardizing the project's timeline and ultimate success. The primary objective here is to secure buy-in, manage expectations across all levels of the organization, and ensure a smooth transition for everyone impacted by the move.
What This Phase Involves
This phase involves creating and executing a formal communication plan that addresses every stakeholder group, from C-suite executives to end-users. It goes beyond simple email updates to include a multi-faceted strategy for conveying information, gathering feedback, and managing the human side of technological change. A key component is mapping out who needs to know what, when they need to know it, and the best channel to deliver that message.
Effective change management, guided by frameworks like the Prosci ADKAR Model, ensures that employees are not only aware of the change but are also prepared and supported through it. This involves identifying potential points of friction, providing necessary training, and celebrating milestones to maintain positive momentum. This proactive approach is a core element of a comprehensive data center migration checklist, transforming potential obstacles into engaged advocates for the project.
Implementation and Key Actions
To execute this phase effectively, project leaders should:
- Establish a Communication Matrix: Develop a detailed matrix that identifies all stakeholder groups (e.g., IT infrastructure team, application owners, business unit leaders, end-users), the key messages for each, the communication frequency, the delivery channel (email, town hall, wiki), and the owner of each communication task.
- Create Role-Specific Messaging: Avoid a one-size-fits-all approach. Executives need concise updates on budget and business impact, while technical teams require detailed information on schedules and procedures. Tailoring messages ensures they are relevant and impactful for each audience.
- Form a Migration "War Room": Set up a dedicated physical or virtual space for the core migration team. This central hub facilitates real-time decision-making, rapid issue resolution, and provides a single source of truth for all project-related updates during critical migration windows.
3. Detailed Infrastructure Mapping and Dependency Analysis
After strategic planning, the next critical step is to create a granular, high-fidelity blueprint of your entire IT ecosystem. This phase moves beyond a simple inventory to build a comprehensive map of all systems, applications, data flows, and their intricate interdependencies. An accurate dependency map is the single most important technical document in a data center migration checklist, serving as the definitive guide for sequencing moves, preventing cascading failures, and identifying potential performance bottlenecks before they occur.
What This Phase Involves
This phase is about visualizing the invisible connections that power your business. It involves tracing how data travels between servers, storage arrays, and network switches, and understanding which applications rely on specific databases or middleware to function. The goal is to answer critical questions like, "If we move this server, what three other applications will be impacted?" or "What is the complete chain of dependencies for our primary ERP system?"
This detailed mapping also extends to disaster recovery and backup systems, ensuring that these critical safeguards are accounted for in the migration plan. Failing to map these dependencies is a primary cause of unexpected downtime and chaotic troubleshooting during the migration cutover. This process also directly informs the sequence of events during the final move, which is a key component of a successful data center decommissioning strategy.
Implementation and Key Actions
To execute this phase with precision, project leaders should:
- Leverage Automated Mapping Tools: Manually mapping a modern, complex environment is nearly impossible. Utilize specialized tools like ServiceNow IT Operations Management, BMC Discovery, or Splunk to automatically discover and visualize application and infrastructure dependencies, creating an accurate and dynamic map.
- Establish a CMDB as the Source of Truth: Use a Configuration Management Database (CMDB) to store and manage all discovered configuration items (CIs) and their relationships. This provides a centralized, reliable repository that the entire migration team can reference, ensuring consistency and accuracy.
- Validate Maps with Application Owners: While automated tools are powerful, they must be validated by human expertise. Schedule review sessions with application owners and business stakeholders to confirm the accuracy of the dependency maps, uncover undocumented connections, and verify business criticality ratings for each component.
4. Security and Compliance Assessment
A data center migration is more than just a logistical or technical challenge; it is a critical security event that must be managed with extreme diligence. This phase focuses on a rigorous evaluation of all security and regulatory obligations tied to your data. Failing to address compliance requirements like HIPAA, GDPR, or SOC 2 from the outset can lead to severe financial penalties, reputational damage, and legal liabilities. The goal is to ensure the new environment not only maintains but enhances your security posture.
What This Phase Involves
This assessment is a deep dive into the policies, procedures, and technical controls that protect your data. It involves classifying data based on sensitivity, defining encryption standards for data both in-transit and at-rest, and mapping out access control policies for the target environment. The process requires a thorough review of industry-specific regulations and contractual obligations to ensure the migration plan is inherently compliant.
Furthermore, this phase establishes a clear framework for maintaining audit trails throughout the project. Every action, from data transfer to equipment decommissioning, must be logged and auditable. This is especially critical for regulated industries where proving a secure chain of custody is non-negotiable. It also extends to the physical security of assets during transit and the certified destruction of data on retired media, a process guided by standards like those outlined in NIST Special Publication 800-88.
Implementation and Key Actions
To integrate security and compliance into your data center migration checklist, project leaders should:
- Engage Compliance and Legal Teams Early: Involve your compliance officers, legal counsel, and security teams from day one. Their input is essential for identifying all applicable regulations and translating them into technical requirements for the migration team.
- Implement a Zero-Trust Security Model: Treat the migration as an opportunity to modernize your security architecture. Adopt a zero-trust approach, which assumes no implicit trust and continuously validates every stage of digital interaction. This means verifying user identities, device integrity, and access privileges before granting access to resources in the new environment.
- Utilize Compliance Automation and Scanning Tools: Leverage tools that continuously scan for compliance gaps and security misconfigurations in the target environment. Services like AWS Compliance Center or Azure Security and Compliance Blueprints provide pre-built, auditable frameworks to accelerate adherence to standards like ISO 27001 and SOC 2.
5. Phase 5: Establish Pilot Program and Testing Strategy
Attempting a full-scale, "big bang" data center migration without preliminary validation is a high-risk gamble. Phase 5 introduces a controlled, methodical approach by establishing a pilot program. This crucial step involves migrating a small, non-critical but representative subset of applications and infrastructure to test your entire process from end to end. The goal is to move from theoretical plans to practical, proven procedures, identifying and resolving issues in a low-impact environment before the main event.
What This Phase Involves
This phase is a dress rehearsal for the full migration. It validates your team's readiness, the accuracy of your discovery data, the effectiveness of your migration tools, and the performance of the target environment. By isolating a small workload, you can measure its performance before and after the move, test rollback procedures if something goes wrong, and gather real-world data on network latency, application response times, and system dependencies.
The pilot program serves as a proof of concept, building confidence among stakeholders and providing invaluable lessons learned. For instance, a financial services firm might pilot a development or QA environment for a trading platform, or a healthcare provider could migrate a non-essential administrative application before touching patient record systems. This step in your data center migration checklist is essential for refining your methodology and training the migration team.
Implementation and Key Actions
To execute a successful pilot migration, project managers should:
- Select a Representative Pilot Workload: Choose an application or system that is non-critical but mirrors the complexity of more important systems. It should have similar dependencies, data volumes, and user interaction patterns to provide meaningful insights.
- Define Clear Success Metrics: Before starting, establish specific, measurable criteria for success. This includes performance benchmarks (e.g., transaction speeds must be within 5% of the baseline), successful completion of user acceptance testing (UAT), and a verified successful rollback test.
- Execute and Monitor Rigorously: Run the pilot migration exactly as you would a production move. Involve end-users in the testing phase to validate functionality and performance from their perspective. Monitor the pilot environment closely for at least two to four weeks post-migration to detect any long-term or intermittent issues.
6. Phase 6: Infrastructure and Environment Provisioning
With a detailed plan in hand, this phase transitions from strategy to construction. Infrastructure and Environment Provisioning is the critical step where the target data center or cloud environment is actively built and configured. This involves setting up everything from the physical racks and power distribution units to the virtual networks and cloud storage buckets. The goal is to create a stable, secure, and performant new home for your applications that is ready to receive the migrated workloads.
What This Phase Involves
This stage involves translating the architectural designs and resource requirements identified in the planning phases into a tangible, functioning environment. It’s where abstract plans for network subnets, virtual machine sizes, and storage tiers become reality. The process requires precise configuration of all infrastructure components, including compute resources, network security groups, firewalls, load balancers, and monitoring tools.
A core principle of modern provisioning is automation. By codifying the infrastructure setup, you create a repeatable, consistent, and error-free process that can be version-controlled and audited. When provisioning a physical data center, ensuring the reliability of core electrical systems is paramount. You should consider services like commercial switch gear infrared testing and upgrades to validate the integrity of your power distribution before bringing critical systems online. This proactive validation is a key part of any successful data center migration checklist.
Implementation and Key Actions
To effectively provision the new environment, project teams should:
- Use Infrastructure-as-Code (IaC): Leverage tools like Terraform, AWS CloudFormation, or Azure Resource Manager (ARM) templates to define and deploy your infrastructure. This approach ensures consistency between development, testing, and production environments and simplifies future modifications.
- Implement a Robust Tagging Strategy: From day one, apply a comprehensive and consistent tagging strategy to all resources. Tags for environment, cost center, application owner, and data sensitivity are crucial for effective cost management, security auditing, and operational automation.
- Establish Baselines and Monitoring Immediately: Deploy monitoring and observability tools as part of the initial provisioning, not as an afterthought. Establish performance baselines for the new, empty environment to accurately measure the impact of migrated workloads and quickly identify performance bottlenecks.
7. Data Migration Execution and Validation
With the strategy set and logistics planned, this phase marks the critical moment of truth: the actual transfer of data. This step is where the digital heart of the organization is moved from its old home to the new one. The focus here is on executing the data transfer with precision, speed, and, most importantly, integrity. A flawed data migration can corrupt information, cause extended downtime, and undermine the entire project's business case.
This process involves using specialized tools and proven methodologies to copy data from the source to the target environment. It's not a simple copy-paste operation; it requires continuous synchronization, robust validation checks, and a mechanism for ensuring zero data loss. The success of this phase is measured by the accuracy and completeness of the data in the new system, verified against the original source.
What This Phase Involves
This phase centers on the technical execution of moving petabytes of data while minimizing business disruption. It includes selecting the right migration tool for the job, whether it's for block-level replication, database synchronization, or large-scale file transfers. The process is often broken into an initial bulk data sync followed by incremental updates (delta syncs) to capture changes made during the migration window.
Validation is a non-negotiable component. Immediately after the transfer, data integrity must be confirmed using techniques like checksums, hash comparisons, and record-count reconciliation. This step proves that the data at the destination is an exact, uncorrupted replica of the data from the source. This meticulous verification is a core part of a responsible data management lifecycle, which also includes the final, secure disposal of the source data.
Implementation and Key Actions
To ensure a smooth and accurate data transfer, project leaders should:
- Use Specialized Migration Tools: Leverage enterprise-grade tools designed for specific workloads. For cloud migrations, services like AWS DataSync or Azure Data Migration Service offer optimized, high-speed transfers. For on-premise or hybrid scenarios, solutions like Zerto or Rubrik provide continuous replication and near-zero RPOs (Recovery Point Objectives).
- Perform a Pilot Migration: Before the main event, conduct a full migration and validation test with a representative subset of data. This pilot run helps identify potential network bottlenecks, tool configuration issues, and validation script errors in a low-risk environment.
- Implement Post-Migration Validation Scripts: Automate the validation process as much as possible. Develop scripts that can quickly perform checksums on files, run
COUNT(*)queries on database tables, and compare record totals between the source and target systems to flag any discrepancies immediately.
8. Application Cutover and Validation
This is the climactic phase of the data center migration checklist where the transition becomes reality. Application cutover is the meticulously planned process of switching from the source production environment to the new target environment. It is immediately followed by validation, a critical step to confirm that all applications, services, and data are functioning as expected and meeting performance benchmarks. This phase is the ultimate test of the planning and preparation stages, determining the immediate success of the migration project.
What This Phase Involves
This phase involves executing a detailed, step-by-step "runbook" that outlines every action required for the switch. This includes final data synchronization, DNS changes, re-routing network traffic, and shutting down old systems. Once the switch is complete, validation begins. This isn't just a simple check to see if an application is "on"; it involves comprehensive functional testing, performance monitoring, and user acceptance testing (UAT) to ensure the end-user experience is seamless and business operations can continue without disruption.
A successful cutover relies on precise timing and coordination across multiple teams, from network engineers to application owners and business stakeholders. It's a high-stakes moment where any deviation from the plan can lead to extended downtime or data integrity issues, making a pre-rehearsed plan essential.
Implementation and Key Actions
To execute a smooth and successful application cutover and validation, project managers should:
- Establish a Cutover Command Center: Designate a physical or virtual command center where all key decision-makers, technical leads, and stakeholders are present. This centralizes communication, enabling rapid decision-making and troubleshooting during the cutover window.
- Create and Rehearse a Detailed Runbook: Develop a minute-by-minute script for the cutover process, including specific commands, expected outcomes, and rollback triggers. Conduct a full dress rehearsal one to two weeks prior to the actual event to identify and resolve any gaps in the plan.
- Implement Phased or "Blue-Green" Cutovers: For complex environments like major e-commerce platforms or banking systems, avoid a "big bang" approach. A phased cutover moves services or user groups incrementally, minimizing the blast radius of any potential issues. A blue-green deployment keeps the old environment running in parallel, allowing for instantaneous rollback if validation fails.
9. Performance Optimization and Tuning
The work isn't over once the final server is live in the new environment. Phase 9 is where the migration’s success is truly forged, focusing on the meticulous process of fine-tuning systems to meet or exceed pre-migration performance benchmarks. This critical stage transitions the project from a logistical success to an operational one, ensuring that applications are not just running, but running optimally. The objective is to proactively identify and resolve bottlenecks in the new infrastructure before they impact end-users and business operations.
What This Phase Involves
This phase is a deep-dive into post-migration operational data. It involves analyzing real-world usage patterns to optimize everything from database queries and network configurations to storage access and virtual machine resource allocation. By comparing live performance against the baseline metrics established in Phase 1, you can systematically address any performance degradation and capitalize on the capabilities of the new hardware or cloud platform.
Tools like Dynatrace, New Relic, and Datadog become invaluable here, providing granular visibility into application performance. For instance, analyzing slow query logs in a database or leveraging execution plans can pinpoint inefficient code that needs refactoring. Similarly, implementing a Content Delivery Network (CDN) for web applications or fine-tuning Elasticsearch for search functionality are concrete optimization actions that ensure the new data center delivers superior performance.
Implementation and Key Actions
To execute this phase effectively, project managers should:
- Leverage Application Performance Monitoring (APM) Tools: Continuously use APM tools to monitor application health in the new environment. These platforms provide real-time insights into response times, error rates, and resource utilization, allowing you to quickly identify and diagnose performance issues before they escalate.
- Right-Size and Auto-Scale Resources: Analyze actual usage data to right-size virtual machine instances and other cloud resources. Over-provisioning is costly, while under-provisioning kills performance. Implement auto-scaling policies to dynamically adjust resources based on demand, ensuring both cost-efficiency and optimal user experience.
- Implement Caching Strategies: Deploy caching layers using technologies like Redis or Memcached to reduce latency and decrease the load on backend systems. Caching frequently accessed data closer to the user or application is one of the most effective ways to boost performance for read-heavy workloads.
10. Documentation, Knowledge Transfer, and Post-Migration Support
A data center migration is not complete when the final server goes live. Phase 10 is the critical handoff that ensures the long-term operational success and sustainability of the new environment. This stage focuses on transforming project-specific knowledge into permanent, accessible documentation and empowering the day-to-day operations teams. Neglecting this final step can lead to prolonged troubleshooting, increased support tickets, and an inability to manage the new infrastructure effectively, negating many of the migration's benefits.
What This Phase Involves
This phase is about creating a comprehensive and lasting record of the new environment. It involves documenting everything from network diagrams and configuration details to operational procedures and escalation paths. The goal is to equip the IT operations and support staff with all the information they need to manage, maintain, and troubleshoot the infrastructure without relying on the original migration team.
Knowledge transfer sessions are a core component, moving beyond static documents to provide hands-on training and walkthroughs for the teams who will inherit the system. This ensures they understand not just the "what" but the "why" behind design and configuration choices. A well-executed knowledge transfer is also the final step in the asset lifecycle before an old system is fully retired, ensuring all relevant data and procedures are captured before final disposition.
Implementation and Key Actions
To ensure a smooth transition to a sustainable operational state, project managers should:
- Establish a Centralized Knowledge Base: Use platforms like Confluence or ServiceNow to create a single source of truth for all documentation. Assign specific "documentation owners" before the migration concludes to ensure accountability for keeping runbooks, diagrams, and procedures up-to-date.
- Automate and Standardize Runbooks: For common operational tasks and incident responses, leverage automation tools like Ansible or PowerShell. Documented, automated runbooks reduce human error, speed up resolution times, and provide a consistent method for handling routine issues.
- Schedule Overlapping Handoff Periods: Implement a structured knowledge transfer period of two to four weeks where the migration team and the operations team work together. This allows for real-world, hands-on training and Q&A sessions, ensuring the operations team is fully confident before taking complete ownership of the new environment.
Data Center Migration: 10-Step Checklist Comparison
| Task | Complexity 🔄 | Resource Requirements ⚡ | Expected Outcomes ⭐ / 📊 | Ideal Use Cases 💡 |
|---|---|---|---|---|
| Assessment and Planning | High 🔄 — thorough, time-consuming | Medium–High ⚡ — discovery tools, SMEs, stakeholder time | ⭐⭐⭐⭐ — accurate timelines, fewer surprises; 📊 improved budgeting & risk reduction | Pre-migration scoping, large/heterogeneous environments |
| Stakeholder Communication and Change Management | Medium–High 🔄 — organizational coordination | Medium ⚡ — comms team, training, engagement activities | ⭐⭐⭐⭐ — higher adoption & lower resistance; 📊 better visibility | Organization-wide migrations, user-impacting changes |
| Detailed Infrastructure Mapping and Dependency Analysis | Very High 🔄 — deep technical mapping | High ⚡ — automated discovery tools, architects, time | ⭐⭐⭐⭐⭐ — precise dependency mapping; 📊 prevents downtime & sequencing errors | Complex integrations, legacy-heavy environments |
| Security and Compliance Assessment | High 🔄 — regulatory complexity | Medium–High ⚡ — compliance experts, scanning tools | ⭐⭐⭐⭐ — regulatory continuity & reduced risk; 📊 maintains trust | Regulated industries (healthcare, finance, GDPR/SOC2 scopes) |
| Establish Pilot Program and Testing Strategy | Medium 🔄 — controlled experimentation | Medium ⚡ — test environments, users, validation tools | ⭐⭐⭐⭐ — validates processes & uncovers issues; 📊 reduces large-scale failures | Phased rollouts, proof-of-concept validation |
| Infrastructure and Environment Provisioning | Medium–High 🔄 — architecture and IaC work | High ⚡ — IaC tooling, cloud resources, networking | ⭐⭐⭐⭐ — reproducible, scalable target environments; 📊 faster deployments | Cloud adoption, large-scale new deployments |
| Data Migration Execution and Validation | High 🔄 — complex scheduling & integrity checks | High ⚡ — migration tools, bandwidth, monitoring | ⭐⭐⭐⭐ — accurate transfers with minimal loss; 📊 measurable data integrity | Large datasets, low-downtime or continuous-replication needs |
| Application Cutover and Validation | Very High 🔄 — high-risk, time-bound activity | High ⚡ — runbooks, command center, cross-team coordination | ⭐⭐⭐⭐ — smooth production switch; 📊 quick rollback and incident containment | Final production cutovers (ERP, e-commerce, banking) |
| Performance Optimization and Tuning | Medium 🔄 — iterative adjustments | Medium ⚡ — APM tools, DB/network tuning expertise | ⭐⭐⭐⭐ — improved UX and cost-efficiency; 📊 better resource utilization | Post-migration stabilization, high-traffic applications |
| Documentation, Knowledge Transfer, and Post-Migration Support | Medium 🔄 — disciplined delivery | Medium ⚡ — authors, trainers, knowledge platforms | ⭐⭐⭐⭐ — operational independence; 📊 faster support resolution | Handover to ops teams, long-term maintenance and upgrades |
Completing Your Migration: Secure Decommissioning and Next Steps
Executing a data center migration is a monumental undertaking that tests an organization's planning, technical execution, and resilience. As we've detailed throughout this comprehensive data center migration checklist, success is not a single event but the culmination of meticulously managed phases. From initial assessment and stakeholder alignment to the final cutover and performance tuning, each step builds upon the last, forming a chain of dependencies where a single weak link can jeopardize the entire project.
The journey requires a strategic blend of high-level vision and granular detail. You've mapped every server, documented every dependency, and established robust testing protocols. You’ve navigated the complexities of provisioning a new environment, executing the physical or logical move, and validating every application to ensure business continuity. This process is far more than just moving hardware; it's a strategic business transformation that, when done right, delivers enhanced performance, scalability, and security for years to come.
However, the migration's final act is often where the most critical security risks emerge. The journey isn't truly over once the new systems are live. The legacy environment, now dormant but still containing sensitive corporate and customer data, represents a significant liability.
Key Takeaways from Your Migration Journey
Reflecting on the entire process, several core principles stand out as non-negotiable for a successful migration:
- Planning is Paramount: The most successful migrations are won long before the first server is moved. An exhaustive discovery and planning phase, accounting for every dependency, compliance requirement, and potential risk, is the single greatest predictor of a smooth transition.
- Communication is a Constant: Keeping all stakeholders, from the C-suite to end-users, informed and engaged is crucial. A well-executed communication plan prevents surprises, manages expectations, and fosters a collaborative environment.
- Testing is Not Optional: Rigorous, multi-phased testing, from pilot programs to full-scale validation, is your only guarantee that applications will perform as expected post-migration. Cutting corners here inevitably leads to costly downtime and frantic post-launch fixes.
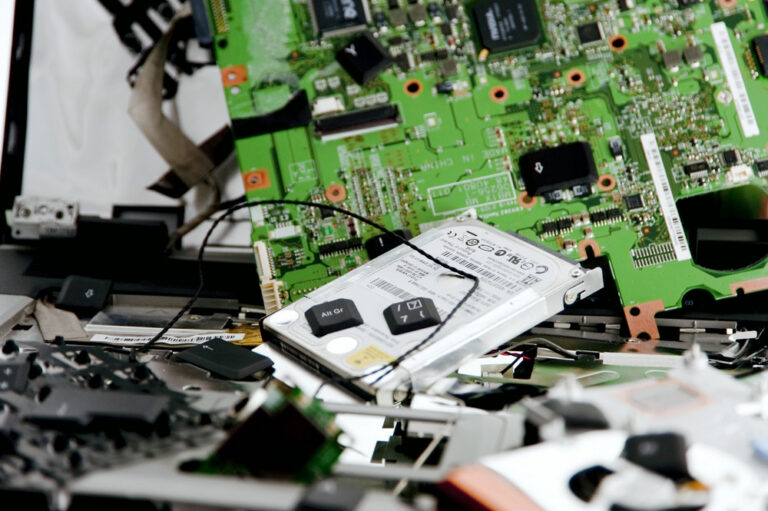
The Final, Critical Step: Secure Decommissioning
With your new data center operational, the spotlight shifts to the old one. The final, and arguably most critical, item on your data center migration checklist is the secure and compliant decommissioning of legacy assets. Leaving old servers, storage arrays, and networking gear in a closet or sending them to an uncertified recycler is a direct invitation for a data breach.
This final phase demands the same level of professional diligence as the migration itself. It involves:
- Certified Data Destruction: Ensuring all data is irretrievably destroyed using methods compliant with standards like NIST 800-88.
- Compliant E-Waste Recycling: Partnering with a certified electronics recycler to ensure hardware is disposed of in an environmentally responsible manner, adhering to R2, e-Stewards, and other regulations.
- Chain of Custody Documentation: Receiving detailed certificates of data destruction and recycling to satisfy internal audits and prove regulatory compliance.
Failing to properly manage this final step can undo all the hard work of a successful migration, exposing your organization to severe financial penalties, reputational damage, and legal liability. This is not a task for an internal team to handle on the side; it requires a specialized partner.
By meticulously following a comprehensive checklist and capping off the project with a secure IT Asset Disposition (ITAD) strategy, you transform a high-risk project into a strategic success. You haven't just moved a data center; you've elevated your infrastructure, fortified your security posture, and ensured your organization is poised for future growth, all while responsibly managing the entire asset lifecycle.
A successful data center migration is only complete when the legacy assets are securely and compliantly handled. Beyond Surplus provides certified data center decommissioning and ITAD services across the United States, ensuring your sensitive data is destroyed and your old equipment is recycled responsibly. Finalize your data center migration checklist with a partner you can trust by visiting Beyond Surplus to schedule a consultation today.