Data Security
Data Security is at the core of services provided by Beyond Surplus. This service is available to all businesses and residential customers. For Businesses See: Hard Drive Shredding & Disposal Services
Recycling hard drives is one of the most important steps we can take to protect our environment and conserve resources. This article will discuss the importance of hard drive recycling and provide tips for safely disposing of old drives. Hard drives are one of the most important components of modern computers and electronic devices.
Hard Drive Recycling Services
Harddrive recycling is a great way to help protect the environment and ensure the safety of your data. Not only does it help protect the environment, but it also helps to keep your data safe and secure. Beyond Surplus has the capacity to securely wipe or shred hard drives at the customer’s premises with a mobile hard drive shredder or offsite at our facility in Smyrna. Contact us for a no-obligation data destruction and hard drive shredding consultation.

Data Security, Hard Drive Shredding & Data Destruction Service
When making the decision to recycle unwanted PCs, data security and privacy is extremely important. Even a non-functional PC still has a hard drive full of data inside it. For businesses, this can include sensitive customer or client data and other business data. Home PCs usually contain personal data, financial data, passwords, and other sensitive material.
Whether you’re sending computers to the recycling center for destructive recycling or donating them to charity, it’s essential that all sensitive data be removed completely, Beyond Surplus can handle all your data destruction requirements.Whether you’re sending computers to the recycling center for destructive recycling or donating them to charity, it’s essential that all sensitive data be removed completely, Beyond Surplus can handle all your data destruction requirements.
- Keep your company compliant. Our data destruction methods are compliant with HIPAA, Gramm-Leach-Bliley Act, Sarbanes-Oxley Act, The Patriot Act, Identity Theft and Assumption Deterrence Act, and others. See Hipaa FAQ
- Our Data destruction methods render all media “unusable and/or inaccessible”.
- Private security service for the facility.
- All hard drives and other storage media are securely locked under 24/7 video surveillance at the Beyond Surplus Secure Facility until destroyed.
Data Security & Secure Data Destruction
All Electronic equipment is assessed for remarketing potential in accordance with contractual agreements. Prior to remarketing, proprietary information will be removed from reusable equipment according to NIST SP 800-88 Guidelines for Media Sanitization, and contractual obligations.
Equipment failing to meet reuse standards, obsolete or not contractually permitted to be remarketed, will be completely destroyed by de-manufacture and or physical destruction. We also recommend that you wipe or reset any phones, pda’s, tablets, enterprise routers, switches and VPN firewalls before recycling. We offer various data destruction options based on your specific needs.
The Benefits of Harddrive Recycling
“Harddrive recycling” is the process of disassembling hard drives and recovering the components for subsequent reuse in other systems. It is a growing practice as more and more computer systems are discarded and replaced with newer models.
E-waste” – the waste generated by electronic devices – has become a growing problem in the modern world. As more and more electronic devices are used, discarded, and replaced, the amount of e-waste has grown exponentially. One of the most common components of e-waste is the hard disk drive (HDD).
Data Security Service #1: Secure Hard Drive Wipe (Free)

By Default for Every Item processed by Beyond Surplus we will thoroughly inspect every item and protect your Data by removing Asset Tags, Stickers and Identifying marks from each unit (Sanitize). During this initial Inspection stage every drive is wiped using a Department of Defense Compliant erasure program free of charge.
We offer Free hard drive wiping using the DoD 5220.22-M 3 Pass data sanitization methods that will prevent all software-based file recovery methods on all hard drives picked up or dropped off at our warehouse. All hard drives & storage devices deemed to be too old or non-functional will be shredded or otherwise physically destroyed according to NIST SP 800-88 Guidelines for Media Sanitization at no cost to the customer.
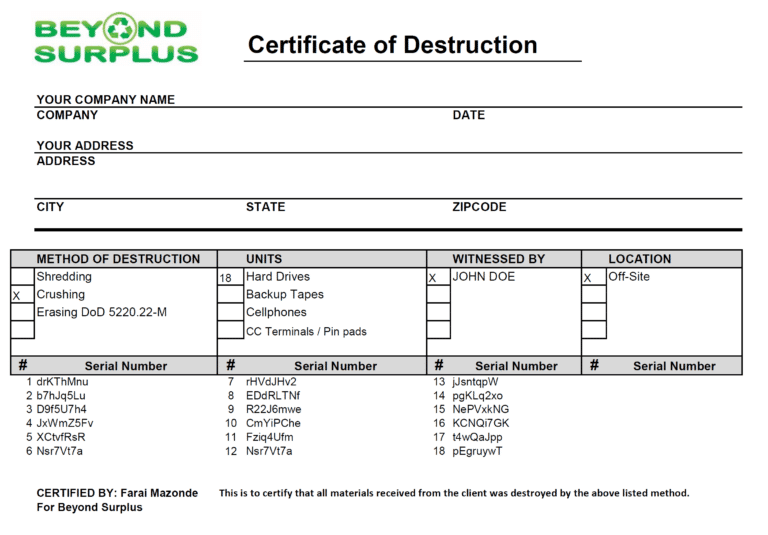
We will supply you with a “Certificate of Recycling & Data Destruction” stating that any drives included with the pickup or drop off of equipment were destroyed, submit this request with your online pickup request. For a nominal fee we can also scan and record all the serial numbers in a spreadsheet in addition to the Recycling & Data Destruction Certificate.
All hard drives are wiped without accessing any data on them, for obvious reason we do now want to know what is on your hard drives. We can create a detailed inventory list of equipment picked up. It will contain each item’s brand, model, serial number, asset tag number(s), and more to help with your compliance needs. All drives that fail, cannot be wiped or obsolete will be shredded at no cost to you by default.
Data Security Service #2: Secure Serialized Hard Drive Shredding
Physical Hard Drive Destruction (Fee Per Drive)
With this service, we will pickup your hard drives & or hard drive containing computers, laptops & servers and securely deliver to our warehouse. At our secure facility we will remove & Shred All Hard Drives & Record Serial Numbers.
After destruction the customer will be emailed a Certificate of Destruction with Date, Media Type Destroyed, Serial Number & Method of Destruction. This service meets all compliance needs.
Data Security Service #3: Visual Verification of Destruction
Physical Hard Drive Destruction (Fee Per Drive)
Beyond Surplus gives you 100% peace of mind offering you Visual Verification of Destruction at our Smyrna Warehouse. We will destroy your hard drives while you watch. This particular physical destruction is considered the most effective way to guarantee absolute data destruction.
Data Security Service #4: Free, Complimentary Shredding Of Hard Drives
For large pickups of servers, computers, laptops etc, Beyond Surplus provides free complementary shredding of storage media. Let us know how much equipment you have to determine if it is enough to offset the cost of shredding.
Data Security For Phones, Tablets, Mobile Devices, Electronic Recycling
All devices are rest to factory devices using the manufacturer’s built-in secure reset feature, if the devices do not power on or cannot be reset, they will be physically destroyed. Most mobile devices, Windows, Apple or Android devices, require the use of passwords, and the devices cannot be used without the password, forcing them to be reset to factory defaults before being usable.
Deinstallation
Our employees are sent to your location(s) to deinstall and or dismantle computer equipment and data centers. We stage it and prepare it for shipment to our warehouse.
Secure Pickup and logistics
We use a network of truck drivers to pick the freight up all over the nation. We use our company-owned truck when servicing companies in the Atlanta metro area. If needed, we can create serial number lists of equipment picked up on pickup. We specialize in working with companies that have hundreds to thousands of locations.
Secure Hard Drive Destruction (Free Service)
We offer Free Physical Hard Drive destruction from from All Business Equipment that we pick up & All Equipment Dropped off at our warehouse; we will supply you with a “Certificate of Recycling & Data Destruction” stating that the drives were destroyed; submit this request with your online pickup request. For a nominal fee we can also scan and record all the serial numbers in a spreadsheet in addition to the Recycling & Data Destruction Certificate.
Local Hard Drive Shredding
If you are looking for a hard drive destruction near you we can help. Beyond Surplus services the data destruction needs of companies in Georgia big and small looking for hard drive destruction in Georgia. We can develop a custom hard drive destruction service just for your organization. Our hard drive destruction service costs businesses next to nothing if we pick up other equipment along with the hard drives.
Searching for hard drive destruction service in Marietta, Roswell or other metro area cities? We can help. All hard drives & storage devices deemed to be too old or non-functional will be shredded or otherwise physically destroyed according to NIST SP 800-88 Guidelines for Media Sanitization at no cost to the customer.
Visual Verification of Destruction (Paid Service)
Beyond Surplus gives you 100% peace of mind offering you Visual Verification of Destruction at our Smyrna Warehouse. We will destroy your hard drives while you watch. This particular physical destruction is considered the most effective way to guarantee absolute data destruction. Contact us to request a quote. You have the option of requesting a Certificate of Destruction that includes serial numbers of all Media that has been destroyed for a small fee.
Certified hard drive destruction (Paid Service)
With this computer hard drive recycling service, we will pickup your hard drives & or hard drive containing computers, laptops & servers and securely deliver to our warehouse. At our secure facility we will remove Record Serial Numbers & Shred All Hard Drives. After destruction the customer will be emailed a Certificate of Destruction with Date, Media Type Destroyed, Serial Number & Method of Destruction. This service meets all compliance needs like HIPPAA with a certificate of destruction hard drive issued.
Contact us if you have special requirements for computer data destruction hard drive. For a nominal fee we can scan and record all the serial numbers in a spreadsheet in addition to the Free Recycling & Data Destruction Certificate. We are a data destruction offering free data destruction services. We can destroy hard drives like no other company in Georgia. We can help destroy laptop hard drives or computer hard drives. We can destroy any hard drive.
Data security has become a paramount concern for individuals and businesses alike. With the ever-increasing risk of cyber-attacks and data breaches, it is crucial to ensure that sensitive information stored on hard drives is properly destroyed when it is no longer needed.
It is crucial to ensure that sensitive information is properly disposed of to prevent unauthorized access. This is where hard drive destruction services play a vital role.
Free Secure Data Destruction (Free Service)
By Default for Every Item processed by Beyond Surplus we will thoroughly inspect every item and protect your Data by removing Asset Tags, Stickers and Identifying marks from each unit (Sanitize). Beyond Surplus is a leading data destruction company in Atlanta offering free data destruction services to businesses in Marietta, Alpharetta, Duluth, Lawrenceville and other Atlanta Metro areas. During te initial Inspection stage every drive is wiped using a Department of Defense Compliant erasure program free of charge. We offer Free Data Destruction aka free hard drive wiping using the DoD 5220.22-M 3 Pass data sanitization methods that will prevent all software-based file recovery methods on all hard drives picked up or dropped off at our warehouse. All hard drives & storage devices deemed to be too old or non-functional will be shredded or otherwise physically destroyed according to NIST SP 800-88 Guidelines for Media Sanitization at no cost to the customer.
At beyond surplus we specialize in destroying hard drives. We can efficiently and securely destroy laptop hard drives. Contact us if you want us to destroy your computer hard drive.
How We Destroy Hard Drives
Beyond Surplus operates an Ameri-Shred industrial hydraulic shredder specifically designed to destroy your hard drives, data backup tapes Beyond Recovery. Only complete, physical destruction will ensure that your digital data is permanently destroyed. As your business faces a surge of privacy breach threats, it’s not enough to simply erase data from your media before it’s discarded. Beyond Surplus offers several approaches to permanent hard drive destruction depending on type of media and volume. We can efficiently and securely destroy any quantity of hard drives. We destroy hard drives like no other companies in the Atlanta metro area.
We are experts at destroying old hard drives. We can effortlessly destroy old computer’s hard drives. We handle hard disk drive disposal for corporations, school districts and fortune 5000 companies. If you are looking to dispose of hard drive in Atlanta you have come to the right place. We can help with disposing of hard drives or hard drive shredding with our free hard drive destroying service.
How To Destroy a Hard Drive?
You ended here because you are searching for how to destroy a hard drive. We have streamlined the process of how to destroy data on a hard drive permanently. We are experts on how to dispose of hard drives and know the different legal requirements of how to safely destroy hard drive.
Hard Drive Shredding
We can shred 750 Server Hard Drives to 1500 Standard Hard Drives Per Hour At our Smyrna facility. A 1-1/2” Shred Width Guarantees the destruction of the hard drive platters, mechanisms and electronic components Beyond Recovery rendering the data unrecoverable.
Hard Drive Crushing
Our Hard Disk Crusher (HDC) drills through the hard disk’s spindles and physically creates ripples in the platters making it impossible to recover the data. We offer secure destruction of the following electronic media: • Hard drives • SSD drives • Backup tapes & storage media • CDs and DVDs • Portable jump drives, thumb drives and flash drive USB devices
Hard Drive Wiping
We offer Free Data Destruction also known as free hard drive wiping using the DoD 5220.22-M 3 Pass data sanitization methods that will prevent all software-based file recovery methods on all hard drives.
All hard drives & storage devices deemed to be too old or non-functional will be shredded or otherwise physically destroyed according to NIST SP 800-88 Guidelines for Media Sanitization at no cost to the customer. Looking for where you can shred my hard drive? Or Atlanta hard drive destruction or where can i take a hard drive we can help. You have found where to dispose of old hard drives or where to wipe your hard drive.
Free Atlanta Hard Drive Recycling
Shredded or destroyed hard drive are recycled, separated for precious metals and smelted as part of the refining process. Hard drives contain precious metals such as gold, silver, platinum and Palladium. You can safely and securely recycle hard drives with Beyond Surplus. If you are looking to recycle hard drives near you, this is the place. You can recycle old hard drives this is the right thing to do.
Recycling old hard drives is simple and easy. Contact us for free computer hard drive recycling services. Regardless of hard drive type we can securely recycle them, laptop hard drives, server hard drives, laptop hard drives, old hard drives can all be securely recycled by Beyond Surplus at our Hard Drive Recycling Facility.
If you are searching for how to dispose of hard drives you have found us. We offer various data destruction methods that render all data unrecoverable. We also offer hard drive recycling. You ended up on this page while searching for secure hard drive destruction service or how to dispose of hard drives.
Free Hard Drive Shredding & Disposal Services Drop Off Center
In an effort to create a safe environment for both our customers and employees, Beyond Surplus is offering a NO-CONTACT Electronics Recycling Drop-Off Service, this service allows our customers to bring in Accepted Recyclable Electronic Equipment and have no direct contact with anyone. Businesses & the general public can drop off accepted equipment at our Atlanta warehouse during our business hours.

Where information is stored and transferred electronically, the importance of hard drive destruction cannot be overstated. Whether you are an individual or a business, protecting sensitive data and maintaining privacy should be a top priority. Hard drive destruction is a crucial step in ensuring that no trace of your confidential information remains on old or unused hard drives.

The Importance of Electronics Recycling

Creative Ways to Recycle Cell Phones

Consequences of Not Recycling Computers

Benefits of Recycling Computers

Atlanta Business Shredding Service

Lab Equipment Disposal Services

Recycle Computers Alpharetta GA

Electronics Waste Disposal Atlanta, Ga

Electronics Recycling Atlanta, Ga

Recycle Laptops Atlanta Ga
Sell Telecom Equipment

Recycle Electronics By Mail For Free
Our Process
Only businesses can schedule a pickup. Residential customers can mail-in or drop-off only.
Compile List of Items to be Recycled
Provide as much detail as possible. e.g 5 computers, 3 printers, 2 laptops, etc.
Contact Beyond Surplus and Request a Recycling Pick up or Drop off
Schedule over the phone, by email or by filling out our form
Pick Up or Drop Off
Pickup or drop off will be scheduled based on your preferred date and time. Confirmation email wil be sent confirming pickup or dropoff
We Handle Logistics
Secure Wiping Data
Our wiping methods are certified. Rest assured your data and information is secure with beyond surplus. Certificates of destruction available upon request.
Certification
Certificates of recycling & data destruction are available for each load of equipment picked up. These are contractual written guarantees that your equipment will be disposed of responsibly.
Service Areas
We do all the planning, heavy lifting, and logistics coordination including on or offsite hard drive shredding so you can focus on your business.
ACR
GAR
SED
KCR
Georgia Service Area

Customer Testimonials
FAQs
Here are frequently asked questions on the services that we provide.
Why should I take my old electronics to an electronic recycling center?
When it comes to disposing of old electronics, electronic recycling centers provide the most responsible and environmentally friendly solution. Electronic recycling is a process that repurposes electronic components such as computers and mobile phones into new, usable items like new computers or cell phones. By taking your old electronics to a recycling center, you will be preventing them from entering landfills where they can cause considerable environmental damage due to hazardous materials such as lead and mercury. In fact, research shows that throwing away an old computer can contribute more than 4 pounds of greenhouse gases into the environment!
Why should hard drives be destroyed by professionals?
Data security: improper disposal of old hard drives can lead to severe data breaches.
The Federal Trade Commission (FTC) is responsible for enforcing the “Disposal Rule” which requires companies to properly dispose of personally identifiable information (PII) on computer hard drives or other digital media. The goal is to reduce the risk of data breaches and identity theft by holding companies accountable for their handling of consumer information. This rule sets the crosshairs of the FTC on the computer-recycling, IT Asset Disposal and digital media destruction process of an organization.
Who recycles computers in Atlanta?
We provide it equipment disposal services to a wide range of clients, including government agencies, healthcare providers, schools, universities, data centers, residential customers and much more.
What area do you service?
We pickup Nationwide from all contiguous United States. Handling All aspects of pickup, removal, and logistics.
Do you charge a fee to pick up equipment for recycling?
Contact Us With A List Of Equipment You Have to go over your options. Beyond Surplus will handle the logistics of equipment pick-up and delivery to its warehouse from your company’s location(s). We also make arrangements to use our own equipment, and or a trucking company to facilitate pick-up and delivery. Beyond Surplus will provide the labor to move and palletize the equipment on site and deliver to its warehouse if necessary. Additionally, Beyond Surplus will provide technicians to de-install equipment if necessary.
Can you recycle iPads?
Yes, you can absolutely recycle your old iPad. iPad recycling or any other electronic device is one of the best ways to reduce waste and limit environmental damage. The benefits of recycling your old device are countless—not only does it keep gadgets out of landfills, but it also helps extend the life cycle of materials used in manufacturing new products and decreases the need to harvest more raw materials from the planet’s resources.
Do you have a list of items you accept for recycling?
Do you have minimum quantity pickup requirements for businesses?
Must the equipment be on a pallet before being picked up?
NO, The best possible way to transport LARGE QUANTITY of obsolete computer equipment is on pallets. Gaylord (Bulk) boxes (a 4-cube, heavy cardboard box that is filled on a pallet) provide the best stability.
We have found that neatly stacking components, even monitors, on a pallet will be stable for transport if shrink-wrapped well.
While having the equipment packed or palletized prior to pick up is ideal and results in a quick pick up, we know some businesses are located in High rise buildings, office parks, or locations without a loading dock or have no Pallets or Boxes to prepare the equipment for pick up. This is not a problem, Let us know, we come prepared with all the required equipment to safely remove the equipment from your building to our truck and to our warehouse.
Do you Accept Paper, Cardboard, Glass?
NO, Please contact your local City or sanitation department for the proper recycling & disposal of these item types.
Do you pick up large office copiers?
Yes, Just the copiers? Copiers Only? Request a quote, Can The Fee Be Waived? Yes Only if picked up with 2 or more pallets worth of computer or IT equipment to offset the cost. Copiers can be dropped off at our warehouse.
Do you buy scrap metal or aluminum cans? Are you a scrap metal yard?
NO, Beyond Surplus currently DOES NOT purchase ferrous and non-ferrous scrap metals. We do accept scrap metal with NO Pay NO Charge.
Do you have an area that the equipment be dropped off at your warehouse after business hours?
NO, All equipment drop offs must be supervised during business hours per EPA guidelines.
Do you charge a fee for recycling?
Yes & No, One of the most frequently asked questions is, “Is there a Fee to drop off equipment for recycling?” For the most part NO depending on the items, please check our accepted items page to determine if there is a fee or not.
NO Charge for Computer LCD or LED Monitors
Do you pay for equipment dropped off for recycling?
NO, some equipment actually costs Beyond Surplus to recycle and dispose off correctly.
Do you pick up items for recycling from homes?
NO, RESIDENTIAL pick ups are available at this time, however items can be dropped off at our warehouse. This includes businesses operated out out homes.
Please refer to the yellow pages for companies that offer residential pickup if items cannot be dropped off at the Beyond Surplus warehouse.
Are there any limits to the amount of electronics customers can drop off?
NO, you can drop off or Businesses can schedule pick up of any quantity of items on our Accepted Items list.
Can I Schedule a Pickup over the Phone?
NO, We prefer that you submit a pickup request online at your convenience gathering all the required information, some information like pictures of equipment and inventory lists cannot be sent over the phone furthermore an online signature is required for all pickup requests.
Do you have other drop off locations In Georgia?
NO, Just the Smyrna location. If you are unable to drop off items at the Marietta Beyond Surplus warehouse please contact your city, county or sanitation department for your nearest recycling drop off center.
Can I mail in my equipment to be recycled by USPS, FedEx, UPS or Freight?
YES, Please contact us for instructions, depending on the items we can pay for shipping.
Don't let obsolete IT equipment become your liability
Without professional IT asset disposal, you risk data breaches, environmental penalties, and lost returns from high-value equipment. Choose Beyond Surplus to transform your IT disposal challenges into opportunities.
Join our growing clientele of satisfied customers across Georgia who trust us with their IT equipment disposal needs. Let us lighten your load.


