A storage room full of retired laptops, a rack of decommissioned servers, a few printers nobody wants to touch, and a manager told to “find e recycle near me” before month end. That’s a common starting point. It sounds like a logistics task, but for a business it’s really a data security, compliance, and asset recovery decision.
Most search results don’t help much. They mix consumer drop-off sites, scrap buyers, and actual ITAD providers into one list. That creates risk fast. In 2022, the United States generated 7.188 million metric tons of e-waste, and over 142,000 computers are thrown out daily in the U.S. according to these e-waste recycling statistics. For a business, that volume is a reminder that disposal has to be managed, documented, and defensible.
From a Simple Search to a Strategic Business Decision

For business equipment, “near me” is often the least important part of the decision. The better question is whether the recycler can document custody, destroy data correctly, and issue the paperwork your legal, compliance, and procurement teams need.
A practical search starts by separating consumer recycling from commercial IT disposition. If a provider’s website talks mostly about household drop-offs, TV fees, and weekend events, it may not be built for office refreshes, multi-site pickups, or chain-of-custody controls. A business search should include terms like IT asset disposition, hard drive shredding, data center decommissioning, and certificate of destruction.
Build a candidate list the right way
Start with certification directories, then validate service fit through direct questions. Generic map results are useful later, not first.
- Search for business terms: Add modifiers like “business electronics recycling,” “ITAD,” or “secure computer disposal.”
- Filter for service scope: Look for pickup, serialized reporting, and handling for data-bearing devices.
- Review their content carefully: If the vendor can’t explain data destruction, they probably can’t defend it.
- Check whether they support your footprint: One office move needs a different partner than a multi-state hardware refresh.
For local SEO context, it helps to understand how buyers phrase service searches. This overview of understanding local search strategies is useful because it explains why “near me” queries often surface broad results that still need qualification.
A good next step is to compare providers that position themselves for commercial work, including options listed on business e-waste recycling near me pages.
Practical rule: If a recycler can’t explain what happens from pickup to final processing, don’t hand over data-bearing equipment.
What works and what fails
What works is a short, disciplined vendor list built around documentation and process. What fails is choosing the closest option and assuming all electronics recyclers operate to the same standard. They don’t.
Finding and Qualifying Professional ITAD Partners
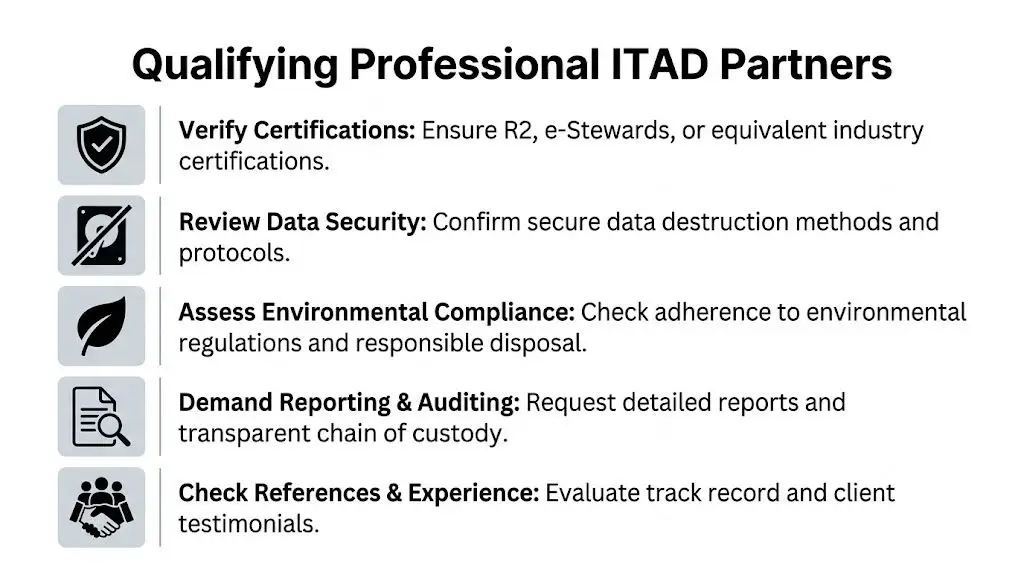
A serious qualification process screens out most vendors quickly. You’re not just hiring a hauler. You’re selecting a company that will touch assets tied to employee data, customer records, licensing controls, and internal audit requirements.
What to verify before the first call
Use a short checklist before you spend time in meetings:
- Certifications: Verify whether the recycler maintains recognized certifications such as R2 or e-Stewards.
- Data process: Ask if they perform NIST 800-88 compliant wiping, physical shredding, or both.
- Reporting: Confirm whether they provide serialized asset reports, destruction records, and recycling documentation.
- Downstream handling: Ask where non-reusable material goes after initial processing.
- Industry fit: Healthcare, finance, education, and government often need tighter controls and clearer records.
If you want a structured internal review document, a vendor due diligence checklist helps procurement and IT work from the same standard.
Compare service models before you compare prices
Different models fit different business situations. Treat them differently.
| Service model | Best fit | Main advantage | Main trade-off |
|---|---|---|---|
| Scheduled pickup | Office refreshes, relocations, recurring disposition | Better control and easier logistics | Requires coordination |
| Secure drop-off | Very small business volumes | Fast for limited non-sensitive loads | Weaker fit for formal custody needs |
| Mail-in | Remote staff, distributed devices | Useful for scattered assets | Packaging and tracking have to be managed |
| Palletized freight | Large enterprise and data center projects | Efficient for bulk loads | Needs planning and staging |
A vendor that mainly promotes drop-off convenience may still be fine for scrap handling. That doesn’t make them a strong ITAD partner.
Pricing conversations often happen too early. First confirm process maturity. A cheaper quote loses its appeal if your team has to chase serial reports, explain missing drives, or clean up inconsistent documentation later.
Comparing E-Recycling Service Models for Your Business

Businesses usually choose among pickup, drop-off, mail-in, or freight-based project logistics. On paper, each one “recycles electronics.” In practice, the service model changes your exposure.
Pickup usually wins for business use
For most offices, scheduled pickup is the cleanest option. Devices stay on site until a documented handoff. Your staff doesn’t need to improvise transport, and the recycler can align labor, pallets, manifests, and destruction workflow in advance.
That matters most when the load includes servers, laptops, network switches, or anything with stored data. For distributed teams, a controlled mail-in workflow can also work well, especially when the provider has clear receiving procedures. Businesses evaluating remote device returns can compare mail-in electronics recycling options as part of a broader ITAD policy.
Where the other models fit
Drop-off has a place, but it’s narrower than many managers think.
- Secure drop-off: Works for a very small quantity of equipment when the devices are low risk and your team can document transfer internally.
- Mail-in programs: Useful when employees are scattered and collecting devices centrally would be slower or more expensive.
- Freight and palletized loads: Best for large refreshes, closures, and decommissions where staging matters as much as processing.
Third-party certifications matter because they force a recycler to prove process discipline. Without that discipline, every convenience feature becomes less valuable. Fast pickup doesn’t help if chain of custody is weak. Free service isn’t attractive if it ends with vague paperwork.
Ask one question early: “What document will you issue that shows the asset left our control, how data was handled, and where the material went next?”
The answer usually tells you whether you’re talking to a scrap collector or a real ITAD operator.
The Critical Vetting Process for Security and Compliance
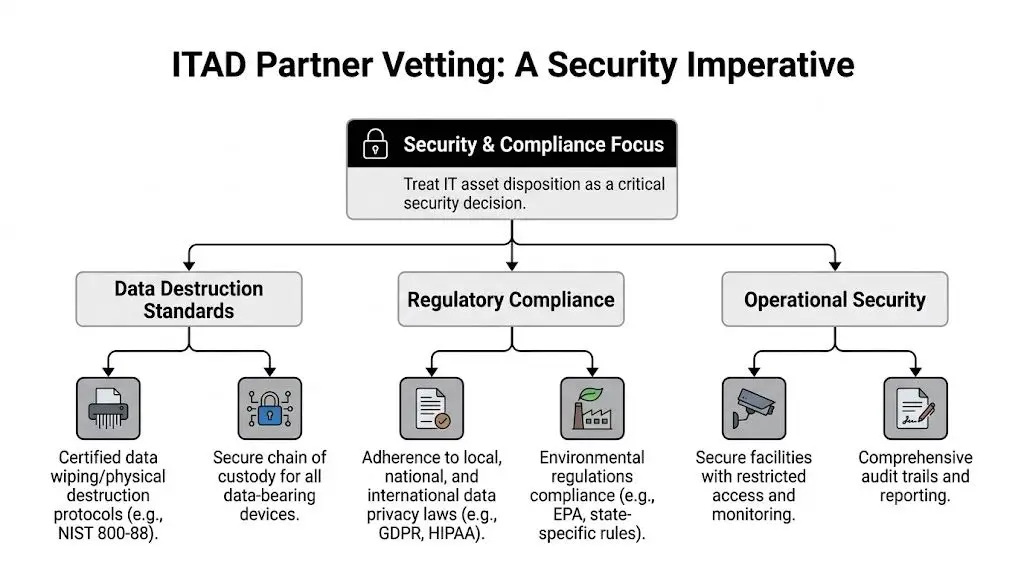
This is the part many companies rush. They get a quote, schedule a pickup, and assume the vendor’s standard paperwork covers everything. Often it doesn’t.
Many businesses miss the compliance side of electronics recycling. Clear guidance on certificates of destruction is still rare, and 90% of generic recycling locators don’t address that gap according to this analysis of recycling locator content and compliance gaps. That matters because documentation is what transfers liability in a defensible way.
Questions that expose weak vendors
Ask direct questions and listen for specifics.
How do you handle data destruction?
You want a clear answer on wiping, shredding, or both, and when each method is used.How is chain of custody documented?
If the answer is loose, your internal audit trail will be loose too.Do you provide certificates of destruction and recycling?
If documents are “available on request,” ask to see sample versions.What happens to reusable equipment versus scrap material?
Reuse, resale, and commodity recovery should be explained separately.Who are your downstream vendors?
A recycler is only as reliable as the outlets it uses after first processing.
To ground the certification discussion, many managers benefit from reading a plain-language explanation of what R2 certification means.
Prepare your side before pickup
Vetting the recycler is only half the process. Your team also needs a clean internal handoff.
- Build an inventory: Record asset tag, serial number, device type, and location.
- Separate data-bearing devices: Laptops, desktops, servers, and storage shouldn’t be mixed casually with peripherals.
- Flag exceptions: Note damaged devices, swollen batteries, or equipment that requires special handling.
- Assign a sign-off owner: One person should approve release and receive final documentation.
Documentation is part of the security control, not an administrative extra.
The strongest ITAD programs treat disposition like any other governed process. There’s an owner, a record, and a decision trail.
Preparing Your IT Assets for a Seamless Handover

Good preparation shortens project time, improves reporting quality, and reduces mistakes at the dock. It also helps you recover more value from equipment that still has a secondary market.
The professional recycling process starts with secure transport and data sanitization using NIST 800-88 standards, and batteries deserve special attention because they pose a fire risk and account for an estimated 20-30% of incidents at recycling facilities if not handled correctly according to this review of the e-waste recycling process.
A handover checklist that works
The strongest handovers are boring. That’s a good thing. Nothing should rely on memory.
- Consolidate by category: Keep laptops with laptops, servers with servers, and loose drives in separately marked containers.
- Match inventory to physical count: Reconcile exceptions before pickup day, not after.
- Isolate batteries and damaged devices: Flag them clearly so transport and receiving teams know what needs special handling.
- Remove non-project items: Personal electronics, legacy media, and unrelated scrap create confusion and reporting errors.
Where companies lose control
Most problems happen before the truck arrives. Staff add a few extra boxes at the last minute. A department slips in unlisted drives. Someone assumes internal wiping was enough but can’t prove it. Those are process failures, not recycling failures.
There’s also a financial angle. Equipment that arrives organized, identified, and complete is easier to evaluate for reuse or buyback. Equipment that arrives mixed, damaged, or undocumented is more likely to be treated as low-value scrap.
Keep the project boundary tight. If it isn’t on the inventory or approved by the project owner, it shouldn’t be loaded.
That one rule prevents a surprising amount of confusion.
Unlocking Value and Managing Specialized Disposals
The phrase “e recycle near me” pushes buyers toward convenience. Businesses should think about outcomes instead. Sometimes the right result is certified destruction. Sometimes it’s refurbishment and resale. The important part is deciding before the equipment leaves your control.
One of the biggest blind spots in this market is value recovery. Many providers talk about free pickup and little else. As noted by this discussion of IT buyback and resale value in electronics disposition, that leaves businesses unaware that retired equipment may still hold resale value. A mature ITAD process separates assets that should be destroyed from assets that should be evaluated for recovery.
Where value recovery belongs
Buyback and asset recovery fit best when equipment is recent enough, complete enough, and documented well enough to move through testing and resale channels. That usually applies to business laptops, enterprise servers, networking gear, and some mobile fleets.
For organizations with that mix, asset recovery services can be part of the same disposition workflow as recycling and data destruction. That’s a more disciplined model than sending everything straight to scrap.
Specialized equipment needs tighter planning
Not all disposals are standard office cleanouts.
Healthcare organizations may have storage devices embedded in equipment. Manufacturers often have ruggedized systems or proprietary components that need product destruction. Data center teams may need coordinated de-installation, serialized removal, and staged pickups tied to shutdown windows.
That’s why the best business process doesn’t start with “Where can I drop this off?” It starts with four decisions:
- What must be destroyed
- What can be remarketed
- What requires special handling
- What records your organization needs to close the project
If you’re choosing among e recycle near me options for a business, use location as a filter, not the decision itself. The decision is whether the provider can protect data, issue the right documents, and manage the asset mix in front of you.
If your team needs a documented path for electronics recycling, secure data destruction, IT buyback, or a multi-site pickup program, contact Beyond Surplus for a business-focused ITAD review.