Your search probably started with a simple problem. There’s a closet, cage, or back room filling up with retired laptops, failed hard drives, old switches, monitors, and a few servers nobody wants to touch until “later.” For an IT manager, that backlog isn’t clutter. It’s dormant risk.
That’s why e-recycle near me can be a useful search, but it often leads businesses to the wrong solution. Consumer drop-off sites are built for convenience. Business IT disposal needs chain of custody, data destruction, audit support, and logistics that won’t waste your team’s time.
The Growing Challenge of Business E-Waste
A growing pile of obsolete equipment usually means one thing. Refresh cycles happened faster than disposition planning.

What the backlog really represents
In a business environment, old electronics are rarely just “junk.” They often contain customer records, employee data, credentials, licensed software, network configurations, and regulated information. Even equipment that seems harmless, such as printers, copiers, and VoIP gear, can retain data that needs proper handling.
The environmental side matters too. The world generated a record 62 million tonnes of electronic waste in 2022, an 82% increase from 2010, and that total is projected to reach 82 million tonnes by 2030, while documented recycling rates are expected to decline, according to the Global E-waste Monitor figures summarized here.
Why businesses feel this problem differently
A household might recycle a few devices each year. A company can generate pallets of retired assets in one refresh, one merger, one office closure, or one data center migration. That changes the decision from disposal to operations.
A business e-waste program has to answer practical questions:
- Who controls the assets: Has every device been identified before it leaves the site?
- Who protects the data: Is sanitization documented, or is everyone relying on assumption?
- Who moves the equipment: Will your staff box, load, and transport everything?
- Who owns the liability: Do you have paperwork that proves final disposition?
Old equipment becomes a compliance issue long before it becomes a space issue.
What works and what doesn’t
What works is treating end-of-life IT as part of asset management. Inventory it. Segment by media type and business sensitivity. Decide what can be remarketed, what must be destroyed, and what needs specialized recycling.
What doesn’t work is waiting until a storage room is full, then sending someone to the nearest public drop-off with mixed equipment and no paperwork. That may remove the pile. It doesn’t remove the risk.
Why a Business Search for E-Recycling is Different
Most search results for e-recycle near me point to retail collection bins, municipal events, or household hazardous waste sites. That’s fine for a broken keyboard from home. It’s not enough for enterprise IT.

Consumer recycling and business ITAD are not the same service
Most e-recycle near me content points to consumer drop-offs and ignores business requirements for secure data destruction. That gap matters because 40% of recycled drives retain recoverable data, and regulations such as the FTC Disposal Rule require certified disposal for businesses, as noted in this review of the local search gap around business-safe electronics recycling options.
If you’re comparing local options, start by understanding what IT asset disposition means for businesses. ITAD is not just recycling. It’s the controlled retirement of technology assets with documentation, data handling, and downstream accountability.
The real business risks
A generic drop-off model usually breaks down in four places:
- Data security: Retail and municipal sites usually don’t sanitize drives for you.
- Chain of custody: Once assets leave your control, there may be no serialized tracking.
- Compliance support: You may get a receipt, but not the documentation an auditor expects.
- Operational drag: Your team still has to sort, pack, load, and transport the equipment.
Practical rule: If a provider can’t explain how they track each asset from pickup through final processing, it’s not a business-grade disposition process.
What an IT manager should require
Ask direct questions. Do you provide serialized inventory reconciliation? Do you sanitize to NIST guidance? Can you issue certificates of destruction and recycling? Who handles downstream processing? What happens to drives removed from laptops, arrays, and servers?
Those answers tell you whether you’ve found a recycler or an ITAD partner. For a business, that distinction is the whole point.
Comparing Your E-Recycling Logistics Drop-off vs Pickup vs Mail-In
The right method depends on volume, asset type, security requirements, and how much labor you want to spend internally. There isn’t one correct option for every situation.

Business E-Recycling Options Compared
| Method | Best For | Security Level | Convenience | Cost |
|---|---|---|---|---|
| Drop-off | Small batches of low-complexity equipment | Depends on provider controls | Lower for business teams because staff must transport | Often suitable when volume is limited |
| Pickup | Office cleanouts, server rooms, multi-pallet loads, decommissions | Stronger when chain of custody starts at your site | Highest for bulk projects | Usually justified for larger jobs |
| Mail-In | Small quantities of portable assets in remote locations | Good if packaging and intake controls are clear | Good for distributed teams | Practical for selected items |
Drop-off works when control stays simple
Drop-off can make sense for a small lot of non-complex assets when the receiving facility is set up for business documentation. The weakness is labor. Your staff still has to stage everything, verify counts, transport it, and hand it off correctly.
It also creates a break point in accountability. If devices move in personal vehicles without formal intake, you’ve introduced avoidable exposure.
Pickup works for scale and discipline
Pickup is the strongest option for office closures, refresh projects, warehouse cleanouts, and data center work. The provider can start chain of custody at your location, load assets in a controlled manner, and reduce the number of hands touching the equipment.
That’s usually the most efficient route when timing matters. It also spares your IT team from turning into a moving crew.
Mail-in works for distributed organizations
Mail-in programs are useful when you have a remote office, a small branch, or a handful of laptops that need controlled disposition. The trade-off is packaging effort. Someone on your side still has to prepare the shipment correctly and keep the asset list clean.
For organizations that need that option, a mail-in electronics recycling program for business assets can fill a real logistics gap.
Choose logistics based on custody and labor, not just distance. The nearest option isn’t automatically the safest or the fastest for your team.
Securing Your Data The Golden Rule of IT Asset Disposition
If the data isn’t destroyed properly, the rest of the recycling process doesn’t matter.
What a defensible process looks like
Professional ITAD uses a certified chain of custody and follows NIST 800-88 for media sanitization through wiping or physical shredding to particles under 2 mm. Certified providers can recover up to 98% of materials, which sharply differs from informal recycling that often mishandles hazardous substances and leaves data-bearing media exposed, as outlined in this review of secure ITAD processing challenges and controls.
For an IT manager, the business takeaway is simple. You need a method that matches the media, the data classification, and the audit requirement.
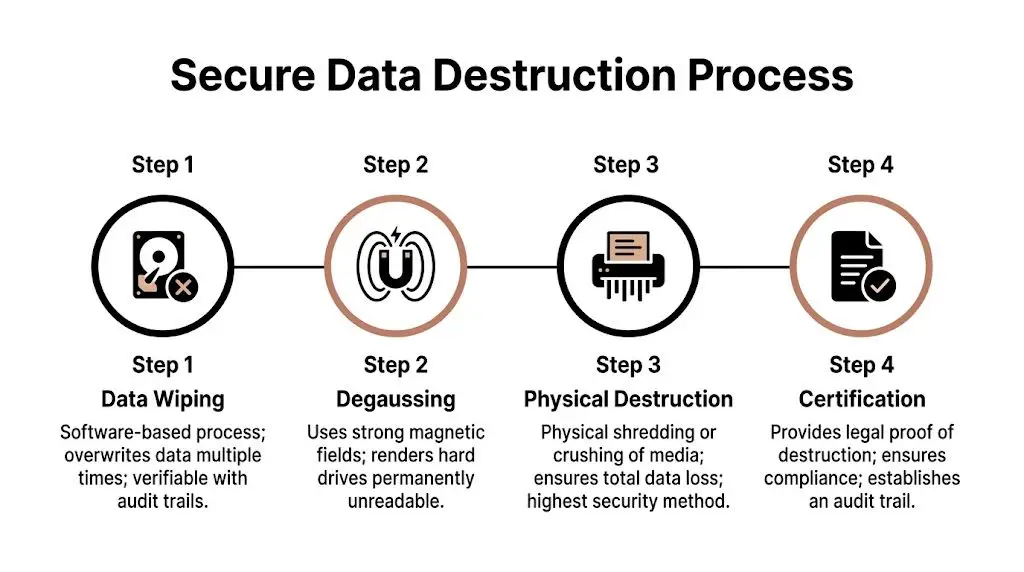
Wiping, degaussing, and shredding
Software wiping is appropriate when assets may be reused or remarketed and the media supports verifiable overwrite processes. The benefit is value recovery. The requirement is proof that the wipe completed successfully and ties back to the right serial number.
Degaussing destroys magnetic media with a strong magnetic field. It can be effective for specific drive types, but it also renders the media unusable. It’s a destruction path, not a reuse path.
Physical shredding is the cleanest answer for highly sensitive media or failed drives that can’t be wiped. If your policy prioritizes certainty over resale, shredding is often the right call.
A clear explanation of NIST SP 800-88 data sanitization methods helps when you’re aligning legal, security, and operations around one policy.
Why retention policy and destruction policy must align
A lot of confusion starts before disposition day. Teams hold devices longer than needed because nobody is sure what must be retained and what can be destroyed. That’s why records policy should sit next to device retirement policy. A practical reference on business records retention compliance can help teams separate retention obligations from unnecessary hardware hoarding.
Destroy the data according to policy. Keep the documentation according to policy. Don’t confuse the two.
The Final Step Certificates of Recycling and Data Destruction
Once the pallets are gone and the drives are destroyed, you still need evidence. Not a verbal confirmation. Not an email saying “all set.”

What the certificates do
A Certificate of Data Destruction documents that data-bearing media was sanitized or destroyed under a defined process. A Certificate of Recycling documents that equipment entered an approved recycling stream for responsible downstream handling.
Together, these records support internal governance, vendor management, audit readiness, and liability transfer. They also help settle the common internal question after a cleanout: “Can we prove what happened to every asset?”
What should be documented
The exact format varies by provider, but useful documentation generally ties back to the job itself and the assets involved. For business clients, the paperwork should be easy to file and easy to retrieve later.
Look for records that support:
- Job traceability: Dates, service scope, and the parties involved
- Asset linkage: The ability to connect certificates to inventory lists or serial records
- Method clarity: Whether media was wiped, shredded, or otherwise processed
- Audit support: A format your compliance, legal, or procurement teams can use
If you need an example of what this documentation is meant to support, review how a certificate of destruction fits into ITAD documentation.
If a recycler can’t produce clear documentation after the job, you’re still carrying part of the risk.
How Beyond Surplus Delivers Nationwide E-Recycling for Businesses
For companies searching e-recycle near me, distance usually isn’t the hard part. Consistency is. A business needs one process that works for a branch office, a headquarters refresh, and a decommission project without reinventing the playbook each time.
What a national business process should include
A workable service model should cover pickup coordination, secure handling, documented data destruction, and downstream recycling accountability. It should also support varied asset mixes, including laptops, desktops, servers, networking gear, and specialized business equipment.
For organizations that need multi-site support, nationwide electronics recycling logistics in Georgia and beyond shows how one provider can coordinate pickups across the contiguous United States while supporting secure IT asset disposition. Beyond Surplus also handles certified data destruction, certificates for compliance records, and projects ranging from routine equipment removal to data center de-installations.
Where businesses usually gain efficiency
The biggest improvement usually isn’t “finding a recycler.” It’s reducing internal handling. When the vendor can coordinate logistics, control intake, separate reuse from destruction, and return documentation cleanly, your IT team gets time back and your legal exposure drops.
That’s what business e-recycling should do. Remove equipment, yes. But also remove uncertainty.
Frequently Asked Questions for Business E-Waste
What affects the cost of business e-recycling
Cost usually depends on volume, equipment type, pickup requirements, data destruction method, and whether any assets have resale value. A mixed pallet of obsolete monitors is different from a rack of servers with recoverable components.
Can specialized equipment be handled
Yes, but it should be scoped in advance. Medical, laboratory, and industry-specific devices often need customized packaging, data review, de-install support, or downstream processing controls.
How does IT buyback work
Assets with remaining market value are typically evaluated by model, age, condition, configuration, and demand in secondary channels. The practical benefit is that resale can offset part of the overall project cost.
Do we need to inventory everything before pickup
You should identify what you have before any disposition project starts. That doesn’t always mean your team must build a perfect spreadsheet alone. A qualified ITAD provider can often help reconcile assets during pickup and processing, but your internal list should still reflect what’s leaving your control.
Contact Beyond Surplus if your business needs certified electronics recycling, secure IT asset disposition, documented data destruction, or nationwide pickup coordination for retired IT equipment.