When your Georgia business is ready for a technology refresh, managing the secure and compliant retirement of old equipment is a critical step. The process, known as IT asset disposition in Georgia, involves the systematic disposal, recycling, and sometimes resale of obsolete IT hardware. More importantly, it is a strategic function that ensures the complete destruction of sensitive data, adherence to strict environmental regulations, and the recovery of any residual value from your assets. This is not simply a disposal task; it's a crucial risk management strategy that shields your company from significant legal and financial repercussions.
Defining a Modern ITAD Strategy in Georgia
IT Asset Disposition (ITAD) is the specialized, end-to-end process for managing the retirement of your company's technology. Many businesses in Georgia mistakenly view the disposal of old computers, servers, and networking gear as a simple cleanup job. This perspective dangerously overlooks the immense liability associated with the sensitive data stored on these devices and the stringent environmental laws governing their disposal.
A comprehensive IT asset disposition Georgia program transcends basic electronics recycling. It is a fully integrated system designed to address several critical business functions simultaneously. Without a formal ITAD strategy, companies in major commercial hubs like Atlanta, Augusta, and Savannah leave themselves vulnerable to severe penalties, ranging from substantial fines for data breaches under regulations like the FTC Disposal Rule to violations for improper e-waste handling.
The Scope of a Professional ITAD Program
A professional ITAD process is far more than a simple pickup service for e-waste. It encompasses a series of secure, documented procedures designed to protect your organization at every stage. You can explore the specifics in our detailed guide on what is IT asset disposition. The primary objectives are always to eliminate risk, guarantee compliance, and maximize any financial value remaining in your retired assets. This strategic approach transforms a potential liability into a structured, secure, and often profitable endeavor.
A common mistake is treating ITAD as an afterthought. It should be an integrated part of your IT lifecycle management, ensuring assets are handled with the same level of security at their end-of-life as they were during active deployment.
To better understand what a robust program entails, it's helpful to break down the essential services that form the foundation of any Georgia-compliant ITAD partnership. Each component is vital for building a secure and accountable chain of custody from the moment equipment leaves your facility.
Core Components of a Georgia-Compliant ITAD Program
Here’s an overview of the essential services and considerations for any Georgia business implementing a secure and compliant IT asset disposition strategy.
| Component | Description | Why It's Critical for Georgia Businesses |
|---|---|---|
| Secure Logistics | Utilizing dedicated, GPS-tracked vehicles and trained personnel for asset transportation from your location to a secure processing facility. | Prevents asset loss or theft during transit, a primary vulnerability for data breaches, and establishes the initial link in a secure chain of custody. |
| Certified Data Destruction | Permanently destroying all data on storage media via methods like NIST 800-88 compliant wiping or physical shredding. | Protects against catastrophic data breaches and ensures compliance with federal regulations such as the FTC Disposal Rule, HIPAA, and others specific to your industry. |
| Asset Tracking & Reporting | Creating a detailed, serialized inventory of every asset and providing comprehensive reports and Certificates of Data Destruction. | Delivers auditable proof of compliance and proper disposal, formally transferring liability from your business to the ITAD vendor. |
| Value Recovery (Remarketing) | Evaluating functional, newer equipment for its resale potential and returning a portion of the proceeds to your business. | Converts a disposal cost into a revenue stream, helping to offset the expense of new technology and improving the overall ROI of IT investments. |
| R2 Certified Recycling | Processing non-reusable materials in an environmentally responsible manner, adhering to strict standards for handling hazardous e-waste. | Ensures compliance with environmental laws, prevents toxic materials from entering landfills, and supports corporate social responsibility (CSR) initiatives. |
Integrating these components doesn't just fulfill a compliance requirement; it builds a protective framework around your business, your data, and your brand reputation.
Meeting Data Security and Compliance Mandates in Georgia
When managing IT asset disposition in Georgia, the hardware is secondary. The primary concern is the vast amount of data residing on it.
Mishandling the sensitive information on retired assets is not merely an operational oversight—it can trigger severe legal and financial consequences. Secure data destruction is not an optional service; it is a federal requirement, and the penalties for non-compliance are substantial.
The market data confirms this. The North American ITAD market is projected to reach USD 4.85 billion in 2025 and grow to USD 6.59 billion by 2030. A key driver of this growth is the small and medium-sized business (SME) sector, which accounts for 63.90% of the market. These businesses are increasingly aware of the devastating impact of a data breach originating from improperly disposed of IT equipment.
This heightened awareness is crucial, as federal regulations like the FTC Disposal Rule apply to nearly every business handling consumer data. The rule mandates that businesses must take appropriate measures to dispose of sensitive information to prevent unauthorized access. Failure to comply can result in significant fines and reputational damage.
Choosing the Right Data Destruction Method
Georgia businesses have two primary, certified methods for ensuring data is irretrievably destroyed. The optimal choice depends on internal security policies, compliance requirements, and whether the storage devices have any resale value.
- Secure Data Wiping: This digital sanitization process uses specialized software to overwrite a hard drive's entire surface with random data, rendering the original files unrecoverable. This is performed according to strict standards like NIST SP 800-88. This method is ideal for newer, functional drives that can be refurbished and resold, allowing you to recoup part of your initial investment.
- Physical Shredding: This is the definitive, brute-force approach. For older, non-functional, or highly sensitive drives, physical destruction is the only acceptable method. An industrial shredder grinds the drives into small metal fragments, making data retrieval physically impossible.
Adherence to proven guidelines like NIST SP 800-88 is essential for meeting government and industry standards for data sanitization.
The Power of Certified and Auditable Destruction
It is not sufficient to simply destroy data—you must be able to prove it. A certified, auditable paper trail is indispensable, especially for Georgia companies in regulated sectors like healthcare (HIPAA) or finance (GLBA). A robust risk management process is fundamental to navigating the data breach and compliance challenges inherent in IT asset disposition.
The most critical document in the ITAD process is the Certificate of Data Destruction. It is more than a receipt; it is a legal document that formally transfers liability for the data from your company to your ITAD partner.
This certificate provides the documented proof that auditors and regulators require. It should always include:
- A unique serial number for tracking.
- The date and method of destruction (e.g., wiping, shredding).
- A detailed inventory listing the serial numbers of the destroyed hard drives.
- A formal statement confirming compliance with relevant data protection laws.
Without this auditable proof, your business remains liable, even if the data was correctly destroyed. Partnering with a certified vendor for your IT asset disposition in Georgia ensures you receive this crucial documentation, effectively closing the loop on your data security responsibilities.
From Cost Center to Revenue Stream: ITAD Value Recovery
For most Georgia businesses, disposing of old IT equipment is viewed as a necessary expense—a budget item required for security and compliance. However, this perspective overlooks a significant opportunity. A strategic IT asset disposition Georgia program can transform this process from a liability into a source of revenue.
This involves more than just recycling; it's about identifying the value in equipment that can be refurbished and resold on the secondary market. Instead of paying to have your assets removed, you could receive a payment.
Evaluating Assets for Maximum Return
The first step in recovering value is a thorough, professional evaluation. While not every retired asset has resale value, valuable components are often missed. An experienced ITAD partner knows how to assess each device based on several key factors to determine its marketability.
Key evaluation criteria include:
- Age and Model: Newer equipment, typically within a three to five-year timeframe, retains the most value. Specific models from leading brands like Dell, HP, Cisco, and Apple are consistently in demand.
- Condition: Functional and cosmetically clean equipment commands higher prices. However, even non-working assets can be valuable for their components, such as memory, processors, or hard drives.
- Current Market Demand: The secondary market for IT equipment is dynamic. A knowledgeable partner understands current trends and knows which items, such as enterprise-grade servers or networking switches, are in high demand.
- Configuration: Specifications like RAM, storage capacity, and processor type directly influence the final resale price.
This systematic evaluation provides a clear picture of the potential financial return.
From Cost Center to Profit Center
The financial difference between a basic disposal service and a strategic ITAD program is substantial. One is a guaranteed expense, while the other offers a potential revenue stream. This is a critical distinction for any IT manager or procurement professional in Georgia looking to optimize their budget. Explore how this works with our professional IT equipment buy-back services.
A strategic ITAD partner sees a pallet of old servers not as e-waste, but as an opportunity to recover capital that can be reinvested into your business, effectively lowering the total cost of ownership for your technology.
Let’s compare the two approaches to see the real impact on your bottom line.
Comparing Financial Outcomes of ITAD Approaches
This table illustrates the financial expectations for a Georgia business choosing basic e-waste recycling versus a strategic ITAD program focused on value recovery.
| Financial Metric | Basic E-Waste Recycling | Strategic ITAD With Value Recovery |
|---|---|---|
| Initial Cost | Almost always involves fees for pickup, processing, and data destruction. It is a guaranteed expense. | Fees are often offset or completely eliminated by the value of the resold equipment. |
| Revenue Generation | $0. The objective is solely disposal, not revenue. You pay for the service and receive no financial return. | Creates a direct revenue stream. A portion of the proceeds from equipment sales is paid back to your company. |
| Total Cost of Ownership (TCO) | Increases the TCO of your IT assets by adding a final disposal cost at the end of their lifecycle. | Reduces TCO by recovering residual value, which helps fund the next technology refresh. |
| Budget Impact | A standard operational expense that depletes the IT budget. | A potential source of income that can augment the IT budget and improve overall profitability. |
By partnering with a vendor that has established remarketing channels, businesses throughout Georgia can transform their IT asset disposition from a necessary cost into a smart financial strategy.
How a Secure Chain of Custody Protects Your Business Assets
An ITAD program's security is only as strong as its logistics. The moment your old equipment leaves your Georgia facility, it enters a critical, vulnerable phase. This is why a secure chain of custody is the absolute backbone of the IT asset disposition process.
This is a documented, unbroken trail that an asset follows from your possession to its final disposition. It's a comprehensive security protocol designed to track, monitor, and account for every device at every stage. This meticulous process mitigates the risks associated with standard movers or uncertified recyclers, where assets can be lost or stolen.
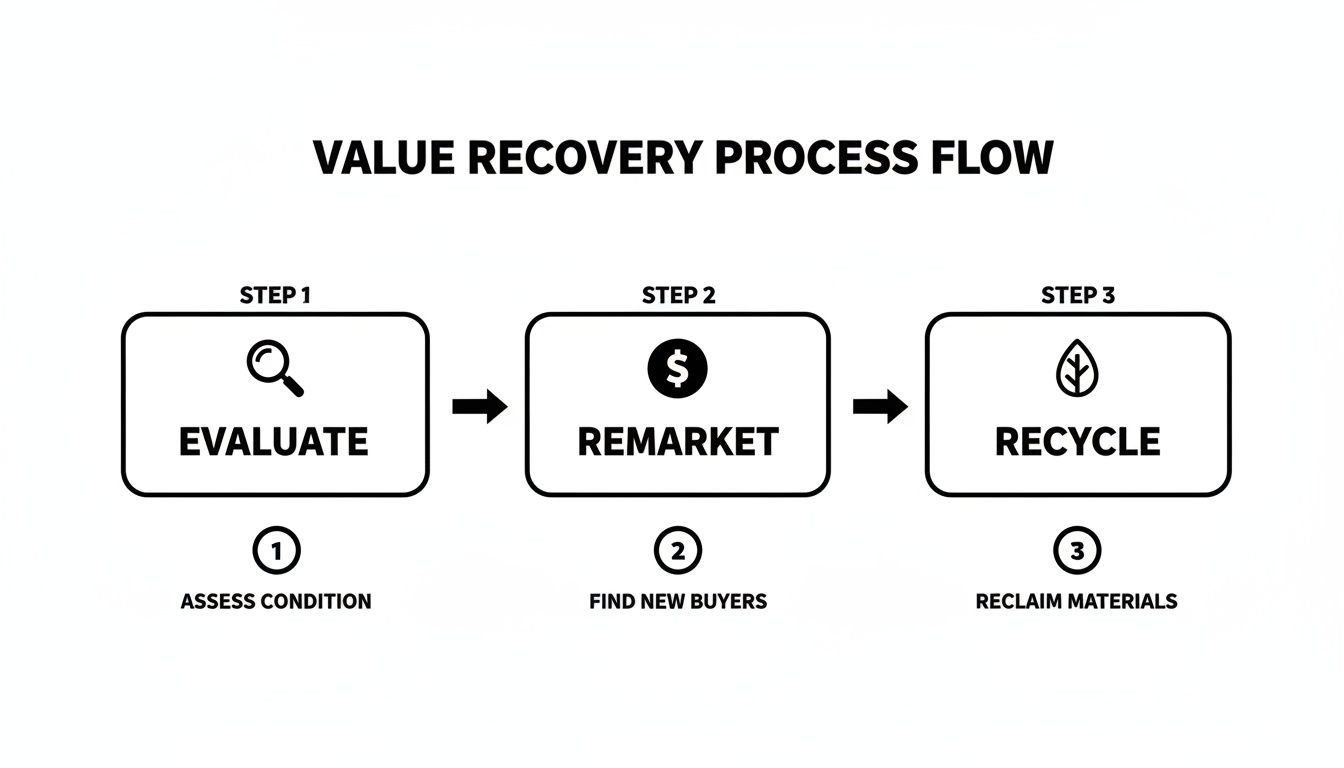
This flowchart illustrates the basic steps of value recovery, all protected by a secure chain of custody.
From initial evaluation to final recycling, every stage must be secure and auditable.
Key Elements of a Secure Chain of Custody
A truly secure chain of custody is a tangible system built on several interlocking components, each adding a layer of protection to ensure your assets are safe.
- Serialized Asset Tracking: Upon arrival at your Georgia location, every asset is inventoried and tagged with a unique serial number. This creates a detailed manifest that is scanned and verified at every transfer point.
- Secure Packing and Transport: Assets are packed into sealed, tamper-evident containers before being loaded onto dedicated, GPS-monitored vehicles. This prevents unauthorized access and provides real-time location data.
- Access-Controlled Facilities: Upon arrival, assets are moved into a secure, monitored facility with strict access controls. Only authorized, background-checked personnel can handle the equipment.
This level of security is non-negotiable as the ITAD market expands. The U.S. IT Asset Disposition market, valued at USD 2.66 billion in 2022, is projected to reach USD 4.90 billion by 2032, driven by data center consolidation and cloud migration that generate massive volumes of retired equipment.
Documentation: The Final Link in the Chain
The chain of custody is not complete until you receive comprehensive, auditable documentation. This is not just a receipt; it is legally defensible proof that your assets were handled correctly from start to finish.
The ultimate goal of a chain of custody is to provide an unbroken, auditable record that can withstand any internal or external scrutiny. It proves due diligence and formally transfers liability.
Upon completion, you receive detailed reporting that reconciles every asset on the initial manifest with its final outcome—data destruction, remarketing, or recycling. This includes the crucial Certificate of Destruction, your official proof of compliance. To understand why this document is so vital, learn more about Beyond Surplus’s process for issuing a certificate of destruction.
This transparent reporting closes the loop, providing your Georgia business with complete peace of mind.
Upholding Environmental Responsibility with Certified E-Waste Recycling
While data security and value recovery are critical, responsible IT asset disposition is fundamentally about environmental stewardship. Rapid technological advancement creates a significant challenge: electronic waste (e-waste), the fastest-growing waste stream globally. For any business in Georgia, managing this e-waste is a core corporate responsibility.
Improper disposal of IT equipment has severe environmental consequences. Old computers, servers, and monitors contain hazardous materials like lead, mercury, and cadmium. If these items end up in a landfill, these toxins can leach into the soil and groundwater, causing long-term environmental damage.
This environmental imperative is a major factor in the global IT Asset Disposition market's projected growth from USD 20.66 billion in 2025 to USD 31.89 billion by 2029. This growth reflects increasing pressure on businesses to manage end-of-life technology responsibly due to stricter regulations and heightened consumer expectations.
The Role of R2 Certification
How can you ensure you are working with an environmentally responsible provider? Look for key certifications. The most important in the industry is the R2 (Responsible Recycling) standard. This is not just a marketing label; it is a rigorous, third-party audited certification that verifies a recycler meets the highest standards for environmental safety, data security, and worker protection.
When you choose an R2 Certified partner for your IT asset disposition in Georgia, you receive a guarantee that:
- Hazardous materials are managed and disposed of correctly.
- There is a strict prohibition on exporting hazardous e-waste to developing nations.
- A secure chain of custody is maintained throughout the recycling process.
Partnering with an R2 Certified recycler is the clearest way for a Georgia business to ensure its ITAD process is both environmentally sound and ethically managed. It elevates a compliance task into a statement of corporate values.
From E-Waste to Reusable Commodities
A certified recycler’s primary function is to de-manufacture retired assets and safely extract valuable materials. This is a critical component of the circular economy, where end-of-life products are converted back into raw materials.
Technicians meticulously break down equipment into its core components. Valuable commodities like aluminum, copper, steel, and precious metals are separated and sent to certified smelters for use in new products. Other materials, such as glass and plastics, are also recovered. Our in-depth guide explains more about what is R2 certification and its significance.
This process does more than just prevent toxic materials from polluting the environment. It also provides your organization with transparent, detailed reports that document the entire recycling journey. This is the documentation needed for sustainability reports, proving to customers and stakeholders your commitment to responsible business practices.
How to Choose the Right ITAD Partner in Georgia
Selecting a partner for your IT asset disposition in Georgia is a critical business decision, not just another vendor procurement task. The right partner acts as an extension of your security and compliance teams, protecting you from significant data, financial, and reputational risks.
A dependable ITAD provider is more than a pickup service; they are a strategic ally who understands the complete technology lifecycle. It's about finding a company that aligns with your organization's specific security and accountability needs. While from a different industry, this guide on choosing the right 3PL partner highlights similar critical points like reliability and process transparency that are equally vital in ITAD.
Key Certifications to Verify
Industry certifications are non-negotiable. They are the best evidence that a vendor adheres to the highest standards for both data security and environmental responsibility. Before signing any contract, ensure the provider holds these credentials:
- NAID AAA Certification: This is the gold standard for secure data destruction. It signifies that the company has passed rigorous, unannounced third-party audits covering their hiring practices, facility security, and destruction processes.
- R2 (Responsible Recycling) Certification: This certification focuses on environmental safety. R2 certification guarantees the provider will not illegally export hazardous e-waste and will maintain a secure, documented process from start to finish.
If a potential partner cannot provide these certifications, there is no independent verification that your data or the environment is being protected.
Essential Questions for Your Vetting Process
Once you have verified certifications, it's time to dig deeper. A provider's answers to these questions will reveal their capabilities and commitment to transparency.
A provider's willingness to give detailed, straightforward answers is a direct reflection of their service quality. Vague responses or an inability to produce documents are major red flags.
Here is a practical checklist of questions to ask every potential IT asset disposition Georgia partner:
- Can you provide a complete, serialized audit report? Ask to see a sample report. A proper report details every asset by serial number, tracking its journey from your facility to its final disposition.
- What does your insurance coverage include? Request a certificate of insurance. Verify they have adequate coverage for general liability, pollution liability, and especially for cyber/data breach liability.
- Do you handle all processing in-house? Inquire about their downstream partners. If they subcontract any part of the process, they must prove that those partners also hold the necessary certifications.
- What is your process for value recovery? Ask how they assess, test, and resell assets. Get details on their revenue-sharing model and how you can track the sales of your equipment.
Using this framework, any Georgia business can confidently select an ITAD partner that provides a secure, compliant, and financially advantageous solution for managing retired technology.
Frequently Asked Questions About IT Asset Disposition in Georgia
When retiring old technology, Georgia businesses often have numerous questions. Getting the right answers is crucial for protecting your company's security, compliance, and financial interests. Here are some of the most common inquiries we receive from clients across the state.
What kinds of IT equipment do you manage?
We handle a full range of commercial-grade IT equipment and electronics for businesses. We do not service residential or consumer electronics.
Our focus is on enterprise-level assets, including:
- Servers, data center hardware, and storage solutions
- Networking equipment (switches, routers, firewalls)
- Business-class laptops, desktops, and workstations
- Specialized medical and laboratory equipment
- Obsolete or excess product inventory requiring destruction
We partner with organizations of all sizes, from a small office in Savannah refreshing a dozen laptops to a major corporation in Atlanta decommissioning an entire data center.
Are your ITAD services available for small businesses in Georgia?
Absolutely. We believe professional ITAD services are essential for businesses of all sizes. Data security and environmental compliance are not just concerns for large corporations. Small and medium-sized businesses are often targeted for data theft because they may lack a formal disposal plan for retired assets.
Our IT asset disposition Georgia services are scalable and designed to be flexible. We provide the same certified data destruction, documented chain of custody, and formal liability transfer for a small business in Macon as we do for a Fortune 500 company in Atlanta.
How can I be certain my company's data is destroyed?
We don't just promise data destruction; we provide a certified, auditable paper trail to prove it. You can select the destruction method that best aligns with your internal security policies and any value recovery goals.
The core of a secure ITAD program isn't just the destruction of data. It's the verifiable proof that it was done correctly. That documentation is your ultimate defense against compliance penalties and data breach liability.
You can choose NIST 800-88 compliant data wiping, which preserves the hard drive for potential resale, or physical hard drive shredding for complete destruction. For maximum assurance, we can perform shredding services on-site at your Georgia facility.
Regardless of the method, we issue a formal Certificate of Data Destruction upon completion. This document lists the serial numbers of every processed drive, serves as your legal proof of compliance, and formally transfers liability from your organization to ours.
Do you provide ITAD pickups outside the Atlanta metro area?
Yes. Our secure logistics services cover businesses across the entire state of Georgia. Our dedicated fleet and professional team coordinate scheduled pickups from any commercial location, ensuring a seamless process whether you are in a major city or a more rural area.
Whether your office is in Columbus, Augusta, or anywhere in between, we maintain a secure chain of custody from the moment the equipment leaves your premises until it arrives at our secure processing facility. Your location within the state is not a barrier to receiving professional, certified ITAD services.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. Contact us today for a secure, compliant, and financially smart solution to manage your company's retired technology.