A network upgrade feels complete when the new gear is live. Then operations opens a cage, a closet, or a warehouse row and finds the actual end of the project. Retired routers, switches, appliances, optics, handsets, and rack equipment are still sitting on your books, still carrying risk, and still consuming space.
That's where ITAD telecom equipment services stop being a disposal task and become an operational control. Telecom hardware retirement touches three things at once: security, compliance, and recoverable value. If you treat it like generic e-waste pickup, you usually lose on all three.
The Strategic Challenge of Retiring Telecom Hardware
A common telecom scenario looks simple on paper. The team completes a core refresh, rolls out newer edge hardware, or consolidates infrastructure after a data center change. Service is stable, the migration window closes, and everyone wants to move on. The old equipment is now the problem nobody planned enough time for.
That gap is expensive in practice. Decommissioned telecom assets often hold configurations, credentials, logs, or embedded storage. They also sit in distributed locations, not just one server room. Some equipment still has remarketing value. Some needs certified destruction. Some can't leave the site until your team confirms service continuity.
Why telecom retirement belongs in the project plan
The market itself shows how central this work has become. Grand View Research estimated the global IT asset disposition market at USD 25.31 billion in 2024, and the IT & telecom segment accounted for over 30.0% of market revenue according to its IT asset disposition market analysis. Telecom isn't a side category in ITAD. It's one of the major demand drivers.
That lines up with what IT directors already see on the ground. Modernization cycles create waves of retired infrastructure, not a few leftover office devices. If you're evaluating future network design choices, it also helps to compare business-grade VoIP solutions with an eye on what those platforms will eventually require at end of life.
Practical rule: If disposition starts after cutover, you're already behind. The best telecom refresh plans define removal, tracking, sanitization, and resale criteria before the first asset is unplugged.
What a strategic response looks like
A disciplined program starts with asset lifecycle thinking, not truck scheduling. That means mapping what gets redeployed, what gets wiped for resale, what gets physically destroyed, and what gets recycled under documented custody. A formal IT asset lifecycle management approach helps prevent the usual last-minute scramble.
Busy teams usually feel the pressure in three places:
- Security exposure: Retired network gear may still contain sensitive data.
- Audit pressure: Procurement, legal, and compliance teams want proof, not assurances.
- Locked-up value: Reusable assets lose resale potential when they sit untested for too long.
Telecom ITAD works best when it's treated as a controlled exit path for infrastructure, not as cleanup after the “real” project ends.
What Differentiates Telecom ITAD from Office ITAD
Office ITAD is mostly about endpoints. Telecom ITAD deals with infrastructure. That difference changes everything from removal planning to data sanitization to resale strategy.

The asset mix is completely different
A standard office project usually centers on laptops, desktops, monitors, and printers. Telecom environments add a more complex mix:
- Carrier and enterprise networking gear: Routers, switches, firewalls, WAN appliances
- Compute and storage tied to telecom workloads: Blade servers, SAN/NAS units, edge systems
- Voice and transport equipment: PBX hardware, gateways, conference systems, handsets
- Infrastructure components: Transceivers, power supplies, rack equipment, specialized modules
These assets often carry more residual value than office devices. They also require more technical evaluation before anyone can decide between resale, redeployment, destruction, or recycling.
The data risk isn't always obvious
Many telecom assets don't look like traditional data-bearing devices. That's where mistakes happen. A router may hold startup configurations. A firewall may retain credentials and logs. A voice platform may contain user, call, or provisioning data. A storage-connected telecom appliance can carry far more than the team remembers.
What fails is the “factory reset and load it out” approach. What works is treating any production network asset as sensitive until its storage profile and sanitization path are confirmed.
A switch that no longer forwards traffic can still create a security incident if its configuration leaves your control.
Value recovery is stronger when equipment is graded properly
Telecom hardware also behaves differently financially. Evertrade notes that value recovery is strongest when infrastructure-grade assets such as servers, routers, and switches are graded for refurbishment, and the resale channel can reduce or completely offset logistics and destruction costs on large refreshes in its explanation of ITAD value recovery and refurbishment.
That's why office-style recycling programs underperform in telecom settings. Scrap-only thinking destroys value that may still exist in line cards, tested switches, rackmount servers, optics, and clean spare units.
A quick comparison makes the distinction clearer:
| Environment | Primary concern | Better disposition path |
|---|---|---|
| Office endpoints | Basic data security and recycling | Standard wipe, recycle, or redeploy |
| Telecom infrastructure | Service continuity, embedded data, value recovery | Serialized tracking, technical grading, secure sanitization, remarketing or certified recycling |
Telecom equipment needs a provider that understands networks, not just electronics pickup.
The End-to-End Workflow for Telecom Assets
The safest telecom ITAD projects run like controlled change management. Removal happens in sequence. Custody is documented at each handoff. Sanitization decisions match the asset type. Final reporting ties back to the original inventory.
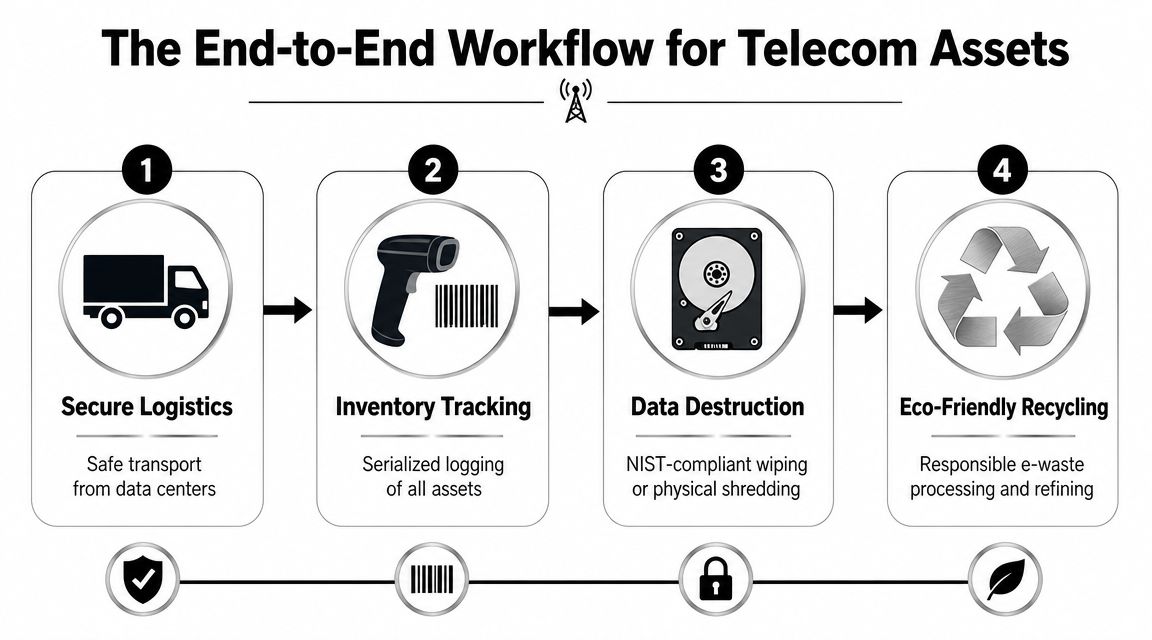
Step one is coordinated de-installation
Telecom gear can't just disappear from racks because a pickup window is available. The removal plan has to respect maintenance windows, cutover timing, and site access restrictions. Devices are usually tagged, counted, and staged in a way that preserves traceability back to the production environment.
Rapidsolutions notes that telecom ITAD has to integrate with network refresh cycles to prevent downtime, using staged removal, detailed inventory reconciliation, and chain-of-custody controls before any resale, reuse, or recycling decision in its write-up on telecommunications ITAD services.
That's the difference between a smooth exit and a post-project fire drill.
Step two is custody-controlled transport
Once assets leave the rack, the risk profile changes. Internal teams need to know what left, who released it, who received it, and where it went next. Good operators document this at item level whenever practical, especially for serialized network gear.
A structured data center decommissioning process usually gives the cleanest model because it forces logistics discipline. For telecom environments, that same discipline matters in MDFs, IDFs, branch locations, and field returns.
What works in this phase:
- Serialized manifests: Match pickup records to processing records
- Secure packaging: Protects equipment condition and preserves resale potential
- Defined handoffs: Named custody points reduce disputes later
Step three is the data destruction decision
That is where many programs get sloppy. Not every asset should be shredded. Not every asset should be wiped for reuse. The right path depends on the device, the data risk, internal policy, and whether remarketing is realistic.
A practical decision view looks like this:
| Asset condition and risk | Common approach |
|---|---|
| Reusable asset with manageable data risk | Auditable data wiping or erasure before remarketing |
| Device with higher sensitivity or uncertain storage state | Physical destruction of data-bearing components |
| Non-viable equipment with no resale path | Material recovery through certified recycling |
Field reality: The wrong destruction choice creates two kinds of loss. Under-secure the asset and you create liability. Over-destroy it and you erase value you could have recovered.
Step four is testing and grading
Once data handling is complete, viable telecom equipment should be tested and graded by people who know what the asset is. A stack of decommissioned switches is not one commodity lot. Condition, completeness, model relevance, module population, and cosmetic state all matter.
This phase determines whether the asset goes to:
- Internal redeployment
- Secondary market resale
- Component harvesting
- Certified recycling
The best recovery programs don't assume every item should be sold. They separate units that can move cleanly through refurbishment from those that will consume labor without returning enough value.
Step five is recycling and final reporting
Anything that doesn't make sense to resell still needs proper downstream handling. That means responsible material processing plus documentation your audit, finance, and sustainability teams can confidently use.
A complete closeout package usually includes:
- Asset reconciliation records
- Data destruction documentation
- Certificates tied to the disposition path
- Recycling support records for non-resalable equipment
A telecom ITAD workflow is only complete when the paperwork closes the loop on the physical work.
Maximizing Value Recovery from Retired Network Gear
Many IT directors still inherit a bad assumption from old disposal programs. The assumption is that retired telecom gear is mostly a cost to remove. In reality, a meaningful share of network hardware sits in the narrow but valuable middle ground between “still in production” and “only worth scrap.”

Why timing matters more than most teams expect
Refresh cycles are tightening. Mordor Intelligence says AI-optimized architectures are shortening hardware refresh intervals to 18 to 24 months, and Cascade Asset Management reported a second consecutive year of double-digit increases in average resale values for refurbished assets in the North America ITAD market analysis. For telecom operators, that creates two realities at the same time. More gear exits production faster, and more of that gear may still have a viable resale window.
That window doesn't stay open forever. Equipment loses value when it sits untested, incomplete, or poorly documented. Missing rails, absent power supplies, unknown config history, and rough handling all reduce recoverable return.
What usually holds value
Not every retired asset deserves refurbishment effort. The strongest candidates are typically infrastructure-grade items with active secondary demand and enough remaining useful life to justify testing.
Common examples include:
- Current or recently retired switches and routers
- Servers tied to telecom or edge workloads
- Modules and transceivers with clean provenance
- Power supplies and compatible spare components
- Complete rack units with known serials and accessories
A practical liquidation path can include outright purchase, consignment, or revenue sharing. Teams comparing options often review telecom equipment liquidation services to understand how providers separate resale from recycle-only material.
What gets in the way of recovery
The biggest value killers are operational, not market-based.
| Value obstacle | Why it hurts |
|---|---|
| Poor inventory data | Buyers won't pay confidently for unknown lots |
| Mixed condition staging | Good units get dragged down by damaged or incomplete gear |
| Delayed sanitization decisions | Remarketable gear sits idle |
| Scrap-first handling | Reusable equipment loses resale potential |
The highest-return telecom projects usually start before shutdown. Teams identify resale candidates while the gear is still installed, not after everything has been piled onto pallets.
A good recovery program doesn't promise that every asset will pay for its own exit. It does something more useful. It separates value-bearing hardware from liability-bearing hardware early enough to make both decisions well.
Navigating Security Compliance and Documentation
Security language in ITAD proposals is usually too broad to be useful. “Secure destruction.” “Compliant recycling.” “Full chain of custody.” Those phrases don't help much when your auditors ask how a firewall, phone system appliance, or SAN-connected network device was sanitized and how that proof ties back to a serial number.

The real compliance gap is evidence
The weak point in telecom disposition isn't usually intent. It's documentation. Human-I-T notes a critical gap around how operators document destruction of data from network gear, and says organizations should require clear evidence such as detailed certificates of destruction to satisfy auditors and rules including the FTC Disposal Rule in its overview of what ITAD includes.
That matters because telecom devices don't always fit the simple hard-drive model people expect. You may be dealing with embedded storage, removable media, cached credentials, call records, customer metadata, or configuration backups that weren't obvious to the operations team during removal.
What to require in the paperwork
A certificate should do more than confirm that “materials were destroyed.” For telecom assets, useful evidence is specific enough to stand up to internal review.
Look for records that identify:
- Which assets were processed: Model or serial reference where available
- What happened to them: Wiped, shredded, recycled, or remarketed after sanitization
- When destruction occurred: Date of service and processing confirmation
- Who handled the work: Custody trail from release through final disposition
If a provider offers a sample certificate of destruction format, review whether it supports reconciliation, not just whether it looks official.
Wiping versus physical destruction
Teams need policy, not improvisation, when managing these scenarios. If equipment has strong resale potential and your risk model allows it, auditable wiping may be enough. If the device class has uncertain storage behavior, a higher sensitivity profile, or limited reuse value, physical destruction is usually the cleaner answer.
A practical comparison:
| Method | Better fit |
|---|---|
| Documented wiping or erasure | Reuse and resale scenarios where sanitization is verifiable |
| Physical destruction | Sensitive assets, uncertain storage states, or no reuse case |
What doesn't work is applying one method to everything because it's operationally easier.
Audit mindset: Your standard shouldn't be “Would this satisfy the vendor?” It should be “Would this satisfy legal, security, and an external auditor six months from now?”
Chain of custody has to survive every handoff
Most documentation failures happen between pickup and processing. The manifest is vague. The serial list is incomplete. The certificate arrives later with broad language and no easy way to match it back to the released assets.
That creates avoidable disputes. Strong telecom ITAD programs protect themselves with release records, item-level or lot-level traceability, sanitization evidence, and final reconciliation that closes every open question. The point of documentation isn't administrative comfort. It's liability transfer backed by evidence.
A Checklist for Selecting Your Telecom ITAD Partner
Vetting a telecom ITAD provider is less about the sales deck and more about process maturity. A capable partner should be able to explain how it handles telecom-specific assets, not just general electronics recycling. If the answers stay generic, keep looking.
Questions that expose real capability
Use a shortlist that forces operational detail. A telecom provider should be able to answer these without hesitation:
- Telecom asset experience: Ask which types of routers, switches, PBX systems, servers, and voice gear they handle regularly.
- Onsite versus offsite options: Some projects need onsite data destruction or staged de-installation. Others don't.
- Inventory control: Require sample manifests and ask how discrepancies are resolved.
- Sanitization decisioning: Ask how they determine wiping versus physical destruction by device class.
- Downstream visibility: They should explain what happens to recycle-only assets after initial processing.
A structured vendor due diligence checklist helps procurement and security teams ask the same questions using the same criteria.
What strong vendors usually provide early
You shouldn't have to fight for the basics. Mature providers usually share documentation samples, service scopes, and reporting examples during the evaluation stage.
Look for these signs:
- Clear service boundaries: Pickup, de-installation, packing, testing, destruction, and resale are defined
- Audit-ready reporting: The provider can show how custody and final disposition are documented
- Flexible financial models: They can explain purchase, consignment, or net recovery structures without vague fee language
Red flags worth treating seriously
Some disqualifiers are obvious once you know what to watch for.
| Red flag | Why it matters |
|---|---|
| “We wipe everything” with no method detail | Security process may be informal |
| No sample certificate or manifest | Reporting may not support audits |
| Generic telecom experience claims | Risk of mishandling specialized hardware |
| Immediate buyback promises without grading logic | Financial expectations may not hold up |
The right partner doesn't just remove retired hardware. The right partner helps you prove what happened to every important asset.
Adopting a Strategic Approach to Telecom Asset End of Life
Telecom hardware retirement sits at the intersection of operations, security, finance, and compliance. That's why generic recycling language falls short. Routers, switches, firewalls, voice systems, and edge infrastructure require a process that protects service continuity during removal, preserves evidence during custody transfer, and captures residual value where the market supports it.
The strongest programs make a few decisions early. They identify which assets are likely to be remarketed. They decide when wiping is acceptable and when destruction is mandatory. They require reporting detailed enough for auditors, not just warehouse staff. They also treat inventory accuracy as part of the control framework, not a clerical task.
Specialized ITAD telecom equipment services address these specific challenges. A provider that understands infrastructure-grade assets can reduce project friction in practical ways. Fewer custody gaps. Better separation between resale candidates and recycle-only material. Cleaner documentation for legal, security, and procurement teams.
There's also a broader management benefit. Once telecom disposition is formalized, future refreshes get easier. Teams know what data to capture before cutover. Facilities knows how staging should work. Finance has a clearer model for recovery versus expense. Security gets predictable evidence instead of last-minute exceptions.
If you're planning a network refresh, voice migration, data center consolidation, or field hardware replacement, build the ITAD workstream into the project now. That's how you avoid turning retired infrastructure into an avoidable risk pool.
If you need a practical next step, contact Beyond Surplus to discuss certified electronics recycling, secure IT asset disposal, telecom equipment disposition, and audit-ready reporting for retired business hardware.