A telecom liquidation project usually lands on someone's desk after a merger closes, a carrier shuts down a legacy footprint, or a network refresh moves faster than the old estate can be cleared. At that point, the pressure is immediate. Finance wants recovery, operations wants space back, security wants proof that no data-bearing device left uncontrolled, and legal wants a clean record for every asset.
That's why large-scale telecom equipment liquidation has to be managed as an asset recovery program, not a warehouse cleanup. Telecom environments combine high-value hardware, fragmented site inventories, retired but still regulated media, and logistics that often stretch across multiple sites. The organizations that handle this well treat liquidation as a scoped project with decision gates, documentation, and a defined end state for each asset.
Framing the Liquidation Challenge
A data center or telecom manager rarely starts with a neat stack of labeled pallets. More often, the project begins with mixed racks, field returns, spares from prior upgrades, and equipment that hasn't been touched since the last migration window. Some of it still has resale potential. Some of it belongs in parts harvest. Some of it can't move until data destruction requirements are signed off.

The scale of the market explains why liquidation can become a serious operational event. The global telecom equipment market was valued at USD 314.6 billion in 2024 and is forecast to reach USD 603 billion by 2034, with North America accounting for more than 35% of the market in 2024. That matters because every refresh, consolidation, and decommission releases switches, routers, optical gear, and radio equipment into secondary channels.
A lot of teams still approach this as “find a buyer for old gear.” That's too narrow. A proper liquidation plan has to answer harder questions first:
- What's on hand: not just model counts, but exact serials, locations, and condition
- What carries data risk: SSDs, controllers, appliances, removable media, and anything embedded
- What has the highest recovery path: resale, redeploy, parts harvest, or certified recycling
- What documentation is required: internal finance records, chain-of-custody, certificates, and final disposition reporting
Practical rule: If the project starts with trucking arrangements before inventory and test criteria are agreed, value and control usually fall apart at the same time.
There's also a strategic difference between disposal and liquidation. Disposal focuses on removing retired assets safely. Liquidation focuses on recovering value while controlling security, compliance, and timing risk. That distinction changes everything from how the inventory is built to which partner handles transport.
For organizations dealing with a network shutdown, M&A integration, or a broad decommission, a structured telecom liquidation services workflow is usually the difference between an auditable recovery project and a rushed asset dump. The latter may clear floor space quickly, but it often leaves money behind and creates unnecessary exposure.
Phase One Strategic Scoping and Inventory
The first mistake in telecom liquidation is touching equipment too early. If technicians begin pulling gear before the asset map is stable, the team loses provenance, mixes value tiers, and creates avoidable disputes over what was removed from which site.
Build the inventory before the trucks move
A workable inventory isn't a simple line count. It needs enough detail to support valuation, data handling, and reconciliation later. For each asset, capture:
- Manufacturer and model: needed for marketability and compatibility screening
- Serial number or unique identifier: the backbone of chain-of-custody
- Configuration details: cards, optics, memory, power supplies, licenses if transferable
- Physical condition: clean pull, damaged, incomplete, or unknown
- Exact location: building, floor, room, row, rack, and position where possible
- Status: active, retired, spare, failed, cannibalized, or staged
- Data-bearing risk: yes, no, or requires verification
A spreadsheet can work for a small project. Large telecom estates need tighter controls. Use a structured asset register and lock down naming conventions before the field team starts. If one site records “ASR chassis” and another records “Cisco router,” reporting quality drops fast.
Classify assets by recovery path early
Scoping has to do more than identify equipment. It has to decide what each item is likely to become. Teams that skip this classification usually send too much into low-value channels.
Use four initial buckets:
Resale
Best for newer, complete, in-demand equipment with clean provenance and no unresolved data issue.Redeploy
Often overlooked. Internal reuse can be the right answer when lead times, sparing strategy, or project timelines matter more than immediate cash.Parts harvest
Useful for incomplete systems, damaged enclosures, or platforms with secondary demand for components.Scrap or certified recycling
The correct path for end-of-life assets, unsupported gear, and items that fail economic test thresholds.
Fast liquidation without triage usually turns profitable hardware into scrap pricing.
The telecom industry has seen what happens when assets are dumped into the market without disciplined scoping. During the early-2000s telecom bust, the industry lost about $2 trillion in market capitalization, and operators were forced to shed assets quickly. The lesson still applies. Speed without structure widens losses.
Define the rules before de-install
A solid scope document answers operational questions that people otherwise settle on the fly:
| Scope item | Why it matters |
|---|---|
| Test standard | Determines resale eligibility and pricing confidence |
| Media handling rule | Prevents disputes over wipe, shred, or quarantine |
| Packaging standard | Reduces transit damage and mixed-load errors |
| Exception process | Keeps unidentified or damaged assets from disappearing into “miscellaneous” |
| Approval path | Stops field improvisation when an unexpected device appears |
For organizations managing broad technology retirement, this work fits naturally into a wider IT asset lifecycle management process rather than a one-off warehouse event. That's how you avoid the common pattern of finding missing serials, unlabeled drives, and unplanned scrap after the equipment has already left the building.
Phase Two Secure Decommissioning and Data Sanitization
Once scope is locked, the work shifts from planning to controlled execution. In this phase, projects either stay clean or become chaotic. The biggest operational risk isn't usually the rack removal itself. It's losing asset identity and data control during fast de-install.

Control the floor before equipment leaves the rack
Telecom rooms and data halls often contain a mix of retired and adjacent production systems. That means decommissioning has to be sequenced with discipline. Good teams label before disconnecting, isolate assets by disposition stream, and verify serial capture at the rack, not later in a staging area.
The practical sequence usually looks like this:
- Tag and verify first: confirm asset identity against the approved inventory
- Power down under site rules: especially where shared circuits or dependent systems remain nearby
- Remove and stage by class: resale, media quarantine, recycle, or exception
- Preserve assemblies where possible: buyers usually prefer complete, undamaged units
- Document exceptions immediately: missing drives, broken rails, and mismatched labels should never wait until day-end
One bad habit shows up constantly in rushed projects. Teams stack loose drives, transceivers, and cards in generic bins “for sorting later.” Later rarely comes with perfect accuracy.
Match the sanitization method to the media
Telecom gear isn't just chassis and line cards. It often includes SSDs, HDDs, embedded flash, controller modules, and appliances that can retain configuration or user data. That's why one destruction method doesn't fit every device.
The three main options are:
Certified data wiping
Best when the media is functional and resale or redeploy is still possible. This preserves asset value because the device remains usable after sanitization.Degaussing
Appropriate for certain magnetic media where the goal is destruction of recorded data, not reuse. It's a terminal choice for many devices.Physical shredding
The right answer when media is failed, high risk, or governed by strict destruction requirements. It also resolves uncertainty when a device can't be reliably wiped.
A certificate only has value if the underlying process is controlled, repeatable, and tied back to a specific asset record.
Organizations that require defensible wiping standards generally align to NIST SP 800-88 guidance for media sanitization. The point isn't the acronym. The point is having a method that compliance, legal, and auditors can accept without argument.
Don't separate data proof from asset proof
A common reporting gap appears when the equipment inventory sits in one system and the data destruction records sit in another. If those records can't be tied together cleanly, the final package becomes much less useful.
Keep these links intact from day one:
- asset identifier to media identifier
- media identifier to sanitization method
- sanitization result to certificate or destruction record
- certificate to final disposition outcome
That linkage is what transfers operational confidence into documented compliance. Without it, a telecom liquidation may still remove hardware from the site, but it won't close the risk.
Phase Three Valuation and Channel Selection
Value recovery in telecom liquidation comes from matching the asset to the right outlet. That sounds obvious, but many losses come from channel mistakes, not market conditions alone. A clean, testable router sold through the wrong channel can perform worse than an average unit sold through the right one.
What drives value
Buyers usually care about a few things immediately: age, demand, completeness, physical condition, test status, and whether the asset comes with clean documentation. Missing faceplates, rails, power modules, or transceivers can change the outcome quickly. So can uncertainty about whether storage was sanitized correctly.
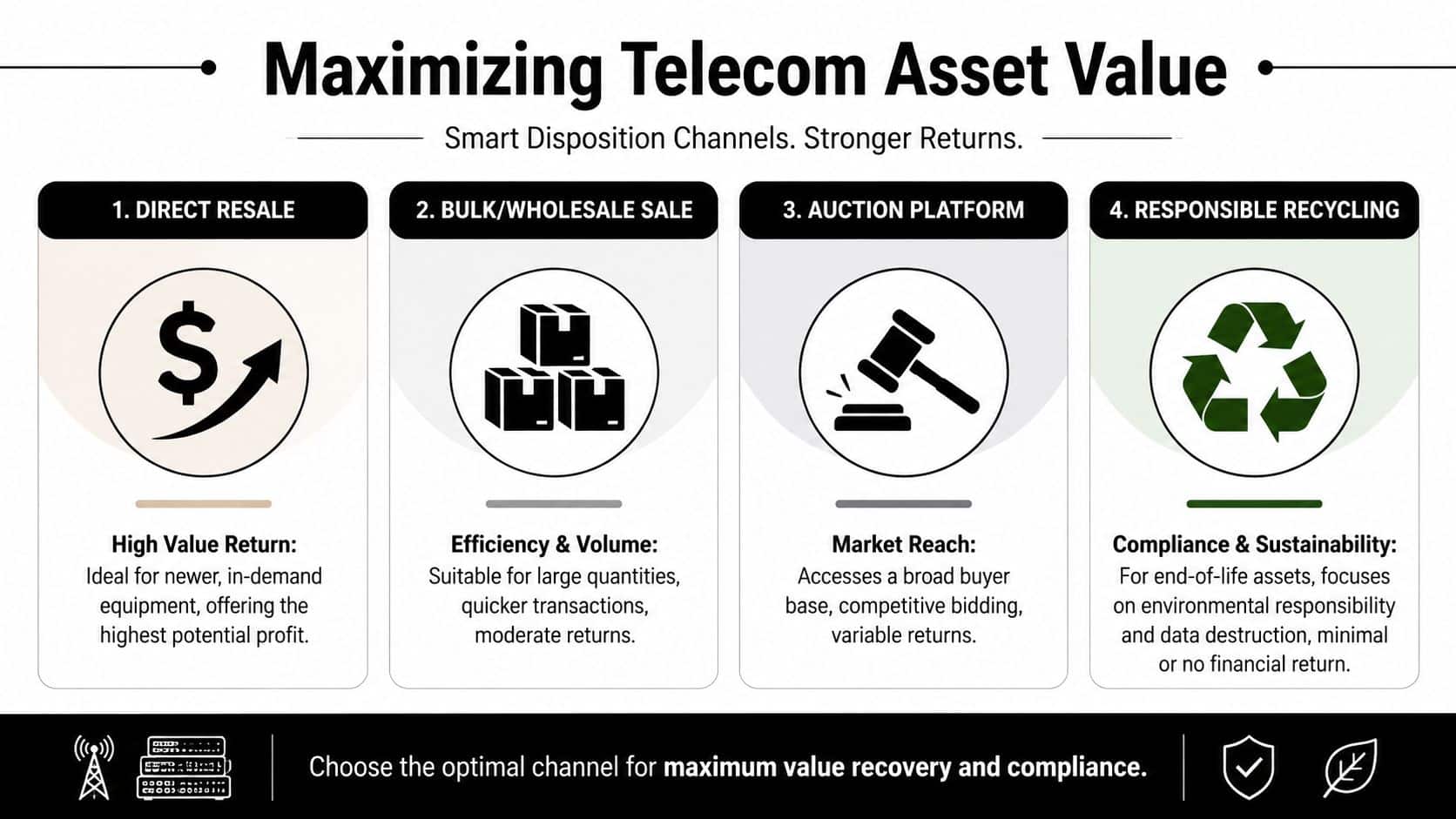
The strongest liquidation programs classify for channel fit, not just for ownership transfer. That's why teams without a strategic process often struggle. According to telecom asset recovery guidance from Beyond Surplus, companies without a strategic ITAD program often recover only 10-20% of asset value, while professionally managed, data-wiped telecom assets can retain 40-60% of resale value.
Choose the outlet that fits the asset
Different channels solve different problems.
Direct resale works when equipment is current enough, complete enough, and documented enough to justify targeted marketing. This tends to suit cleaner enterprise and carrier-grade equipment with visible buyer demand.
Bulk or wholesale sale trades margin for speed. It's often the right call when the seller wants rapid conversion, mixed lots need to move together, or labor costs would overwhelm a more selective strategy.
Auction platforms increase exposure, but they also increase variability. They can help where the asset mix is unusual or broad, yet they aren't a cure for poor inventory quality.
Responsible recycling is the correct endpoint for assets that no longer pass the economics of remarketing. It's not a failure. It's disciplined triage.
A useful way to think about this comes from adjacent secondary markets. Even in smaller categories, sellers who want a simple transaction often use specialized channels such as this guide on how to sell your consoles, while higher-value or more complex inventory may justify a more selective route. Telecom liquidation works the same way, just with far higher documentation and compliance stakes.
Distressed sales are their own category
Many internal stakeholders compare liquidation proceeds to purchase price or book value. That comparison often creates unrealistic expectations. In distressed conditions, urgency changes everything.
A current route for sellers that want structured recovery is working with nationwide telecom equipment buyers who can separate remarketable gear from lower-yield material and document the outcome. That still doesn't change a hard truth. If the seller is under creditor pressure, timeline pressure, or court constraints, the market will price that urgency.
Liquidation value is not a historical cost discussion. It's a timing, condition, and marketability discussion.
That's why finance teams should ask better questions than “What did we pay?” The better questions are: What can be tested? What can be sold intact? What must be destroyed? Which channel can absorb volume without crushing price? Those answers drive recovery.
Phase Four Logistics and Final Reconciliation
Many telecom liquidation projects are damaged after the hardware has already been removed from the rack. The mistake is treating logistics as a freight problem instead of a control problem. Once assets start moving across buildings, state lines, yards, and processing centers, the audit trail has to move with them.

Serialized packing beats generic shipping
Pallet counts aren't enough for high-stakes liquidation. What matters is the relationship between the item removed, the container it entered, the carrier that took possession, and the facility that received it.
Good projects use handling controls such as:
- Serialized pallet or container IDs: so the shipment can be reconciled at receipt
- Tamper-evident labeling where needed: especially for media-bearing assets
- Separated load plans: resale, quarantine, and scrap shouldn't travel as an anonymous mix
- Signed custody transfers: each handoff should identify who released and who received the assets
When teams skip this, they create avoidable blind spots. A missing chassis becomes a freight claim instead of a traceable exception. A destroyed drive becomes impossible to connect back to the original device record.
Multi-state movement raises the documentation bar
This issue gets harder on nationwide projects. Different sites may have different internal standards, and regulated equipment may move through multiple handlers before final processing. The safest operating model is the one that can survive the toughest review.
Beyond Surplus notes in its telecom asset recovery services guidance for USA projects that the key challenge is managing cross-border and multi-state chain-of-custody and proving destruction, and that the safest approach is to build an audit trail that meets the most demanding likely requirement. That's the right standard. It keeps one weak site process from compromising the whole project.
If your chain-of-custody depends on memory, screenshots, or email threads, you don't have a chain-of-custody. You have a reconstruction exercise.
Final reconciliation closes the project
The most useful deliverable in a liquidation program is the final reconciliation file. It should answer one question for every asset: what happened to it?
That package typically includes:
| Reconciliation element | What it proves |
|---|---|
| Original inventory record | The asset existed in the project scope |
| Pickup or de-install record | The asset left the site under control |
| Receipt confirmation | The downstream facility took possession |
| Test or grading result | The asset's condition and channel eligibility |
| Data destruction record | Media was sanitized or destroyed properly |
| Final disposition | Resold, redeployed, harvested, recycled, or destroyed |
Organizations planning a formal shutdown or migration usually need this level of documentation built into the data center decommissioning process, not bolted on afterward. Reconciliation is where operational work becomes defensible reporting.
Choosing the Right ITAD Partner
Vendor selection goes wrong when procurement treats telecom liquidation like commodity hauling. The low quote can become the expensive option if the provider can't control de-install labor, sanitize media correctly, or produce a defensible final report.
What to verify before award
Start with capability, not marketing claims. The provider should be able to explain how it handles serialized intake, media control, test criteria, exception processing, and downstream reporting in plain language. If the answers stay vague, assume the execution will be vague too.
Look carefully at these areas:
- Certifications and compliance posture: ask which standards govern recycling, data destruction, and environmental handling
- Insurance: verify coverage relevant to pollution and data exposure
- Logistics capability: especially for multi-site rollouts and sensitive freight
- Reporting discipline: sample certificates are helpful, but sample reconciliation files are better
- Downstream transparency: know where assets go for resale, harvest, and recycling
ITAD Partner Vetting Checklist
| Evaluation Category | Key Questions to Ask | Look For (Green Flags) |
|---|---|---|
| Certifications | Which certifications govern your recycling and data destruction processes? | Clear, current certifications and staff who can explain how they apply operationally |
| Data sanitization | How do you decide between wiping, degaussing, and shredding? | A documented decision tree tied to media type and client requirements |
| Chain-of-custody | How is custody recorded from site removal through final disposition? | Serialized tracking, signed handoffs, and auditable records |
| De-install capability | Do you use trained crews for rack removal and site staging? | A defined floor procedure with labeling, staging, and exception handling |
| Value recovery | How do you route assets into resale, redeploy, parts harvest, or recycling? | Channel logic based on condition, demand, and compliance constraints |
| Reporting | What does the final client report include? | Asset-level reconciliation, certificates, settlement detail where applicable |
| Downstream vendors | Who handles material that you don't process directly? | Identified downstream partners and documented controls |
| Insurance and liability | What policies do you carry for data and environmental exposure? | Relevant coverage with proof available during diligence |
Price matters, but scope clarity matters more
A strong RFP should force bidders to describe process detail, not just pickup speed and revenue share. Ask how they handle unlabeled media, mixed site inventories, damaged gear, and court or stakeholder reporting requirements. Those edge cases are where weak vendors fail.
One provider option in this space is Beyond Surplus, which offers telecom liquidation, secure data destruction, logistics coordination, and serialized reporting for business projects. Whether you evaluate that firm or another one, the standard should stay the same. Choose the partner that can document control, not just remove equipment.
Frequently Asked Questions on Telecom Liquidation
How much value should we expect in a distressed telecom liquidation
Expect realism, not book-value recovery. In a distressed sale, urgency, court process, buyer appetite, and asset condition shape proceeds more than original purchase cost. A recent example reported by Wireless Estimator described assets with book value over $361 million selling for about $22 million. That's a reminder that liquidation pricing follows market conditions and seller pressure.
What documentation should we demand at the end
Ask for an asset-level reconciliation package. It should tie original inventory to pickup, receipt, test outcome where relevant, data destruction evidence, and final disposition. If the project spans multiple sites, require a format that lets you filter by site, asset class, and disposition stream.
Can we mix resale and scrap in the same project
Yes, and most telecom projects should. A blanket rule usually destroys value. The better approach is controlled triage, with each asset assigned to the highest defensible recovery path after identity, condition, and data risk are verified.
Is certified data destruction still necessary if the equipment is old
Yes. Age doesn't eliminate data risk. Old network appliances, storage modules, and embedded media can still hold credentials, configs, logs, or customer-related information. If the media can't be verified as clean, treat it as a liability first and an asset second.
What causes liquidation projects to fail most often
The recurring failures are basic but expensive: incomplete inventories, unidentified storage media, poor labeling at removal, and transport arranged before disposition rules are agreed. Most of the serious downstream problems start with one of those mistakes.
Contact Beyond Surplus if your organization needs a documented plan for large-scale telecom equipment liquidation, secure data destruction, nationwide pickup coordination, and auditable final reporting.