A lot of telecom gear doesn't leave the business when the project ends. It moves to a cage, a branch closet, a staging room, or a warehouse corner. Then it sits there. Old Cisco switches, transport shelves, handsets, optics, PDUs, routers, and cards slowly turn from “might use later” into a balance-sheet blind spot.
That's where telecom equipment asset recovery services matter. This isn't just disposal with better branding. Done properly, asset recovery converts retired hardware into recovered value, documented compliance, and cleaner operations. Done poorly, it creates write-downs, audit problems, and avoidable security exposure.
Enterprise IT directors usually inherit this problem midstream. A network refresh is complete, a site consolidation is underway, or a carrier migration leaves racks of gear behind. The hard part isn't identifying that the equipment is obsolete. The hard part is deciding what still has resale value, what must be sanitized, what can be refurbished, and what needs certified recycling without losing control of the chain of custody.
Turning Retired Telecom Hardware into a Strategic Asset
In most organizations, retired telecom hardware becomes someone else's future task. Operations wants the room back. Finance wants write-offs closed. Security wants assurance that no config data, subscriber records, or routing information survives on the equipment. Procurement wants to know whether anything can be monetized.

That pressure is one reason the category keeps expanding. The asset recovery services market analysis values the global market at USD 14.73 billion in 2025 and projects USD 30.95 billion by 2034, with 8.6% CAGR, while identifying IT and Telecom as the second-most dominant end-user segment. That lines up with what enterprise teams see on the ground. Telecom environments turn over quickly, and retired hardware piles up faster than many disposal workflows can handle.
Why telecom gear is different
Telecom equipment doesn't behave like generic office IT. Secondary value depends on software state, port health, optics compatibility, module completeness, and whether the gear came out cleanly. A router with bent ears, missing cards, or unknown firmware can move from resale candidate to parts donor fast.
For organizations planning broader voice and network modernization, a practical reference point is this Hosted Telecommunications business phone guide, which helps frame why legacy telecom estates often shrink in waves rather than all at once. That matters because recovery programs work better when they're tied to migration milestones, not left for end-of-year cleanup.
What changes when you treat it as a program
A formal program does three things at once:
- Recovers value from hardware that still has market demand
- Reduces risk through documented data destruction and recycling records
- Prevents sprawl by moving assets out of storage before they lose condition and marketability
Practical rule: The longer decommissioned telecom gear sits untested, the more likely your organization treats an asset recovery problem like a junk removal problem.
Teams that need a starting point often begin by mapping retired inventory against a remarketing path such as selling surplus telecom hardware. That shift in mindset is usually the definitive turning point. Once retired network gear is classified as recoverable inventory rather than waste, better decisions follow.
The Complete Telecom Asset Recovery Workflow Explained
Most failed recovery efforts break at handoff points. Inventory is incomplete. Equipment is pulled without enough labeling. Storage media isn't identified. Logistics are arranged before testing criteria are agreed. A professional workflow avoids that by controlling each stage from assessment through final reporting.
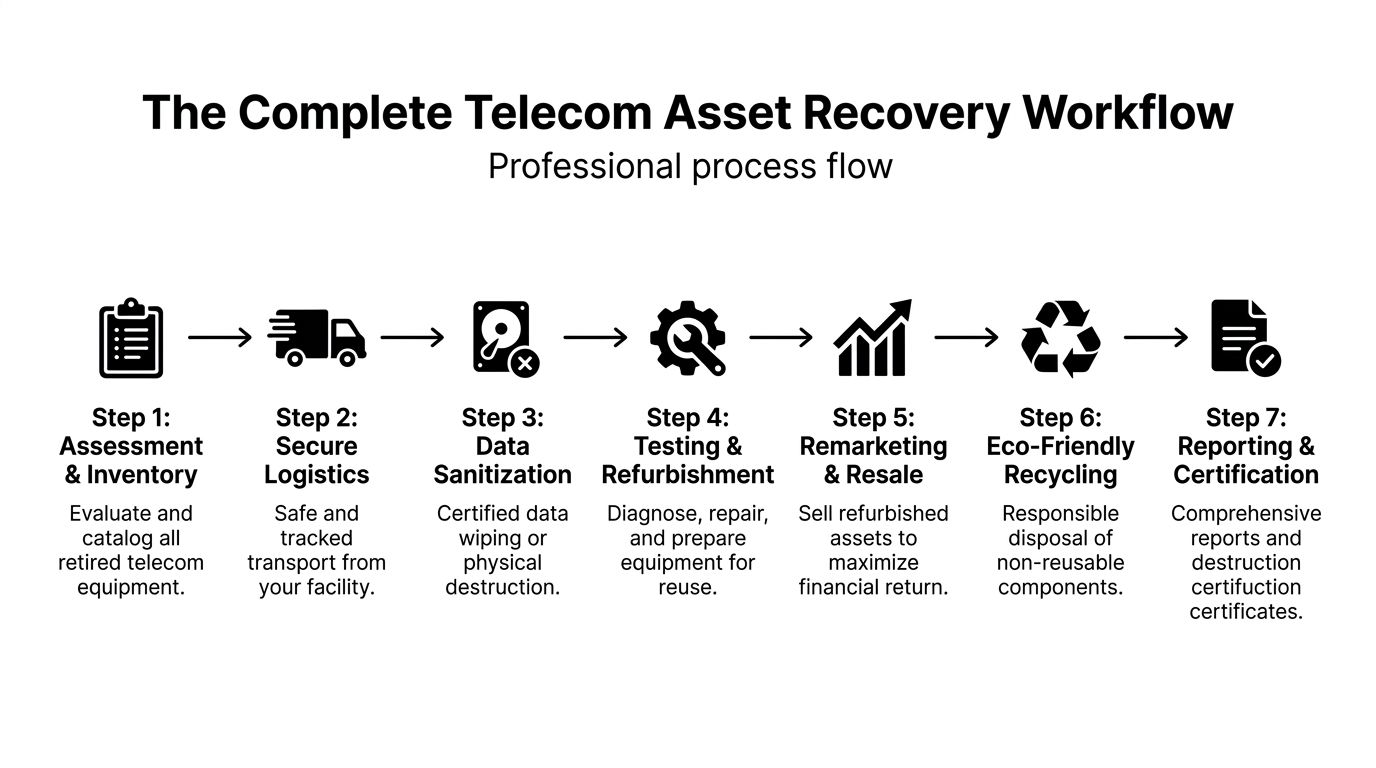
Assessment and inventory
The job starts with an asset list, but not just a spreadsheet of model numbers. Good assessments capture serial numbers, installed modules, power supplies, cosmetic condition, storage components, and whether the equipment is still in-rack, already palletized, or disconnected and loose.
That detail matters because de-installation damage alone can cause 20-40% failure rates, and professional diagnostics can determine repairability with over 80% precision, according to telecom asset recovery screening guidance. If you don't know what condition the gear is in before movement, you lose both pricing advantage and planning accuracy.
Secure logistics and chain of custody
Once equipment is identified, logistics need to preserve value and accountability. Telecom gear often travels poorly when crews use generic removal practices. Blades get separated from chassis. Rails and faceplates disappear. Optics get mixed into unlabeled bins.
A disciplined pickup process usually includes:
- Site preparation so teams know what stays, what goes, and what must be wiped first
- Packaging controls for shelves, cards, handsets, and fragile components
- Tracked transport with documented custody from site release to processing
- Receipt verification so the asset list is reconciled against what arrived
Gear loses value in transit more often than executives realize. A careful de-install crew protects residual value before the remarketing team ever sees the equipment.
Data sanitization and technical processing
Telecom equipment can store more than people expect. Config files, credentials, routing tables, customer data, and management access details may live on drives, flash modules, controllers, or embedded storage. That's why sanitization has to be planned by asset type, not handled as a generic wipe event.
At the processing facility, assets are typically separated into categories:
- Network hardware with removable or embedded storage
- Handsets and end-user telecom devices
- Transport and optical equipment
- Damaged assets for parts harvesting or recycling
Testing follows sanitization or approved physical destruction. Functional units move to grading. Marginal units may be refurbished. Failed units are stripped for recoverable components or routed to recycling streams. Buyers evaluating telecom equipment liquidation options should ask for this triage logic in writing, because it determines whether value is created or discarded.
Disposition paths that actually work
Not every retired asset belongs in the same channel.
| Path | Best fit | What good providers look for |
|---|---|---|
| Direct resale | Clean, tested, current-demand gear | Complete units with known provenance |
| Refurbishment | Repairable equipment with market demand | Module swaps, firmware checks, cosmetic remediation |
| Parts harvesting | Incomplete or failed systems with valuable subcomponents | Optics, power supplies, fans, cards |
| Certified recycling | Broken, obsolete, or nonviable equipment | Material recovery with environmental documentation |
The key is triage discipline. Sending everything to scrap is easy, but expensive. Sending everything to resale is unrealistic. The return comes from matching each asset to its highest defensible use.
Unlocking the Financial Value of Decommissioned Telecom Gear
Most IT directors don't need to be sold on the idea that retired telecom hardware has some value. They need a model they can defend internally. Finance will ask what recovery looks like, operations will ask how long it takes, and security will ask what has to happen before anything leaves the building.

The blunt financial reality is that firms without a strategic program often recover only 10-20% of asset value, while organizations using professional services for data-wiped telecom assets can retain 40-60% of resale value. The same research notes that enterprises lose 40-60% of potential value through delayed decommissioning, as outlined in this telecom liquidation services analysis.
What actually drives resale value
Residual value usually comes down to five variables:
- Market demand for the brand and model
- Completeness of the unit, including cards, bezels, rails, and power supplies
- Test status, because unverified gear sells at a discount
- Condition after de-install and transit
- Timing, especially around refresh cycles and support milestones
A stack of untested switches may look valuable on paper. In the market, buyers pay for certainty. If serials can't be matched, firmware state is unknown, or modules are missing, bids fall quickly.
Common commercial models
Different vendors structure recovery differently. The right model depends on your risk tolerance and how fast you need inventory off the books.
Outright purchase
This is the cleanest option operationally. The provider buys the equipment, takes title, and handles downstream processing. It's useful when the organization wants speed, fixed economics, and less administrative involvement.
Consignment
This model can produce stronger returns on assets with active secondary demand, but it requires more patience and clearer reporting. The provider sells into its channels and remits proceeds under an agreed schedule.
Profit share
This approach sits between the first two. It works when inventory quality is mixed and both parties want aligned incentives around testing, resale, and component harvesting.
If your portfolio includes current-generation routers, optics, or enterprise voice gear, ask whether the vendor can separate high-demand assets from low-value bulk material instead of pricing everything as one blended lot.
Hidden costs of waiting
Storage feels cheap because it's already paid for. It isn't. Delays create shrinkage, missing accessories, poorer test outcomes, and lower buyer confidence. The gear also keeps consuming internal time. Someone has to answer questions, escort pickups, manage serial disputes, and explain why retired equipment is still on-site.
Organizations evaluating secondary value often compare offers from network equipment buyers in the USA. That exercise is useful, but only if the inventory has been properly identified and sanitized first. Otherwise, you're comparing guesses, not recovery strategies.
Managing Compliance and Security in IT Asset Disposition
The compliance side of telecom asset recovery is where many internal projects go wrong. Teams assume the risk lives only on servers and laptops. In practice, network gear can retain credentials, call records, signaling data, subscriber information, management logs, and cached configurations. A retired appliance in the wrong hands can still create a live incident.

Research focused on telecom disposal notes that improper data sanitization can trigger significant penalties under rules such as the FTC Disposal Rule, with some settlements exceeding millions. It also states that certified processes aligned to NIST 800-88 and backed by full chain-of-custody records reduce breach risk from 1 in 1,000 to 1 in 1,000,000, according to this telecom compliance and disposal overview.
Why in-house wiping often falls short
Internal teams can wipe some equipment safely. The problem is consistency. Telecom estates include multiple OEMs, legacy platforms, field devices, and gear with odd storage footprints. A desktop disposal workflow doesn't automatically apply to SBCs, PBX systems, routers, or transport nodes.
What usually breaks in-house:
- Asset identification gaps where hidden or embedded storage is missed
- Procedure drift across sites and technicians
- Weak custody records when equipment moves before destruction evidence is issued
- Audit exposure because the organization can't prove what happened to each unit
Liability transfer is documentation, not a promise
Vendors often say they “take responsibility.” That only matters if the process produces auditable evidence. For enterprise IT directors, the minimum paperwork should tie each disposition event to serial-level or lot-level records, sanitization outcome, transport custody, and final disposition.
Look for these deliverables:
- Certificate of Data Destruction
- Certificate of Recycling
- Serialized inventory reconciliation
- Chain-of-custody records
- Exception reporting for missing, failed, or physically destroyed assets
A certificate without traceable inventory behind it won't help much in an audit. The paperwork has to connect the asset list, the handling record, and the final outcome.
Telecom logistics create their own compliance problems
This issue gets overlooked when organizations move gear across borders or through multiple freight partners. Batteries, boards, and mixed electronic assemblies can trigger shipping and environmental handling requirements that general office movers don't understand. If your team ships retired gear internationally, this guide to understanding hazardous materials for international shipping is a useful operational reference.
For U.S. organizations seeking a documented handoff model, secure telecom equipment disposal services typically combine logistics, sanitization, and reporting under one chain. That structure is often the difference between “we think it was destroyed” and “we can prove how each asset was processed.”
Choosing Your Telecom Asset Recovery Partner A Vetting Checklist
A telecom recovery partner should look more like a controlled operations vendor than a scrap buyer. If the conversation focuses only on pickup speed or metal recycling, that's a warning sign. You need a provider that understands resale markets, data risk, and serialized accountability.
The shortlist criteria that matter
Use this checklist during vendor screening and RFP review.
Security controls
Ask how assets are tracked from pickup through final disposition. If they can't explain custody clearly, stop there.Telecom-specific processing
General ITAD experience helps, but telecom gear needs deeper familiarity with chassis systems, line cards, handsets, optics, and embedded storage.Testing and grading capability
A vendor should explain how it distinguishes direct resale units from refurbishment candidates and from parts-recovery material.Downstream transparency
If they use subcontractors for recycling or remarketing, ask how those partners are audited and documented.Reporting quality
You want serialized reports, sanitization records, and final disposition detail that can stand up to procurement, audit, and legal review.
Questions worth asking in the RFP
Some questions expose real capability fast:
- Which telecom OEM families do you process regularly?
- How do you identify assets with removable versus embedded storage?
- What happens to equipment that has no resale value?
- Can you separate tested resale inventory from scrap-bound material in your reporting?
- How do you handle missing modules, failed units, or serial mismatches?
- What chain-of-custody evidence do you provide from pickup to final disposition?
- Do you offer onsite and offsite sanitization options?
A simple scoring model
A practical way to compare vendors is to score them across four categories:
| Category | What to look for |
|---|---|
| Operational discipline | Clear intake, inventory, logistics, and reconciliation workflows |
| Security maturity | Documented sanitization standards and custody controls |
| Commercial strength | Real remarketing channels, not generic resale language |
| Transparency | Detailed reports, exception handling, and accessible records |
One useful mindset comes from outside ITAD. This checklist on seven checks for security firms is about another industry, but the buying logic applies well here. Verify process, accountability, insurance, and supervision before you trust anyone with sensitive assets.
The right partner doesn't just remove hardware. They preserve evidence, protect recoverable value, and make your decision defensible after the fact.
A basic hauler can clear a room. A qualified recovery partner can clear a room without creating a finance problem or a compliance problem.
Building a Strategic Asset Recovery Program for the Future
The strongest telecom recovery programs don't start at disposal. They start earlier, during procurement, deployment standards, and decommission planning. When IT, security, facilities, and finance agree on asset handling before the refresh begins, the end-of-life phase becomes controlled instead of reactive.
That shift changes outcomes. Equipment moves faster, custody stays intact, and resale decisions happen while the hardware still has market relevance. Compliance also gets easier because the documentation model is built into the process rather than assembled after the fact.
A durable program usually includes:
- Refresh planning tied to recovery windows
- Standardized inventory capture before gear leaves service
- Defined sanitization paths by asset type
- Approved disposition channels for resale, refurbishment, parts, and recycling
- Executive reporting that shows recovered value and documented disposition
For organizations that want to treat retirement as part of a continuous technology strategy, IT asset lifecycle management provides the right operating frame. Telecom gear shouldn't become a last-minute cleanup project. It should move through a repeatable cycle that protects value at entry, during use, and at exit.
When that happens, telecom equipment asset recovery services stop being a procurement afterthought. They become part of how the organization manages cost, risk, and infrastructure change.
If your team is planning a telecom refresh, site closure, network migration, or warehouse cleanout, contact Beyond Surplus for certified electronics recycling and secure IT asset disposal designed specifically for enterprise telecom equipment.