You decommission a PBX, replace edge routers, migrate voice to cloud, and suddenly a back room fills with retired telecom gear. It looks like a storage problem. It isn't. Old switches, VoIP phones, servers, backup media, and network appliances can still hold call logs, credentials, contact data, and configuration files.
That's why secure telecom equipment disposal services matter. A qualified ITAD process doesn't just remove hardware. It controls data risk, documents custody, supports compliance, and determines whether an asset should be destroyed, recycled, or recovered for value.
The Growing Challenge of Retired Telecom Equipment
Most IT managers don't get into trouble when equipment is active. Trouble starts after the refresh. A stack of decommissioned telecom hardware often sits waiting for “later,” with no owner, no inventory, and no approved disposition path.
That delay creates several problems at once. Data-bearing devices stay accessible. Equipment loses resale value while it sits. Facilities teams lose usable space. Compliance teams still remain responsible for what's on those assets, even if the gear is unplugged.
The scale of this issue is one reason the market for secure disposal keeps expanding. The global secure data disposal market was valued at approximately USD 1.5 billion in 2023 and is projected to reach USD 4.1 billion by 2032, with a CAGR of 11.8%, driven by data privacy concerns, regulatory pressure, and growing volumes of electronic data, according to Dataintelo's secure data disposal market report.
Why retired telecom gear is different
A retired laptop is easy to spot as a data risk. Telecom equipment is easier to overlook. Routers, PBX systems, voice gateways, and call management servers often store more persistent information than people expect.
A second point confuses buyers. Disposal doesn't always mean destruction. Some organizations separate reusable devices from end-of-life scrap. If your team also evaluates secondary-market options for mobile assets, a refurbishment marketplace such as UsedMobiles4U iPhones shows how reuse can extend device life when security controls are handled correctly.
Practical rule: If a device had storage, assume it has recoverable data until sanitization is documented.
Environmental handling matters too. Telecom equipment contains metals, plastics, boards, batteries, and other components that need controlled downstream processing. Beyond the security question, the disposal path affects waste exposure, sustainability reporting, and internal governance. That's why many IT teams now align asset retirement with broader electronic waste environmental impact planning.
Why Secure Disposal is a Non-Negotiable Business Function
Treating disposal as janitorial cleanup is a mistake. It belongs with security, legal, procurement, and facilities because the business risks cut across all four.
The urgency has increased as the telecom market has tightened. The telecom equipment market saw a historic 11% revenue decline in 2024, the sharpest in two decades, which flooded the market with excess inventory and increased the need for professional liquidation. The same source notes that firms in liquidation often recover only 10% to 20% of asset value without a proactive disposition plan, as described in Beyond Surplus telecom liquidation services.
Data risk doesn't end at shutdown
Powering off a device doesn't remove the information inside it. Telecom hardware may retain:
- Call detail records that expose communications patterns
- Saved credentials for admin interfaces and remote access
- Network configurations that reveal architecture and security design
- User and contact data stored locally in voice systems or endpoints
A storage closet with unmanaged assets is still part of your attack surface.
Liability follows the asset
If a recycler, broker, mover, or liquidator mishandles equipment, your organization still has to explain what happened. That's why secure disposal is really a liability transfer process. It requires inventory control, chain of custody, and proof of sanitization or destruction.
Three failures appear often in weak programs:
- No asset register: Teams can't prove which units left the site.
- No custody trail: Nobody can show who handled equipment in transit.
- No destruction evidence: Audit teams get verbal assurance instead of records.
A missing certificate creates the same operational problem as a missing backup. You may not notice until an audit, claim, or incident forces the question.
Delay also destroys value
IT managers usually see destruction as the safe option. Sometimes it is. Sometimes it burns money. The longer equipment sits, the harder it becomes to identify resale candidates, isolate damaged units, and recover usable components. Delay also complicates site closures, lease returns, and de-installation projects.
Environmental mistakes become operational problems
Improper e-waste handling isn't just an ESG concern. It can affect vendor approval, customer due diligence, and internal reporting. Hazardous components need controlled processing. Mixed loads need sorting. Batteries and boards can't be treated like ordinary scrap.
Secure telecom equipment disposal services solve this by turning one vague problem into a documented workflow: identify, sanitize, separate, transport, process, and report.
Core Security and Environmental Controls Explained
The technical language around disposal confuses a lot of teams. The simplest way to think about it is this: first decide the required security outcome, then decide the environmental processing path for what remains.
Federal sanitization guidance often frames destruction choices in three categories: Clear, Purge, and Destroy. Standards such as DoD 5220.22-M and NIST SP 800-88 use these concepts to define how media should be sanitized, and for higher-security needs, physical destruction such as shredding or pulverizing is required because software erasure alone may not be enough against advanced forensic recovery, as summarized by Living Green Technology on data destruction standards.
What the three methods mean
- Clear removes data using logical techniques suitable for reuse in lower-risk settings.
- Purge applies stronger sanitization so data can't be recovered through standard laboratory methods.
- Destroy physically damages media so the storage device itself can't be reused.
For a practical breakdown of sanitization expectations, many IT teams use NIST SP 800-88 guidance as the working reference.
Comparison of Data Destruction Methods
| Method | Security Level | Best For | Allows Reuse? | Compliance Standard |
|---|---|---|---|---|
| Clear | Baseline sanitization | Lower-risk devices slated for controlled redeployment | Yes | NIST SP 800-88 |
| Purge | High sanitization | Media needing stronger erasure before remarketing or reassignment | Usually | NIST SP 800-88 / DoD 5220.22-M context |
| Destroy | Maximum finality | Classified, damaged, or high-risk data-bearing media | No | NIST SP 800-88 / DoD 5220.22-M context |
When software wiping is enough
Software wiping can work well when the device is functional, the media type is supported, and your policy allows reuse. It's often appropriate for servers, endpoints, and certain storage devices that remain operational.
That said, sanitization has to be verifiable. A successful process should produce asset-level records, not a broad statement that a pallet was “wiped.”
When physical destruction is the right call
Physical destruction becomes the better choice when:
- The media is damaged and can't be reliably wiped
- Security classification is high and policy requires final destruction
- The asset has no resale path and recovery value doesn't justify reuse review
Some teams ask whether data recovery is realistic from old hardware. In many cases, yes. That's why organizations dealing with failed media often consult specialized technical resources, including firms such as CTF data recovery experts, to understand how recoverable information can remain on improperly handled devices.
Operational takeaway: Choose destruction based on media type, device condition, and risk tolerance, not on convenience.
Environmental controls are more than recycling bins
After data is handled, the material side starts. Responsible processors separate metals, plastics, boards, cabling, and hazardous components into distinct downstream streams. “Zero-landfill” in practice means the vendor has a defined path for components that can be reused, refined, or regulated for hazardous handling rather than dumped as mixed waste.
That matters for telecom gear because a typical retirement batch may include circuit boards, copper-heavy cabling, rack components, batteries, and peripheral hardware, all of which require different handling rules.
Navigating the Complex Web of Compliance

Compliance often breaks down because teams think only about privacy laws, not disposal obligations. In practice, secure disposition sits at the intersection of records management, information security, environmental controls, and vendor oversight.
What matters most to IT managers
The first question isn't “Which law applies?” It's “What data was on the equipment, and what proof do we need after it leaves?”
For most organizations, that means documenting three things:
- What assets were collected
- How data was sanitized or destroyed
- Where the resulting materials went
If any one of those is missing, the audit trail is weak.
The role of disposal-specific documentation
A Certificate of Destruction matters because it shows your organization didn't merely hand equipment to a hauler. It documents that a defined destruction event occurred under controlled conditions. A Certificate of Recycling serves a related but different purpose by documenting downstream environmental processing.
Vendor qualifications matter too. If your compliance team evaluates downstream practices, they'll likely ask about recognized electronics recycling standards and whether the provider's process aligns with R2 certification expectations.
Plain-English view of key requirements
- FTC Disposal Rule: Focuses on proper disposal of consumer report information. If telecom equipment touched regulated personal information, disposal must prevent unauthorized access.
- HIPAA: Applies when covered entities or business associates retire devices containing protected health information.
- NIST and DoD sanitization guidance: Often becomes the practical benchmark for defensible media handling, even outside government work.
The regulation may differ by industry, but the audit question is usually the same. Can you prove the asset was controlled from pickup through final processing?
This is why procurement and security should approve the same vendor. A cheap pickup service without documented controls can create a compliance problem that costs more than the original project.
The Secure Disposal Process From Pickup to Certificate
A professional process should be boring in the best way. Every step is planned, logged, and repeatable. That's what reduces risk.
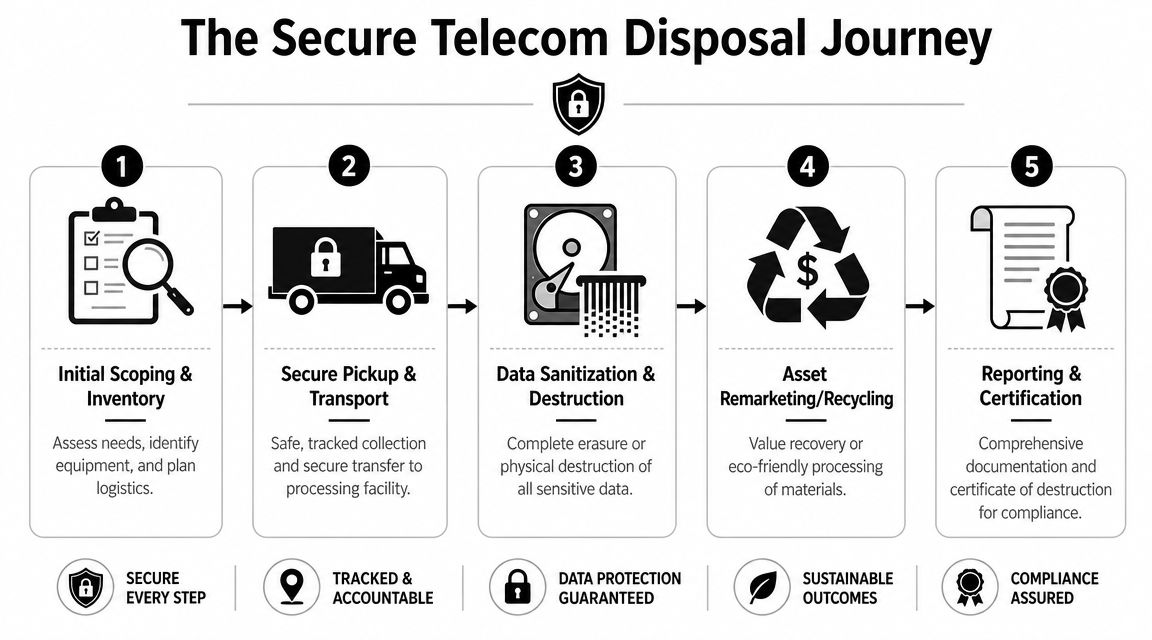
Step 1 through Step 2
Initial scoping and inventory comes first. The provider identifies locations, asset types, access constraints, and which devices are likely to contain data. Leased gear, customer-owned assets, and scrap-only items should be separated at this stage.
Secure pickup and transport follows. Equipment should be packed, labeled, and transferred under documented chain of custody. If your team needs formal evidence after processing, the Certificate of Destruction process should be defined before the truck arrives.
Step 3 through Step 5
Data sanitization and destruction happens according to device type and policy. Reuse candidates may be sanitized and tested. End-of-life media may be shredded or otherwise physically destroyed.
Asset remarketing or recycling comes next. Units with recoverable value are separated from scrap streams. Components without reuse potential move into controlled material recovery.
Reporting and certification closes the job. You should receive records that tie assets, handling actions, and final outcomes together.
A solid final report usually includes:
- Serialized inventory results when available
- Disposition status such as reused, recycled, or destroyed
- Certificates for destruction and recycling as applicable
- Exceptions log for damaged, unidentified, or nonconforming items
Good chain of custody is less about paperwork volume and more about continuity. There shouldn't be gaps between who packed the asset, who moved it, who processed it, and who signed off.
How to Choose a Secure Telecom Equipment Disposal Partner

A common failure starts after the equipment is already retired. The IT team has approved removal, operations wants the room cleared, and procurement selects a low-cost recycler that also handles office electronics. Two weeks later, questions start. Which devices contained storage. Who signed for the shipment. Which assets were resold, destroyed, or sent downstream as scrap. At that point, the disposal job is no longer a cleanup task. It is a risk transfer problem.
A qualified telecom disposal partner should reduce that risk in four areas at once: data exposure, compliance gaps, environmental liability, and lost asset value. That combination matters because telecom retirements rarely involve a single material stream. One rack can hold reusable network hardware, data-bearing appliances, batteries, cabling, and scrap metal. Treating all of it as generic e-waste is like sending a mixed pallet of servers, drives, and paper records through the same process and hoping the paperwork sorts itself out later.
Start with evidence, not marketing language
The fastest way to evaluate a provider is to ask for proof of how they operate under audit conditions. Sales language tells you what a vendor wants to offer. Process records show what they can defend.
Use questions such as these:
- Sanitization scope: Which telecom and network devices can they sanitize, and which media types require physical destruction?
- Operational control: How do they document handoff points, serialized intake, exception handling, and final disposition?
- Reporting quality: Can they provide sample reports that tie assets to outcomes, including reuse, recycling, or destruction?
- Downstream accountability: Which partners handle circuit boards, batteries, metals, and residual scrap, and what documentation supports that chain?
Procurement and IT teams often formalize these requirements with a telecom disposal vendor due diligence checklist.
Evaluate whether the provider can separate risk from value
Some assets should be destroyed without hesitation. Others can be sanitized, tested, and resold under policy. A capable partner knows the difference before processing begins, not after everything reaches the shredder.
That distinction has direct financial impact. It also affects liability. If a vendor lacks technical screening ability, your organization can lose resale value on recoverable equipment or, worse, send data-bearing hardware into the wrong stream. Good providers treat disposition like triage in an operations center. High-risk assets go to controlled destruction. Reuse candidates go through documented sanitization, testing, and remarketing review. Scrap moves into material recovery only after those decisions are made.
What a qualified partner should be able to handle
Telecom retirements often involve more than boxed devices waiting on a dock. The provider should be prepared for field conditions, site constraints, and mixed asset classes in the same project.
Look for a partner that can:
- Support de-installation activities for racks, mounted gear, cabling, and telecom room clear-outs
- Identify data-bearing equipment early so those items are isolated from commodity scrap
- Assess remarketing potential where internal policy allows buyback or resale recovery
- Produce audit-ready documentation that supports internal review, customer questions, and regulator requests
Beyond Surplus is one example of a provider that offers secure pickup, data destruction, recycling, and IT buyback services for business equipment. The important point is broader than any single brand. Your disposal partner should be able to manage security controls, environmental handling, documentation, and value recovery within one accountable process, so your team is not left stitching together responsibility across multiple vendors.
Understanding Logistics and Pricing Models
Pricing gets clearer once you separate the job into three buckets: handling, data security, and material outcome. Most quotes combine all three, which is why two vendors can describe the same project very differently.
Common pricing approaches
You'll typically see one of these structures:
- Per-item pricing for devices such as servers, switches, phones, or drives
- Per-pound pricing for mixed scrap, cabling, or bulk electronics
- Project pricing for site closures, multi-room cleanouts, or decommissioning work
The right model depends on what is in the load. A pallet of mixed telecom scrap shouldn't be priced the same way as a serialized batch of data-bearing network appliances.
What changes the cost
Several operational details can push pricing up or down:
- Device mix: Data-bearing hardware requires more controlled processing.
- Access conditions: Stairs, loading limitations, or after-hours removal increase labor complexity.
- Documentation needs: Detailed inventory reporting adds handling time.
- Recovery potential: Reusable assets can offset disposal charges.
Professional recycling economics also depend on downstream material separation. Under zero-landfill approaches, metals, plastics, and circuit boards are sorted for refining and reuse, which can avoid landfill fees and create revenue from commodity recovery, as described by SAMR's telecom equipment recycling guide.
Why pricing and recovery should be reviewed together
A low disposal quote may hide weak reporting or blanket shredding. A better quote sometimes costs more upfront but returns value through reuse, refined material streams, or reduced compliance exposure.
That's why procurement should ask for a disposition model, not just a hauling price. You want to know which assets will be destroyed, which may be recycled, and which might offset the project.
Frequently Asked Questions About Telecom Disposal
What if the telecom equipment is leased
Start with the contract, not the loading dock.
Leased telecom gear follows a different set of rules than owned equipment. A carrier, finance company, or manufacturer may require return in original condition, documented data erasure before return, or approval before any part is removed or destroyed. If your team mixes leased assets into a general disposal batch, the problem is no longer just operational. It can become a contract breach with added fees and disputed liability.
A simple control helps prevent that. Keep leased equipment on a separate inventory and hold area until the lessor's instructions are confirmed.
Can one provider handle equipment across multiple sites
Yes, but only if the provider can keep the process consistent from one location to the next.
Multi-site telecom disposal fails when each branch improvises its own packing, labeling, handoff, and documentation practices. The better model works like a standardized shipping protocol. Every site follows the same chain-of-custody steps, the same asset identification rules, and the same reporting format. That consistency protects your audit trail and makes exceptions easier to spot.
What's the difference between a Certificate of Destruction and a Certificate of Recycling
They document two different outcomes.
A Certificate of Destruction confirms that data-bearing media or equipment was destroyed under a defined process. A Certificate of Recycling confirms that the remaining materials entered an approved downstream recycling stream for environmental processing. If a project includes both data-bearing hardware and general telecom scrap, your records may need both certificates to show that security controls and environmental handling were completed.
Should every retired device be shredded
No. The decision should follow risk, not habit.
Shredding makes sense for failed drives, high-sensitivity media, or assets governed by a destruction-only policy. Sanitization and controlled resale can be the better choice for equipment that still has market value and can be cleared to your standard. The practical question is not which method sounds stronger. It is which method meets your security requirement while preserving recoverable value where policy allows.
What should my team prepare before pickup
Good preparation reduces disputes later. It also shortens the time equipment spends in an uncontrolled state.
Before pickup, your team should:
- Confirm decision makers: Know who approves destruction, recycling, return, or resale.
- Flag data-bearing assets: Identify PBX systems, servers, storage, network appliances, and devices with embedded flash memory.
- Separate lease returns: Keep them physically apart from owned scrap.
- Define evidence requirements: Decide what inventory detail, serial number capture, and certificates your legal, security, or audit teams expect.
- Document site constraints: Note loading access, restricted hours, escort requirements, or rooms with special handling needs.
What question should IT managers ask first, but often don't
Ask where legal responsibility changes hands, and what documentation proves it.
That point matters because disposal risk does not disappear when equipment leaves the building. If custody records are incomplete, your company may still be answering questions about a missing firewall, an unprocessed storage device, or improperly handled material weeks later. A qualified provider should be able to show the handoff points clearly, from pickup through final disposition, so liability transfer is documented rather than assumed.
If your team is planning a telecom refresh, site closure, or network decommission, contact Beyond Surplus for secure telecom equipment disposal services, certified data destruction, and documented IT asset disposition support.