If you're responsible for old PBX cabinets, VoIP handsets, routers, switches, conferencing gear, or carrier equipment, disposal usually starts as a space problem. Then it turns into a security, compliance, and liability problem.
Most organizations don't get into trouble because they forgot to recycle. They get into trouble because retired telecom gear still held data, moved without a clear chain of custody, or went to a vendor that couldn't document what happened next. That's why learning how to dispose of telecom equipment safely has less to do with cleanup and more to do with controlled decommissioning.
The Challenge of Retiring Telecom Assets
A telecom closet full of retired hardware can look harmless. In practice, it often contains devices that still store call logs, contacts, credentials, system configurations, and customer information. That includes obvious assets like communications servers and less obvious ones like phones, gateways, and routers.

The wider context matters. Global e-waste reached 62 million tonnes in 2022, and only 22.3% was formally collected and recycled, leaving $62 billion in recoverable natural resources unaccounted for, according to global e-waste statistics compiled here. Telecom disposal sits inside that larger failure. When companies treat network and voice hardware like ordinary surplus, gear tends to sit too long, move informally, or leave the site without proper records.
Why telecom assets create more risk than ordinary scrap
Telecom equipment combines three difficult issues in one project:
- Data risk because many devices retain operational and customer information.
- Operational risk because equipment may still be tied to live circuits, racks, batteries, and structured cabling.
- Environmental risk because disposal mistakes push regulated or hard-to-process material into the wrong downstream channel.
A facilities team may see obsolete hardware. A compliance officer sees stored business records. An ITAD consultant sees assets that need traceability from rack position to final disposition.
Old telecom equipment is rarely "just metal." It usually carries a history of users, settings, and business communications.
This is also where many businesses confuse junk hauling with asset disposition. General clear-outs have their place. If you're separating office furniture, packaging, and non-IT debris alongside telecom hardware, a practical reference on junk removal in Durham region, Durham region junk removal shows how cleanup logistics differ from controlled handling. But telecom gear itself needs a tighter process.
What a controlled retirement process looks like
Safe disposal starts with an ITAD mindset. That means documenting the asset, deciding whether it holds data, decommissioning it safely, sanitizing or destroying storage media, and sending the remaining hardware into a verified reuse or recycling stream.
For organizations managing enterprise voice and network refreshes, IT and telecom equipment disposal services are built around that chain of custody rather than simple pickup. That difference is what separates a defensible project from a room-clearing exercise.
Your Disposal Project Plan and Asset Inventory
Disposal projects fail early. They fail when nobody defines scope, when remote closets are missed, when one team assumes another team captured serial numbers, or when equipment leaves the building before anyone decides what data destruction method applies.
Build the project before you touch the rack
Start with a short written plan. It doesn't need to be elaborate, but it does need ownership.
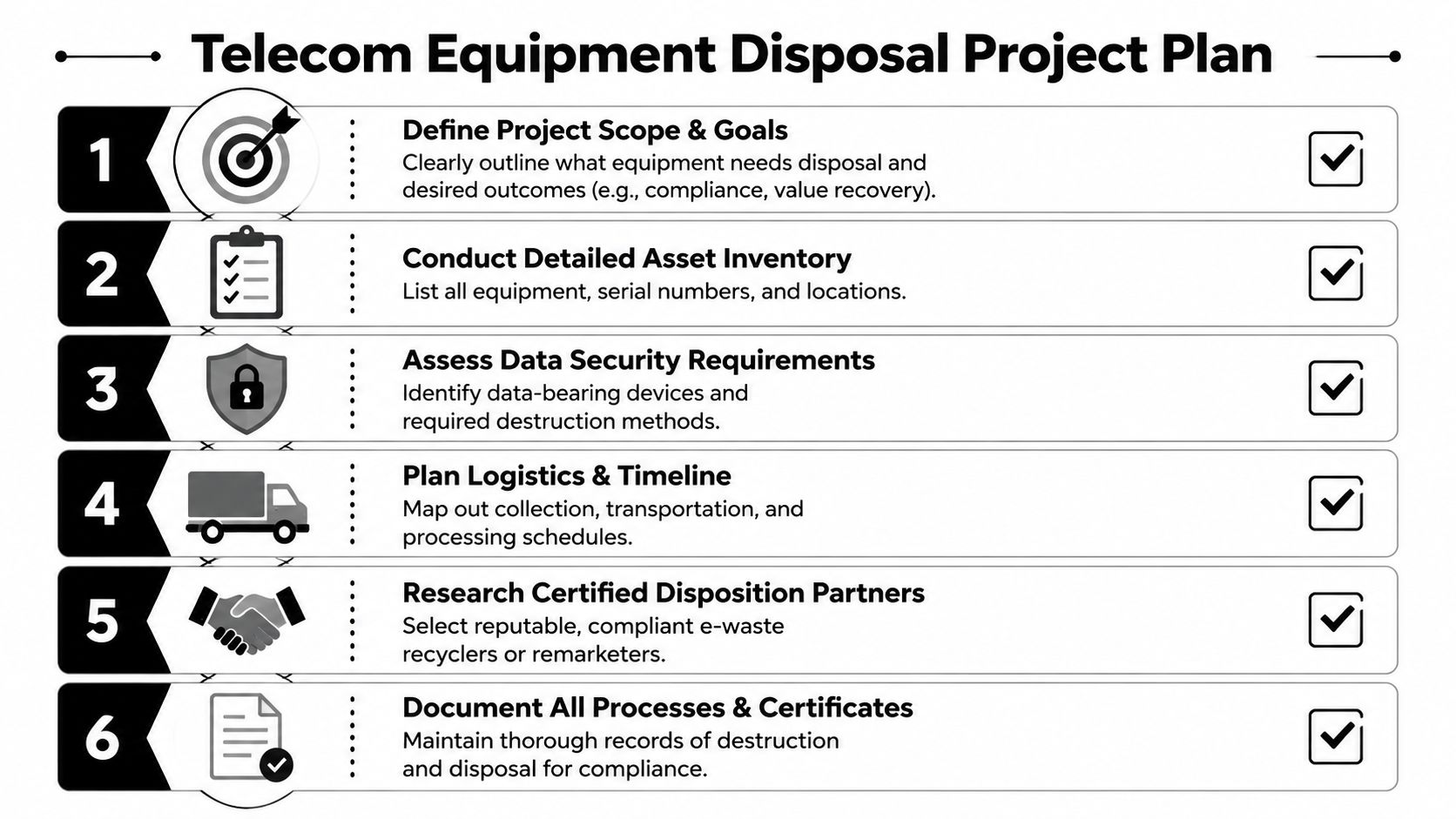
Your plan should identify:
- Scope. Which sites, rooms, racks, cabinets, and storage areas are included.
- Asset classes. Phones, servers, switches, firewalls, PBX gear, UPS units, cabling, spares, and accessories.
- Decision owners. IT, information security, facilities, procurement, and compliance.
- Disposition goals. Reuse, remarketing, material recovery, or destruction.
- Logistics timing. De-install dates, loading access, staging areas, and transportation windows.
A project plan matters because telecom environments are messy. Gear gets moved between locations. Labels go missing. Spare phones sit in unopened boxes while retired gateways remain mounted in live racks. If you don't define the boundary of the project, your inventory won't be reliable.
Inventory is your chain of custody foundation
The asset list is more than a spreadsheet for finance. It's the document that supports custody, valuation, and destruction records. For data-bearing devices, serialized tracking is the standard worth aiming for because it ties each item to its final outcome.
Capture these fields wherever possible:
- Asset tag if your organization assigned one.
- Serial number from the manufacturer label.
- Make and model so the processor can identify handling requirements.
- Device type such as VoIP phone, PBX appliance, router, switch, or server.
- Physical location down to site, room, rack, or closet.
- Condition such as working pull, damaged, or incomplete.
- Power status so no one assumes a disconnected asset is safe to remove.
- Data-bearing status to flag storage media or embedded flash.
- Accessories present including power supplies, line cards, optics, and handsets.
Practical rule: If a device can store settings, logs, credentials, or user information, classify it as data-bearing until proven otherwise.
Separate assets by processing path
Don't wait until pickup day to decide what goes where. Sort the inventory into logical groups:
| Asset group | Main concern | Likely path |
|---|---|---|
| Communications servers and PBX systems | Data retention | Sanitization or destruction first |
| Routers, firewalls, and switches | Configurations and credentials | Verified data destruction, then reuse or recycle |
| VoIP phones and mobile handsets | Contacts, logs, flash storage, batteries | Battery segregation plus sanitization |
| UPS units and battery-backed gear | Safety and hazardous components | Special handling before transport |
| Cabling, handsets, plastics, metal chassis | Material segregation | Recycling stream |
Organizations also benefit from reviewing a formal server decommissioning checklist because many telecom retirements include rack servers, storage, and virtual infrastructure that support voice systems.
What works and what doesn't
What works is a serialized inventory, one owner for approvals, and staging assets by disposition path before removal. What doesn't work is bulk boxing mixed equipment and trying to reconstruct the asset list afterward.
That reconstruction almost never gets easier later. It gets worse when labels tear off, accessories separate from the base unit, and nobody remembers whether the device came from a branch office or the primary data room.
Secure Decommissioning and Hazardous Material Handling
The riskiest mistakes often happen before data destruction starts. A technician pulls the wrong connection, stacks powered gear in a hallway, or tosses battery-backed devices into a gaylord with metal scrap. Safe disposal depends on shutting systems down cleanly and handling specialized components correctly on site.

Decommission in the right order
Telecom equipment should come offline under a controlled change process, not as a warehouse cleanout. Disconnect services, confirm cutovers, remove network dependencies, and verify that no failover function still points to the hardware you're retiring.
Basic discipline goes a long way:
- Confirm service retirement before unplugging anything in a shared rack.
- Label disconnected cabling if another team still needs traces for documentation.
- Use ESD-safe handling for boards, optics, and memory-bearing modules.
- Stage by category instead of piling all equipment together.
- Keep access restricted once assets are removed from production.
Small items create outsized trouble here. SFP modules, removable drives, controller cards, and handset battery packs are easy to miss. They should be pulled, counted, and packed deliberately.
Hazardous components need separate handling
Telecom disposal isn't just a data issue. It's also a worker safety and environmental issue. Improper e-waste disposal can release up to 1,000 different chemical substances into the environment, and unsound recycling methods such as open burning can release lead and other neurotoxicants, as outlined in this telecom equipment recycling guide.
That risk starts with poor segregation at the customer site. Common problem materials include:
- Batteries in UPS units, wireless handsets, and backup modules.
- CRT or legacy display components in older systems.
- Circuit boards and mixed electronic assemblies that need dedicated downstream processing.
- Optical transceivers and specialty modules that shouldn't be tossed loosely into bulk containers.
Simple handling rules that prevent avoidable problems
A good site team keeps physical safety separate from data work. Use containers for batteries. Protect optics. Avoid crushing mixed hardware just to save floor space. Don't let staff improvise disposal for odd components.
If your organization manages battery streams or mixed electronic components internally, universal waste labeling requirements are worth reviewing before the move begins. Labeling and segregation errors create trouble long before an auditor asks for records.
A secure disposal project starts with safe hands-on work. If the on-site handling is sloppy, the downstream paperwork won't fix it.
Ensuring Total Data Destruction
This is the part that determines whether your disposal process is merely tidy or actually defensible. Telecom devices can store far more than users expect. Servers hold call records and databases. Routers and firewalls hold credentials and configurations. VoIP phones may retain contacts, logs, and flash-based settings.
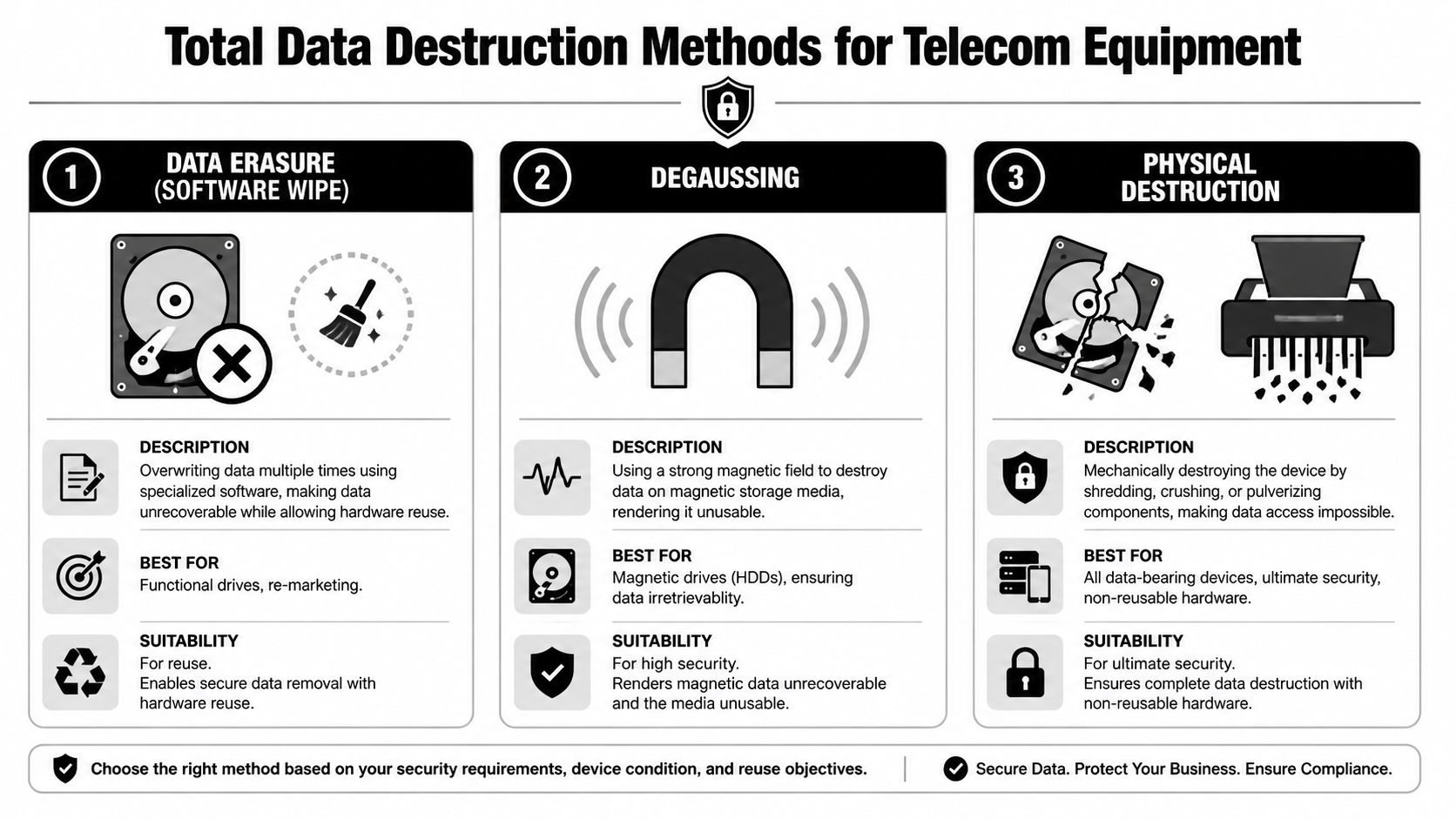
The strongest approach is a multi-step sanitization process that can include DoD-compliant wiping, NSA-approved degaussing for magnetic media, and physical destruction through shredding to a particle size of less than 2mm, with verification required to ensure 100% data irrecoverability, as described in this guidance on safe ways to dispose of telecom equipment.
When software wiping makes sense
Software wiping is usually the first option when the hardware still has reuse or remarketing value. For magnetic drives, DoD 5220.22-M style overwriting is still commonly referenced. For SSDs and flash media, NIST 800-88-aligned approaches such as cryptographic erasure are often more appropriate because flash storage behaves differently from spinning media.
Use software erasure when:
- The device is functional and may be reused or resold.
- You need an audit trail tied to a serial number.
- The media type supports verified erasure with the right tool set.
Verification is the key point. Running a wipe utility without a validation report isn't enough in a compliance-driven environment. If your team needs a standards reference, NIST SP 800-88 guidance is the benchmark most organizations use to frame sanitization decisions.
Where degaussing fits and where it doesn't
Degaussing is effective for magnetic media, especially hard disk drives, because a strong magnetic field disrupts the stored data permanently. It is not the right method for SSDs or other flash-based storage.
That's one of the most common practical mistakes in mixed telecom projects. Older PBX infrastructure may contain magnetic drives, while desk phones, edge appliances, and modern compact systems often rely on flash storage. Treating those media types as if they were the same creates a false sense of security.
A simple comparison helps:
| Method | Best use case | Reuse possible | Main caution |
|---|---|---|---|
| Software wipe | Functional drives and resale candidates | Yes | Must be verified |
| Degaussing | Magnetic HDD media | No | Not suitable for SSDs or flash |
| Physical destruction | High-security or damaged media | No | Hardware value is lost |
Physical destruction is the final answer for high-risk media
Physical destruction removes ambiguity. Shredding is the preferred choice when policy, legal exposure, device condition, or media type makes reuse inappropriate. In telecom environments, this often applies to failed drives, unidentified storage, and media from highly regulated workloads.
Some certified ITAD firms, including Beyond Surplus, offer in-house hard drive shredding, DoD 5220.22-M wiping, and serialized chain-of-custody documentation as part of telecom equipment processing. That's useful when a project includes both remarketable assets and media that must be destroyed.
If you can't prove the media type, the wipe result, and the asset identity, you don't have a strong destruction record.
Match the method to the asset
Use this logic when deciding:
- Rack servers supporting voice systems often need drive-by-drive review because they may contain multiple storage devices.
- Routers, firewalls, and appliances should be checked for internal flash, removable modules, or configuration backups.
- VoIP phones shouldn't be dismissed as harmless endpoints. Many store local settings and user-related information.
- Damaged or incomplete devices often go straight to physical destruction because testing and verification may not be reliable.
What doesn't work is choosing one method for every item in the project. Safe disposal requires matching the method to the actual media, then documenting the result.
Choosing Your Disposition Path Recycle vs Resale
Once the data issue is resolved, the next decision is economic and strategic. Should the equipment be recycled for material recovery, refurbished for reuse, or held back for parts? The right answer depends on age, condition, market demand, internal policy, and your tolerance for downstream complexity.

A practical industry question is whether to refurbish telecom equipment for reuse or send it for domestic material recovery. Refurbishment supports the circular economy, but it also raises questions about export controls, downstream transparency, and ethical processing. That's why guidance on outdated telecom equipment puts so much weight on transparent audit trails and certified downstream partners.
Resale can recover value, but only under the right conditions
Remarketing makes sense when the equipment is complete, functional, supported, and still wanted in the secondary market. That usually means newer switches, quality server hardware, certain business phones, and accessories with broad compatibility.
Resale is less attractive when gear is heavily customized, physically damaged, obsolete, locked to a narrow ecosystem, or expensive to test. In those cases, labor can exceed recoverable value.
Recycling is simpler, but it shouldn't be blind
Material recovery is often the cleanest path for legacy telecom fleets. It avoids uncertain resale cycles and puts metal, boards, plastics, and cabling into defined recycling streams. But "recycling" isn't enough by itself. You still need to know who processed the equipment, whether components stayed domestic or moved abroad, and what documentation exists.
For organizations trying to balance sustainability and usable life, consumer repair and refurbishment examples can still offer a useful mindset. This article on iPhone repair for longer device use shows the broader principle well. Extend life where it is practical, secure, and transparent. Recycle when it isn't.
A simple decision filter
Use these questions:
- Can the asset be sanitized and tested reliably?
- Is there realistic secondary-market demand?
- Will resale create export or downstream transparency concerns?
- Does your policy favor domestic recycling for certain categories?
- Will the audit trail satisfy procurement, compliance, and ESG stakeholders?
Reuse is valuable only when you can explain where the asset went, who processed it, and how security controls were applied before it left your custody.
Proving Compliance and Transferring Liability
A disposal project isn't complete when the truck leaves. It's complete when the records show what was picked up, how data was destroyed, how material was processed, and who accepted responsibility at each handoff.
The legal standard that matters for many organizations is straightforward. The FTC Disposal Rule requires businesses to take "reasonable steps" to destroy customer information, and in practice that increasingly means documented, third-party certified destruction. Using an uncertified provider can void liability protection and expose an organization to penalties that far exceed the savings from cutting corners, as explained in this article on proper disposal of old telecommunications equipment.
What your records should include
At minimum, ask for documentation that ties assets to outcomes. That often includes:
- Serialized inventory records showing what was received.
- Chain-of-custody documentation showing transfer points.
- Certificate of Data Destruction for sanitized or shredded media.
- Certificate of Recycling for processed equipment streams.
- Settlement or value recovery reporting if assets were remarketed.
A real certificate of destruction is more than a courtesy PDF. It should support your internal audit trail and help your legal, compliance, and procurement teams show due diligence.
Cheap disposal often becomes expensive later
The hidden cost in uncertified disposal isn't usually visible on day one. It appears later when a customer asks how records were destroyed, when an auditor wants proof, or when internal security reviews discover that retired equipment left the site with no serialized documentation.
The same logic applies in smaller device markets. Buyers looking at the best refurbished iPhones care about grading, trust, and process transparency. Enterprise telecom disposal raises that standard much higher because the stakes include regulated data and organizational liability.
Documentation is what turns disposal from an operational task into a completed risk transfer.
Frequently Asked Questions on Telecom Disposal
Do a few desk phones require the same process as a full telecom room?
The scale changes, but the discipline doesn't. A small batch still needs asset identification, data review, and a documented disposition path. A full room decommissioning adds logistics, staged removal, and usually more stakeholders.
Are VoIP phones really a data security risk?
Yes, they can be. Many retain settings, contacts, call-related information, and user associations. Treat them as potentially data-bearing until your team or processor verifies otherwise.
What should we do with cabling, power supplies, and accessories?
Keep them separated by material and use case. Power supplies, battery-backed accessories, line cards, handsets, optics, and bulk cabling should not be tossed together if you want clean downstream processing and accurate reporting. Mixed gaylords create sorting problems and can complicate both reuse and recycling.
Should we erase devices in-house or use a certified provider?
In-house work can be appropriate if your team has the right tools, validation process, and documentation discipline. The problem isn't the location. It's whether you can prove the method, verification, and custody trail later. Many businesses decide that third-party certified processing is the cleaner risk decision.
What should be on a Certificate of Destruction?
Look for asset identification, dates, method used, and enough detail to tie the certificate back to your inventory. A generic statement that "equipment was destroyed" isn't very useful if it doesn't identify what equipment was involved.
Is donation a safe alternative?
Only after data sanitization and only with clear records. Donation can support reuse, but it should never become an informal exit path for unverified devices.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal.