Your telecom room is getting cleared for a migration, a lease exit, or a data center refresh. Pallets of phones, gateways, cards, and edge gear are sitting in storage. Finance wants recovery. Security wants documentation. Operations wants it gone without creating another project that drags on for weeks.
That's where bulk telecom equipment buyers enter the picture. The secondary market is active because 5G and fiber upgrades keep pushing older hardware out of service. At the same time, sellers are dealing with a tougher pricing environment because global telecom equipment revenues fell 17% in the first half of 2024 due to excess inventory and weaker demand, as reported by Telecoms on Dell'Oro Group findings. In practice, that means you can still recover value, but only if you control the inventory, pricing logic, and compliance process from the start.
Initial Preparation and Asset Inventory
Most disappointing offers start with bad information. If your file says “assorted Cisco phones” or “misc. telecom parts,” a buyer has to price for uncertainty. Uncertainty lowers bids.
Start with a working inventory that a reseller or refurbisher can use. Record manufacturer, model, part number, serial number, quantity, physical condition, power status, included accessories, rack ears, handsets, licenses if transferable, and whether the equipment is boxed, palletized, or loose. Separate complete working systems from parts-only material.

Build the inventory buyers need
A useful inventory has three layers.
- Commercial identity. Brand, model, and quantity.
- Technical identity. Revision, firmware note, modules installed, and compatibility details.
- Disposition identity. Reuse, repair, parts harvest, or recycle.
If you're dealing with multiple rooms or sites, asset-tracking platforms can help standardize naming and prevent duplicate entries. Teams that don't already have that process in place can look at tools like Material Handling USA asset tools to tighten location control before pickup.
Practical rule: If a buyer can't tell what's in the lot from your spreadsheet and photos, the buyer will assume the worst-case mix.
Sort for value before you request bids
Don't send one mixed lot if the lot contains very different value bands. Sort equipment into categories such as:
- Ready for resale with clean housings, matching components, and no obvious defects
- Refurbishable units that need testing, minor repair, or missing accessories
- Parts recovery items with damage, incomplete assemblies, or older revisions
- Recycling only material with no realistic resale path
Data-bearing devices need special handling from the first day of the project. VoIP systems, voicemail hardware, storage components, and some network appliances may retain configuration data or user information. Flag those assets early so the chain of custody stays intact.
Short photo sets help. Front, rear, model tag, and pallet-level photos are usually enough to improve bid quality. If you're deinstalling racks, a practical prep list such as this server decommissioning checklist helps keep labeling, removal order, and documentation from drifting.
Establishing Fair Market Value for Your Equipment
The phrase fair market value gets used constantly in telecom resale. It often isn't explained. That's a problem when you're comparing offers from several bulk telecom equipment buyers.
The resale market itself is large and fragmented. The telecom equipment resale market reached $23.4 billion in 2025 across over 2,500 companies, and many enterprise IT directors say they can't independently verify pricing models, as noted by Beyond Surplus on telecom equipment resale. That fragmentation is exactly why sellers need their own framework.
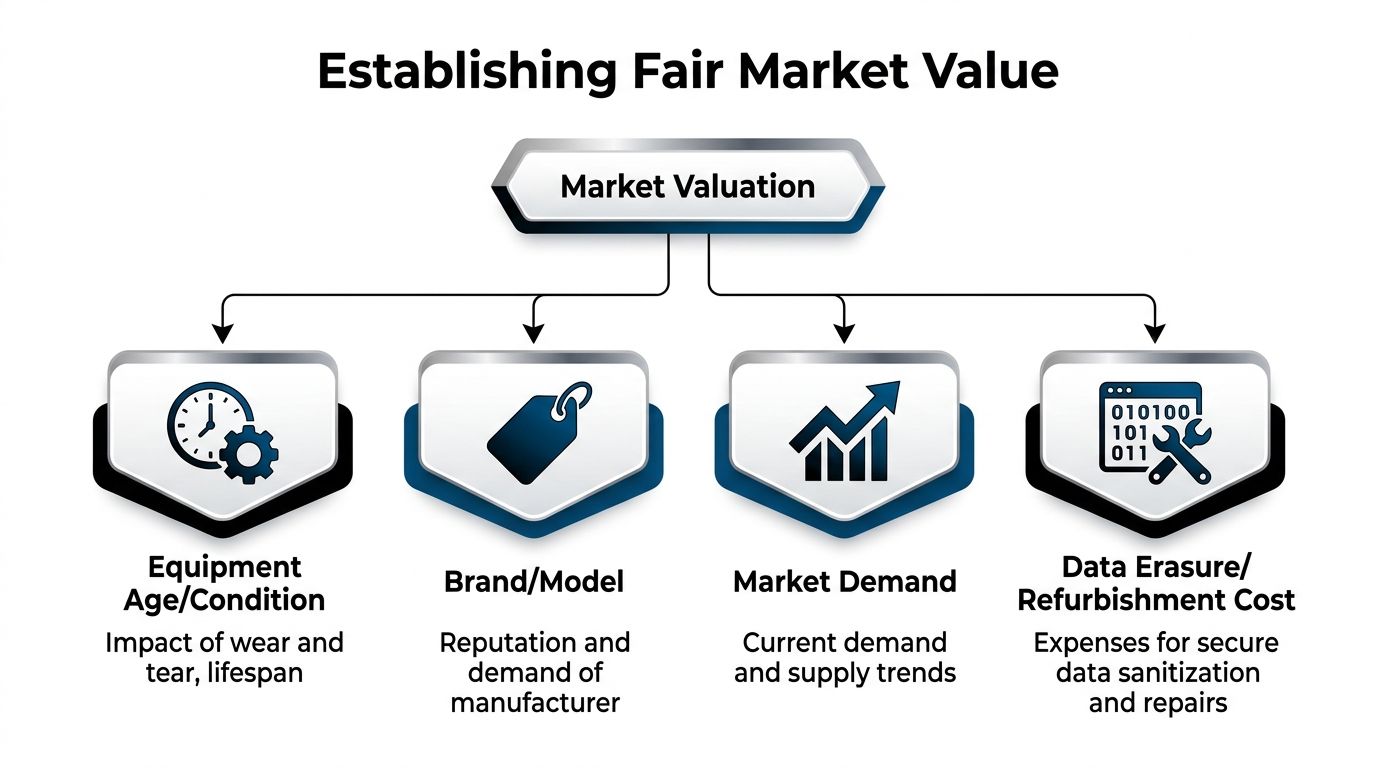
What actually moves price
Book value rarely tells you what a buyer will pay. Secondary-market value usually comes down to four variables.
| Factor | What to check | Why it matters |
|---|---|---|
| Age and condition | Cosmetic wear, test status, completeness | Buyers discount unknown condition fast |
| Brand and model | Installed base, parts demand, supportability | Popular lines move more easily |
| Market demand | Current upgrade cycles, surplus levels, buyer geography | Demand changes faster than depreciation schedules |
| Recovery cost | Data wiping, repair labor, freight, repackaging | Higher processing cost lowers the offer |
A complete lot of current-generation handsets with matching accessories can outperform a larger lot of mixed, untested equipment. Completeness matters because refurbishers price the labor burden into every purchase.
A practical valuation method
Use a simple range instead of chasing one perfect number.
- Start with current secondary-market observations. Check active listings and completed-market behavior on telecom marketplaces and industrial resale channels.
- Adjust for sell-through reality. A listing price is not a realized price.
- Subtract buyer-side cost. Testing, sanitization, freight, repair, and warranty exposure all affect the net offer.
- Separate premium SKUs from bulk scrap value. High-demand cards, phones, and modules should not be buried inside a mixed gaylord quote.
A low offer isn't always bad pricing. Sometimes it's an honest signal that your lot needs sorting, better documentation, or a different sales channel.
For many organizations, the smartest move is to ask buyers to quote by category rather than one blended number. That exposes where the value is being created or lost.
If you need a second benchmark before signing, this guide on where to sell telecom equipment is useful because it frames different outlet types and why they price differently. The main thing to avoid is accepting the first “all-in” bid without asking how the buyer handled condition, completeness, and processing cost.
Vetting Criteria for Reputable Bulk Buyers
Price gets attention. Vetting protects the company.
A buyer that pays quickly but can't document downstream handling creates legal and operational exposure you'll still own after the truck leaves. That's why procurement discipline matters here. A data-driven supplier evaluation methodology can mitigate 90% of technology acquisition failures, with key checks including certifications, large-order capacity, and pilot orders aimed at quality consistency with a defect rate under 2%, according to the Academy of Management Perspectives reference provided.
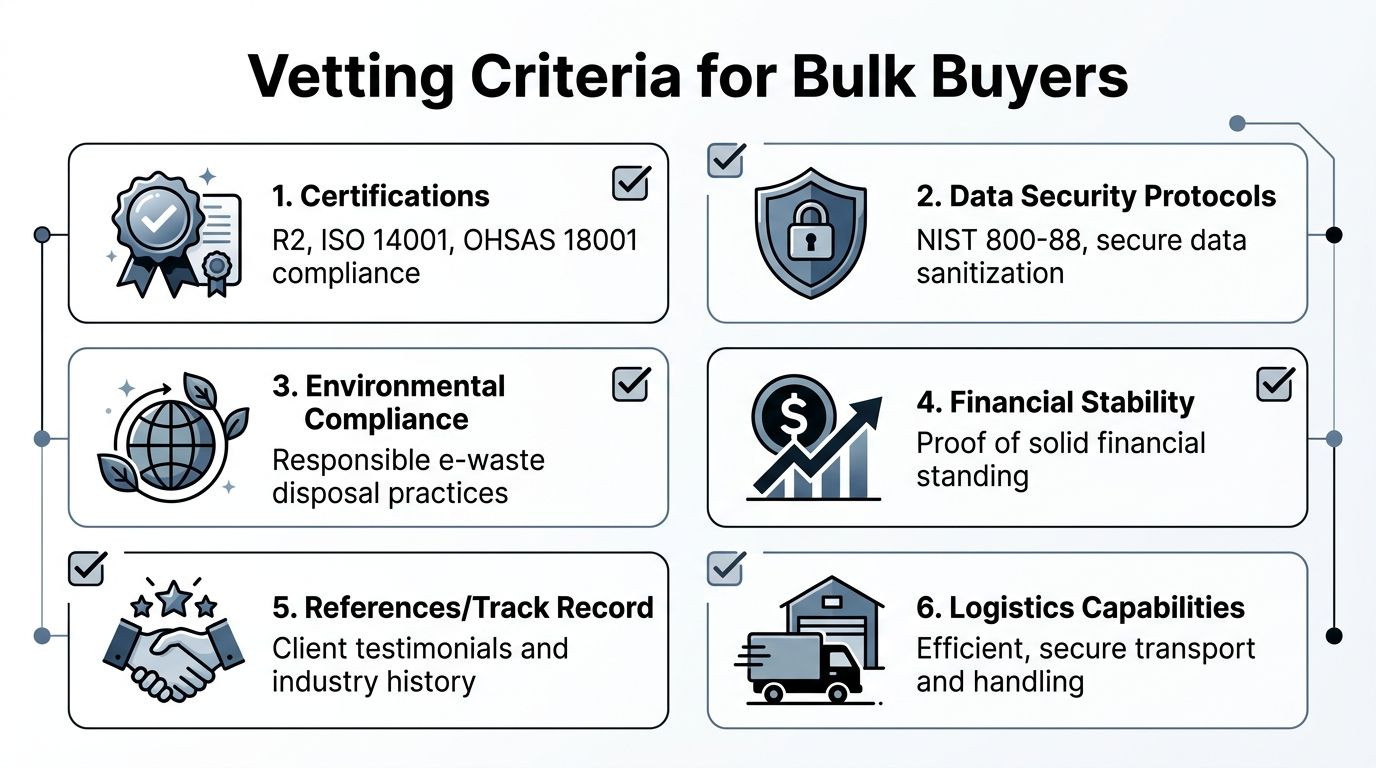
What to verify before you compare offers
Start with evidence, not claims.
- Compliance credentials matter because telecom lots often include equipment that crosses from reuse into regulated disposal. Ask what certifications the buyer maintains and what they apply to.
- Data handling controls should be specific. If the buyer says assets are wiped, ask how that process is documented and whether it aligns with NIST 800-88.
- Operational capacity matters more than many sellers expect. A buyer may quote aggressively, then stumble on packaging, pickup windows, or multi-site coordination.
- Reporting samples tell you how mature the operation is. Ask for example chain-of-custody reports, recycling certificates, and destruction certificates.
A good diligence process also tests consistency. If the transaction is large, start with a pilot release from one cage, one room, or one site. That shows you how the buyer handles labeling, counts, exceptions, and communication before the full lot moves.
Questions that expose weak buyers
Ask direct questions and listen for vague answers.
| Question | Strong answer | Weak answer |
|---|---|---|
| How do you document serialized custody? | Item or lot-level tracking with timestamps | “We track everything internally” |
| How do you handle data-bearing telecom assets? | Defined sanitization workflow and certificates | “We remove data as needed” |
| Who manages logistics? | Named team, pickup scope, packaging rules | “We'll figure it out after award” |
| What happens to non-resalable units? | Clear reuse, parts, and recycling path | “We move all material downstream” |
Due diligence test: If the buyer can't explain where equipment goes after pickup, you don't have enough visibility.
For a practical screening model, use a structured vendor due diligence checklist and score each buyer the same way. That keeps the selection from turning into a pure price contest.
One factual option in this market is Beyond Surplus, which buys bulk telecom equipment from businesses and provides chain-of-custody documentation, secure data destruction options, certificates of recycling, and nationwide pickup coordination for organizations.
Key Negotiation Strategies and Contract Terms
Once you've chosen a preferred buyer, attention turns to contract detail. Here, companies either preserve value or give it back through vague language.
Organizations that use a structured methodology for vendor selection and contract negotiation report 15% to 35% cost savings with a 96% success rate, and vendor lock-in through multi-year contracts can inflate future costs by 20% to 40%, according to CenterPoint Group's telecom procurement strategy practices.

Terms worth negotiating
Don't focus only on price per lot. Push on the terms that shape the actual outcome.
- Payment timing. Define whether payment is due on pickup, receipt, inspection, or final reconciliation.
- Logistics responsibility. State who covers packing, loading, freight, and cargo risk.
- Testing and grading window. Set a firm period for dispute notices and quantity adjustments.
- Title and liability transfer. Make the transfer point explicit.
- Exception handling. Spell out how missing accessories, damaged units, and count variances are resolved.
A buyer-friendly contract leaves room for repricing after pickup. A seller-friendly contract narrows the adjustment rules and requires evidence for deductions.
Avoid soft language
Watch for phrases like “subject to final audit,” “commercially reasonable adjustments,” or “industry-standard data removal.” Those terms sound normal, but they create room for argument.
Short contracts can be risky contracts. If a term affects money, custody, or compliance, it needs plain language.
It also helps to align operations and legal before the paper is drafted. Procurement may care about payment terms, while security cares about data-bearing gear and facilities cares about dock timing. A shared review process usually catches the gaps. This overview of vendor management best practices is a useful internal checkpoint before final signature.
Ensuring Full Compliance and Secure Chain of Custody
The riskiest moment in any asset-disposition event is physical transfer. Equipment leaves your control. If the paperwork and custody process are weak, your organization may still carry the exposure.
For regulated industries, buyer value extends beyond price. Partners that can provide certified chain-of-custody and measure environmental impact address a real need for organizations dealing with the FTC Disposal Rule, HIPAA, or GLBA, as discussed in Sadoff's guidance on excess telecommunications assets.
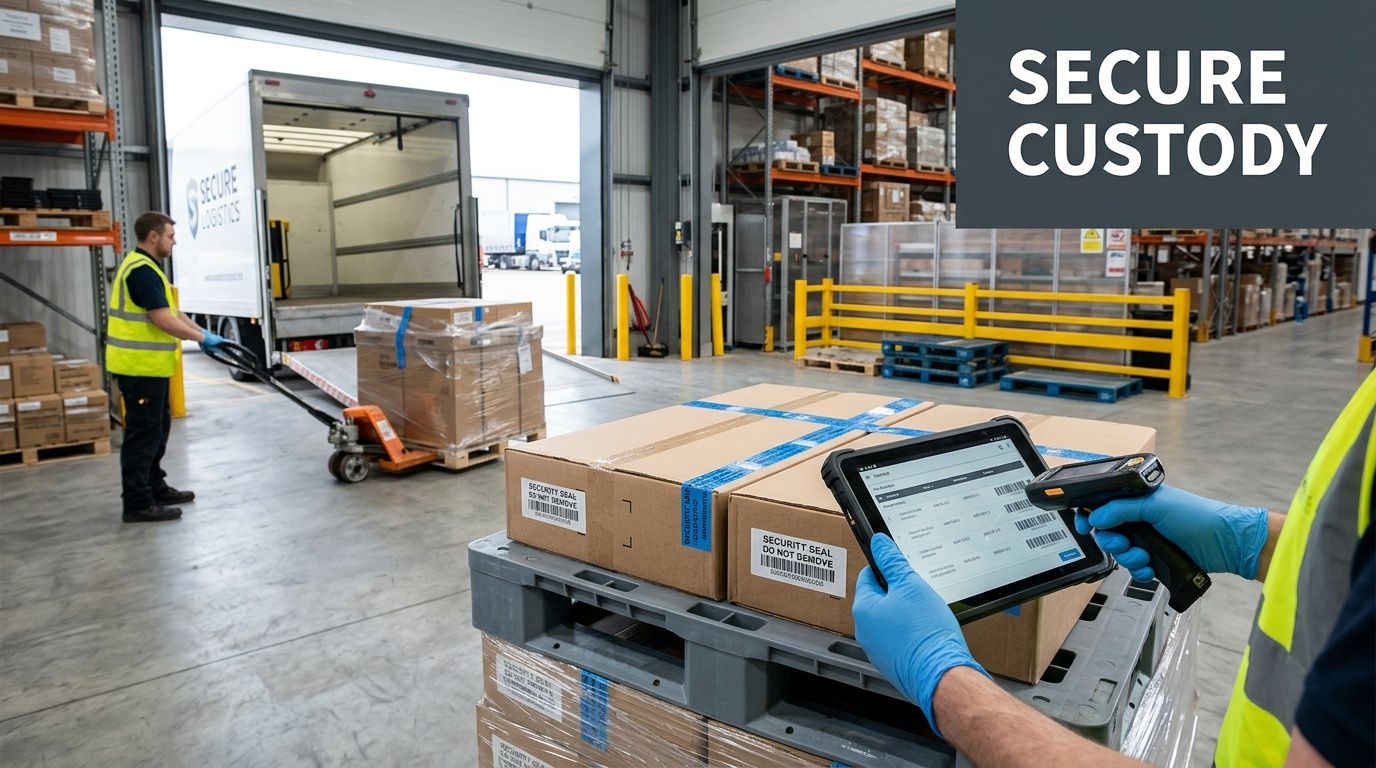
Documentation that should exist every time
A compliant process produces an audit trail, not just a bill of sale.
- Serialized or lot-based chain of custody showing when assets were packed, moved, received, processed, and closed out
- Certificate of data destruction for applicable assets
- Certificate of recycling for non-resalable material
- Liability transfer language tied to the actual disposition workflow
- Pickup and receiving records that match your internal inventory
If a buyer says certificates are available “on request,” ask to see samples before release day. Mature operators have standard reporting formats and defined retention practices.
Where custody often breaks down
Problems usually show up in ordinary places. Mixed pallets, unlabeled accessories, site staff handing over gear outside the approved list, or carrier substitutions that nobody documented.
If equipment includes radios, encryption-related components, or devices moving across borders, the classification question also matters. Teams that need a plain-English overview can use resources that demystify the Commerce Control List when export controls become part of the disposition review.
Compliance is operational. It lives in labels, signatures, timestamps, and exception logs.
For data-bearing telecom and network assets, your internal policy should map directly to the buyer's sanitization process. If that standard references NIST, make sure the documentation does too. A practical reference point is NIST SP 800-88 guidance, especially when audit teams want proof that “wiped” means a defined process rather than a verbal assurance.
Integrating Asset Disposition into Your ESG Strategy
Telecom liquidation used to be treated as a cleanup task. It isn't anymore. The decisions made at end of life affect environmental reporting, governance controls, and brand risk.
The strongest ESG outcomes usually come from prioritizing reuse first, then certified recycling for what can't be remarketed. That approach supports circularity and gives internal stakeholders a cleaner story than simple removal. It also creates governance value because the company can show how assets were tracked, sanitized, transferred, and closed out.
Why ESG changes buyer selection
A buyer that only talks about cash recovery is giving you one slice of the outcome. A partner that can document reuse, recycling, and chain of custody supports multiple internal goals at once.
Consider what your sustainability or compliance team may need after the project closes:
- Reportable environmental results tied to resale and recycling activity
- Evidence of responsible downstream handling
- A documented governance trail for legal, audit, and risk teams
- Consistency across locations so one business unit doesn't improvise disposal practices
That last point matters more than most organizations expect. Inconsistent disposition practices create governance problems long before they create environmental ones.
Turn one-off cleanouts into policy
The mature move is to standardize telecom disposition before the next refresh. Create thresholds for resale review, define approved documentation, and decide who signs off on chain-of-custody release. Once that policy exists, asset liquidation becomes repeatable instead of reactive.
The companies that recover the most value usually aren't chasing better luck. They're running a repeatable process.
If your organization is building that process into broader sustainability reporting, this page on an ESG recycling partner in Georgia offers a useful example of how disposition work can connect to governance and environmental reporting.
When you're evaluating bulk telecom equipment buyers, don't settle for a simple pickup quote. Ask how the inventory is valued, how custody is documented, how data-bearing assets are handled, and how resale and recycling results are reported. For organizations that need secure ITAD, certified documentation, and value recovery from surplus telecom gear, contact Beyond Surplus.