A hard drive destruction certificate is the official, legally defensible record proving that your business's sensitive data has been permanently eliminated. More than just a simple receipt, it is a crucial legal document that verifies your company’s retired hard drives were physically or digitally destroyed, rendering all stored information completely unrecoverable. For any IT manager or compliance officer, this certificate serves as the primary defense during a regulatory audit or in the event of a data breach investigation.
Understanding Your Proof of Data Elimination
A hard drive destruction certificate formally transfers the liability for the data from your business to your certified IT Asset Disposition (ITAD) partner. For IT directors, facility managers, and procurement professionals, this certificate is the final, essential step in the IT asset lifecycle. It provides the undeniable, documented proof required to demonstrate compliance with data security regulations like HIPAA, GLBA, and the FTC Disposal Rule.
In the high-stakes environment of enterprise data security, these certificates are indispensable. Their importance is magnified by the fact that data breaches have skyrocketed, with thousands of cases reported in the U.S. each year impacting a staggering number of people. These certificates are not just administrative paperwork—they are your organization's ironclad proof that sensitive data on retired IT hardware has been obliterated beyond recovery, shielding your business from crippling fines and severe reputational damage.
The Core Purpose of a Certificate
At its heart, this document serves a critical, straightforward function: to provide a third-party, auditable record that specific media storage devices were destroyed. Without it, your business is left with only a verbal promise that its sensitive corporate, client, or patient information was handled correctly—a significant risk no enterprise can afford to take. A proper certificate closes this compliance loop, giving you tangible evidence to present to auditors, stakeholders, and legal teams.
This certificate is the definitive line of defense that separates responsible data management from potential negligence. It transforms the abstract process of data destruction into a concrete, verifiable event, safeguarding your company's reputation and bottom line.
Who Needs a Destruction Certificate?
Any commercial or enterprise organization that handles sensitive electronic information requires this documentation when retiring old IT assets. This is especially true for businesses operating in highly regulated industries.
Key sectors that rely on these certificates include:
- Healthcare Providers: To comply with HIPAA and protect Patient Health Information (PHI).
- Financial Institutions: To meet GLBA requirements for safeguarding consumer financial data.
- Government Agencies: To adhere to strict federal and state data protection mandates.
- Legal Firms: To protect confidential client information and maintain attorney-client privilege.
- Enterprise IT Departments: To enforce internal data security policies and manage IT asset lifecycle documentation.
By obtaining and retaining these documents, your organization demonstrates a robust commitment to due diligence and data security. It is a foundational practice for any modern business managing digital assets. Learn more about Beyond Surplus’s certified hard drive destruction services that provide this essential documentation for businesses across the United States.
Decoding the Anatomy of a Destruction Certificate
A hard drive destruction certificate is far more than just a piece of paper. It's a legally binding document that transforms a service into a verifiable act of compliance. To be truly audit-proof, this certificate needs specific, concrete details that go well beyond a company logo and a quick signature. Think of it less like a receipt and more like a forensic report—every single detail counts.
This document serves as the final, unbroken link in the chain connecting the physical hard drive that left your facility to the documented proof of its complete destruction. Any vague descriptions or missing information create gaps in that chain, leaving your business exposed during an audit or a security incident.
Core Components You Must Verify
When a destruction certificate lands on your desk, your team should treat it like a critical checklist. Every one of the following elements must be present and accurate for the document to stand up to scrutiny. Missing even a single component can render the certificate useless for proving your due diligence.
Here’s what to look for:
- Unique Certificate Number: This is a serialized ID tied exclusively to your service order. It prevents fraudulent duplication and makes it simple to pull up in your records.
- Chain-of-Custody Reference: The certificate must clearly link back to the chain-of-custody paperwork that tracked the assets from pickup to destruction. This is the glue connecting the physical transfer to the final outcome.
- Your Company's Information: The document has to clearly state your business’s legal name and the service address where the drives were collected.
- ITAD Vendor Details: The full name, address, and contact info of the certified vendor who performed the destruction must be front and center.
Asset and Method Specifics
Beyond the administrative details, the real value of the certificate lies in the specifics of what was destroyed and how. This is where many subpar certificates fall flat. A truly compliant document provides granular detail that leaves no room for doubt.
A strong hard drive destruction certificate is built on specificity. It should answer not just that something was destroyed, but precisely what was destroyed and how it was accomplished, creating an irrefutable record for compliance.
This level of detail is non-negotiable. Imagine an auditor questioning the disposal of a server from your asset inventory. You need to be able to point to a certificate that lists that server's hard drive by its unique serial number.
These next details are absolutely essential:
- A Detailed List of Assets: The certificate must include an itemized list of every single hard drive destroyed, identified by its unique serial number. A simple count like "50 hard drives" is not sufficient for a serious audit.
- Explicit Statement of Destruction Method: The method used has to be clearly stated. Was it physical shredding, crushing, or degaussing? If it was shredded, the final particle size should be noted to confirm it meets industry standards.
- Date and Location of Destruction: The certificate must specify the exact date the destruction happened and the location of the secure facility where it was performed.
- Authorized Signature: The document must be signed by an authorized representative of the ITAD vendor, who is legally attesting to the accuracy of all the information provided.
By carefully examining each hard drive destruction certificate for these critical components, you empower your organization to confidently manage its data security and compliance obligations. For a closer look at how these documents should be structured, check out our detailed guide on the ideal destruction certificate format to ensure your records are always audit-ready. This proactive verification is the cornerstone of a secure IT asset disposal program.
How This Certificate Becomes Your Compliance Shield
A hard drive destruction certificate is far more than just a piece of paper. It is your frontline defense against staggering regulatory fines and complex legal battles. This single document is your proof that you’ve responsibly handled data, directly connecting your actions to major privacy laws like HIPAA, the Gramm-Leach-Bliley Act (GLBA), and the Fair and Accurate Credit Transactions Act (FACTA).
Imagine an auditor showing up and asking you to prove what happened to the sensitive patient data on 300 decommissioned clinic computers. A verbal promise that "we took care of it" will not suffice. Your destruction certificate, complete with matching serial numbers, provides the definitive, documented answer that satisfies even the toughest scrutiny.
This document is the bedrock of a critical legal principle: transfer of liability. When a certified IT Asset Disposition (ITAD) vendor like Beyond Surplus issues this certificate, the legal responsibility for ensuring the data’s permanent destruction officially shifts from your organization to ours.
The Legal Framework for Data Destruction
Several federal and state laws don't just recommend—they mandate—the secure disposal of sensitive information. A certificate of destruction is the tangible evidence that you’ve met these legal requirements, effectively closing the loop on your data security duties.
Here are a few key regulations where this certificate is absolutely vital:
- HIPAA: The Health Insurance Portability and Accountability Act demands that healthcare organizations protect patient health information (PHI). A destruction certificate is essential proof that electronic PHI on retired devices was disposed of correctly.
- GLBA: This act holds financial institutions responsible for protecting consumers' private financial information. Certified destruction ensures customer data on old servers and workstations is permanently eliminated.
- FACTA: The FTC’s Disposal Rule under FACTA requires businesses to properly destroy consumer report information. Failing to do so can lead to massive penalties, making certified destruction a non-negotiable risk management step.
This certificate is a key piece of the puzzle when it comes to demonstrating compliance, especially when it’s part of a well-thought-out system for IT Asset Lifecycle Management.
From Liability to Peace of Mind
The transfer of liability is an incredibly powerful concept. It means that once we issue the certificate, if data were ever to surface from a drive listed on that document, the legal and financial fallout would land on the ITAD vendor—not you. This shift provides immense peace of mind for the executives, IT leaders, and compliance officers who are ultimately accountable for data protection.
In the world of compliance, if it isn't documented, it never happened. The hard drive destruction certificate is the official, notarized entry in your compliance diary, proving your due diligence beyond any doubt.
And this isn't just a minor detail. Real-world cases have shown that a simple, properly documented destruction process has saved businesses from seven-figure fines and the kind of reputational damage that takes years to repair. It’s the final, secure link in the chain of custody, turning a potential weak spot into a documented strength.
The growing demand for certified destruction is hard to ignore. The global hard drive destruction service market, valued at USD 1.65 billion, is expected to explode to USD 5.05 billion by 2035, growing at a healthy 10.7% CAGR. This massive growth is driven by tightening regulations and ever-present cyber threats, especially in North America, where IT, finance, and healthcare firms are held to strict standards like HIPAA and CCPA.
When you partner with a certified vendor, you aren't just outsourcing a task; you're acquiring a compliance shield backed by a legal document. This certificate ensures your data disposal methods meet the highest industry standards, like those outlined in NIST Special Publication 800-88. To see how we put this into practice, check out our guide on how Beyond Surplus aligns with NIST SP 800-88 guidelines for media sanitization. It’s a strategic move that protects your organization and proves your commitment to data security.
Matching Destruction Methods to Your Certificate
Not all data destruction methods are created equal, and your hard drive destruction certificate needs to accurately reflect the technique used to sanitize your media. The documentation for a physically shredded drive looks completely different from one that’s been digitally wiped, and knowing the difference is key to verifying you received the secure service you paid for.
The right method often comes down to your organization's risk profile, the sensitivity of the data, and whether you plan to reuse or recycle the hardware. Each approach is unique, and the certificate must capture the specific actions taken to ensure that data is permanently unrecoverable.
Physical Destruction: Shredding and Degaussing
When you need an absolute, no-questions-asked guarantee that your data is unrecoverable, physical destruction is the solution. The goal is simple: destroy the internal platters where the data lives, making it impossible to read. This is the go-to for devices that held highly sensitive information.
Two main methods fall into this category:
- Hard Drive Shredding: This is the gold standard for secure data destruction. Industrial shredders physically grind hard drives into a pile of small, mangled metal fragments. A proper certificate for shredding will explicitly state this and, just as importantly, specify the final shred size (e.g., 2mm, 10mm). That detail is your proof that the destruction meets specific government or industry security standards. You can learn more about how Beyond Surplus provides secure hard drive shredding that meets these strict requirements.
- Degaussing: This technique uses an incredibly powerful magnetic field to scramble and permanently erase the data stored on traditional hard disk drives (HDDs). A certificate for degaussing should identify the degausser model and its magnetic force rating to prove it was strong enough for the job. One critical note: degaussing is completely ineffective on Solid-State Drives (SSDs) because they do not store data magnetically.
A certificate for physical destruction provides an absolute guarantee. It confirms that the physical media storing your data no longer exists in a recoverable form, offering the highest level of assurance for auditors and stakeholders.
Digital Destruction: Data Wiping and Cryptographic Erasure
Sometimes, an enterprise wants to reuse or resell the physical drive. To do that securely, the data must be digitally destroyed with the same permanence as shredding. This is where data sanitization, or wiping, comes in.
The documentation for these methods gets a bit more technical:
- Data Wiping (Overwriting): This process uses specialized software to write over every single sector of the hard drive with random data, often in multiple passes. A certificate for data wiping must reference the specific software standard used, like NIST 800-88 Purge or Department of Defense 5220.22-M. This certificate is almost always paired with a detailed report listing each drive's serial number and confirming a successful, verified wipe.
- Cryptographic Erasure (CE): This is a feature on most modern self-encrypting drives (SEDs). Instead of overwriting data, the process instantly deletes the media encryption key. Without the key, the encrypted data on the drive is rendered permanently unreadable—like locking a vault and throwing away the only key. A CE certificate will state this method was used and confirm the key was successfully erased for each drive's serial number.
Choosing the right method is a critical risk management decision. The table below breaks down these techniques to help you align your security needs with the right service and documentation.
Data Destruction Methods and How They Are Certified
Here’s a quick comparison of the most common hard drive destruction methods, their best applications, and how they should be documented on your certificate.
| Destruction Method | How It Works | Best Use Case | Certificate Documentation Details |
|---|---|---|---|
| Physical Shredding | Mechanical grinders reduce the drive to small metal pieces. | Disposing of high-security data, failed drives, or SSDs. | Method stated as "shredding" with final particle size noted. |
| Degaussing | A powerful magnetic field erases data on magnetic platters. | Bulk destruction of functional or failed HDDs. | Method stated as "degaussing" with equipment specs listed. |
| Data Wiping | Software overwrites all existing data with random characters. | Preparing functional drives for reuse, resale, or donation. | Wiping standard (e.g., NIST 800-88) and software used. |
| Cryptographic Erasure | The internal encryption key is deleted, locking the data forever. | Rapid sanitization of modern self-encrypting drives (SEDs). | Method stated as "cryptographic erase" with verification. |
Ultimately, whether a drive is shredded into confetti-sized pieces or digitally wiped to government standards, your certificate is the final piece of the puzzle. It’s your official record that proves you took every necessary step to protect your sensitive information.
Why Chain of Custody Is the Backbone of Your Certificate
A hard drive destruction certificate is only as strong as the process that backs it up. Without a rigorously documented and unbroken chain of custody, the certificate becomes almost worthless. This unbroken trail is the backbone of your certificate, guaranteeing its validity.
The journey of your assets begins the moment they are scheduled to leave your facility. It's a series of secure, documented handoffs that create an auditable trail, making sure the specific hard drive collected from your office is the exact one listed on the final certificate. This process transforms a potential security gap into a verifiable strength.
The Journey From Your Office to Destruction
From the initial pickup, every step is designed to eliminate uncertainty. This rigorous tracking guarantees that assets are never lost, misplaced, or mishandled between your location and the secure destruction facility. The process is transparent and built on clear documentation at every critical checkpoint.
Key steps in establishing an unbroken chain of custody include:
- On-Site Asset Scanning and Inventory: Before anything is moved, a technician scans the serial number of each individual hard drive at your location. This creates an initial inventory list that serves as the foundation for the entire process.
- Signed Transfer of Custody Forms: A formal transfer document is signed by both your representative and the ITAD technician. This legally transfers possession and documents the exact assets being collected.
- Secure, Sealed Transport: All assets are placed in locked, sealed containers before leaving your premises. For high-security projects, GPS-tracked vehicles provide real-time location data, adding another layer of security.
- Logged Facility Entry: Upon arrival at the secure facility, the container seals are inspected and broken. Each asset is scanned again to reconcile the shipment against the initial on-site inventory, confirming that everything arrived as expected.
This is where the physical or logical destruction finally happens, all built on the trust established by a secure chain of custody.
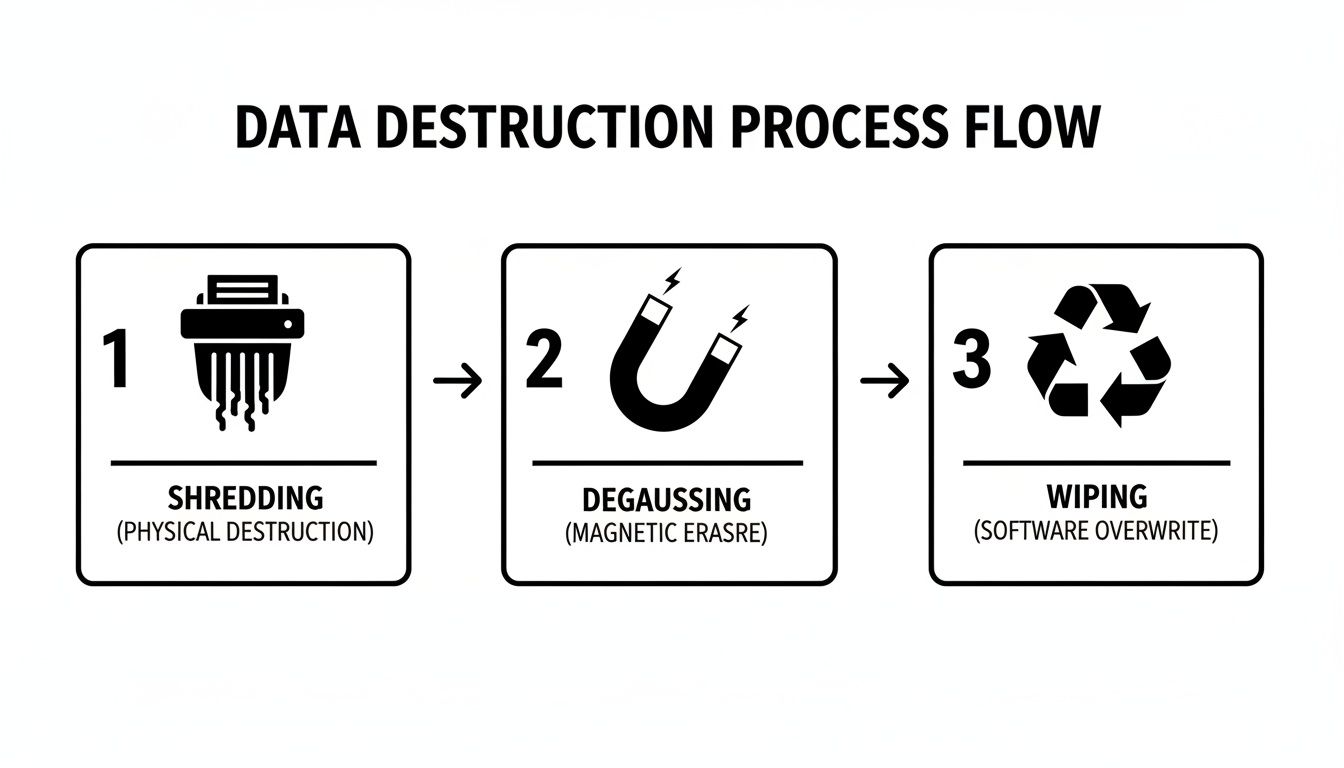
This process flow shows how different methods—shredding, degaussing, and wiping—are applied to achieve permanent data sanitization once assets are securely processed.
How Documentation Prevents Liability
Each document generated along this journey—from the initial inventory list to the final signed certificate—builds a powerful, interconnected audit trail. This chain of evidence is what allows you to definitively prove due diligence to regulators, stakeholders, or legal counsel. It closes any potential loopholes that could otherwise create significant liability for your business.
An unbroken chain of custody isn't just a best practice; it's the core mechanism that validates your entire data disposal program. It ensures that the serial number on your certificate perfectly matches the drive that was physically destroyed.
This meticulous documentation is especially critical during large-scale projects like data center decommissioning, where you could be managing hundreds or thousands of assets. A flawless tracking system is non-negotiable. To see how this fits into the bigger picture, check out our comprehensive server decommissioning checklist, which highlights the importance of asset tracking from start to finish.
Ultimately, this rigorous process provides the peace of mind that comes from knowing every single asset is accounted for and securely destroyed, with the paperwork to prove it.
Putting It All Together: Your Certified Destruction Process
Implementing a secure, certified destruction program should be a seamless, integrated part of your IT asset management strategy. When you work with a trusted ITAD partner, the process flows from scheduling a pickup to receiving the final, verifiable paperwork your business needs to operate with confidence.
The journey starts the moment you schedule a nationwide pickup for your retired IT assets. From that point on, a clear, documented process ensures every single device is accounted for, transported securely, and either sanitized or destroyed to the highest industry standards. The entire operation is built for transparency and efficiency.
Receiving and Managing Your Certificate
Once the destruction is complete, you will receive your verifiable hard drive destruction certificate through a secure online portal. This digital delivery provides instant access to critical compliance documents, creating a permanent, digital filing cabinet for all destruction-related records.
Of course, receiving the certificate is just the first step. Managing it properly is what really counts. Here are a few best practices for handling this documentation:
- Go Digital: Set up a dedicated, secure folder on your company’s network for all your certificates of destruction and recycling. Keeping everything in one place makes life so much easier.
- Use Smart Naming Conventions: Name your files consistently so you can find what you need in seconds. Something like "Destruction_Certificate_VendorName_Date_ServiceOrder#" works wonders.
- Link It to Your Asset Records: Connect the certificate's unique ID back to your internal asset management database. This creates a rock-solid link between a specific asset’s serial number and its proof of destruction.
Best Practices for Long-Term Retention
Your responsibility doesn't end when the certificate lands in your inbox. Retaining these documents is absolutely critical for future audits and protecting your business from long-term liability. Since regulations like HIPAA do not specify an expiration date for this type of proof, the industry standard is simple: keep them forever.
Think of your hard drive destruction certificate as a permanent asset. It’s not just a temporary record—it's a lasting shield that proves your due diligence and protects your organization from data-related headaches for years to come.
This approach ensures you’re always prepared for a compliance review, no matter how far back it goes. By keeping a complete and organized archive, you're cementing your company’s commitment to data security and staying on the right side of regulations.
At Beyond Surplus, we back up this commitment by providing the essential documentation your business needs to operate without the constant worry of data-related risks. Our process is designed to be straightforward and secure, giving you the certified proof required to close the loop on your IT asset lifecycle.
We invite you to connect with our ITAD specialists. Let us help you design a secure, compliant, and certified solution that fits your unique business needs perfectly.
Answering Your Questions About Destruction Certificates
When you're dealing with certified data destruction, a few practical questions always come up. Let's walk through some of the most common ones we hear from businesses, clearing up the key principles of secure and compliant IT asset disposal.
How Long Should We Keep Hard Drive Destruction Certificates?
The simple answer? Forever. Think of a hard drive destruction certificate as a permanent shield against future liability. Since regulations like HIPAA don't put an expiration date on this kind of proof, holding onto them indefinitely ensures you're always ready for an audit, no matter how far back it goes. It’s best practice to file them away as part of your permanent compliance and asset management records.
Is a Certificate of Recycling the Same as a Certificate of Destruction?
No, they serve two very different—but equally important—roles. A Certificate of Recycling is your proof of environmental compliance, showing that your e-waste was handled responsibly and did not end up in a landfill. On the other hand, a Certificate of Data Destruction proves your data security compliance.
For any retired device that ever stored sensitive information, your business needs to obtain both documents. This is the only way to be fully protected from both environmental and data privacy liabilities.
Can We Get a Certificate for Destroying Just One Hard Drive?
Absolutely. Any professional ITAD vendor should issue a serialized certificate whether you're destroying one drive from a small business or thousands from a massive data center decommissioning. A key sign of a reputable provider is that they record each hard drive's unique serial number on the certificate. This meticulous tracking guarantees a complete and accurate audit trail for every single asset, regardless of how big or small the project is.
What Happens If We Lose Our Destruction Certificate?
Don't panic. A professional ITAD partner like Beyond Surplus keeps secure, long-term digital archives of every certificate they issue. If you misplace your copy, all you need to do is contact your vendor and ask for a duplicate. They can usually pull it up with your company name, the date of service, or the unique certificate number. This gives you essential peace of mind, knowing you can always produce proof of destruction whenever an audit or internal review calls for it.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. We deliver the meticulous documentation and transparent process your business needs to manage IT assets with confidence. Learn more at https://www.beyondsurplus.com.