After your company’s network refresh, you're usually left with a pile of retired routers, switches, and old PBX systems. Just tossing them out isn't an option. This equipment is loaded with sensitive data and materials that need to be handled responsibly. This is where R2 certified telecom recycling comes in, acting as a verifiable 'trust audit' for your old electronics.
What R2 Certified Telecom Recycling Actually Means
Think of R2 certification not as a simple sticker on a bin, but as a strict, audited set of rules that ensures your retired telecom gear is managed securely and ethically. For business owners and IT managers, it’s proof that your hardware is being handled the right way, reducing risks tied to data security and environmental rules.
Just like a financial audit gives you confidence in a company's books, R2 certification gives you confidence in a recycler's process. The entire system is built on a few core principles that cover everything from the moment the equipment leaves your office to its final destination.
The Core Pillars of R2 Certification
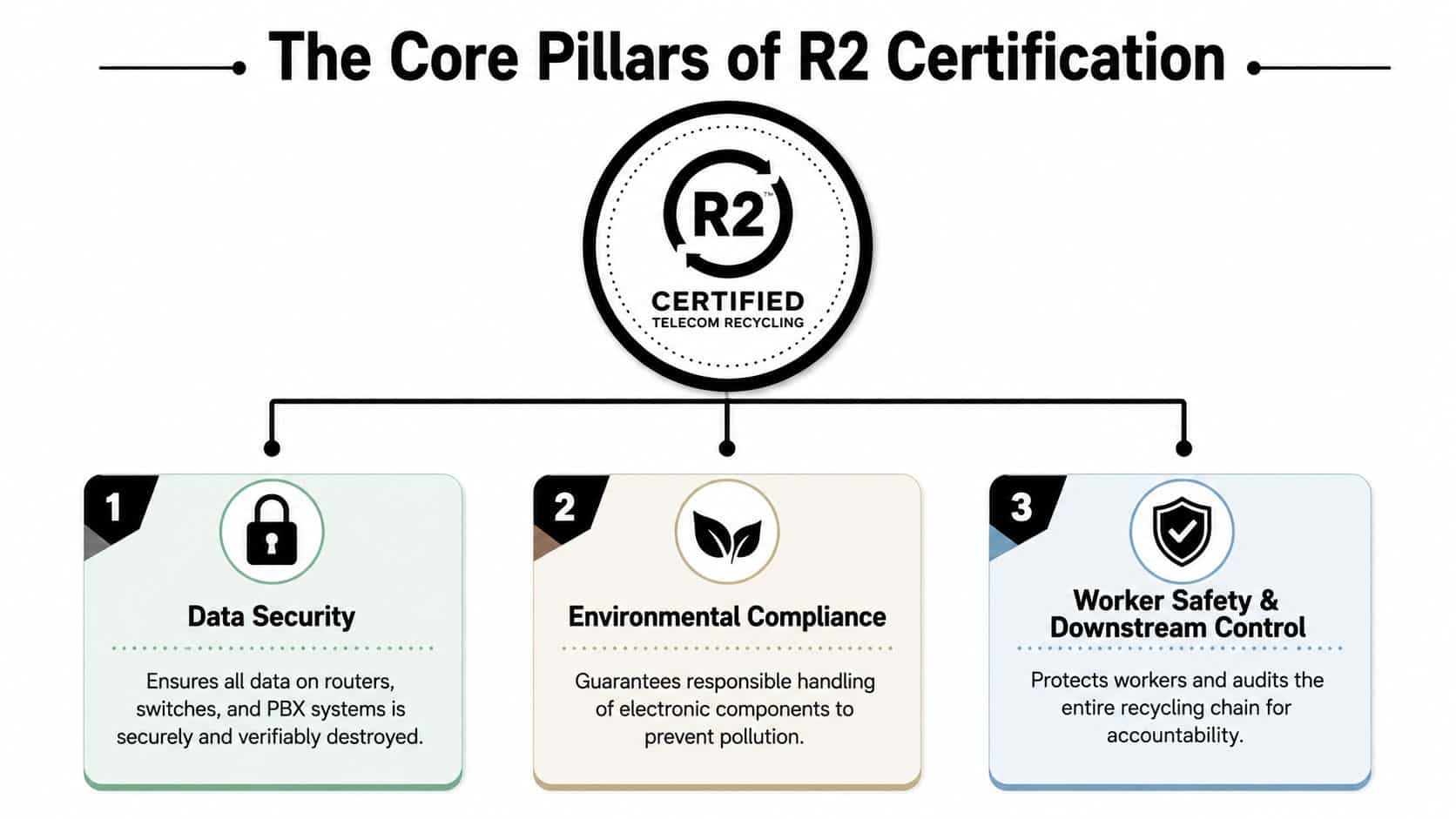
To see why R2 is so important for business equipment, it helps to look at what it’s built on. These principles are the backbone of the standard, making sure every step is accountable.
The table below breaks down the key pillars that define the R2 standard and explains why each one is so crucial when dealing with telecom assets.
The Core Pillars of the R2 Standard for Telecom Recycling
| Pillar | Description | Why It's Critical for Telecom Gear |
|---|---|---|
| Protect the Planet | Requires recyclers to manage materials in an environmentally responsible way and track hazardous e-waste to its final destination. | Telecom equipment contains materials like lead, mercury, and batteries. This pillar ensures they don't end up polluting landfills. |
| Protect People | Sets high standards for worker health and safety, ensuring employees are protected from hazards associated with processing electronics. | Dismantling network hardware can expose workers to sharp materials and harmful substances. This ensures a safe working environment. |
| Protect Data | Mandates that all data on used devices is completely destroyed according to industry-best practices before the equipment is resold or recycled. | Routers, switches, and servers store network configurations and sensitive corporate data. This pillar is your guarantee against a data breach. |
These three pillars work together to create a comprehensive system that protects your data, the environment, and the people handling the equipment.
Why R2 Is the Gold Standard for Telecom Gear
The R2 standard has become a major seal of approval in electronics recycling because it's built around third-party audits, documented tracking of all materials, and standardized processes. In the United States, the EPA officially recognizes only two accredited certification standards for electronics recyclers: R2 and e-Stewards. This means R2 isn't some niche label; it's one of the top-tier systems used to verify responsible recycling.
What really makes R2 stand out for telecom hardware is its specificity. The latest version, R2v3, includes Appendix D, which is designed specifically for specialty electronics like network gear that have a different lifecycle than consumer devices. This is a huge deal, as routers and switches contain mixed components, embedded data, and proprietary modules that demand careful handling.
R2 also has an appendix for facilities that process materials in-house, which helps strengthen the chain of custody for large-scale network retirements. For any business retiring assets from multiple locations, the certification's focus on documentation is what provides real peace of mind. To get a closer look at the standard, check out our complete guide that answers, what is R2 certification.
The Bottom Line: Partnering with an R2 certified recycler means you're not just hoping your assets are handled correctly—you have auditable proof. It’s the difference between crossing your fingers and knowing your security and compliance needs are fully met.
How R2v3 Modernized Telecom Asset Management
The Responsible Recycling (R2) standard isn't just a piece of paper; it’s a living document that grows and adapts to the rapid pace of technology. The latest version, R2v3, is a major leap forward, and it completely changes the game for how companies should handle retiring their telecom assets. Think of it less like a simple software update and more like a full system overhaul designed for the risks of modern IT.
If you’re an IT manager or business owner, getting a handle on R2v3 is non-negotiable. It raises the bar significantly for security, transparency, and accountability. This isn’t just about general recycling principles anymore—R2v3 digs into specific, auditable requirements for the entire journey of your retired electronics, from data-heavy routers to old circuit boards.
Key R2v3 Upgrades for Telecom Recycling
The R2v3 framework brought in much stricter rules that are especially important for telecom gear. These changes create a stronger system for managing not just the financial value of your old hardware, but also the data risks that come with it.
Here are the most important enhancements:
- Mandatory Data Flow Management: R2v3-certified recyclers must track and document the entire downstream path of any device that holds data. This means they have to know—and prove—exactly where your old switches, servers, and routers are going and how the data on them is being sanitized.
- Stricter Downstream Vendor Vetting: A recycler can’t just hand off your equipment to any old third party. R2v3 demands a tough due diligence process for every partner in the recycling chain, making sure each one meets the same high standards.
- Enhanced Data Sanitization Protocols: The standard now requires data destruction methods that align with gold-standard guidelines like NIST 800-88. It’s no longer enough to do a simple factory reset; vendors must provide clear documentation and a verifiable process for data erasure or physical destruction.
These requirements create a secure, transparent process you can trust. You're not just dropping off equipment anymore. You’re partnering with a vendor who is bound by contract and ethics to follow a documented, secure workflow. For companies also focused on the financial return, Beyond Surplus offers comprehensive services for large-scale telecom equipment liquidation, making sure you recover value while staying fully compliant with R2v3 standards.
The Power of R2v3 Appendices
One of the smartest changes in R2v3 was the addition of specific appendices. These aren’t optional—they are separate certifications for specialized skills. For managing telecom assets, two of them are absolutely critical:
- Appendix D – Specialty Electronics Reuse: This is for high-value equipment that can be tested, repaired, and sold back into the market. A lot of telecom gear fits this description. A vendor with Appendix D certification has proven they have the right processes to safely test and refurbish these assets to get you the most value back.
- Appendix E – Materials Recovery: This certification is for facilities that break down end-of-life electronics to recover raw materials like copper, aluminum, and precious metals. A vendor with this certification can process non-reusable items in-house, which tightens the chain of custody and reduces downstream risks.
When you're vetting a partner, asking which appendices they're certified for is a must. It immediately tells you if they have the specific skills needed to handle your entire telecom retirement project, from recovering value to final recycling.
The rapid growth of the R2 standard shows how effective it is. Today, more than 1,000 facilities across over 20 countries have earned R2 certification. This global footprint is crucial for the telecom industry, where equipment is often used across continents and needs to be retired under a consistent set of rules. R2v3’s focus on documentation provides a single framework, allowing a company to decommission hardware in multiple countries through one certified partner instead of dealing with a patchwork of local scrap handlers.

Securing Your Data During Telecom Recycling
For any IT manager, the biggest headache with retiring old hardware isn't the plastic or metal—it's the data left behind. An R2 certification is far more than an environmental promise; it's a security-first framework designed to protect your business by requiring secure, documented data destruction for all telecom equipment.
This focus on security is absolutely non-negotiable. Your routers, switches, servers, and even VoIP phones can hold a treasure trove of sensitive information, from network configurations and access credentials to cached corporate data. Simply unplugging these devices and sending them off for recycling without certified data destruction is an open invitation for a data breach.
Data Wiping vs. Physical Destruction
When it comes to making data disappear for good, not all methods are created equal. R2 certified recyclers use two primary, verifiable techniques to ensure your information is completely unrecoverable. Knowing the difference is crucial for making the right security call for your assets.
Think of it this way: deleting a file on your computer is like tearing a single page out of a phone book. Sure, that page is gone, but the rest of the book and all its information are still there. Certified data destruction, on the other hand, is like feeding the entire phone book into an industrial shredder until it’s nothing but confetti.
1. Data Wiping (Sanitization)
This method uses highly specialized software to completely overwrite a device's storage with random data, making the original information impossible to get back.
- Method: It follows strict standards like NIST 800-88 Purge, which is widely considered the gold standard for data sanitization.
- Best For: Newer, functional telecom gear that still has resale value. Wiping keeps the hardware intact for reuse.
- Verification: This certified process produces a detailed report proving the wipe was successful for each specific device, identified by its unique serial number.
2. Physical Destruction
This is the most final form of data destruction. It involves the physical shredding or complete disintegration of the device that holds the data.
- Method: Industrial-grade shredders grind hard drives, solid-state drives, and other media into tiny, unsalvageable pieces.
- Best For: Equipment that is at its end-of-life, damaged, or proprietary hardware where reuse isn't an option. It's also used when a company's policy demands total physical destruction, no exceptions.
- Verification: You are issued a Certificate of Destruction, which documents the date, method, and a full list of the assets destroyed, officially transferring liability.
Key Takeaway: An R2 certified partner doesn't just say they'll destroy your data; they follow auditable, documented procedures that align with federal standards and give you the paperwork to prove it.
Compliance and Regulatory Pressures
The need for certified data destruction isn't just a best practice—it's often a legal must-have. Regulations like the FTC Disposal Rule require businesses to take reasonable steps to protect consumer information on any discarded records and devices. Failing to do so can lead to massive fines and a damaged reputation that’s hard to repair.
Understanding how non-profits can secure student information highlights the universal importance of these strict security measures, which are just as critical for corporate telecom equipment. An R2 certified process gives you the documented proof needed to show you’ve done your due diligence and met your regulatory obligations.
An R2 certified partner helps you check all the right boxes by providing:
- A clear, auditable trail for every single data-bearing asset.
- Documented proof of destruction through official certificates.
- Processes that are built to align with federal guidelines from agencies like NIST.
For businesses looking to get their own practices in line with federal standards, you can learn more about how Beyond Surplus puts these rigorous protocols into action in our guide to NIST SP 800-88. By working with a certified expert, you ensure your company is shielded from both data breaches and regulatory heat.
A Practical Checklist to Vet Your R2 Recycling Partner
Choosing the right partner for R2 certified telecom recycling involves more than just checking a box. Simply asking, "Are you R2 certified?" isn't enough to protect your business from risk. True due diligence means you have to dig deeper into a vendor’s processes, capabilities, and documentation.
Think of this checklist as your playbook for asking smarter questions. It’s built to help your IT, procurement, and facilities teams conduct a real evaluation, separating the basic vendors from best-in-class partners who can actually manage enterprise-level compliance.
Essential Questions to Ask Your Potential Partner
Before you sign any agreement, your team needs clear, direct answers to these critical questions. A trustworthy R2 partner will have this information ready and will welcome the extra scrutiny.
"Can I see your current R2v3 certificate and its specific scope?"
- Why it matters: This is the most fundamental question. A certificate proves they are certified, but the scope tells you what they are actually certified to do. The scope document lists the exact processes and materials they are audited for, confirming they’re qualified to handle your specific telecom equipment.
"Which R2v3 appendices are you certified for?"
- Why it matters: Not all R2 certifications are created equal. Appendix D (Specialty Electronics Reuse) is crucial for telecom gear that still has resale value, while Appendix E (Materials Recovery) applies to partners who process end-of-life materials themselves. If a vendor lacks these, they are likely outsourcing key functions, adding another link to your chain of custody.
"Can you provide a sample Certificate of Data Destruction and a serialized inventory report?"
- Why it matters: This is your proof of compliance. A sample certificate shows you the level of detail you can expect, and a serialized report proves they track each asset individually. Vague, non-specific documentation is a major red flag.
By using this structured approach, you ensure your organization doesn't just offload old equipment, but creates a defensible, auditable trail of its disposition. For a more detailed framework, our vendor due diligence checklist provides an even deeper dive into the vetting process.
Comparing Basic Vendors and Best-in-Class Partners
The difference between a vendor that meets the minimum R2 standard and a true enterprise partner is huge. It often comes down to the level of detail, security, and transparency they provide. This comparison shows you what to look for when evaluating potential R2 certified telecom recycling services.
Comparing R2 Telecom Recycling Partners
| Evaluation Criterion | Basic R2 Vendor | Best-in-Class R2 Partner (e.g., Beyond Surplus) |
|---|---|---|
| Data Destruction | Offers basic data wiping or bulk destruction. | Provides NIST 800-88 compliant wiping and on-site shredding options with serialized certificates. |
| Asset Reporting | Provides a simple certificate of recycling with asset weights or pallet counts. | Delivers detailed, serialized inventory reports that track each asset from pickup to final disposition. |
| Value Recovery | May offer a lump-sum payment based on weight with unclear fee structures. | Offers transparent, itemized revenue sharing based on the fair market value of reusable telecom assets. |
| Logistics | Standard dock-to-dock pickup services. | Offers secure, GPS-tracked transport, on-site de-installation, and packing services by trained technicians. |
| Compliance | Mentions compliance but provides minimal supporting documentation. | Proactively provides all necessary documentation to support audits for FTC, HIPAA, and other regulations. |
As you can see, a best-in-class partner moves beyond simple disposal and acts as a strategic extension of your IT and compliance teams, offering services designed to protect your organization from every angle.

Why This Level of Scrutiny Is Necessary
The R2 standard has become vital for telecom asset disposition for good reason. The EPA confirms that R2 is one of only two accredited electronics recycling standards in the U.S. and recommends that recyclers demonstrate compliance through an independent third-party auditor.
That third-party structure is especially important when telecom equipment contains sensitive data. Certified recyclers are required to follow formal safety, documentation, and secure handling procedures from start to finish.
For enterprise IT leaders, that consistency reduces procurement risk and ensures a certified vendor can support every step of the process. This isn't just about theory; an implementation study of electronics recycling standards found that R2 programs are being implemented transparently and effectively across the industry.
The Right Partner Provides Proof, Not Promises: A best-in-class R2 partner doesn't just promise security and compliance; they provide the detailed documentation, transparent reporting, and specialized services to prove it. This turns your telecom retirement from a potential liability into a well-managed and documented business process.
Ensuring a Secure Chain of Custody for Your Assets
When your retired telecom equipment leaves your building, you need more than just a pickup. You need a documented, unbroken line of sight that protects your assets from the moment they're unplugged to their final destination. This is what we call a secure chain of custody, and it's the bedrock of any trustworthy R2 certified telecom recycling program.
Think of it like a bank moving cash. They don’t just toss it in a truck. Every dollar is counted, recorded, and sealed in a locked container. It's tracked from point A to point B, with signatures required at every single handoff. A proper chain of custody for your old telecom gear works exactly the same way, turning a potential headache into a documented, manageable process.
What a Secure Logistics Process Looks Like
A solid chain of custody isn't one single action but a whole system of connected, verifiable steps. It's designed from the ground up to prevent asset loss, data breaches, and compliance nightmares.
Here’s what that looks like in the real world:
- Serialized Asset Tracking: The process starts before anything even moves. Every single asset—every router, switch, and server—is inventoried by its serial number. This creates a master list that every following step is checked against.
- Secure On-Site Handling: Trained pros should be the ones de-installing and packing your equipment. Assets are carefully staged, palletized, and shrink-wrapped to stop any damage or loss during the move.
- Locked and Sealed Transport: Your gear should always travel in locked, GPS-tracked vehicles. For especially sensitive assets, using sealed cages or containers adds another layer of security, guaranteeing no one gets unauthorized access between your site and the processing facility.
- Access-Controlled Facilities: When the truck arrives, it's at a secure, monitored facility with tightly restricted access. The shipment is then checked against the original manifest to confirm every last item made it.
This disciplined approach means there are no blind spots where equipment could mysteriously disappear or be tampered with.
The Power of Documentation and Transferring Liability
The single most important job of a secure chain of custody is to generate the paperwork that legally transfers liability from your company to your recycling partner. This documentation is your official proof that you did everything right.
A Certificate of Data Destruction is the ultimate security document. It legally confirms that the data on your specified assets has been completely destroyed according to recognized standards. This is the document that officially shifts responsibility for data security from your shoulders to your certified partner.
Without this certificate, your organization is still on the hook for any data breach, even long after the hardware is gone. A simple "recycling receipt" just won't cut it. For a deeper look at this critical document, our guide on the Certificate of Destruction breaks down its legal importance.
Ultimately, a true R2 certified partner doesn't just pick up your equipment; they take full ownership of its security and compliance journey. They provide the concrete evidence you need to satisfy auditors, stakeholders, and regulators, giving you complete peace of mind.
Partnering with Beyond Surplus for R2 Certified Solutions
Choosing the right partner for your R2 certified telecom recycling boils down to one thing: trust. Who can you trust to handle the entire process, from pickup to final disposition, without creating security holes or compliance headaches?
At Beyond Surplus, we see ourselves as an extension of your IT, facilities, and compliance teams. Our services are designed specifically for the complex world of enterprise telecom retirement. This isn't just about hauling away old equipment; it's about providing a strategic, documented, and secure process that shields your organization from risk.
A Partnership Built on Certification and Expertise
Our R2v3 certification is more than just a line on a document—it's a verifiable promise that we follow the industry's most rigorous standards for data security, environmental protection, and worker safety. We specialize in managing complex enterprise gear, including high-value routers, switches, servers, and complete data center infrastructures.
We also know that decommissioning projects rarely happen in one place. Our nationwide pickup services ensure your assets receive the same secure, consistent handling, no matter where they are. Our logistics network is built to manage complex, multi-location projects without a hitch.
- R2v3 Certified Processes: We apply the highest standards to every project, ensuring your telecom assets are managed securely and in an environmentally responsible way.
- Nationwide Logistics: Our own fleet and trusted partners provide secure, GPS-tracked pickups across the contiguous United States.
- Specialized Expertise: We have years of experience with the unique challenges of telecom, data center, and lab equipment, guaranteeing proper handling from start to finish.

Uncompromising Security and Absolute Compliance
We understand that data security is your number one priority. It’s ours, too. That's why our entire process is built to give you undeniable proof of data destruction. We provide both on-site and off-site shredding, giving you the option to witness the physical destruction of your drives for complete peace of mind.
Our system is designed to provide all the paperwork you need to prove compliance and transfer liability away from your organization. You'll receive Certificates of Data Destruction confirming every device was sanitized to NIST 800-88 standards and Certificates of Recycling that legally move environmental responsibility to us.
Beyond Surplus is your compliance shield. Our services are designed to meet or exceed the requirements of regulations like the FTC Disposal Rule, HIPAA, GLBA, and SOX, providing you with an auditable paper trail that stands up to scrutiny.
When you work with us, you’re choosing a partner that puts your security first. We deliver detailed, serialized reports that give you full visibility into the disposition journey of every single asset. This isn’t a sales pitch—it's a promise backed by expertise. We are the trusted choice for secure, compliant, and efficient R2 certified telecom recycling.
Frequently Asked Questions About R2 Recycling
When you’re dealing with retired telecom equipment, a lot of questions about R2 certified recycling can pop up. Getting clear answers is key for any IT manager or business owner looking to make the right call on their asset disposal plan. Here are some quick insights into the questions we hear most often.
What Is the Difference Between R2 and e-Stewards Certification?
People often ask us about R2 versus e-Stewards. The short answer is, you're in good hands with a vendor certified for either one. Both are recognized by the EPA as top-notch standards for responsible electronics recycling.
Historically, e-Stewards earned its reputation for a very strict stance against exporting e-waste, which has always been a major issue in our industry.
The R2 standard, on the other hand, was developed by a wider group of industry experts. It puts a heavy focus on data security, worker safety, and building a transparent, fully documented recycling chain. The latest version, R2v3, has really raised the bar, especially when it comes to data security. For any business handling telecom gear, what matters most isn't just the name on the certificate, but the vendor’s specific R2v3 scope and appendices that prove they can handle specialized business hardware securely.
Is R2 Certification Necessary for a Small Number of Items?
Yes, absolutely. Using an R2 certified recycler is a best practice for any business, no matter how much equipment you have. A single retired router can still hold sensitive network data, and privacy laws like the FTC Disposal Rule don't offer exemptions based on quantity. Your organization is on the hook for protecting that data until it’s verifiably destroyed.
Key Takeaway: Partnering with an R2 certified recycler means every single item, from one switch to an entire data center, is managed with the highest standards for security and compliance. You get a Certificate of Data Destruction to prove you did your due diligence, which is a must-have for managing risk.
What Documentation Should I Get After Recycling?
Any legitimate R2 partner has to provide a clear, auditable paper trail. This documentation is what officially transfers liability from your organization to theirs, and it's your definitive proof of compliance for audits and regulators.
You should always expect to receive these three key documents:
- A Certificate of Recycling: This is the legal document that transfers all environmental liability for the equipment from your company to the recycling vendor.
- A Certificate of Data Destruction: This confirms that every bit of data on your assets was destroyed according to recognized standards like NIST 800-88, transferring data security liability.
- A Detailed Inventory Report: This gives you serialized tracking for each asset, creating a complete record of what was processed and tying it directly to your certificates.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. Schedule your nationwide pickup at https://www.beyondsurplus.com.



