After completing a network refresh, site consolidation, or data center shutdown, the hardware left behind is more than just old equipment. It consists of routers with configs still onboard, switches tied to production environments, optics, firewalls, chassis, cards, and spares that maintain resale value. The question isn't who will buy it. Instead, the question is who can take it off your hands without creating a security, compliance, or chain-of-custody problem for your team.
That's why evaluating nationwide telecom equipment buyers has to go beyond price sheets. A high bid means very little if the buyer can't document data destruction, control pickup logistics, or support an audit months later.
The Hidden Value and Risk in Surplus Telecom Assets
Most telecom surplus starts the same way. A carrier upgrade, WAN redesign, UC migration, or edge refresh leaves rows of decommissioned equipment waiting in a cage, storeroom, or loading area. Operations wants the space back. Finance wants recovery. Security wants proof that nothing leaves the building with data still exposed.
The scale matters. The telecom equipment market was valued at USD 654.65 billion in 2025 and is projected to reach USD 942.76 billion by 2031, according to Mordor Intelligence telecom equipment market data. For IT directors, that signals a simple reality. Huge deployment cycles create huge retirement cycles, and more decommissions mean more gear that has to be resold, recycled, or destroyed correctly.
Why old telecom gear is different
Telecom equipment isn't handled like generic office electronics.
- It may contain sensitive data such as saved configurations, credentials, call records, routing data, or customer-related information.
- It often has layered value because line cards, optics, power supplies, and chassis can each have different resale outcomes.
- It creates environmental obligations when batteries, boards, mixed metals, and non-remarketable hardware enter the disposition stream.
Practical rule: Treat every retired telecom asset as both a value-recovery item and a liability source until documented otherwise.
That changes how you approach buyers. A broker may be able to quote quickly. A recycler may be able to haul it away. But your responsibility doesn't end when the truck doors close.
What usually goes wrong
The most common failures are operational, not theoretical.
One team exports a partial spreadsheet with no serials. Another pallets equipment without separating working gear from scrap. Someone assumes the buyer will wipe everything later. Then the lot gets repriced, delayed, or rejected. In the worst cases, the equipment moves without the paperwork needed to prove what happened to the data-bearing devices.
If you're trying to recover value from telecom hardware, a structured resale process matters. If you need a reference point for what that looks like in practice, telecom equipment resale services generally start with inventory discipline, secure handling, and documented downstream processing.
Preparing Your Telecom Equipment for Sale
Preparation decides whether buyers compete for your lot or discount it. The fastest way to lose your advantage is to send vague descriptions like "miscellaneous Cisco switches" or "rack of telecom gear." Buyers price uncertainty into every offer.

Industry benchmarks show that a disciplined sale process starts with inventory and categorization, and poor categorization can cause a 25% loss in potential value, as explained in Beyond Surplus' guide to network equipment buyers in the USA.
Build an inventory buyers can actually use
A useful inventory sheet should let a buyer assess resale potential without guessing.
Include:
- Manufacturer and model such as Cisco ASR series, Juniper MX, ShoreTel, Mitel, or Polycom systems
- Serial number and part number so hardware can be verified and matched to market demand
- Configuration details like port density, optics, supervisor modules, power supplies, and installed cards
- Physical condition including dents, broken ears, missing faceplates, corrosion, or cut cables
- Functional status such as pulled working, powered on, untested, or known defective
If you want stronger offers, attach clear photos of front, rear, and asset tags. For larger projects, I recommend grouping equipment by platform and status rather than by room. Buyers think in resale pathways, not in where the gear sat in your building.
Separate remarketable from recycling candidates
Don't mix high-value equipment with obvious scrap.
A practical triage looks like this:
- Remarketable gear with clean identifiers, intact housings, and known demand
- Parts harvest inventory with reusable modules, fans, power supplies, or cards
- Recycling-only material with severe damage, missing components, or no resale path
Many enterprise sellers underperform in this area. They send one mixed lot and hope the buyer sorts it out. The buyer will sort it out, but the pricing won't favor you.
A documented lot nearly always gets cleaner bids than a mixed pallet with incomplete labels.
Lock down data before anything moves
Sanitization can't be an afterthought. Routers, firewalls, PBX systems, gateways, and certain storage-adjacent telecom devices may hold more information than internal stakeholders expect.
Your process should require:
- Device identification for data-bearing assets
- Wiping to recognized standards such as NIST 800-88 when appropriate
- Escalation to physical destruction when wiping isn't possible or practical
- Chain-of-custody records from the moment equipment is staged
For organizations that need an operational checklist before engaging buyers, this walkthrough on how to sell surplus telecom hardware is a useful reference.
Valuing Your Assets and Understanding Pricing
Valuation gets misunderstood because sellers often compare wholesale buyback offers to retail asking prices. Those aren't the same market. Nationwide telecom equipment buyers are pricing for testing risk, holding time, market demand, refurbishment cost, and resale margin.
What actually drives value
The strongest pricing usually comes from a mix of technical relevance and resale liquidity.
Buyers look closely at:
- brand reputation and installed base
- current demand for the platform
- licensing and firmware considerations
- port speeds and interface types
- whether the unit is complete, tested, and cleanly removed
A chassis with desirable cards can outperform a newer but less marketable unit. A common Cisco or Juniper platform may move faster than niche gear because more secondary buyers know how to deploy it.
For broader context on valuation logic, especially the difference between intrinsic value and market value, this overview of how to value a business is helpful. The same principle applies here. An asset is worth what a real buyer will pay in the market you're selling into, not what the original invoice says.
Set expectations around wholesale reality
For remarketable gear from top brands such as Cisco and Juniper, a realistic sale often reflects a 15% to 30% margin for the wholesale buyer, and 70% to 85% of well-documented inventory may sell within 30 to 60 days, based on the industry benchmarks already noted earlier.
That doesn't mean every item in the lot will move. It means the market rewards clean documentation, recognizable models, and practical resale paths.
Three value bands to keep in mind
| Value band | What it usually includes | Typical buyer view |
|---|---|---|
| Fair market resale | In-demand, identifiable, complete equipment | Competitive offer possible |
| Orderly liquidation | Mixed lots, slower-moving inventory, partial testing | Discounted but recoverable |
| Scrap or recycling | Damaged, obsolete, incomplete, or nonfunctional gear | Commodity or processing value only |
The mistake is forcing all assets into the top band. Experienced sellers don't do that. They maximize value by matching each asset to the right channel.
How to Evaluate and Vet Nationwide Buyers
The buyer you choose becomes part of your risk profile. That's why this decision belongs with IT, compliance, procurement, and whoever owns data governance. The right buyer won't just remove hardware. They will provide the documentation and handling controls that stand up when legal, audit, or cybersecurity teams ask questions later.
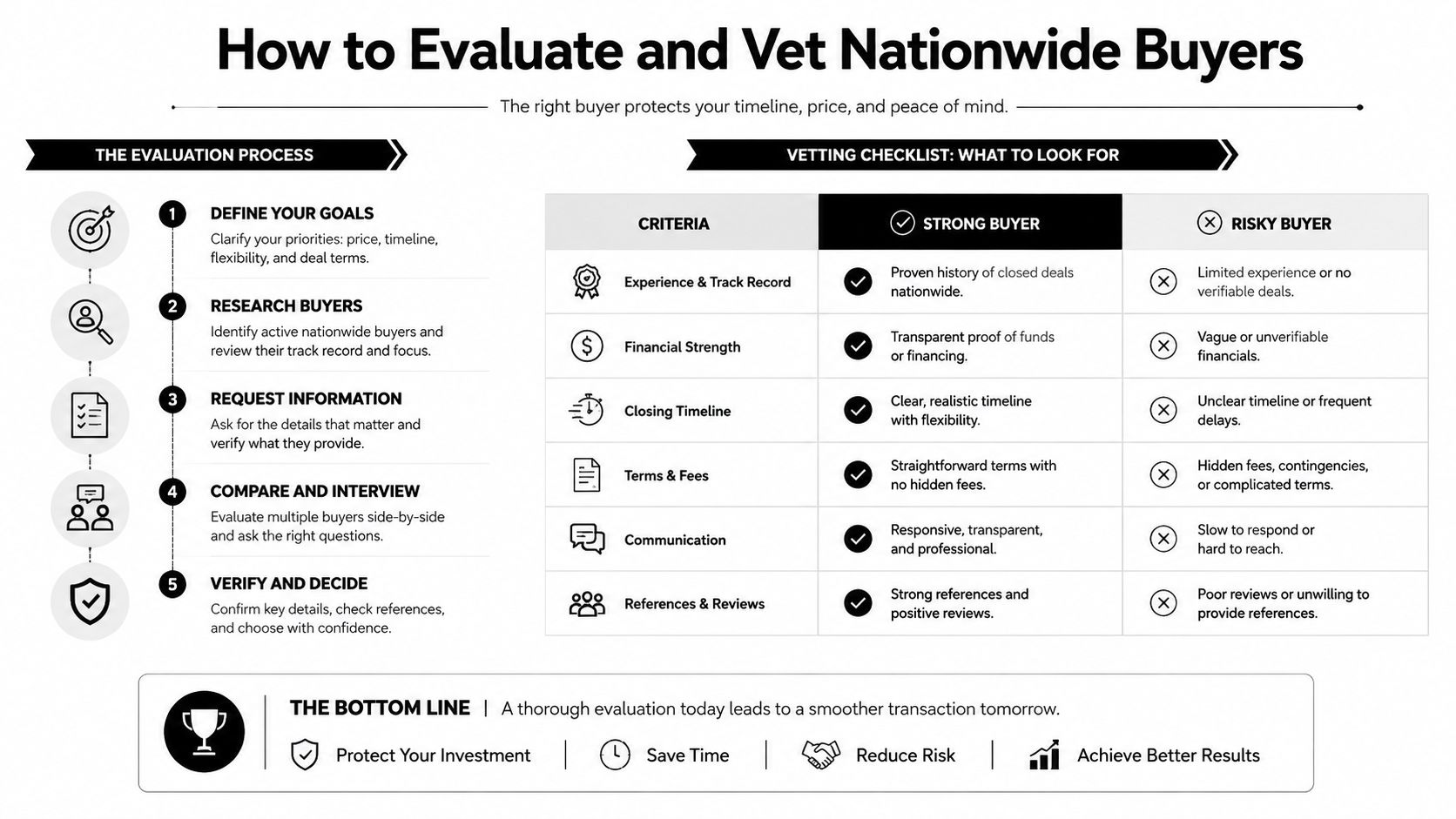
A critical market gap is compliance and liability transfer. Improper IT asset disposal costs U.S. firms an average of $4.88 million in 2025, and certified ITAD providers can issue Certificates of Data Destruction that transfer liability in a way brokers typically don't, as discussed in Beyond Surplus' overview of companies that buy telecom equipment.
What to ask before you approve any buyer
Start with direct questions.
- Who performs data destruction and is it done on-site, off-site, or through a subcontractor?
- What documents are issued after processing, and do they identify specific assets or lot references?
- How is chain of custody maintained from pickup through final disposition?
- What happens to non-remarketable gear that can't be resold?
- Can they support regulated environments with auditable handling procedures?
If the answers are vague, keep looking.
Comparison of Telecom Equipment Buyer Types
| Feature | Equipment Broker | Local Recycler | Certified ITAD Partner (e.g., Beyond Surplus) |
|---|---|---|---|
| Primary focus | Resale placement | Material processing | Secure disposition plus recovery |
| Data destruction documentation | Often limited or outsourced | May be limited | Typically formal and auditable |
| Chain of custody | Varies widely | May stop at dock receipt | Usually structured from pickup to final processing |
| Liability transfer support | Limited | Limited to recycling scope | Strongest fit for compliance-driven organizations |
| Suitability for regulated industries | Inconsistent | Inconsistent | Better aligned |
| Ability to manage mixed telecom lots | Depends on network | Usually low resale focus | Strong if resale and recycling are both needed |
Buy the process, not just the price. A slightly higher recovery figure can disappear fast if the paperwork fails under audit review.
What good vetting looks like in practice
Procurement teams should treat this like vendor due diligence, not surplus clearance. Review policies, sample certificates, transport controls, and escalation procedures for failed sanitization.
A formal vendor due diligence checklist helps standardize that review so the decision doesn't come down to who answered the email first.
Navigating Compliance and Documentation Requirements
Once a buyer is chosen, the documents matter as much as the shipment itself. If your organization is subject to internal audit, privacy controls, sector-specific rules, or customer security questionnaires, undocumented disposition is a weak point.
The U.S. telecommunications networking equipment manufacturing industry reached $4.5 billion in revenue in 2025, driven by 5G expansion and federal programs, according to IBISWorld's industry data on telecommunications networking equipment manufacturing. More hardware entering the field means more retiring assets that need compliant end-of-life handling.
The documents you should expect
At minimum, ask for two records after processing:
- Certificate of Data Destruction documenting how data-bearing devices were sanitized or destroyed
- Certificate of Recycling documenting downstream processing for non-remarketable material
Those documents should match your internal asset references or pickup lot numbers. Generic letters with no asset trail don't help much in an audit.
What makes a certificate defensible
A useful certificate should clearly show:
- the seller or client entity
- pickup or processing date
- asset identifiers, lot references, or supporting inventory attachment
- disposition method
- processor identity
- authorized signature or equivalent record control
If you work in healthcare, finance, education, or government, ask your legal or compliance team what they need preserved in the file. Don't assume the buyer's standard paperwork fits your policy.
The strongest documentation is specific enough that someone outside your team can reconstruct what happened to the equipment without asking for context.
For internal review and policy alignment, a sample destruction certificate template can help teams decide what fields need to appear before the first pallet leaves the site.
Managing Logistics for Nationwide Pickup
Logistics can destroy both value and control. Telecom equipment is heavy, rack-dense, awkward to pack, and easy to damage if a team treats it like routine office electronics.
Decide how hands-on the pickup needs to be
Some organizations can palletize internally. Others need full-service removal from data halls, MDFs, IDFs, branch sites, or warehouses. The right option depends on site access, staffing, and how much time your team can spare.
A workable pickup plan usually covers:
- palletizing or rack removal responsibilities
- labeling by lot or asset group
- dock access, liftgate needs, or inside pickup
- pickup windows and onsite contacts
- custody handoff at the point of loading
Protect the chain of custody in transit
Use sealed, labeled pallets when possible, and avoid loose mixed equipment. High-value modules, phones, and optics tend to disappear first when lots are poorly packed.
For multi-site programs, route planning matters more than expected. If you want a practical explanation of how sequencing pickups reduces delays and confusion, this article on route optimization explained is a useful operational read.
The best logistics process is the one your receiving, security, and facilities teams can all support without improvising on pickup day.
Your Next Step Schedule a Pickup with Beyond Surplus
Selling into the market of nationwide telecom equipment buyers isn't just a resale exercise. It's an end-of-life control process that touches data security, environmental handling, legal documentation, freight coordination, and value recovery.
If your team is staring at racks of retired telecom hardware, keep the decision framework simple. Inventory it correctly. Segment resale from recycling. Require data destruction records. Vet the buyer like a compliance vendor. Make logistics part of chain of custody, not a separate afterthought.
Operational discipline matters inside your own staging area too. If you're organizing pickup prep in a cramped cage or warehouse corner, some of the same principles in this guide to optimizing storage efficiency for small spaces apply well to temporary telecom asset marshalling.
When you're ready to move equipment, use a process that ties together pickup, documentation, and downstream handling. You can schedule a pickup or register for drop off once your asset list and internal approvals are ready.
Contact Beyond Surplus for certified electronics recycling, secure IT asset disposal, and nationwide telecom equipment pickup with documented data destruction and compliant downstream processing.