A network refresh usually ends with the same awkward scene. New circuits are live, cloud migrations are signed off, and the old room is still full of routers, switches, PBX gear, optics, UPS components, and patching that nobody wants to touch twice.
That pile isn't just leftover hardware. It's a mix of data-bearing assets, accounting questions, environmental obligations, and recoverable value. Enterprise telecom equipment disposal works well only when those issues are handled together. If one part breaks, the whole project gets messy fast.
The Modern Enterprise Challenge of Retiring Telecom Gear
An IT director rarely calls this project “disposal” at the start. It usually begins as a closure task after a carrier migration, a UC replacement, or a data center consolidation. Then facilities wants the space back, finance wants retired assets reconciled, security wants proof that nothing left with data on it, and operations wants the work done without disrupting production cabinets that are still in service.

Why the backlog grows so quickly
Telecom environments age unevenly. Core switches may be current while edge gear, legacy voice hardware, firewalls, and spares stay parked in closets or cages for years. That's how organizations end up with “temporary” storage areas full of hardware nobody has formally retired.
The scale of this end-of-life market is growing. The global enterprise IT asset disposition market is projected to grow from $8.67 billion in 2026 to $21.51 billion by 2034, according to Fortune Business Insights on the enterprise IT asset disposition market. That projection tracks what most infrastructure teams already feel on the ground. Hardware churn is faster, governance is tighter, and informal cleanup methods don't hold up.
What clients usually underestimate
The problem usually isn't identifying the obvious assets in the rack. The problem is everything around them:
- Stored equipment sitting in staging rooms, branch offices, and cabinets
- Mixed ownership records where leased, purchased, and capitalized assets are blended together
- Embedded storage inside telecom equipment that many teams forget to treat like a data-bearing device
- Unclear disposition paths for resale, redeployment, parts harvest, and recycling
Old telecom gear becomes risky the moment it loses an owner inside the organization.
For teams building policy from scratch, this e-waste and recycling guide for businesses is a useful high-level reference because it frames retirement work as a governance issue, not just a hauling job.
If your program needs a formal business recycling path, enterprise electronics recycling services in Georgia show the kind of service scope enterprise teams usually need: pickups, documentation, and controlled processing.
Why Strategic Disposal is a Non-Negotiable Business Function
Many companies still treat enterprise telecom equipment disposal like surplus removal. That's a mistake. Once equipment leaves controlled use, the business is exposed in three directions at the same time: data security, compliance, and environmental liability.
The risk sits inside ordinary hardware
A retired router or voice appliance may look harmless on a pallet. It isn't. Telecom equipment can retain call records, credentials, configuration files, authentication details, and network topology data. If retirement is handled casually, the organization creates a breach path with its own equipment.
The broader waste stream shows why disciplined handling matters. In 2019, the world generated 53.6 million metric tons of e-waste, with only 17.4% formally recycled, as noted by PICS Telecom's telecom sustainability statistics. For enterprises, that means a larger share of retired gear still moves through channels with weak controls or poor documentation.
Disposal affects more than compliance
A weak process usually creates problems in clusters, not one at a time.
- Security exposure: Devices leave the building without verified sanitization.
- Audit gaps: Asset records don't match what was removed.
- Environmental issues: Non-resalable equipment gets treated as scrap instead of routed through compliant recycling streams.
- Financial leakage: Functional assets lose resale value because they were mishandled, mixed, or stored too long.
What works and what fails
A strategic process works because it forces the organization to answer basic questions before pickup day:
| Issue | What works | What fails |
|---|---|---|
| Asset control | Serialized inventory and disposition records | Counting pallets or “miscellaneous network gear” |
| Data handling | Approved sanitization method by asset type | Assuming reset or reformat is enough |
| Value recovery | Triage before transport and testing after intake | Sending everything straight to scrap |
| Reporting | Certificates, audit trail, and final reconciliation | Email chains and handwritten load lists |
The real cost of poor disposal isn't the pickup invoice. It's the combination of missing equipment, unverifiable data destruction, and assets that should have been monetized.
When disposal is handled as a business function, the project gets easier to defend internally. Security sees control. Finance sees recovery and reconciliation. Sustainability teams get reporting they can use.
Phase 1 Assessment and Inventory Management
The first serious mistake in enterprise telecom equipment disposal happens before a single rack screw is removed. Teams skip the inventory discipline and jump straight to boxing, hauling, and “sorting later.” Later is where assets disappear.
Start with a disposition-grade inventory
A useful inventory isn't a room count. It's an asset register built for chain of custody, financial review, and downstream processing. Each item should be tied to a specific record before removal starts.
Capture at least:
- Asset identity: manufacturer, model, and device class
- Control point: site, room, rack, and where relevant, cabinet position
- Unique traceability: serial number or other unique asset identifier
- Physical condition: intact, damaged, incomplete, or missing components
- Disposition intent: redeploy, remarket, recycle, or hold for review
The rule that cuts through most confusion is simple. “If your team can't tie each retired unit to a serial number, location, and disposition path, you don't have a resale program, you have a cleanup project,” as stated in Beyond Surplus' enterprise telecom equipment resale guidance.
Build triage before removal
Inventory should feed triage. Don't move everything into one stream and hope someone figures it out later. Telecom assets usually split into a few practical categories.
Resalable gear
Current-enough equipment in usable condition with market demand and complete identifiers.Parts candidates
Units that may not be worth full refurbishment but still contain usable modules, faceplates, optics, or power supplies.Recycling-only assets
Damaged, obsolete, incomplete, or low-demand equipment that should go directly into controlled recycling.
Inventory is where value recovery begins. If the asset record is weak, every later decision gets weaker too.
How to avoid the “cleanup project” pattern
Most failed projects share the same symptoms:
- Teams inventory by pallet instead of by unit.
- Detached modules lose their parent chassis relationship.
- Branch office equipment is excluded because it seems too small to matter.
- Staged assets sit too long and become impossible to reconcile.
A better operating model is to use one intake standard across data centers, headquarters, and remote locations. The same fields should follow the asset from floor removal to final disposition.
For organizations managing larger footprints, telecom asset recovery services across the USA reflect the kind of serialized intake and logistics support that prevents those mismatches.
What a good inventory enables later
A disciplined register gives each stakeholder what they need:
| Stakeholder | Inventory outcome |
|---|---|
| Security | Verifiable list of all potentially data-bearing devices |
| Finance | Support for asset retirement and settlement review |
| Operations | Clear scope for de-installation crews |
| Sustainability | Defensible counts tied to final disposition records |
Without that foundation, everything downstream becomes harder to prove.
Phase 2 Navigating Data Destruction and Compliance
Data destruction is where enterprise telecom equipment disposal stops being a warehouse project and becomes a control process. Telecom devices often hold more than teams expect. Configuration files, routing information, call logs, administrative credentials, and cached records can remain on equipment long after service has ended.
Match the method to the asset and the risk
NIST SP 800-88 defines three sanitization levels: Clear, Purge, and Destroy. For high-security assets, physical destruction is the final standard, including shredding to particles smaller than 2mm, as summarized in this overview of telecom equipment recycling and sanitization methods. The same source notes that improper sanitization can create severe exposure under privacy and sector rules.
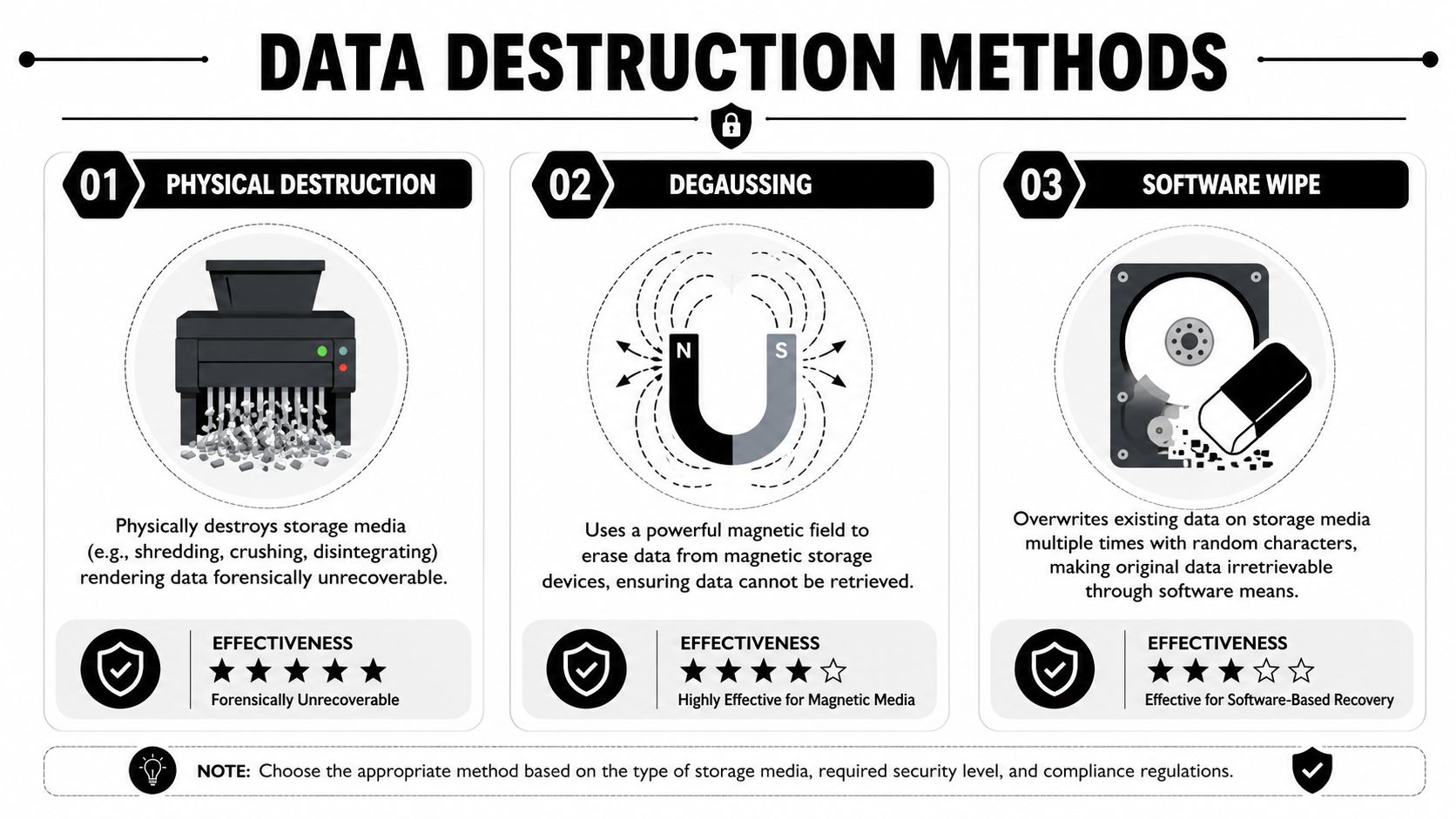
Three methods and when to use them
| Method | Best use | Main trade-off |
|---|---|---|
| Software wipe | Reusable assets headed for remarketing | Requires asset-specific validation and compatible media |
| Degaussing | Certain magnetic media | Doesn't fit every modern storage type |
| Physical destruction | High-security assets or failed media | Ends resale potential |
A software wipe is the right call when the business wants value recovery and the media supports certified erasure. Physical destruction is the safer choice when security requirements override resale, or when media condition prevents trustworthy wiping. Degaussing still appears in some programs, but it should never be treated as a universal answer.
What compliance teams should insist on
A compliant process has to produce evidence, not just activity. That means documented intake, sanitization decisioning, execution records, and final certificates tied back to specific assets or lots.
Look for these controls:
- Approved method selection: each device class should have a defined sanitization path
- Chain of custody: every handoff should be documented
- Exception handling: failed wipes, damaged drives, and inaccessible media need a defined fallback
- Certificates: final proof of destruction or sanitization should be issued and retained
A certificate matters only if it traces back to a controlled asset record and a documented process.
For teams aligning internal policies to an accepted standard, NIST SP 800-88 guidance for data sanitization is the benchmark reference to anchor that workflow.
The practical decision most teams face
The question usually isn't “wipe or shred?” It's “which assets can be wiped safely enough to preserve value, and which assets should be destroyed because risk outweighs resale?”
That decision should be made before pickup, not on the dock. Once mixed loads leave the site without a clear sanitization plan, the organization loses control over both risk and recoverable value.
Phase 3 Logistics De-installation and Value Recovery
The physical move matters more than many teams expect. A clean inventory and an approved data plan can still produce a poor outcome if removal crews damage units, separate matched components, or create custody gaps between the site and the processor.

De-installation is part of value protection
Telecom equipment loses remarketing value quickly when crews treat removal like demolition. Chassis get separated from blades, faceplates snap, rails disappear, and optics end up in unlabeled bins. Once that happens, even useful assets may fall into recycling-only status.
A disciplined de-installation plan usually includes:
- Site sequencing: identify live versus retired cabinets before work begins
- Component preservation: remove and pack modules with parent systems where appropriate
- Staging control: hold serialized assets in a secure area pending transport
- Load integrity: pack by asset type and disposition path, not by convenience
Chain of custody drives financial results
Logistics and ROI connect at this junction. The same controls that reduce risk also preserve resale options. Tracked transport, controlled receiving, and transparent reporting let the processor test, grade, and route equipment correctly instead of writing it off as mixed scrap.
According to Beyond Surplus' telecom equipment asset recovery services overview, R2v3 and ISO 14001 standards mandate transparent reporting, and proper ITAD with a tracked chain of custody can help telecom providers recover 10-20% of initial capital expenditure through certified buyback programs while cutting Scope 3 emissions by up to 80% compared to landfilling.
Secure logistics don't just protect the shipment. They preserve the asset's ability to be sold, harvested for parts, or recycled responsibly.
For teams that need a broader primer on transport handoffs and managed freight coordination, Coreties guide to freight forwarding is a useful operational reference.
What the best settlement reports show
A strong post-processing report should separate outcomes instead of hiding everything inside one scrap line.
| Disposition path | What you should see |
|---|---|
| Remarketing | Tested assets, grades, and settlement detail |
| Parts recovery | Identified salvage value where applicable |
| Recycling | Material handling documented through compliant streams |
| Destruction | Confirmation tied to prior asset controls |
If resale or liquidation is part of the strategy, telecom liquidation services are relevant because they connect retired inventory to downstream recovery instead of defaulting everything to commodity scrap.
Phase 4 Selecting Your ITAD Partner
A lot of vendors can remove hardware. Far fewer can support enterprise telecom equipment disposal in a way that stands up to security review, procurement scrutiny, and audit follow-up.

Ask for proof, not promises
Start with documentation. A credible ITAD partner should be able to show sample chain-of-custody records, certificates of data destruction, recycling documentation, and a settlement format before you award work.
The review should include:
- Certifications: ask which environmental and process standards the vendor operates under
- Data services: confirm whether they offer wiping, shredding, or both
- Logistics capability: determine whether pickup, de-installation, and regional or nationwide coordination are handled directly or outsourced
- Reporting detail: verify whether asset-level reporting is available where needed
Separate strategic providers from scrap haulers
A scrap hauler answers the pickup question. A strategic ITAD provider answers the control question.
Use this screen:
| Question | Strong answer | Weak answer |
|---|---|---|
| Can they track by serialized asset? | Yes, through intake to final disposition | “We count by pallet” |
| Can they support data-bearing telecom gear? | Yes, with defined sanitization paths | “We recycle everything” |
| Can they show final documentation samples? | Yes, before contract award | “You'll get paperwork later” |
| Can they support multi-site work? | Yes, with consistent process | “Depends on the location” |
One practical resource during procurement is a vendor due diligence checklist for ITAD programs. It helps procurement, IT, and compliance teams review the same controls instead of evaluating vendors in separate silos.
What to verify in the first call
Don't spend the first meeting on marketing language. Ask direct questions:
- How do you maintain chain of custody from site removal to receiving?
- What happens when an asset fails software sanitization?
- How do you document recycling for non-resalable equipment?
- What does the final financial and compliance package include?
Beyond Surplus is one example of a provider that offers pickup logistics, de-installation coordination, certified data destruction, and reporting for enterprise clients. That kind of end-to-end scope matters because telecom projects usually break when too many handoffs sit between removal, sanitization, and final disposition.
Your Enterprise Telecom Disposal Implementation Checklist
A workable program doesn't need to be complicated. It needs to be controlled. The best telecom retirement projects usually follow a simple sequence and resist the temptation to improvise midway through.
A practical rollout sequence
Define scope early
Identify sites, rooms, racks, and storage areas included in the project. Include branch and closet assets if they're in scope for retirement.Align stakeholders
Bring in IT, security, facilities, procurement, and finance before scheduling removal.Create the asset register
Record serialized assets and assign a preliminary disposition path.Set sanitization rules
Decide which device classes can be wiped and which require physical destruction.Plan de-installation and transport
Sequence the physical work so active environments aren't disrupted.Review documentation at closeout
Match final reports, destruction records, recycling records, and settlement details to the original scope.
A brief field example
A typical enterprise scenario looks like this. A company retires legacy VoIP platforms, edge switches, and stored spares after a network modernization. At first, the team treats the old gear as a facilities cleanup issue.
Then reality shows up. Several devices still have storage, asset ownership records are incomplete, and some cabinets contain gear that may still have resale value. The project improves once the team pauses, inventories by serial number, separates wipe candidates from destruction candidates, and uses a controlled removal and reporting process. Finance gets a clean retirement trail. Security gets documentation. Operations gets the room back without creating another backlog.
The most successful projects don't move the fastest at the beginning. They move the cleanest from inventory to final report.
The checklist to keep on your desk
| Project stage | Required output |
|---|---|
| Scope | Approved list of sites and asset categories |
| Inventory | Serialized asset register with location and condition |
| Security | Sanitization decision by device class |
| Logistics | Scheduled de-installation, staging, and transport controls |
| Processing | Clear paths for resale, parts harvest, and recycling |
| Closeout | Certificates, final reconciliation, and settlement review |
Enterprise telecom equipment disposal should reduce risk, satisfy compliance demands, and recover value where the equipment still has a market. If the process can't do all three, it isn't finished.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal, including telecom equipment de-installation, documented chain of custody, data destruction, and asset recovery support for enterprise organizations.