Your network refresh is probably already on the calendar. New switches are approved, firewall replacements are in procurement, and someone on your team is staring at racks full of retired gear that still looks too valuable to scrap.
That's the moment where many organizations lose money. They treat decommissioned telecom hardware as a disposal problem first, not an asset recovery event with security obligations attached. In regulated environments, that mistake gets expensive twice. Once when value is left on the table, and again if chain of custody, data sanitization, or downstream handling is weak.
Enterprise telecom equipment resale works best when it sits inside a disciplined ITAD process. The resale decision, the compliance workflow, the shipping plan, and the reporting package should all connect. If they don't, the project drifts into partial inventories, missing power supplies, disputed counts, slow pickups, and avoidable risk.
Your Next Tech Refresh Could Be A Major Revenue Stream
A typical refresh creates the same scene. Core switches come out first. Edge gear follows. Routers, firewalls, VoIP hardware, optics, line cards, and spares start collecting in a staging room. Finance sees old equipment. A strong ITAD strategist sees recoverable value.

The reason this matters is simple. The secondary market is established, active, and large enough to justify real process discipline. The refurbished enterprise networking equipment market was valued at USD 14.6 billion in 2024 and is projected to reach USD 35.2 billion by 2034, with a 9.2% CAGR. North America held a 36.7% share in 2024, generating about USD 5.3 billion in revenue, according to Market.us research on refurbished enterprise networking equipment.
That changes the conversation. Used telecom hardware isn't automatically e-waste. In many cases, it's inventory that still has demand if you identify it correctly, remove data risk, and route it through a buyer channel that understands enterprise gear.
What strong teams do differently
The strongest programs don't wait until the equipment is already off the network and mixed on pallets. They build resale into the refresh plan early.
- They identify likely resale items before de-installation. That includes routers, switches, firewalls, PBX systems, phones, optics, and spare modules.
- They separate remarketable assets from scrap immediately. Mixing everything together lowers recovery and increases handling errors.
- They assign one owner for inventory accuracy. Disputes usually start with bad counts, incomplete part numbers, or missing accessories.
Practical rule: If your team can't tie each retired unit to a serial number, location, and disposition path, you don't have a resale program. You have a cleanup project.
A structured telecom equipment buyback program gives IT and procurement a cleaner way to return dollars to the budget while maintaining disposal controls. That matters even more when legal, compliance, and finance all want the same answer to different questions: where did the gear go, who handled it, and what did the company recover?
What doesn't work
Late decisions. Mixed lots. No accessories. No documented sanitization. Those issues turn good hardware into low-confidence inventory.
Resale creates value, but only when the organization treats decommissioning like a controlled commercial process.
Where Your Used Telecom Equipment Actually Goes
Most organizations have three realistic resale paths. They can sell direct to another end user, work through a hardware broker, or hand the project to a full-service ITAD partner. Each route can work. The right choice depends on whether your priority is price, speed, internal workload, or risk transfer.
Direct sale
Direct sale can produce the strongest gross return on specific models, especially when your team knows the equipment, has clean records, and already has buyer relationships. It can also consume far more staff time than expected.
Your team has to identify exact configurations, field buyer questions, verify condition, manage packing, coordinate freight, and deal with claims if something arrives damaged or incomplete. For a procurement manager, this often looks attractive on paper and painful in practice.
Broker model
A broker sits between your organization and the eventual buyer. This usually reduces internal selling effort, especially for mixed lots or when market demand is uneven across models.
The trade-off is visibility. Some brokers are efficient and market-savvy. Others are mere middlemen with limited compliance depth. If the broker can't document sanitization, chain of custody, and downstream handling, the commercial convenience may create legal exposure.
Full-service ITAD partner
A capable ITAD partner combines asset recovery with data destruction, logistics, inventory management, recycling for non-resalable items, and reporting. That usually produces the cleanest operational outcome for enterprises with compliance requirements.
The price on any single item may not always match an ideal direct transaction. What you gain is process control, cleaner reporting, fewer internal touchpoints, and a better mechanism for handling everything that won't resell.
| Comparison of Telecom Equipment Resale Channels | |||
|---|---|---|---|
| Channel | Potential Return | Effort & Resources | Security & Compliance Risk |
| Direct to end user | Often highest on select assets | Highest internal effort | Highest if internal controls are inconsistent |
| Hardware broker | Moderate to strong, depends on network | Moderate effort | Moderate, depends on broker discipline |
| Full-service ITAD partner | Balanced return across mixed lots | Lowest internal burden | Lowest when documentation and controls are mature |
The best resale channel is the one your organization can execute cleanly, not the one that looks best in a spreadsheet before logistics and compliance show up.
A practical decision filter
Use direct sale when the lot is small, high-value, well documented, and your team can support the transaction. Use a broker when you need market reach but can still manage some operational details. Use ITAD when the project includes mixed equipment, secure handling requirements, or multiple sites.
If you're evaluating what buyers and processors do after pickup, this overview of what happens to recycled electronics helps clarify where resale, refurbishment, parts harvesting, and certified recycling diverge.
What usually fails is trying to force one channel onto every asset. High-demand units may deserve resale attention. Damaged, obsolete, or incomplete equipment may belong in a certified recycling stream from day one.
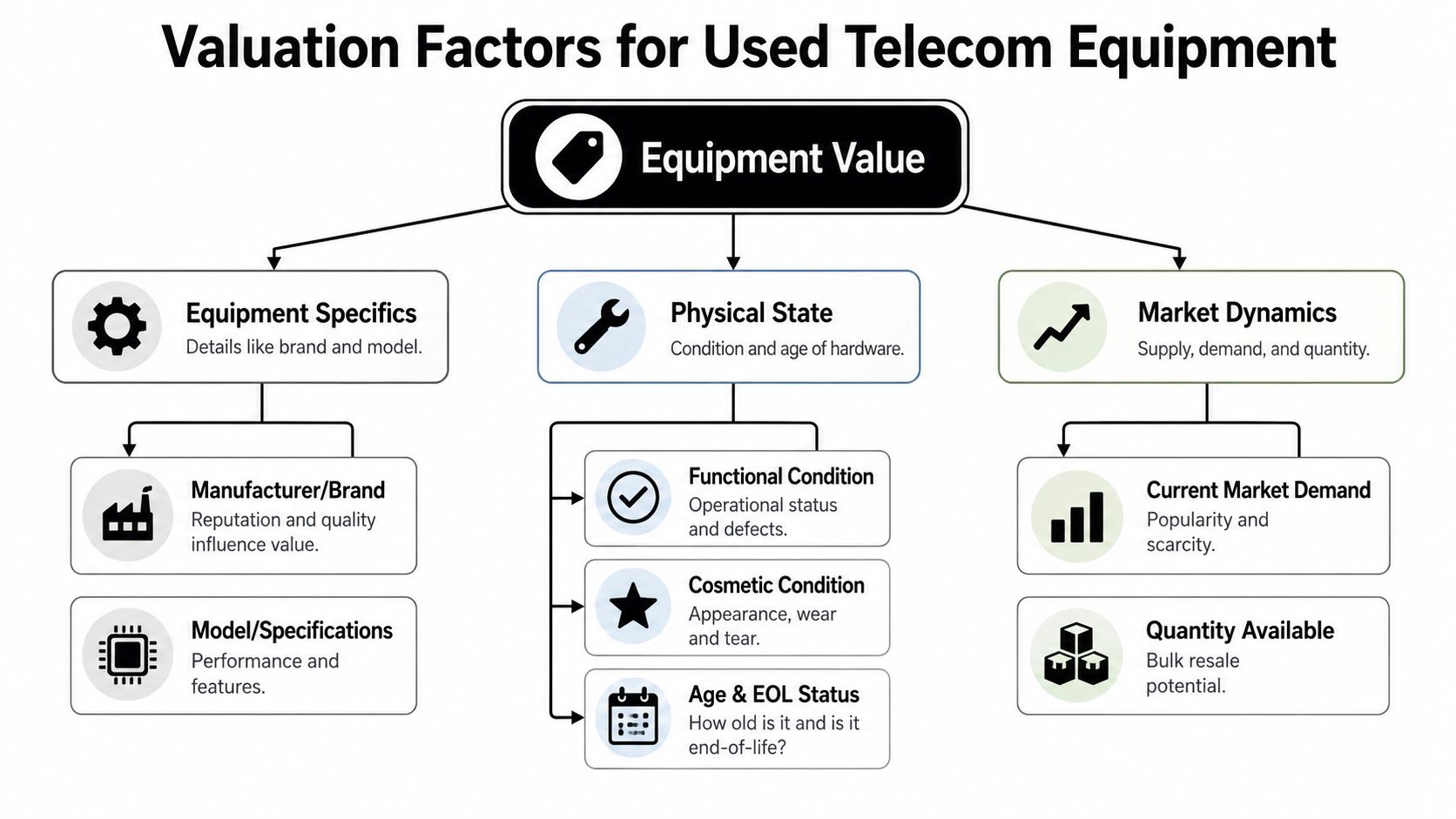
What Makes Your Old Hardware Worth Money
Telecom equipment doesn't hold value evenly. Two boxes that look similar in a rack can have very different resale outcomes because the market buys exact configurations, not generic categories.
The broader supply pipeline is substantial. The global telecom equipment market was valued at USD 314.6 billion in 2024 and is forecasted to reach USD 603 billion by 2034 at a 7.5% CAGR, which helps explain why refresh cycles keep feeding the secondary market with retired enterprise gear, as noted by Beyond Surplus on telecom equipment resale.
The equipment details buyers actually price
Brand matters, but part number matters more. Cisco, Juniper, Arista, Mitel, Nortel, Panasonic, Polycom, Shoretel, and Toshiba equipment can all attract interest in the right conditions. Still, buyers don't quote “used switch” or “used phone system.” They quote exact models, revisions, modules, and included components.
A useful internal review should capture:
- Manufacturer and model. The full identifier, not the shorthand your team uses internally.
- Installed components. Line cards, transceivers, supervisor modules, memory, licenses if transferable, and power supplies.
- Form factor and mounting hardware. Rails, ears, brackets, and faceplates matter more than many teams expect.
Condition is more than appearance
Functional condition drives value first. Cosmetic condition still matters because buyers use it as a proxy for storage quality and handling discipline.
A switch that powers on, passes test, and includes matching power supplies has a different resale path than one with bent rack ears, missing blanks, and unknown boot status. I've seen organizations lose value because they separated chassis from modules during decommissioning and never rebuilt the original configuration.
In resale, “complete and tested” beats “probably works” every time.
Age and support status
Older hardware can still sell. What hurts value is uncertainty around supportability, replacement parts, and demand from the installed base. Gear that's no longer attractive for mainstream enterprise deployments may still move into secondary use cases, lab environments, temporary deployments, or parts demand. But it must be identified accurately.
Large quantities can help, too. A buyer may pay more attention to a clean lot of matching units than to isolated singles scattered across sites. Standardization creates efficiency in testing, listing, and remarketing.
What procurement teams often miss
The hidden value leaks usually happen before the quote stage.
- Missing accessories reduce resale confidence.
- Bad inventory data forces conservative pricing.
- Delayed pickup can hurt marketability if the equipment sits exposed, gets mixed, or loses traceability.
- Incomplete segregation sends good hardware into scrap handling.
A specialized market for network equipment buyers in the USA is useful because these buyers understand exact telecom and networking SKUs, not just broad categories of used electronics.
If you want stronger returns, start with a disciplined asset list, preserve complete assemblies, and avoid treating decommissioned gear like surplus office furniture.
The Critical Steps for Secure and Compliant Resale
A telecom resale project can create value and still fail if the security controls are weak. For healthcare, finance, government, education, and any enterprise with contractual data obligations, resale starts with defensible sanitization and documented custody.
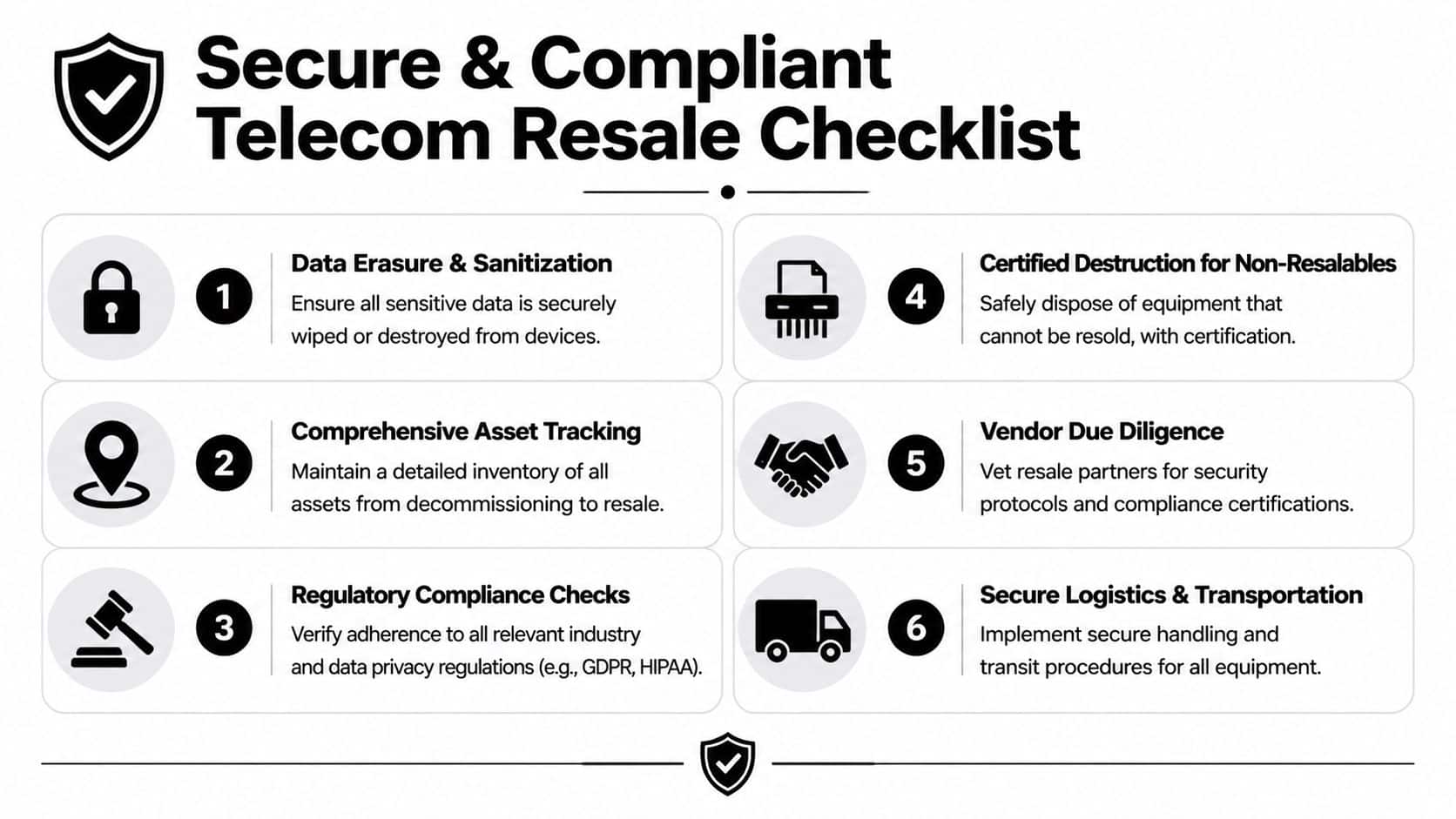
Start with data-bearing risk
Not every telecom asset stores meaningful data, but many do. Firewalls, routers, switches, PBX systems, VoIP servers, unified communications platforms, call recording systems, and management appliances may hold credentials, call logs, configurations, certificates, IP schemas, user information, or other sensitive operational data.
That means the first question isn't “What's this worth?” It's “What does this store?”
Build the process in the right order
A secure resale workflow usually follows this sequence:
- Identify data-bearing devices early. Don't assume networking gear is clean because it isn't a server.
- Apply a documented sanitization standard. For most enterprises, that means using a process aligned with NIST SP 800-88 guidance.
- Segregate devices that can't be sanitized for resale. If a unit fails sanitization or isn't suitable for remarketing, send it for certified destruction or recycling.
- Issue documentation. Certificates of data destruction and asset reports matter because legal, audit, and procurement teams will ask for them later.
Why liability transfer depends on documentation
A vendor saying “we wipe everything” isn't enough. You need records that show what was received, how it was processed, and what disposition path each asset followed.
That's where chain of custody becomes more than a logistics term. It's the evidence trail that proves the equipment remained under controlled handling from pickup through resale, recycling, or destruction.
Operational standard: If the reporting package can't answer an auditor's follow-up questions without extra emails and manual reconstruction, the process isn't mature enough.
Vendor due diligence matters more in regulated sectors
Enterprises often focus on the pickup date and the buyback number. Regulated organizations should focus just as hard on downstream controls.
Ask the vendor how they sanitize network equipment, how they verify completion, how they handle failed devices, and what proof they provide. Ask who touches the hardware after pickup. Ask where non-resalable material goes. Ask whether they can support internal policy reviews and legal holds when needed.
Some ITAD providers also coordinate recycling for what can't be sold. One practical example is Beyond Surplus, which offers secure data destruction, certificates of data destruction and recycling, logistics coordination, and telecom buyback within broader ITAD workflows. That combination is often more useful than working with separate firms that each handle only one piece of the project.
Environmental compliance still matters
Resale is not a loophole around environmental responsibility. Equipment with no resale path still needs proper downstream processing. A competent partner should be able to distinguish between remarketing, parts harvesting, and certified recycling without blurring the lines.
For IT directors, the objective isn't just asset recovery. It's controlled disposition with security, compliance, and audit defensibility built in.
Best Practices for Packing and Shipping Telecom Assets
Once the equipment is approved for resale, the physical handling starts affecting both value and risk. I've seen clean projects unravel because a team used the right buyer and the wrong packing method.

Prepare the inventory before the first box is sealed
Don't start packing until the asset list is finalized. The inventory should match the units being removed, including serial numbers, accessories, and site origin. If the list changes during de-installation, update it immediately.
That one step reduces disputes later. It also protects your organization if a pallet arrives short, damaged, or mixed with gear from another project.
Pack for shock, static, and stacking pressure
Telecom gear isn't hard to damage. Rack ears bend. Faceplates crack. Modules loosen in transit. Power supplies disappear when they're packed separately without labeling.
Use practical packing controls:
- Anti-static protection for components and sensitive assemblies.
- Foam or fitted cushioning so units don't shift inside cartons or cases.
- Clear accessory bundling so rails, cords, modules, and screws stay tied to the correct asset group.
- Pallet stabilization with shrink wrap and proper stacking to prevent crush damage.
Protect the chain of custody during transit
The shipping label isn't the chain of custody. The documentation is. You want a record of who packed the gear, when it left the site, which carrier or fleet handled it, and when the receiving facility acknowledged delivery.
That matters for two reasons. First, physical losses reduce recoverable value. Second, missing equipment creates security questions no one wants to answer after the fact.
Good logistics preserve resale value and security posture at the same time.
Avoid common shipping mistakes
Some failures are predictable.
- Loose packing of heavy chassis often causes cosmetic and structural damage.
- Mixing resalable gear with scrap creates confusion at receiving.
- Shipping unidentified modules separately leads to orphaned components that get priced down or recycled.
- Using generic movers without IT asset handling discipline increases breakage and custody gaps.
A disciplined shipping process keeps the commercial side intact. It also supports the compliance story, because custody doesn't stop when the truck leaves your dock.
A Checklist for Selecting Your Resale Vendor
Choosing a resale vendor is a procurement decision, not a cleanup task. The wrong partner creates hidden cost through weak reporting, poor downstream controls, and slow exception handling. The right one helps your team close a refresh with fewer surprises.
The questions that separate vendors
Start with documentation, not promises.
- Ask for sample reporting. You want to see inventory detail, final disposition categories, and destruction documentation before the project starts.
- Ask how they handle mixed lots. A vendor should explain what gets resold, what gets dismantled for parts, and what gets recycled.
- Ask what happens to failed or damaged assets. That answer tells you whether they have a real process or a sales script.
Check operational depth
A serious vendor should be able to explain how pickup, de-installation support, receiving, testing, sanitization, and remarketing fit together. If those functions are split across loosely managed subcontractors, your control over the project weakens.
Insurance and contractual clarity matter too. If there's loss in transit or a downstream issue, your team needs to know where liability sits and how claims are handled.
Evaluate the downstream network
Resale quality depends on buyer reach and product knowledge. A vendor that understands enterprise networking and telecom equipment will usually classify assets more accurately and route them more intelligently.
Reviewing a vendor due diligence checklist is a practical way to compare partners using the same criteria across procurement, IT, security, and compliance stakeholders.
A recycler removes equipment. A qualified ITAD resale partner documents it, secures it, and places it into the right downstream channel.
Use this shortlist before signing
Reporting quality
Can they show you the documents you'll receive at project close?Data handling discipline
Can they explain sanitization methods for telecom and network devices clearly?Logistics control
Do they manage pickup and transit in a way that preserves custody and equipment condition?Mixed disposition capability
Can they handle resale, destruction, and recycling in one program?Commercial transparency
Are valuation assumptions, exclusions, and reconciliation terms easy to understand?
The best vendor isn't necessarily the one with the highest opening quote. It's the one that can complete the project without forcing your internal team to solve preventable problems later.
Common Questions on Telecom Equipment Resale
Can we resell equipment that once held configuration data
Yes, if the device has been properly sanitized and the process is documented. The important point is not whether the device is a router, switch, firewall, or phone system. The important point is whether it stored sensitive data and whether that data was removed in a defensible way.
What if some equipment has no resale value
That's normal in almost every enterprise lot. Some assets should be resold. Others should move directly to certified recycling or destruction. Trying to force zero-value equipment into a resale channel usually adds delay and handling cost.
Do licenses transfer with the hardware
Sometimes, sometimes not. License transfer depends on the manufacturer's policies and the product type. Don't assume installed software or subscription rights move with the chassis. Validate that early, because non-transferable licensing can change the resale path.
Is a broker the same as an ITAD partner
No. A broker focuses on the transaction. An ITAD partner should manage secure handling, documentation, data destruction coordination, logistics, and recycling for anything that won't be remarketed. Some firms do both well. Many do only one side well.
Should we de-install everything before getting quotes
Usually no. Get enough inventory detail first to support a meaningful evaluation. Once equipment is removed and mixed, identification gets harder and value can drop. Photos, serials, model numbers, and accessory notes are worth gathering before teardown begins.
Can we include phones, PBX gear, and network hardware in the same project
Yes, and that often makes operational sense. One coordinated disposition event is easier to document and reconcile than multiple fragmented pickups, especially across several locations.
Contact Beyond Surplus if you need enterprise telecom equipment resale handled as part of a secure ITAD program, with documented chain of custody, data destruction support, and responsible downstream disposition.