An Atlanta IT manager usually notices the telecom problem late. A closet fills with retired switches, rack gear, PBX hardware, VoIP phones, antennas, and backup batteries after a network refresh, office move, carrier change, or merger. The equipment is out of service, but the risk isn't. A forgotten drive, an untracked serial number, or a vague recycling receipt can create audit trouble long after the gear leaves the building.
That pressure is why local telecom recycling services matter. This isn't just junk removal with pallets. It's a controlled handoff of assets that may contain data, licensed components, regulated materials, and residual market value. It also matters because only 20% of e-waste is properly recycled globally, with the rest often untracked or dumped, according to Sadoff Electronics Recycling's summary of e-waste data.
Atlanta businesses need a process that protects data, preserves documentation, and keeps downstream handling visible. A specialized provider for telecom equipment recycling gives you that structure. The practical questions are straightforward. What do you have, what carries data, what still has value, and what proof will you receive when the project is complete?
Your Guide to Managing Telecom E-Waste in Atlanta
The hardest part of telecom decommissioning isn't usually the lifting. It's the uncertainty. Teams know they need the room back. Procurement wants closure. Security wants proof. Finance wants idle services terminated and recoverable value captured.
That mix of objectives is where projects go sideways. The hardware leaves, but nobody can answer basic questions later. Which assets were picked up. Which drives were wiped or shredded. Which serial numbers were included in the final report. Whether the equipment was processed domestically or pushed into an opaque downstream channel.
Practical rule: If you can't trace an asset from rack or closet to final disposition, you haven't finished the job.
Atlanta organizations also face a local operations challenge. Telecom assets rarely sit in one neat pile. They may be split between branch offices, IDF closets, data rooms, warehouse shelves, and carrier demarc spaces. A workable plan has to bring those fragments into one disposal record without disrupting day-to-day operations.
Three priorities usually determine whether the project succeeds:
- Data security first: Treat any storage-bearing telecom gear as sensitive until verified otherwise.
- Compliance second: Require chain-of-custody records, destruction evidence, and recycling documentation that your auditors can use.
- Value recovery third: Separate reusable equipment from scrap early so you don't destroy resale value by accident.
Building Your Telecom Asset Inventory for Disposal
A disposal project gets easier the moment the inventory becomes real. Not approximate. Not "about four pallets." Real means a working asset list with enough detail for logistics, valuation, and chain-of-custody.
What your inventory needs to capture
At minimum, record:
- Asset identity: Manufacturer, model, serial number, and any internal asset tag.
- Physical location: Building, floor, room, rack, closet, or storage area.
- Condition notes: Working, untested, damaged, incomplete, or parts only.
- Data status: Contains drive, no drive, unknown, or requires verification.
- Disposition target: Reuse, buyback, recycle, shred, or hold for lease return.
This does more than help the recycler. It gives your team a document that legal, finance, security, and facilities can all use.
A good inventory also improves internal discipline before pickup day. Teams that already follow mature asset controls often borrow the same habits used in broader IT asset management for Indiana companies, where consistent tagging and lifecycle records prevent confusion at retirement.
Why inventory is the control point
An incomplete list creates problems that do not appear until later. Billing may continue on retired circuits or support contracts. A device may be wiped but never reconciled to a serial number. Finance may expect buyback revenue from equipment that was scrapped.
Use a simple spreadsheet if that's what your team can maintain accurately. A practical layout looks like this:
| Field | Example |
|---|---|
| Asset type | Router |
| Make and model | Cisco ISR |
| Serial number | Manufacturer serial |
| Asset tag | Internal ID |
| Location | HQ, MDF, Rack B |
| Condition | Powers on, untested ports |
| Data bearing | Yes, flash storage |
| Planned action | Wipe and resale review |
What works and what doesn't
What works is assigning one owner to the inventory and having site contacts validate counts before pickup. What doesn't work is letting each location use its own format and trying to merge conflicting records at the end.
Clean inventories reduce friction. Sloppy inventories force everyone to argue over exceptions.
For enterprise projects, barcode scans and serialized intake logs are ideal. But even when you don't have that infrastructure internally, you should still hand over assets in grouped, labeled categories. Separate tested network gear from obvious scrap. Keep leased assets on a different line item. Flag anything from healthcare, finance, or government environments for stricter review.
Navigating Secure Data Destruction Choices
Data destruction is the point where telecom recycling turns from operations into risk management. Old switches, servers, unified communications systems, firewalls, and PBX platforms often contain storage you can't afford to guess about.
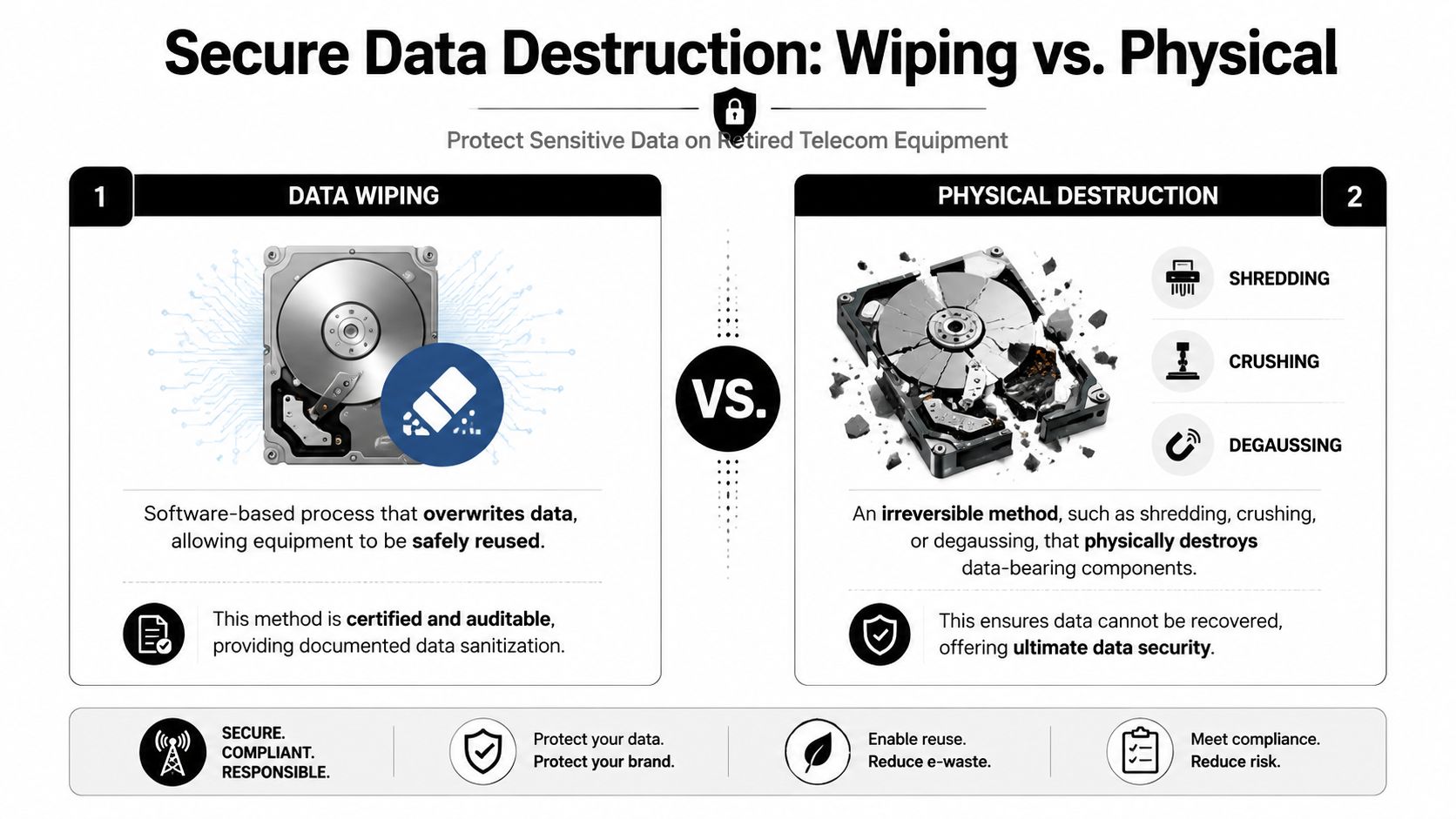
Wiping versus shredding
The first decision is whether the asset should be sanitized for reuse or physically destroyed.
Software sanitization preserves resale potential. Physical destruction eliminates the media entirely. Both have a place.
According to OEM Source's telecom recycling methods overview, certified data wiping using NIST 800-88 methods can make data recovery impossible on over 99.9% of drives, while physical shredding offers absolute certainty. The same source notes that incomplete inventory tracking can leave 20-30% of obsolete services on the books and still being billed.
If your security policy allows reuse, NIST SP 800-88 data sanitization is the standard to ask about by name.
Four common service choices
| Option | Best fit | Trade-off |
|---|---|---|
| On-site wiping | Reusable gear in controlled environments | Slower on premises, but strong verification |
| Off-site wiping | Larger mixed loads with resale potential | Requires confidence in chain-of-custody |
| On-site shredding | Highly regulated or highly sensitive assets | Fast assurance, no resale on destroyed media |
| Off-site shredding | Bulk destruction where efficiency matters | Lower site disruption, but less direct observation |
How to choose by risk profile
On-site wiping makes sense when the organization wants to preserve hardware value and keep visibility high during processing. It often fits branch consolidations, office closures, and telecom refresh projects where some gear may still be marketable.
Off-site wiping can be efficient for larger loads if the provider documents every serial number and returns sanitization evidence. This option only works when intake controls are disciplined.
On-site shredding is the conservative choice for regulated sectors and executive environments. If the drive cannot leave the facility intact under policy, this is your answer.
Off-site shredding is useful for volume. It can be operationally smoother, but the provider must close the gap with strong serialized reporting, sealed transport, and final destruction certificates.
If the media's existence would trigger a legal hold question, a board-level concern, or a breach response drill, don't choose the cheaper method by default.
Questions that reveal weak process
Ask these before pickup is approved:
- What standard governs wiping: If they can't clearly answer with NIST 800-88 or an equivalent documented method, keep looking.
- How is each drive verified: You want serialized reporting, not a blanket statement.
- What happens to failed media: A mature process escalates failed wipes to destruction.
- Can they separate reusable hardware from destroyed media: That split is where risk control and value recovery meet.
The wrong choice isn't always shredding or wiping. The wrong choice is selecting a method that doesn't match the asset's risk class.
Ensuring Environmental and Corporate Compliance
Compliance in telecom disposition isn't about saying the right words. It's about whether your paperwork would stand up in an audit, dispute, or breach investigation.

Certifications that actually matter
Many vendors say they're compliant. That phrase doesn't tell you much. What matters is whether they can tie their claims to recognized certifications and documented operating controls.
According to this Georgia-focused compliance discussion, many organizations choose ITAD vendors based on certification verification over price. The same source says regulated industries should look for R2, e-Stewards, or NAID AAA because auditable chain-of-custody and liability transfer matter under HIPAA, GLBA, and the FTC Disposal Rule.
A provider offering compliant electronics recycling in Georgia should be able to explain which controls apply to your industry and what documents you'll receive afterward.
What those documents protect you from
A certificate of recycling isn't just a courtesy PDF. A certificate of data destruction isn't just a closing packet. These records show that custody transferred and that the agreed method of processing occurred.
For IT directors and procurement managers, the practical value is clear:
- Audit defense: You can show what left, when it left, and how it was processed.
- Liability transfer: Your company isn't relying on informal email assurances.
- Vendor accountability: The recycler's representations become part of your compliance file.
Red flags during vendor review
Use this filter during procurement:
- Missing certification detail: If a vendor says "EPA compliant" but avoids specifics, that's not enough.
- Generic destruction language: "Data removed" isn't the same as documented sanitization or shredding.
- Weak downstream visibility: If they won't explain where materials go after intake, assume you have a blind spot.
- No sample certificate: Mature operators can show the structure of the reporting package before you sign.
A strong recycler reduces your burden of proof. A weak recycler hands it back to you when something goes wrong.
Healthcare, finance, public sector, and critical infrastructure teams should be especially strict here. Telecom assets often sit outside mainstream endpoint workflows, which means they can be missed in standard disposal reviews. That gap is exactly where compliance failures tend to appear.
Maximizing Value Recovery from Retired Telecom Gear
Not every retired telecom asset is scrap. Some loads contain genuine recovery value, but only if the provider separates reusable equipment from material recycling early and tests it correctly.

What usually holds value
In commercial telecom environments, recoverable value often sits in enterprise network hardware, newer switches, routers, transceivers, memory, processors, and certain modular components. Complete systems with clean provenance usually perform better than loose parts pulled from mixed pallets.
The appraisal process should look boring. That's a good sign. Serial check, cosmetic grading, power test where appropriate, component verification, and market review. Dramatic promises usually mean someone is quoting before they've seen the condition details that determine recovery.
One caution matters here. According to Beyond Surplus's Colorado electronics recycling page, up to 40% of U.S. devices given to some recyclers are exported offshore instead of being processed domestically. That matters for both environmental oversight and data security. If you're trying to recover value responsibly, use a provider with transparent downstream handling and a defined telecom asset recovery process.
What destroys resale potential
A few mistakes cut recoverable value fast:
- Mixing everything together: High-value gear tossed into gaylords with scrap metal often gets downgraded.
- Removing labels or tags: Missing serials make resale and audit reconciliation harder.
- Destroying media too broadly: Destroy the data-bearing component if needed, not the entire asset if the rest can be reused.
- Waiting too long: Telecom resale markets don't reward indecision.
The most profitable asset is usually the one your team identified early, stored correctly, and documented before the office cleanout started.
Set realistic expectations
Some equipment will have no resale value. That's normal. The gain comes from separating marketable items from non-reusable material instead of treating the whole load as waste.
IT directors should also expect the final settlement to reflect testing results, completeness, age, and demand. Honest recovery programs don't promise the same outcome for every switch, router, or voice platform. They classify, verify, and report.
Coordinating Logistics and Secure Pickup in Atlanta
Good logistics make secure recycling possible. Bad logistics undo everything you documented earlier.
For Atlanta pickups, the process should begin with site scoping. Identify loading dock access, freight elevator constraints, pallet count, loose equipment, cage requirements, and any after-hours rules. A provider with local telecom recycling services experience will ask these questions before trucks arrive.
What preparation should look like
Use simple staging rules:
- Palletize stable loads: Shrink wrap where needed and keep similar equipment together.
- Label exceptions clearly: Mark leased assets, media for shredding, and hold items.
- Control handoff points: Decide who signs custody documents on site.
- Limit informal adds: Last-minute "take this too" items are how records break.
For teams managing multiple sites, route planning matters more than many logistics managers realize. A useful outside reference is OnRoute's guide to route management, which explains why sequencing, timing, and stop design affect operational reliability.
A local option for Atlanta e-waste pickup should be able to support coordinated collection, documented transfer, and secure transportation without forcing your staff to improvise on loading day.
What to expect after pickup
The handoff shouldn't end with a truck leaving the property. Expect intake confirmation, reconciliation against the submitted inventory, exception reporting, and final documentation tied to disposition. If there are discrepancies, you want them surfaced immediately, not buried in a summary later.
Plainly put, the pickup is part of the security process, not a separate moving task.
Atlanta Telecom Recycling Checklist and FAQs
Use this checklist before approving any telecom disposition vendor in Atlanta.
Vendor vetting checklist
- Verify certifications: Ask which certifications support environmental handling and data destruction claims.
- Demand chain-of-custody detail: Require serialized intake, custody records, and final reporting.
- Match the destruction method to risk: Decide in advance which assets are wiped and which are shredded.
- Review downstream transparency: Ask where reusable and non-reusable material goes after intake.
- Confirm logistics controls: Know who picks up, how assets are secured in transit, and how discrepancies are reported.
- Check settlement methodology: For value recovery, ask how assets are tested, graded, and reconciled.
FAQs that come up on real projects
What happens to equipment with no resale value
It should move into documented material recycling, not disappear into a vague bulk category. You still need the same reporting discipline.
Can you handle leased telecom equipment
Yes, if the project is structured that way from the start. Keep leased assets segregated and tie them to the return obligation in your inventory.
How is value recovery paid or credited
That depends on the provider's settlement model. The important point is transparency. You want a clear reconciliation between the inventory received, the assets approved for resale, and the items processed as scrap.
What about a large data center or multi-site voice decommissioning
Those projects need phased pickups, stronger site coordination, and tighter exception handling. Don't run them as a standard office cleanout.
The safest telecom recycling project is the one that leaves a paper trail strong enough for security, finance, and legal to all sign off without guesswork.
If you're planning a telecom refresh, site closure, or full decommissioning, contact Beyond Surplus for certified electronics recycling and secure IT asset disposal with documented data destruction, chain-of-custody reporting, and commercial pickup support.