In many IT closets, the telecom refresh is already over, but the old gear is still sitting there. Routers, switches, VoIP phones, firewalls, access points, rack hardware, UPS units, and boxes of small peripherals often stay in limbo because nobody wants to guess wrong on data security, environmental handling, or residual value. For a facilities manager or IT director, that backlog isn't just clutter. It's unmanaged risk.
That's the essential context for sustainable telecom equipment recycling. It isn't about hauling away scrap and checking a sustainability box. It's a controlled business process for retiring equipment without creating a data exposure, a compliance gap, or unnecessary loss on assets that may still have reuse value. If you're managing a multi-site office footprint, a voice migration, a network modernization project, or a data center decommission, the difference between “remove it” and “dispose of it correctly” matters.
In Georgia, this comes up constantly because organizations often centralize old telecom hardware after relocations, acquisitions, and staged refresh cycles. By the time the project team is ready to deal with it, labels are inconsistent, storage media may still be installed, and chain of custody is already fuzzy. That's when discipline matters. A formal IT asset disposition process gives you a framework for inventory, secure handling, documented destruction, and downstream accountability.
Introduction The Challenge of Retiring Telecom Hardware
Why old telecom gear becomes a business problem
Telecom hardware ages in uneven waves. Core switches may be replaced on one cycle, branch routers on another, and IP phones only when a platform migration forces the change. The result is a mixed pile of equipment with different ownership statuses, different data risks, and very different resale prospects.
Some of it looks worthless but isn't. Some of it looks reusable but should never leave your control without verified sanitization. And some of it has no practical second life, which means your vendor's downstream process matters more than their pickup service.
Practical rule: If a vendor talks about “recycling” before asking about testing, reuse, storage media, or chain of custody, you're probably talking to a scrap handler, not an ITAD partner.
What managers are actually trying to solve
Most business clients aren't looking for a feel-good recycling story. They're trying to solve four operational problems at once:
- Data risk: Telecom equipment can store credentials, call records, configs, logs, or cached network information.
- Space pressure: Old gear takes up secured rooms, cage space, and warehouse shelves.
- Compliance exposure: Disposal records matter when auditors ask what happened to retired hardware.
- Value leakage: Functional assets lose resale potential the longer they sit unmanaged.
That's why sustainable telecom equipment recycling works best when it starts with disposition planning, not with a truck arriving at the dock.
What Sustainable Telecom Recycling Really Means
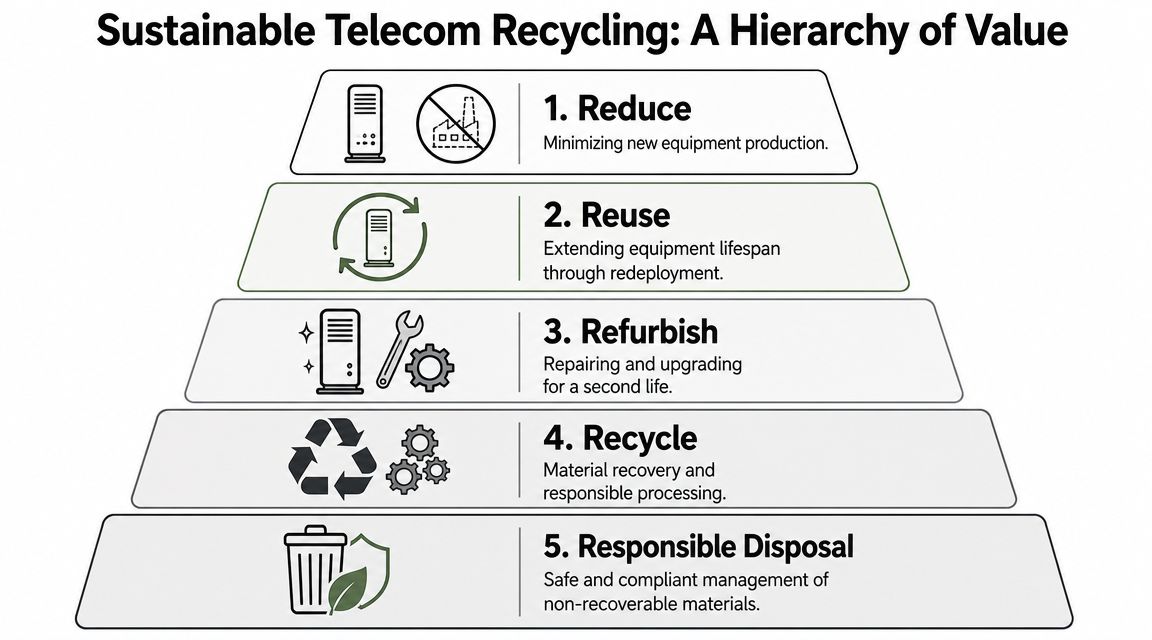
Sustainability in telecom disposition follows a simple hierarchy. Keep equipment in productive use if possible. If it can't stay in service as-is, restore it. If that fails, recover materials responsibly. Disposal sits at the bottom because it preserves the least value.
The value pyramid that actually matters
A useful way to think about sustainable telecom equipment recycling is as a value pyramid:
- Reduce: Buy and deploy with lifecycle in mind so you don't over-purchase or replace too early.
- Reuse: Redeploy working gear internally where performance and security requirements allow.
- Refurbish: Test, clean, repair, reset, and grade equipment for a second life.
- Recycle: Recover metals, plastics, boards, and other fractions after reuse options are exhausted.
- Responsible disposal: Handle non-recoverable materials safely and compliantly.
This is why “we shred everything” is not a sustainability strategy. It may be necessary for specific media or failed assets, but as a blanket approach it destroys recoverable value and skips the most circular options.
Reuse comes before recycling
A reuse-first model is not theoretical. Telefónica's circular economy work reports that 75% of collected electronic equipment is reused and the remaining 25% recycled, and it also reports reusing more than 4 million devices in a year. That's the distinction many vendors blur. Real sustainability is measured by how much equipment avoids end-of-life processing in the first place.
For managers evaluating vendors, the practical question is straightforward: what percentage of collected assets are tested for continued use before material recovery begins? If that answer is vague, sustainability claims usually are too.
The most sustainable outcome for a functioning device is not better shredding. It's continued use under controlled, documented conditions.
What this looks like in the field
In practice, this means a provider should have a triage workflow. Cosmetic damage shouldn't automatically push a device into the recycling stream. A router with a scratched enclosure may still be perfectly suitable for redeployment after inspection, reset, and testing. The same logic applies to phones, access points, and some server-adjacent networking hardware.
For procurement teams comparing replacement versus secondary-market sourcing, reviewing examples like refurbished iPhones can help illustrate how refurbishment works in mature device categories. The principle is the same in enterprise telecom. Tested, graded equipment can keep delivering value long after its first deployment.
Organizations that want a local framework for this broader approach can also review sustainable electronics recycling in Georgia, especially when telecom and general IT assets are retired together.
Environmental and Regulatory Drivers for Your Business
The sustainability case gets attention, but most business programs move forward because risk becomes impossible to ignore. Telecom equipment sits inside the larger e-waste stream, and the scale of that stream is moving in the wrong direction.

The environmental pressure is real
According to the UN Global E-waste Monitor 2024, the world generated a record 62 million tonnes of e-waste in 2022, and that volume is projected to rise to 82 million tonnes by 2030. The same source reports that only 22.3% of the 2022 total was formally documented as collected and recycled.
For a business, that matters because retired telecom gear doesn't disappear when it leaves your site. If your downstream process is weak, your hardware can move through opaque channels with little accountability. That creates environmental exposure and reporting problems, especially for companies with ESG commitments or supplier oversight requirements.
Compliance is about control, not paperwork
Regulatory pressure doesn't only come from e-waste rules. It also comes from privacy, contractual obligations, and internal governance. A switch, firewall, IP phone system, or edge appliance can contain stored configurations and operational data that your security team would never knowingly release without sanitization. Yet that's exactly what happens when retired equipment gets handled as generic scrap.
A disciplined process aligned with EPA universal waste handling principles helps reduce that risk because it forces the organization to treat retired electronics as controlled assets, not office trash.
What doesn't work
Three habits cause most of the trouble:
- Bulking unlike assets together: Network gear, batteries, drives, and peripherals shouldn't all move under one vague label.
- Skipping audit trails: If no one can show who packed, moved, received, and processed the assets, your documentation is already weak.
- Choosing on haul-away price alone: The cheapest quote often assumes the least labor in testing, sorting, reporting, and secure handling.
Cheap pickup can become expensive remediation if an auditor, customer, or legal team asks where the equipment went and what happened to the data.
The Secure End-to-End Recycling Process Explained
A professional telecom disposition workflow should be boring in the best sense of the word. Every step is documented. Every handoff is controlled. Every final outcome is defensible.

Step one decommission and identify
Start on-site. Equipment should be disconnected methodically, labeled, and matched to an inventory record before it leaves the room. Projects often go wrong at this stage if teams rush. A pallet of “miscellaneous network gear” is a custody problem waiting to happen.
At minimum, the decommission phase should separate assets into categories such as redeployable hardware, data-bearing devices, leased units, and obvious end-of-life material. If serials or asset tags are still available, capture them here, not later.
Step two secure transport and chain of custody
Once the equipment is off the floor, logistics takes over. Containers, pallets, gaylords, or sealed transport methods should fit the asset class and the handling risk. For multi-site businesses, consistency matters more than improvisation. Every site should follow the same intake and release procedure.
The key output here is a clear chain of custody. You should be able to answer who released the assets, when they moved, who received them, and whether counts reconciled at intake.
Step three data destruction
Not every telecom asset stores the same kind of data, but enough do that you can't rely on assumptions. Firewalls, call managers, PBXs, routers, unified communications systems, storage modules, and some printers or multifunction devices all need review. The sanitization method depends on the media and the reuse decision.
A provider following NIST SP 800-88 guidance should be able to explain when they wipe, when they purge, and when they physically destroy media. If they can't explain that plainly, they probably aren't running a mature process.
If the asset can be reused safely after verified sanitization, preserve the asset. If it can't, destroy the data-bearing component and document it.
Step four triage testing and remarketing review
After data risk is addressed, the next decision is functional. Does the equipment deserve a second life? At this stage, sustainable telecom equipment recycling becomes more than a disposal event.
A serious triage process usually includes:
- Functional testing: Power-on checks, port tests, diagnostics, and firmware review.
- Configuration reset: Removal of tenant-specific settings and credentials.
- Cosmetic grading: Sorting by resale, redeployment, or parts-harvest potential.
- Channel decision: Redeploy, refurbish, remarket, harvest parts, or recycle.
Step five materials recovery
When equipment reaches end of life, the technical quality of the recycling process matters. NGMN eco-design guidance states that equipment should be designed for disassembly and separation into recycling fractions, and the same source notes that SK tes reported processing over 70,000 metric tonnes of e-waste in 2020 with 98.7% of materials recycled. That's a reminder that high-yield recovery depends on design, sorting, and capable downstream processing. It does not happen automatically.
For managers, this affects purchasing as much as disposal. Equipment with removable boards, standard fasteners, accessible cabling, and clearer material separation is easier to process responsibly later.
Navigating Compliance and Industry Certifications
Certifications matter because they reduce guesswork. In telecom recycling, that's not branding. It's risk control.

Why certifications change the conversation
Any vendor can promise secure recycling. An audited certification program requires them to prove process discipline. For most business buyers, the key point isn't memorizing every standard. It's knowing whether the vendor operates under independent controls for environmental handling, downstream accountability, and data security.
That's why many organizations ask first about R2 certification requirements. It gives procurement, legal, and compliance teams a common baseline for evaluating recycler maturity.
Regional gaps make vendor quality more important
The global e-waste statistics summary highlights the operating gap across regions. Europe documented 6.0 million tonnes recycled in 2022, equal to 46% of its 13.1 million tonnes of generated e-waste, versus the global average of 22.3%. For businesses, the lesson is simple. You can't assume local infrastructure alone will protect your assets. Vendor controls matter.
The documents you should insist on
At closeout, the paperwork is part of the service. You should expect records that support audits, internal controls, and customer due diligence.
- Certificate of data destruction: Confirms the sanitization or physical destruction method used for covered media.
- Certificate of recycling: Documents downstream disposition for processed material.
- Asset inventory report: Shows what was received and how it was categorized.
- Chain-of-custody records: Supports defensible transfer of control.
A vendor that avoids detailed documentation is asking you to accept their story instead of their records.
Building Your Telecom Asset Disposition Program
Most companies eventually face the same decision. Build an internal program for telecom retirement, or hand the process to a specialized vendor. The right answer depends on asset volume, internal staffing, security requirements, and how often these projects occur.
In-House vs. Vendor-Managed Telecom Recycling
| Factor | In-House Program | Vendor-Managed Program (e.g., Beyond Surplus) |
|---|---|---|
| Cost structure | More direct control, but internal labor and training can be underestimated | External service cost, but fewer hidden labor demands |
| Data handling | Depends on internal tools, procedures, and staff consistency | Usually stronger if the vendor has formal sanitization workflows and documentation |
| Logistics | Harder for multi-site or phased projects | Better fit for pickups, de-installs, palletization, and transport coordination |
| Reuse and resale | Often limited by lack of testing and remarketing channels | Better when the vendor has triage, grading, and secondary-market outlets |
| Compliance records | Must be built and maintained internally | Usually standardized and easier to audit |
| Scalability | Works for small, infrequent projects | Better for recurring refreshes, relocations, and data center work |
| Liability control | Stays largely with your team until final disposition is proved | Easier to transfer operational responsibility with complete documentation |
When in-house works
An internal program can work if you have a narrow asset mix, a small number of locations, experienced security staff, and enough process discipline to maintain inventory and custody records. It also helps if you already own approved sanitization tools and have a reliable downstream recycling network.
When outsourcing usually wins
Outsourcing makes more sense when telecom retirement is intermittent but high stakes. That's common in branch closures, UC migrations, M&A integrations, and rack decommissions. In those cases, specialized labor, packaging, secure transport, and reporting are hard to replicate internally without pulling staff off core work.
A practical vendor checklist should include:
- Security scope: Ask how they identify data-bearing telecom hardware.
- Reuse workflow: Ask whether testing happens before material recovery.
- Downstream transparency: Ask what documentation they provide after final processing.
- Logistics capability: Ask who performs pickup, de-installation, and freight coordination.
- Exception handling: Ask how leased or customer-owned assets are separated.
Maximizing Value Recovery and ESG Reporting
The strongest telecom disposition programs don't treat all retired equipment as waste. They sort for value first, then process what is at end of life. That changes the economics of the project and improves the quality of sustainability reporting.
Where value actually comes from
Residual value usually survives in newer network gear, branded telecom systems, business-class phones, and equipment with healthy demand in secondary channels. But that value isn't realized by pickup alone. It depends on testing, cleaning, firmware reset, grading, and a realistic remarketing path.
Deutsche Telekom's circular economy reporting offers a useful benchmark. It says more than 4.6 million CPEs were taken back in 2024, and 44% were refurbished. That is the operational difference between a value-recovery program and a scrap program.
Why this matters for ESG teams
Reuse and refurbishment produce cleaner reporting than vague claims about landfill diversion. They show that assets stayed in productive use longer, which is the core of circular practice. For sustainability teams, that makes reporting more credible because the data connects to actual disposition outcomes instead of generic environmental language.
For finance and procurement, value recovery can offset retirement costs. For ESG reporting, disposition records can support disclosures around reuse, recycling, and controlled end-of-life management. For operations, the same reporting creates a cleaner archive for audits and internal reviews.
One example of a service category businesses often use for this purpose is IT buyback and value recovery, where resale-capable assets are evaluated before they're pushed into a recycling stream.
Your Next Steps and Common Questions
Start with an inventory. Separate what may contain data, what may still have market value, what is leased, and what is clearly end of life. Then choose a process owner and require documented custody from the moment assets leave service.
Common questions
Is reselling always better than recycling
No. If the device can't be sanitized, tested, or supported in a compliant secondary channel, recycling is the safer path. Reuse only works when control stays tight.
What is the biggest risk in telecom disposal
Data exposure is usually the first concern. Telecom and networking hardware often carries more retained information than teams expect.
How should leased equipment be handled
Keep leased assets segregated from owned equipment. Confirm return terms, data handling requirements, and approved disposition paths before anything is shipped.
How do you know a recycler is really sustainable
Ask for evidence of reuse-first triage, downstream documentation, and certification-backed controls. Broad green claims without process detail don't tell you much.
If your organization is planning a telecom refresh, office closure, migration, or decommission project, contact Beyond Surplus for secure telecom equipment recycling, documented data destruction, and business-focused IT asset disposition support.



