For any thriving business in Georgia, figuring out what to do with old IT assets is a huge part of managing risk, keeping data secure, and even making smart financial moves. When we talk about IT equipment recycling in Georgia, it’s not just about tossing old gear in a bin. It's about partnering with a certified specialist who can guarantee your data is destroyed, environmental rules are followed, and you get back any potential value from those old devices. At Beyond Surplus, we deliver certified electronics recycling and IT asset disposal services exclusively for commercial and enterprise clients across Georgia.
Why Smart IT Equipment Recycling Matters for Georgia Businesses
Georgia is a major hub for tech companies, data centers, and corporate headquarters, meaning the pile of outdated servers, laptops, and networking gear is growing faster than ever. Every single one of those retired devices, whether it's a lone corporate laptop or a whole rack of servers from a data center decommissioning, is packed with sensitive data and materials that can be hazardous if not managed correctly.
Getting this wrong isn't a minor slip-up—it's a massive business risk. The fallout can be brutal, exposing your company to devastating data breaches, eye-watering regulatory fines, and long-term damage to your brand's reputation. A single misplaced hard drive can spiral into a full-blown compliance nightmare.
The Strategic Solution: ITAD for Commercial Clients
This is exactly where a professional process called IT Asset Disposition (ITAD) comes into play. ITAD isn’t just another buzzword; it's a structured, secure framework for managing technology at the end of its life, designed for commercial and enterprise needs. It goes way beyond simple recycling to offer a complete service designed to protect your organization from top to bottom.
A solid ITAD program tackles several critical business needs all at once:
- Data Security: It guarantees that every bit of sensitive information on hard drives and other storage media is permanently wiped or destroyed, meeting strict standards like the FTC Disposal Rule.
- Compliance and Risk Mitigation: You get a clear, auditable paper trail, including certificates of destruction and recycling. This is your proof that you met every legal and environmental requirement.
- Value Recovery: It singles out any equipment that still has market value. Those assets are then remarketed through secure channels, turning what could have been a disposal cost into a revenue stream for your business.
By bringing in a professional ITAD strategy, Georgia businesses can flip a potential liability into a real strategic advantage. The whole mindset shifts from just "getting rid of old stuff" to securely managing assets, protecting data, and squeezing out the maximum financial return.
Beyond Simple Disposal
Thinking of IT equipment recycling as a core business function is the first real step toward protecting your company’s future. It shields your most valuable asset—your data—while proving you operate as a responsible corporate citizen. Neglecting this process can unravel years of hard work spent building customer trust and a solid reputation.
As you'll see, a certified partner brings the expertise and infrastructure needed to manage this process the right way, from start to finish. You can learn more about the environmental impact of electronic waste and see why professional management is so crucial.
Understanding Georgia's E-Waste and Data Compliance Landscape
Figuring out the rules for IT equipment recycling in Georgia can feel a bit like navigating a maze. Unlike some other states, Georgia doesn’t have a single, overarching state law that tells businesses exactly how to handle their old technology. But don’t let that fool you—it doesn’t mean you’re operating in a regulatory free-for-all.
Quite the opposite, actually. Businesses in Georgia are still bound by a whole host of powerful federal laws and strict industry-specific rules. If your company handles any kind of sensitive information, these regulations aren't just suggestions; they’re non-negotiable and carry some serious weight.
The Federal and Industry Mandates You Must Follow
Your responsibility to protect sensitive data doesn't just vanish when you unplug a server or retire a laptop. Several major regulations follow your IT assets all the way through their final disposal. To stay on the right side of the law, businesses need to build solid information security compliance strategies that account for the entire lifecycle of their equipment, especially its secure retirement.
Here are a few of the big ones that impact Georgia businesses:
- HIPAA (Health Insurance Portability and Accountability Act): If you're in the healthcare world, HIPAA's privacy and security rules don't just apply to active systems. They extend to every piece of retired IT gear, and failing to completely destroy patient health information (PHI) on old hard drives can lead to crippling fines.
- GLBA (Gramm-Leach-Bliley Act): This one’s for the financial sector. Banks, lenders, and investment firms must follow GLBA to protect their customers' private financial data. That means ensuring information on old computers, servers, and networking hardware is destroyed beyond any possibility of recovery.
- FTC Disposal Rule: This federal rule is pretty straightforward—it requires businesses to take proper steps to get rid of sensitive information gathered from consumer reports. This makes certified, professional data destruction an absolute must.
The price for getting this wrong is steep. We're talking about everything from devastating financial penalties and legal battles to a full-blown PR crisis that can completely erode the trust you've built with your customers.
Why a Certified Partner is Your Compliance Shield
This is exactly where a certified ITAD vendor like Beyond Surplus becomes an essential part of your team. Working with a professional adds a powerful layer of protection, effectively shifting the risk and liability off your plate and onto ours. We create a clear, auditable paper trail that proves you did everything by the book.
Partnering with a certified electronics recycler isn't just about outsourcing a task; it's about adopting a risk management strategy. It provides documented proof of compliance, safeguarding your business against potential legal and financial fallout from a data breach.
This documentation is your concrete proof of due diligence and includes things like:
- A Secure Chain of Custody: We meticulously track your assets from the second they leave your facility until they are fully processed.
- Certificates of Data Destruction: This is your official proof that all data was wiped or destroyed according to tough NIST 800-88 standards.
- Certificates of Recycling: This document verifies that all materials were handled in an environmentally responsible way.
It’s really important to understand what these certifications mean. For example, knowing what R2 certification means gives you insight into the high standards for both data security and environmental protection that certified recyclers must meet.
Georgia's Data Center Boom Amplifies the Need
The compliance challenge isn't getting any smaller—it's growing. Georgia is experiencing a massive boom in its data center sector, which brings with it an enormous need for IT equipment recycling. In fact, over the last year, our state landed the second-largest amount of data center investment in the country, right behind Northern Virginia.
This explosive growth, largely driven by AI, is forcing companies to upgrade their hardware at a blistering pace. Refresh cycles are getting shorter, which means retired servers, storage arrays, and networking gear are piling up faster than ever. This creates a huge sustainability problem, especially since Georgia lacks a unified statewide recycling policy. This surge makes professional ITAD services more critical than ever for managing asset turnover securely and responsibly.
The Blueprint of a Professional ITAD Program
So, what does a professional and secure IT recycling process actually look like for a business in Georgia? It’s far more than a simple pickup; it’s a meticulously planned operation designed to protect your organization at every single turn. A solid ITAD strategy needs a clear, well-defined blueprint for a professional program to guarantee safety, security, and compliance.
The moment your IT equipment is scheduled for removal, a strict chain of custody begins. This isn't just about loading boxes onto a truck. It’s a documented, transparent process that tracks your assets from your facility to their final destination, ensuring nothing gets lost and everything is accounted for.
Secure Logistics and Transportation
The first physical step in any reputable ITAD process is the secure transit of your assets. A professional vendor doesn’t just show up with an open-bed truck. Instead, they use GPS-tracked, locked vehicles operated by vetted, uniformed personnel who understand the importance of handling sensitive corporate assets.
This initial phase is critical for cutting down risk. The goal is to create a secure, tamper-proof bubble around your equipment from your loading dock to the processing facility. This is your first line of defense against theft or loss during transit.
Meticulous Inventory and Asset Tracking
Once your equipment arrives at the secure facility, the real inventory process begins. Every single asset is meticulously recorded. This involves scanning serial numbers, asset tags, and other identifying information to create a detailed inventory report that you can actually use.
This isn't just about counting items; it's about accountability. This step gives you a comprehensive list of every device being processed, which is crucial for your internal asset management records and for the auditable trail you need for compliance. This detailed tracking is a core component of what IT asset disposition is all about.
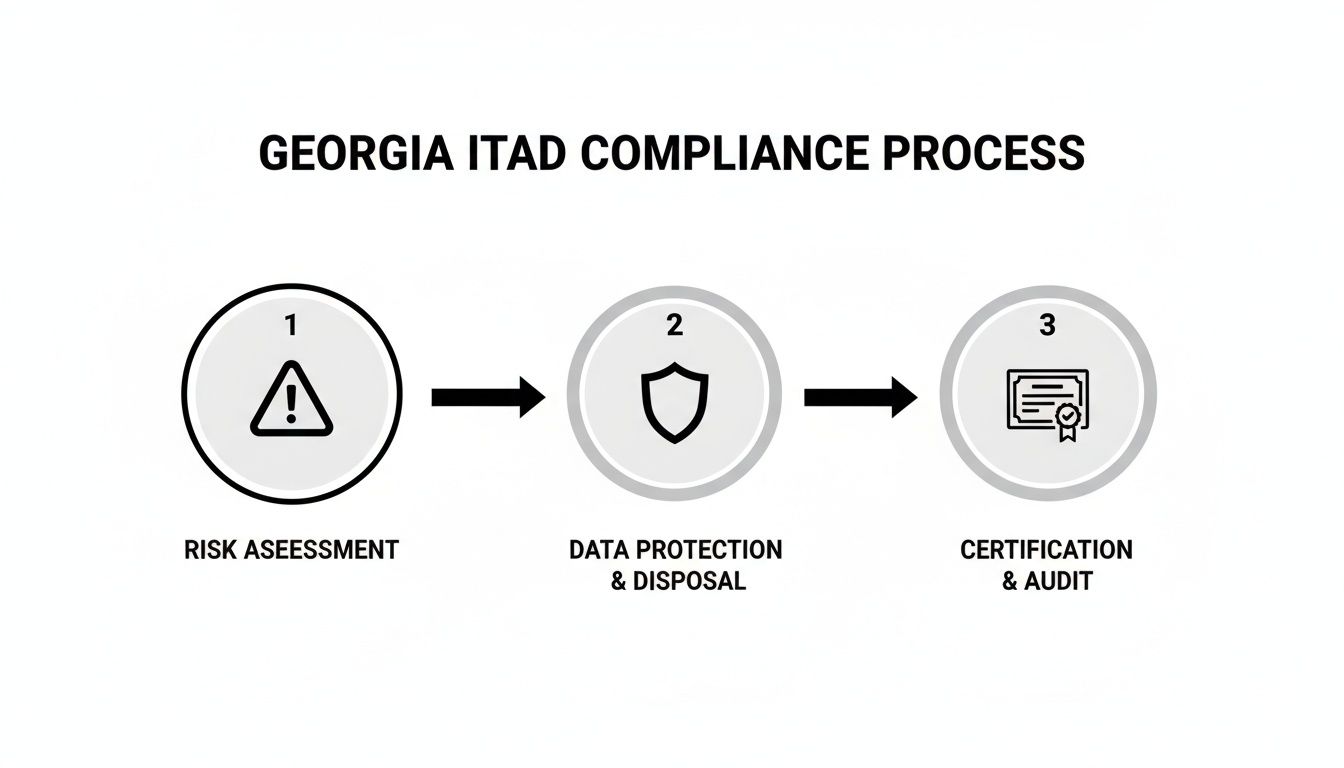
The following infographic illustrates the key stages of maintaining compliance in a Georgia ITAD program, from identifying risks to receiving final proof of secure processing.
This visual breakdown shows that a compliant ITAD strategy is a proactive journey. It starts with a smart risk assessment, moves through active protection of your data and assets, and finishes with certified documentation that proves the job was done right.
Certified Data Destruction Methods
With the inventory complete, the most critical stage begins: certified data destruction. This is the absolute heart of any secure ITAD program. A top-tier partner will offer multiple methods that meet NIST 800-88 guidelines, ensuring your data is forensically unrecoverable.
The choice of method really depends on the asset type, its potential for reuse, and your specific security requirements.
When it comes to destroying data on your old business IT assets, not all methods are created equal. You have options ranging from software-based wiping that preserves the hardware to complete physical obliteration. The table below breaks down the most common approaches to help you decide which is right for your needs.
Comparing Data Destruction Methods for Business IT Assets
| Destruction Method | Process Overview | Security Level (NIST 800-88) | Best For | Asset Reusability |
|---|---|---|---|---|
| Data Wiping/Sanitization | Software overwrites the entire drive with random data, often in multiple passes. | Clear/Purge | Assets planned for resale or redeployment; value recovery. | High (Drive is fully functional) |
| Degaussing | A powerful magnetic field is used to instantly scramble the magnetic data on drives or tapes. | Purge | Rapid, secure erasure of magnetic media like HDDs and tapes. | None (Drive is rendered inoperable) |
| Physical Shredding | The storage device is fed into an industrial shredder and ground into small fragments. | Destroy | Highest-security needs; end-of-life assets; compliance mandates. | None (Asset is physically destroyed) |
Ultimately, choosing the right method is a strategic decision. Wiping is ideal for getting value back from your old gear, while shredding offers the ultimate peace of mind for highly sensitive data. A reliable partner will walk you through the pros and cons to help you determine the best approach for each asset class.
Environmentally Responsible Recycling and Disposition
After your data has been securely destroyed, the final step is handling the physical materials in an environmentally responsible way. Not all equipment can be remarketed, and these end-of-life assets must be processed correctly.
A certified vendor, especially one with an R2v3 certification, will de-manufacture the equipment into its core commodity streams—metals, plastics, circuit boards, and glass. These materials are then sent to vetted downstream partners for responsible recycling, making sure that hazardous materials like lead and mercury are kept out of our landfills.
The final stage of an ITAD program closes the loop on corporate responsibility. It’s the documented assurance that your retired assets were handled not only securely but also in a way that protects the environment, fulfilling your company's sustainability goals.
Turning Retired IT Assets into Revenue for Your Business
Most business leaders in Georgia look at old tech equipment and see a sunk cost. It's just an operational headache that adds to the expense column. But this perspective misses a huge financial opportunity. Your old IT assets aren't just junk; many devices, even after years of service, still have significant market value that a professional ITAD partner can help you unlock.
This whole process is called IT asset value recovery, and it completely reframes your equipment recycling program from a necessary expense into a smart financial move. Instead of paying to get rid of every single item, you can generate a direct return that helps offset recycling costs or even contributes to your next technology purchase.
How the IT Buyback Process Works for Georgia Companies
At its heart, value recovery is all about the IT buyback process. It kicks off when a certified ITAD partner takes a look at your inventory of retired equipment to pinpoint assets with resale potential. Anything viable is then moved to a secure facility where it undergoes data sanitization, testing, and refurbishment before hitting the secondary markets.
An effective ITAD partnership transforms the end-of-life stage of your technology from a cost center into a value generator. By strategically remarketing viable assets, you can capture residual value that would otherwise be lost in a simple disposal process.
The entire system is built on a foundation of security and transparency. All data is completely destroyed using certified methods long before any device is ever considered for resale. You get a share of the profits, turning those depreciated assets into real, tangible revenue. Our guide to IT asset recovery services in Atlanta, GA dives deeper into how this process maximizes returns for businesses like yours.
Identifying Your Most Valuable Corporate Assets
Let's be clear: not all old equipment is created equal. The secondary market places a premium on specific types of hardware that are in high demand. An experienced partner knows exactly what to look for and how to get the best possible price for it.
Here are some of the most sought-after categories for IT buyback programs:
- Recent-Model Laptops and Desktops: Devices that are only a few generations old, especially from enterprise brands like Dell, HP, and Lenovo, are always hot commodities.
- Enterprise-Grade Servers: Servers, particularly those with modern CPUs and a good amount of RAM, are incredibly valuable for smaller businesses or data centers needing cost-effective hardware.
- Networking Equipment: High-performance switches, routers, and firewalls from brands like Cisco and Juniper often hold a surprisingly high resale value.
- Data Center Components: Don't forget the parts inside. Specific components like enterprise SSDs, high-capacity hard drives, and graphics processing units (GPUs) are also highly marketable.
Factors That Drive Resale Value
Several key factors ultimately determine what your old IT assets are worth. Understanding these variables can help you manage your tech refresh cycles more strategically to get the biggest bang for your buck when it's time to retire equipment.
The most important factors include:
- Age and Condition: It’s no surprise that newer equipment in good cosmetic and working condition will always fetch a higher price.
- Brand and Model: Gear from reputable enterprise brands typically holds its value much better than generic or consumer-grade hardware.
- Configuration: What's inside matters. The specific components, like the processor type, amount of RAM, and storage capacity, heavily influence its market value.
- Market Demand: Simple supply and demand. The current need for specific models or types of hardware on the secondary market plays a massive role in setting the final price.
By working with an ITAD partner that gets these market dynamics, you can ensure your Georgia business isn’t leaving money on the table. This strategic approach to IT equipment recycling in Georgia makes managing your end-of-life assets both secure and profitable.
How to Choose the Right Commercial IT Recycling Partner in Georgia
Picking a partner for your IT equipment recycling in Georgia is about so much more than just logistics. This isn't like hiring a standard disposal service; the vendor you select becomes a temporary guardian of your most sensitive data and a direct reflection of your company's commitment to security and environmental stewardship. Getting this choice right is absolutely critical for protecting your reputation and your bottom line.
Think about it—partnering with the wrong vendor can instantly undo all of your internal security efforts, opening up vulnerabilities you thought were long gone. That’s why a thorough vetting process isn't just a good idea; it's a non-negotiable part of your risk management strategy.
Non-Negotiable Certifications
The very first filter you should apply when looking at potential ITAD partners is their certifications. These aren't just fancy logos they stick on a website. They are hard-earned proof that a company adheres to strict, internationally recognized standards for data security, environmental safety, and operational transparency.
For any business in Georgia, two certifications should be at the top of your must-have list:
- R2v3 (Responsible Recycling): This is the gold standard for the electronics recycling industry worldwide. An R2v3 certified vendor has proven they have a rock-solid, secure process for handling used electronics, with a heavy emphasis on data sanitization and a commitment to tracking every single component downstream.
- RIOS (Recycling Industry Operating Standard): This certification focuses on the operational side—quality, environmental, and health and safety standards. When a company is both R2v3 and RIOS certified, you know you're dealing with a top-tier operation that has integrated quality and safety into every part of their business.
Choosing a certified partner is the single most effective move you can make to ensure compliance and minimize your risk.
Evaluating the Chain of Custody
A secure chain of custody is the documented, unbroken trail that tracks your assets from the moment they leave your building until they are completely destroyed or resold. Any vendor worth your time must be able to walk you through their process clearly and confidently.
Don't be shy. Ask them direct questions:
- How are my assets transported? (You're looking for answers like locked, GPS-tracked vehicles and background-checked personnel.)
- How do you manage inventory when it arrives? (They should mention detailed receiving reports and serial number scanning.)
- What paperwork will I get at each stage? (Expect serialized reports and final certificates of destruction or recycling.)
This paper trail is your proof of due diligence. It’s what you’ll use to confirm that no device was ever lost, stolen, or mishandled—something that’s absolutely vital if you're ever audited.
"A vendor’s chain-of-custody process is the backbone of their security promise. If they can't provide a clear, auditable, and unbroken trail for every asset, they are not a viable partner for any business that values its data."
Globally, the e-waste problem is almost too big to comprehend. A staggering 62 million tonnes of devices were thrown away in 2022, and that number is expected to hit 82 million by 2030, even as collection rates fall. In a tech hub like Georgia, this issue is amplified. Certified ITAD partners are on the front lines, helping manage this wave by securely reselling what’s usable, destroying data to NIST standards, and recycling responsibly. This helps businesses navigate compliance while often recovering some value. To see how Georgia is tackling this on a broader scale, you can read about Georgia’s bold experiment in e-waste recycling.
Scalability and Comprehensive Services
Your ITAD needs are going to fluctuate. One quarter it might be a small office cleanout, and the next you could be staring down a full data center decommissioning. The partner you choose has to be able to scale their services up or down to meet your exact needs without ever cutting corners on security or efficiency.
Beyond Surplus offers the full spectrum of services built for Georgia businesses, whether you have a few pallets of laptops or a complex, large-scale project that spans the country. Our deep experience across different industries means we know how to build a solution that fits your unique operational and compliance challenges. Understanding the landscape of different providers is key to making a smart decision. For more on this, check out our guide on how to evaluate IT asset disposition companies.
Got Questions About Business IT Recycling in Georgia? We've Got Answers.
Even with a solid plan, it's natural for business leaders and IT managers in Georgia to have questions about how IT equipment recycling actually works. Let's tackle some of the most common ones head-on, giving you the clear, straightforward answers you need to manage your company's old tech with confidence.
What Does IT Recycling Typically Cost for a Business?
There's no simple, one-size-fits-all price tag for professional IT equipment recycling in Georgia. The final cost really depends on the specifics of your project. Factors like the sheer volume and type of equipment, the level of data destruction you need (basic wiping versus physical shredding), and any special logistical help, like on-site packing and transport, all play a role.
But here's the good news: many businesses discover that the costs are dramatically reduced—or sometimes completely erased—by the value we can recover from your reusable assets. When you get a quote from a partner like Beyond Surplus, we'll give you a transparent breakdown of every potential cost and credit, so you see the full financial picture from the start.
How Can I Be 100% Certain My Corporate Data Is Secure?
This is easily the most important question, and the answer is simple: documentation. A trustworthy ITAD partner will provide a complete, auditable paper trail that proves your data was handled securely every step of the way.
This proof isn't just a handshake; it's a set of official documents:
- A Secure Chain of Custody: This is the detailed log that tracks your assets from the moment they leave your office until they arrive at our secure facility.
- A Certificate of Data Destruction: This is the legal document that confirms all data was destroyed according to strict NIST 800-88 standards. It officially transfers liability from your company to ours.
- A Certificate of Recycling: This document verifies that any materials that couldn't be reused were processed in an environmentally responsible way, meeting all compliance standards.
What Actually Happens to My Equipment After You Pick It Up?
Once your equipment gets to our secure facility, the first thing we do is triage. Every item is assessed.
Anything with potential resale value is thoroughly tested, its data is professionally sanitized, and then it's prepped for the secondary market. For devices that are truly at the end of their life—obsolete, broken, or non-functional—they head to the de-manufacturing line.
This process involves carefully breaking down each item into its core materials, like plastics, metals, and circuit boards. These commodities are then channeled into responsible recycling streams, making sure hazardous materials are managed properly and kept far away from Georgia's landfills.
The scale of this challenge is massive. In 2023 alone, the U.S. generated 6.9 million tons of e-waste, with old computer equipment leading the charge thanks to regular corporate tech refresh cycles. When you consider that making just one new desktop computer takes a staggering 530 pounds of fossil fuels and over a ton of water, responsible IT equipment recycling in Georgia becomes more than a security measure—it's an environmental necessity. You can discover more insights about the impact of e-waste to see why professional handling is so critical.
Can You Handle a Large-Scale Project, Like a Data Center Decommissioning?
Absolutely. This is what separates a true ITAD partner from a simple recycler. We have the ability to scale our services for any project, no matter the size. That means we can manage everything from a small office cleanout with a few dozen laptops to a massive, complex data center decommissioning involving hundreds of servers, storage arrays, and networking racks.
These large-scale projects demand specialized logistics, on-site expertise, and the capacity to handle enormous volumes of equipment securely and efficiently. These are the core capabilities you should look for in any vendor you consider for enterprise-level IT recycling in Georgia.
Ready to put a secure, compliant, and even profitable IT asset disposition program in place for your Georgia business?
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal. Schedule your pickup and get total peace of mind.