Old telecom equipment rarely leaves all at once. It piles up in network closets, under benches in MDF rooms, on pallets after a phone system upgrade, or in a storage area nobody wants to inventory. Routers get replaced, switches come out during a refresh, VoIP handsets lose support, and old PBX hardware stays in place because nobody wants to touch it without a plan.
That clutter isn't just a housekeeping issue. It can hold saved configurations, credentials, call data, labels tied to sites or departments, and enough asset value to justify a formal retirement process. It also sits inside a much larger disposal problem. In 2022, the world generated 62 million tonnes of e-waste, but only 22.3% was formally collected and recycled, and small IT and telecommunication equipment reached only a 22% recycling rate, according to the UN Global E-waste Monitor update.
The Hidden Risk in Your IT Storage Closet
A facilities lead asks for a storage room to be cleared before an office reconfiguration. Your team opens the door and finds decommissioned switches, old firewall appliances, conference phones, wireless controllers, handsets, and a PBX shelf with no current owner. The equipment looks inactive. The compliance exposure is not.
Retired telecom hardware often leaves behind more than metal and plastic. Routers can retain saved configurations. Switches may still hold management settings, IP information, and site identifiers. VoIP phones, call processing hardware, and security appliances can contain logs, user details, credentials, or other operational data depending on how they were deployed.
For regulated organizations, that changes the disposal decision immediately. Healthcare, financial services, government, and education teams need defensible records that show what equipment was removed, how data was sanitized, who handled the assets, and when custody changed. If your team is reviewing broader exposure at the same time, it helps to explore security risk frameworks so telecom retirement is treated as part of your control environment, not a last-minute cleanup task.
I tell IT managers to treat the storage closet like an extension of the production network until every asset is identified and cleared. That approach slows down the rush to haul equipment out, but it prevents the mistakes that create audit findings, data exposure, and disputes over downstream handling.
The primary deliverable in telecom disposition is not extra floor space. It is documented risk reduction.
That is why the first question is not who will pick the gear up. The first question is what compliance and data risk each item carries. A practical telecom equipment disposal process starts there, then moves to sanitization, chain of custody, and only after that to resale or recycling.
Building Your Decommissioning Inventory
A telecom disposition project usually goes off track before a pallet is wrapped. It happens at inventory. If the list is incomplete, your team cannot prove what was removed, what needed sanitization, or whether every asset followed the right disposition path.
For regulated organizations, that gap is a compliance problem first and an operational problem second.

Classify assets by control requirements
Start by sorting equipment according to how it must be handled, not how old it is or what someone labeled on the shelf five years ago. That keeps security, legal, and facilities teams aligned from the start.
Use three practical categories:
- Assets that may retain data such as routers, switches, firewalls, PBX systems, call managers, session border controllers, and some VoIP phones
- Assets with no known data storage but controlled downstream handling needs such as handsets, power components, cabling accessories, faceplates, and mounting hardware
- Assets with unknown status because no one can confirm whether they contain storage, removable media, retained configurations, or regulated information
Unknown gear deserves special attention. I advise clients to quarantine it in the inventory, assign an owner to verify the device type, and block pickup until that review is complete. Guessing here creates the exact audit trail problems that are hardest to fix later.
Capture the details your auditor and ITAD partner will need
A weak inventory forces everyone to reconstruct facts after the equipment has left the building. That is expensive, slow, and avoidable.
For each asset, record:
- Unique identifiers such as serial number, asset tag, make, model, and hostname if available
- Current and prior location including site, room, rack, closet, and business unit
- Configuration or storage status including onboard flash, hard drive, removable media, battery-backed memory, or unknown
- Physical condition such as complete, damaged, missing modules, failed, or untested
- Operational status including powered on, powered off, boot failure, or partially functional
- Ownership and disposition notes showing whether the item is approved for reuse, resale review, parts harvest, recycling, or destruction
Photos help. Module-level detail helps more. In telecom environments, line cards, supervisor modules, SSDs, and removable flash media often get separated from the chassis. If the inventory only says "switch removed," your record is not strong enough.
Reconcile records against a physical walk-through
Procurement records and old CMDB exports are a starting point. They are not proof of what is sitting in a branch closet or still mounted in a rack.
Run a physical verification by site. Check shelves, staging rooms, desk drawers, wall-mounted cabinets, and any area where failed telecom gear tends to accumulate. Then reconcile what your team found against asset records and open service tickets. That step usually surfaces the mismatches that matter most, including retired devices that were never removed from tracking and live assets that were never entered correctly.
Separate value review from control decisions
Some equipment has remarketing value. That does not change the order of operations. First determine whether the asset requires sanitization, destruction, or special handling. Then decide whether resale is appropriate.
That sequence protects the business. It also produces cleaner resale lots because the assets have been identified properly, matched to their accessories, and documented with usable condition notes. If your team wants a practical reference for what secondary-market buyers review, this guide on where to sell used network switches and routers shows the information that usually affects recoverable value.
A simple triage table keeps the project disciplined:
| Asset type | Main question | Likely next step |
|---|---|---|
| Router or switch | Does it retain configs, credentials, or removable media? | Hold for sanitization review, then test for resale if approved |
| PBX or call control gear | Does it store call records, user data, or system backups? | Verify storage components and assign destruction or sanitization path |
| VoIP handsets | Is there meaningful resale value at the model and quantity level? | Batch by model, test selectively, recycle low-value units |
| Optics and modules | Are they current, genuine, and matched to known platforms? | Sort, test, and separate reusable units from scrap |
| Damaged legacy gear | Is repair justified after handling and processing costs? | Recycle through a certified downstream process |
Practical rule: If your team cannot confirm whether a telecom device stores data, inventory it as data-bearing until technical review proves otherwise.
A defensible inventory does more than count equipment. It gives your security team a review queue, gives your ITAD partner clear handling instructions, and gives compliance staff records they can stand behind. That is what keeps a telecom cleanup from turning into a reporting problem months later.
Executing Secure Data Destruction for Telecom Hardware
A telecom closet can look harmless right up to the point legal, security, or audit asks what was on each device and how it was cleared. Routers, firewalls, PBX platforms, call managers, and even some handsets can retain startup configurations, certificates, admin credentials, extension data, logs, and call routing information. In regulated environments, that turns retirement into a records and risk project, not just an asset removal task.
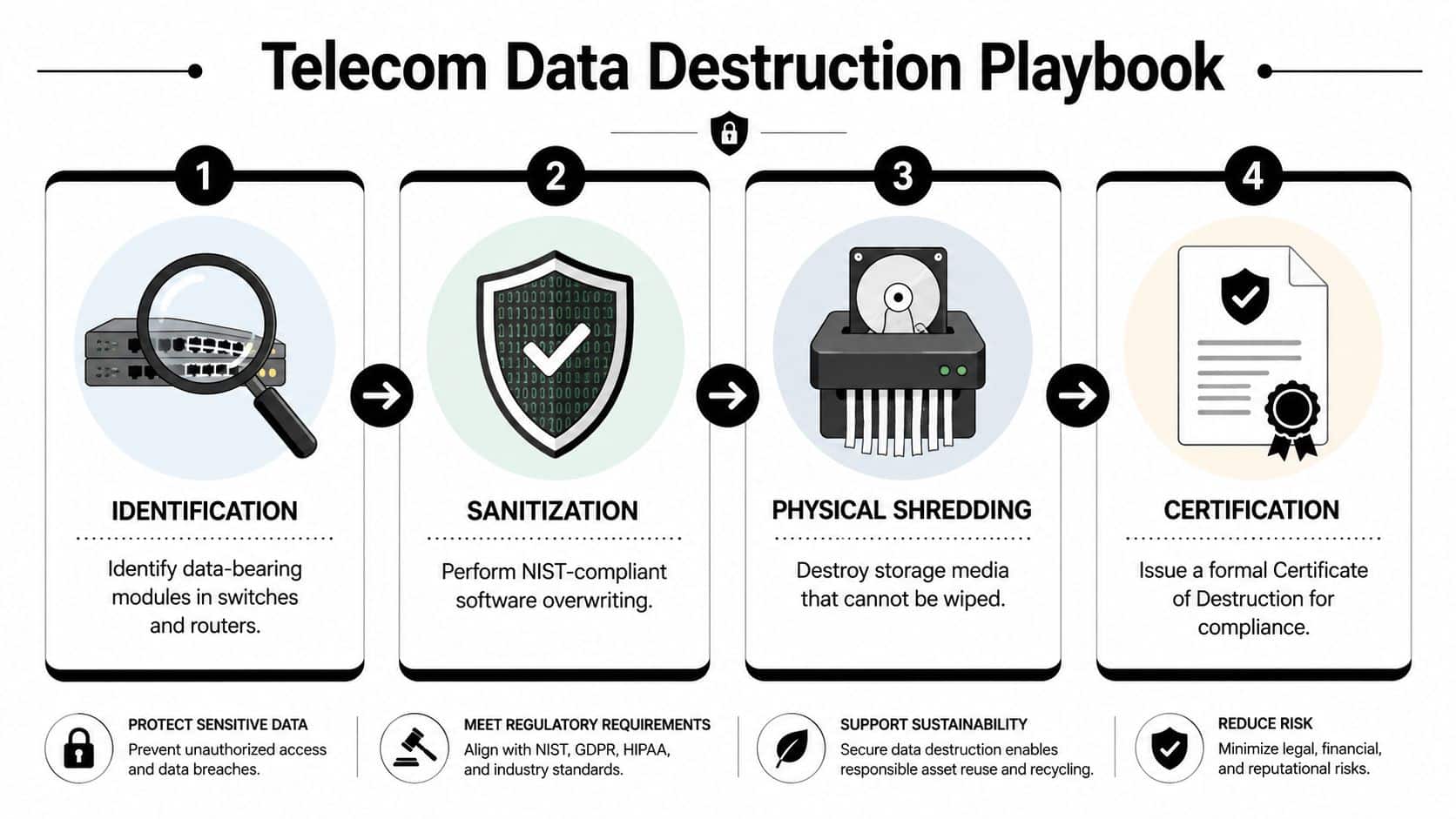
Know what method fits the hardware
Use the sanitization method that matches the actual media inside the device.
Software wiping fits equipment with accessible, supported storage that can be overwritten and verified. This path preserves resale options, but only if the process is documented and the wipe result is tied back to the asset record.
Degaussing applies to magnetic media. It works well when drives are present and your policy calls for rendering them unreadable before any downstream handling.
Physical shredding is the right choice when media is failed, inaccessible, unsupported, encrypted with unknown key status, or subject to stricter internal policy. Many healthcare, finance, government, and critical infrastructure teams default to destruction for higher-risk telecom assets because it is easier to defend in an audit.
The trade-off is simple. Wiping can preserve value. Shredding usually ends value recovery, but it closes the data question faster and with less ambiguity.
Telecom devices need device-specific handling
A branch router, a call manager appliance, and a pallet of VoIP handsets should not go through the same workflow. Device design matters. So does the type of data the equipment may have touched.
Use this decision pattern:
- Enterprise routers and firewalls usually need config review, media identification, sanitization, verification, and only then release for remarketing consideration.
- Switches often have lower data risk than security appliances, but they still need confirmation of stored configs, local credentials, and removable media before reuse.
- PBX systems, voicemail platforms, and voice servers deserve tighter controls because they may contain user associations, call detail records, routing data, and backups.
- VoIP handsets are best handled in batches by model and generation. Some can be reset, verified, and reused. Others are more practical to recycle.
- Failed or inaccessible devices should move to physical destruction of the affected media without delay.
I tell clients to assume telecom gear is data-bearing until a technician proves otherwise. That standard prevents the common mistake of treating voice and network hardware like low-risk scrap.
Sanitization has to be auditable. If you cannot show which method was used on a specific serial number, you do not have a defensible compliance record.
What works and what fails
What works is controlled execution with clear approval points. Identify the asset. Confirm the media type. Apply the approved sanitization method. Verify the outcome. Record the result. Then release the equipment for resale or recycling.
What fails is mixing collection, triage, and destruction into one loosely managed pickup. Once serial numbers, media status, and destruction evidence stop matching, the project becomes hard to defend to auditors, privacy counsel, or internal security.
For organizations that need a provider focused on this stage, secure telecom equipment disposal services should support data-bearing network and voice gear, asset-level tracking, and documented sanitization outcomes instead of basic electronics hauling.
Ask for proof, not promises
Before handing over telecom equipment, ask the ITAD or recycler questions that expose process maturity:
- Which telecom asset types do you classify as data-bearing by default?
- Which sanitization methods do you perform, and on what media?
- How do you connect the sanitization result to the serial number, pickup record, and final disposition?
- Do you issue destruction records at the asset level, the batch level, or both?
- What is your process when a device fails wipe verification or has inaccessible storage?
- Which certifications and downstream controls support your handling of telecom hardware?
A certified partner should answer those questions clearly and in writing. If the answers are vague, the compliance risk stays with your organization.
Choosing Your Disposition Pathway Value Recovery vs Recycling
Once the data risk is closed, the question becomes financial and operational. Do you remarket the gear, recycle it, donate it, or scrap it for parts?
The right answer depends on model age, condition, support status, demand in secondary markets, and how much labor you're willing to invest in testing and sorting. Not every asset deserves the same effort.
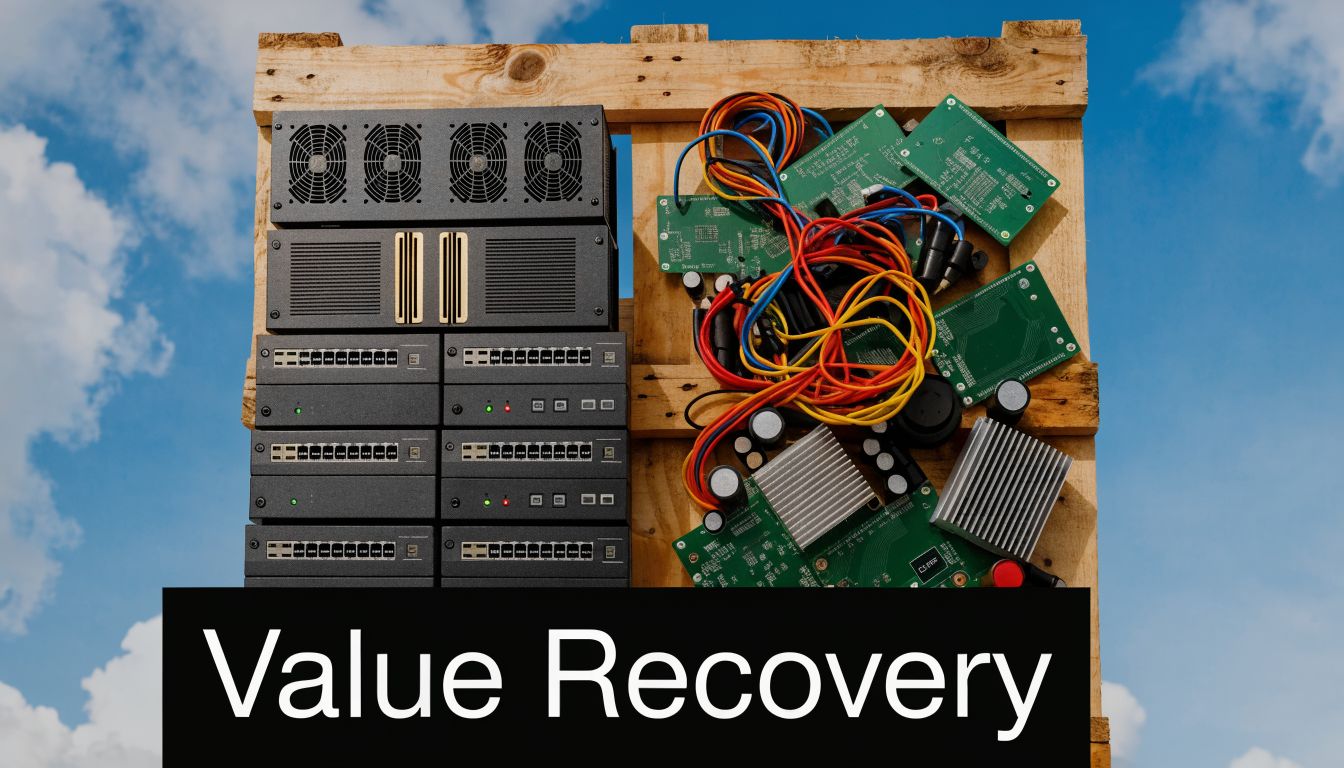
Resale works when the equipment is still marketable
For many enterprises, the strongest return comes from routers, switches, optics, and telecom hardware that still has a usable service life. In a formal retirement process, 40-60% of enterprise routers and switches can be refurbished for secondary markets, potentially yielding a 10-25% ROI, and skipping that assessment can mean giving up $500 to $5,000 per rack, according to this benchmark on recycling used telecom and IT assets the right way.
That doesn't mean every closet full of gear is valuable. It means testing and grading matter.
Assets usually move into the resale lane when they have:
- Clear provenance with known removal date and ownership
- Stable demand in secondary markets
- Clean cosmetic condition and complete components
- Successful sanitization records attached to the asset file
If your team is evaluating remarketing options, this overview of selling surplus telecom hardware shows the types of equipment that tend to fit buyback programs.
Recycling is the right choice for obsolete or low-demand gear
Certified recycling becomes the right answer when the hardware is too old, damaged, incomplete, or low-demand to justify remarketing labor. That includes mixed pallets of handsets, unsupported network appliances, broken chassis, and deinstalled gear with poor resale prospects.
Recycling still requires discipline. You want the equipment dismantled through documented downstream channels, not dumped into general scrap. Telecom gear contains recoverable metals and regulated materials, and the disposal record matters as much as the material recovery.
A simple comparison helps:
| Pathway | Best fit | Upside | Trade-off |
|---|---|---|---|
| Resale | Current, testable enterprise gear | Recover value | More sorting and verification |
| Recycling | Obsolete, damaged, mixed legacy hardware | Clean compliance outcome | Lower direct return |
| Donation | Select functional gear with a clear recipient | Social benefit | Still requires sanitization and documentation |
Donation sounds simple, but often isn't
Donation can work for certain accessories or still-usable business hardware, but it's not a shortcut around compliance. The sanitization requirement remains. So does documentation. If the receiving organization can't use unsupported or incomplete telecom gear, donation just pushes your disposal problem downstream.
Donation only works when the recipient can actually deploy the equipment and your team can document sanitization first.
Don't let value recovery outrun compliance
Organizations frequently face challenges during this process. They identify a resale opportunity, then rush equipment out before the data review is complete. That flips the order of operations. Value recovery should follow verified sanitization, not compete with it.
In practice, the strongest programs use a sequence like this:
- Identify and segregate data-bearing assets
- Sanitize or destroy media according to policy
- Test and grade units eligible for resale
- Recycle the balance through certified downstream processing
That sequence protects both the balance sheet and the audit trail.
Managing Logistics and Chain of Custody
Even a sound disposition plan can fail in the loading dock.
The risk isn't only what happens inside the recycler's facility. It's what happens between your rack room and that facility. Assets get moved by facilities teams, third-party movers, parcel carriers, temporary labor, and freight handlers. If custody isn't documented from pickup through processing, your compliance story has a gap.

Ad hoc transport creates avoidable exposure
A common failure looks harmless. A team finishes a refresh, stacks old telecom gear near receiving, and books a standard freight pickup. The driver signs for pallets, but the paperwork only says "electronics." No serialized manifest. No seal numbers. No item-level confirmation. No proof of what was loaded.
That's not chain of custody. That's shipment by assumption.
Businesses need stronger logistics now because upgrade cycles are producing more dispersed hardware. With 5G-to-6G transitions accelerating network upgrades, businesses need scalable logistics, and the rise in telecom hardware waste calls for partners with nationwide pickup capabilities for multiple sites and data centers, as noted in this article on disposing of outdated telecom equipment.
What secure pickup should look like
A professional process should include:
- Pre-pickup reconciliation between your asset list and the expected shipment
- Site packaging controls such as palletizing, shrink-wrap, sealed gaylords, or crated high-value gear
- Pickup documentation that records counts, asset classes, and custody transfer
- Arrival verification at the processing site with exceptions logged immediately
For bulky projects, planning freight footprint matters too. Operations teams often review pallet counts, loading constraints, and trailer space before removal. If you're mapping larger shipments, this guide to 40 foot shipping container dimensions is a practical reference for space planning and staging conversations.
Prepare the load like it may be audited later
That mindset changes how teams pack equipment.
Don't mix clean reusable switches with damaged scrap if you want accurate valuation. Don't bury potentially data-bearing appliances under low-value handsets. Label pallets by category. Keep site identifiers on the paperwork, not taped loosely to the hardware.
A short prep list helps:
- Separate by disposition path so resale candidates don't get mixed with scrap
- Stabilize the load with wrap, banding, and proper pallet condition
- Attach manifests carefully so pickup staff and receiving teams are working from the same list
- Escalate exceptions early if counts differ, devices are missing, or unexpected storage media appears
If your logistics record only proves that some pallets left the building, it doesn't prove that the right assets reached the right processor.
For multi-site organizations, logistics capability becomes part of the security standard. The provider needs to manage branch pickups, office closures, rack removals, and consolidation without breaking documentation at each handoff.
Finalizing Compliance with Certificates and Reporting
A telecom retirement project closes when your records can stand up to an audit.
That standard matters more than many teams expect. Six months after pickup, legal, internal audit, procurement, or a customer security reviewer may ask for proof of what left the site, how data-bearing gear was handled, and who accepted custody. If your team has to piece that story together from emails and dock paperwork, the process was not controlled well enough.
Treat the closeout file as part of the disposal work
For regulated organizations, the final record set carries as much weight as the physical removal. It should tie back to the decommissioning inventory, show the processing outcome, and document the point where custody transferred to the downstream processor. Without that chain, it is harder to prove due diligence if a device is later questioned.
At minimum, the documentation should answer four basic compliance questions:
- Which assets were processed
- What happened to each asset or batch
- How data was destroyed or sanitized
- When custody and liability transferred
Review the package before anyone archives it
I tell IT managers to read the closeout packet the same way an auditor would. Check it while the project is still fresh and exceptions can still be resolved. Once equipment has been consolidated, shredded, or moved through downstream recycling, missing details get harder to correct.
A useful packet usually includes serialized or batch-level inventory references, pickup records, processing dates, destruction details for data-bearing items, and recycling documentation where applicable.
Review these points closely:
- Asset identifiers that match your internal inventory or approved variance list
- Processing descriptions that reflect the actual disposition path
- Sanitization or destruction details for drives, storage modules, and other data-bearing components
- Custody dates and transaction references tied to pickup and final processing
- Documented exceptions for missing, damaged, unverified, or substituted units
- Authorized signatures or issuer details from the processor
A generic receipt is not enough. It may show that equipment was collected, but it does not prove compliant destruction, verified recycling, or a defensible transfer of responsibility.
Store records where compliance teams will actually retrieve them
Good documentation loses value when it lives in one person's inbox or in an unlabeled shared drive folder. File the closeout package with your asset disposal records, retention schedule, and site-level decommissioning documents so audit, legal, and security teams can retrieve it without chasing the operations staff who handled the project.
If your team needs a benchmark for the final document, review what a Certificate of Destruction for IT asset disposition is expected to show and compare that standard against your provider's paperwork.
The hardware may be gone. The compliance burden is not gone until the records are complete, accurate, and easy to produce.
Partner with Experts for Your Telecom Disposition
What to do with old telecom equipment comes down to sequence and control. Identify the assets correctly. Separate data-bearing gear from simple peripherals. Apply the right sanitization method. Move the equipment through documented logistics. Close the project with certificates your compliance team can use.
That sounds straightforward until you're dealing with mixed hardware across several offices, uncertain asset records, unsupported phone systems, and pressure to clear space quickly. That's why many IT managers treat telecom disposition as a specialized ITAD project rather than a routine recycling pickup.
A qualified partner should be able to handle serialized inventory, secure data destruction, nationwide pickups, value recovery review, and final reporting without forcing your team to stitch together multiple vendors. Beyond Surplus is one example of a provider that offers telecom equipment pickup, data destruction, buyback evaluation, and documentation for business customers.
Choose the partner the same way you'd choose any security-sensitive vendor. Ask how they classify data-bearing telecom gear, how they document custody, how they handle exceptions, and what certificates they provide at closeout. The right answers are specific. The wrong ones are vague.
If your organization needs a compliant path for old routers, switches, PBX systems, VoIP phones, or mixed telecom hardware, contact Beyond Surplus for certified electronics recycling and secure IT asset disposal.