title: "Certificate Of Destruction Hard Drive in Birmingham, AL | Beyond Surplus"
description: "Looking for a certificate of destruction hard drive in Birmingham, AL? Beyond Surplus provides certified electronics recycling, secure e-waste management, and IT asset recovery services. Contact us today."
A Certificate Of Destruction for a hard drive in Birmingham, AL is your proof that retired storage hardware has been rendered irretrievable. At Beyond Surplus, our Birmingham electronics recycling services and secure e-waste management in Birmingham, AL ensure each drive’s serial number is mapped to a specific destruction method—shredding, crushing, or degaussing—along with an exact date and time. That record shields your organization from audit scrutiny and hefty compliance fines.
Quick Overview Of Certificate Of Destruction Hard Drive

Below is a concise snapshot of what a Certificate Of Destruction Hard Drive delivers:
| Aspect | Detail |
|---|---|
| Purpose | Document proof of destruction |
| Tracking | Links serial number to method |
| Timing | Records date and time |
| Liability Transfer | Shifts risk from your company |
Think of this certificate like a death certificate for data-bearing devices. It legally confirms that every drive has been purged from your environment for good. By logging serial numbers, destruction techniques, and timestamps, you create an unbroken chain of custody that stands up to any auditor’s test.
Key Benefits And Features
- Audit Defense: Provides formal proof for regulators and auditors
- Liability Transfer: Clearly assigns disposal responsibility
- Risk Reduction: Prevents any chance of forensic data recovery
- Compliance Support: Aligns with FTC Disposal Rule, HIPAA, PCI DSS, and state regulations
- Audit Trail Visibility: Consolidates records for quick retrieval
- Operational Efficiency: Streamlines disposal workflows
Every certificate entry must be signed off by trained staff, which seals the chain of custody. Issuing this document not only eases audit stress but also shows stakeholders you’ve carried out irreversible data elimination with due diligence.
For all the details on what your certificate needs to include, check out our full guide on Certificate of Destruction procedures at Beyond Surplus. This overview equips you with the essentials before we dive into legal requirements, data-wiping versus physical destruction, and best practices for retention and audits.
Understanding Key Concepts
Imagine each retired hard drive as a sealed vault deposit box. From the moment it leaves your shelf, you need a foolproof chain of custody.
A certificate of destruction for hard drives does exactly that. It captures every detail you need to prove data is gone forever.
- Asset Identifier: Serial number and model for each drive
- Destruction Method: Detailed steps for shredding, degaussing, or crushing
- Timestamp: Exact date and time logged for every action
- Staff Oversight: Operator signature plus witness confirmation
Core Details Recorded
First, you note the serial and model numbers. These asset identifiers act like unique fingerprints, ensuring no two drives ever get mixed up.
Next, you map out the destruction method step by step. Whether you’re running a high-powered degausser or cranking through an industrial shredder, every parameter goes on record.
“Every sealed box is tracked and its destruction logged to shield businesses from audit surprises.”
Consider this real-world jolt: in 2024, Statista reported 3,158 data breach cases in the U.S. alone, impacting 1.35 billion people globally. That marks a huge leap from 1,108 cases and 310 million affected in 2020. Proper disposal—and a rock-solid certificate—aren’t optional anymore. Read the full research about data breach trends on Reworx Recycling
Building A Verifiable Trail
Every action gets a timestamp, crafting a chronological audit trail. Auditors see exactly when each drive left your facility—and never returned.
You also log container seals and handoff details, meeting chain-of-custody standards. This level of precision aligns with NIST SP 800-88 for secure decommissioning. Check out our guide on media sanitization best practices in our article on NIST SP 800-88
Implementing Secure Processes
Think of your destruction zone like a bank vault. Each sealed container gets a unique barcode, and staff scan it at every stage.
When the shredding or degaussing run finishes, the mobile unit uploads the complete log automatically. No gaps, no guesswork.
Best Practices For Audit-Ready Disposal
- Use tamper-evident seals on transport boxes
- Require dual signatures for every handoff
- Store digital logs in encrypted archives
These steps mirror financial-vault drills—testing every door and lock. With each scan, seal, and signature airtight, your certificate will hold up under any compliance audit.
Next Steps For Preparation
Start by auditing your drive inventory. Tag each unit with a unique identifier and record it in your asset registry.
Then schedule a certified destruction session with your ITAD provider.
- Create an asset registry listing all drives
- Train your team on scanning and documentation procedures
With these measures in place, you’ll have flawless, audit-ready documentation—fast.
Regulatory Compliance Requirements
Disposing of old hard drives can feel like wandering through a maze of regulations. A Certificate of Destruction for a hard drive is your compass—proof you’ve met every twist and turn.
Federal statutes demand solid evidence that data is gone for good, plus an unbroken chain of custody. Miss the mark and fines can soar to $2.4 billion.
- FTC Disposal Rule requires certified proof of media disposal
- HIPAA mandates specific destruction certificates for health data devices
- PCI DSS demands logs of data shred or wipe operations
Key Federal Rules
Think of the FTC Disposal Rule as a rulebook for financial outfits and consumer reporting agencies. It ties each device’s serial number to the moment it’s crushed, shredded, or wiped clean.
HIPAA’s safeguards zero in on electronic protected health information. If you’re dealing with patient data, a destruction certificate must log every shred or pulverization—whether it happens on-site or off.
For payment card data, PCI DSS raises the bar on accountability. Your certificate isn’t just a form; it needs the details of how the drive was destroyed and who signed off on it.
- Certify media destruction within 30 days of decommissioning
- Retain certificates for seven years for audit readiness
- Include chain-of-custody logs with timestamps and seals
International Data Mandates
GDPR rewrote the playbook in Europe. Missed or unverifiable hard drive destruction can trigger fines up to €20 million.
A hard drive destruction certificate here isn’t busywork—it’s the gold standard for demonstrating you followed the rules in a tough regulatory field. The UK, Germany, and France lead the pack for certified shredding services.
“In Europe, companies face steep GDPR penalties without documented data annihilation.”
Learn more about data destruction trends on 360iResearch.
Meanwhile, North American standards like HIPAA and CCPA demand granular certificates. The result? A booming market for U.S. certified destruction services.
- Verify EU media destruction compliance methods
- Support GDPR audits with timestamped reports
State Law Requirements
State regulations pile on extra checks. In California, CCPA forces companies to produce certificates for anything storing consumer info.
Fines under CCPA can top $7,500 per violation. New York and Massachusetts aren’t far behind with their own reporting mandates.
- Notify state regulators within 60 days of device destruction
- Retain sealed chain-of-custody logs for audit reviews
- Submit annual destruction reports if over 1,000 devices are destroyed
Audits And Penalties
Skip the certificate and you’re inviting a high-stakes audit. Banks and healthcare providers have settled for millions when hard drives went missing—or worse, still held data.
One bank was hit with a $35 million penalty after an audit found shoddy disposal practices. A missing chain-of-custody log can cost more than money; it can cost your reputation.
- Conduct pre-audit certificate reviews
- Simulate chain-of-custody checks quarterly
- Store backup records both digitally and physically
Common Regulatory Demands
Across the board, regulators want proof of irreversible data elimination. They expect detailed logs tracking every handoff.
Certificates usually must show:
- Serial Numbers and Asset Details
- Date & Time Stamp of Destruction
- Method Description with Technical Specs
- Personnel Signatures and Witness Records
- Chain-of-Custody Reference Codes
These components form the backbone of a compliance-ready certificate. By aligning with FTC, HIPAA, PCI DSS, GDPR and state laws, you shield your organization.
Documenting every detail in a certificate of destruction hard drive proves you took the right steps.
Next we explore the required elements of a valid certificate including templates and signatures.
Consequences Of NonCompliance
Ignore certificate requirements and you could trigger state or federal investigations. Companies have faced injunctions, public notices, and costly remediation orders.
The blow to your brand from a public audit warning often outstrips any financial penalty.
- Loss of customer trust and contracts
- Increased insurance premiums
- Mandatory compliance oversight
Audit readiness starts with a certificate.
Stay compliant.
Elements Of A Valid Certificate
Think of a hard drive destruction certificate as the flight recorder for your data disposal process. It captures every twist and turn—from the moment a drive leaves your storage rack to the instant it meets the shredder or degausser.
When auditors or regulators come knocking, they want proof of an unbroken chain of custody. This certificate is that proof, built on a foundation of detailed, time-stamped actions.
To stay audit-ready, every certificate needs these pieces:
Required Elements Of A Hard Drive Destruction Certificate
| Element | Purpose |
|---|---|
| Asset Identifier | Links each drive’s serial and model numbers to a unique record |
| Date and Time Stamp | Documents the exact moment of destruction for audit precision |
| Method Details | Specifies shredding specs or degaussing strength achieved |
| Personnel Signature | Confirms an authorized operator conducted the destruction |
| Witness Attestation | Provides independent verification of the process |
| Provider Credentials | Validates disposal provider’s licensure and insurance coverage |
Together, these items transform a simple form into an ironclad record that stands up under scrutiny.
How Each Element Builds Trust
A clear date and time stamp locks in precisely when destruction occurred. That timestamp fits neatly into your compliance window, leaving no room for “what if?” questions.
Digging into the method details is equally important. Whether you’re shredding at 6,000 RPM or degaussing at 2.8 Tesla, pinpointing exact specs quashes any doubt about incomplete destruction.
- Personnel Signature verifies a trained technician handled the job
- Witness Attestation brings an extra, impartial set of eyes
- Provider Credentials prove your vendor carries the right licenses and insurance
Standardized certificates speed up audit reviews. And when you pair that with digital archiving, you can pull up a certificate by serial number in seconds—no more rifling through file cabinets.
“An organized certificate is your best defense against audit delays.”
For a ready-made template, see our guide on certificate formatting in the Destruction Certificate Format article.
Digital archives can cut retrieval time by 50% compared to paper systems. With all these elements in place, your certificate of hard drive destruction becomes bulletproof.
Summary Of Core Elements
- Asset Identifier to track each drive
- Date and Time Stamp for audit accuracy
- Method Details with technical specs
- Personnel and Witness Signatures for verification
- Provider Credentials for compliance proof
Document every item in a consistent form and store it in a searchable digital archive. Beyond Surplus issues audit-ready certificates that tick all these boxes—reach out for certified electronics recycling and secure IT asset disposal.
Remember to keep your digital certificates for at least five years, as most audit retention guidelines require. And regularly test retrieval by searching for a serial number or date. That quick drill reveals gaps long before an auditor does.
Comparing Wiping And Physical Destruction
Deciding how to retire your hard drives boils down to three main considerations: risk, cost, and compliance. On one hand, wiping software can safely clear data for a second life. On the other, physical destruction guarantees that information never sees the light of day again. Let’s walk through both options and see how they stack up—so you can choose the right path and back it up with a solid certificate of destruction.
Security And Reversibility
When you overwrite a drive, software performs multiple passes to replace old bits with new patterns. It’s like repainting an old fence—you can still see the shape of the boards, but the original color is gone. However, if the process is cut short or misconfigured, a skilled forensic team might still piece together fragments.
Physical destruction, by contrast, is the equivalent of turning that fence into mulch. Shredders, crushers, and degaussers render drives into pieces. There’s simply no second chance at reconstruction.
- Wiping is ideal if you plan to reuse the drives
- Destruction makes data recovery impossible
- Wipe time varies based on drive size and pass count
- Shredder throughput dictates how fast you can destroy
Still, certain regulations—like GDPR—often lean on destruction as the only bulletproof method. If you need a bulletproof certificate of destruction hard drive, shredding wins every time.
Comparison Of Wiping Vs Physical Destruction Methods
Before digging into audit paperwork, let’s visualize the trade-offs:
| Method | Security Level | Reversibility | Audit Trail | Cost |
|---|---|---|---|---|
| Data Wiping | Medium to High | Partial | Moderate | Moderate |
| Physical Destruction | Highest | None | Superior | High |
In this table, you’ll notice that physical destruction offers the top security rating and the clearest audit trail. Wiping can save money, but you’ll need robust logging to satisfy auditors.
Audit Trail Quality And Compliance
Whether you choose overwrites or crushers, a credible audit trail is non-negotiable. With destruction, you tie each drive’s serial number to a timestamp, an operator signature, and often a witness attestation. Wiping logs usually capture the software version, date, and number of passes—but nothing more.
“A certificate of destruction backed by physical methods leaves zero room for doubt.”
For regulations such as HIPAA, PCI DSS, and the FTC Disposal Rule, most auditors insist on destruction certificates. However, some authorities will accept drives wiped to NIST SP 800-88 standards.
Key elements for a compliant certificate:
- Serial Numbers and model identifiers
- Date, Time, and operator initials
- Method Description (software version or shredder model)
- Witness Sign-Offs to close the chain of custody
- Digital Logs for quick audit retrieval
If you’re curious about secure wiping best practices, check our Secure Hard Drive Erasure Guide from Beyond Surplus.
Real World Use Cases
Imagine a data center replacing aging hardware. By wiping and redeploying drives, they shaved 20% off procurement costs. Yet when those same drives reached their end of life, policy mandated shredding.
In another scenario, a healthcare provider retired 100 drives last year. At $15 per drive for shredding, they eliminated any audit risk and satisfied patient-privacy laws. The signed certificate of destruction hard drive—complete with batch details—became their proof of compliance.
Deciding which route to take often hinges on:
- Asset End Use
- Regulatory Requirements
- Environmental Objectives
- Budget Limits
Many organizations blend both methods: wipe for reuse, then destroy at final decommission. This hybrid strategy maximizes value and keeps you covered from both an ROI and an audit standpoint.
As we move on, we’ll dive into the exact language you need for a certificate, plus chain-of-custody steps to ensure your documentation stands up to any audit. Whether you opt for overwrites or crushers, clear records—serial numbers, timestamps, operator credentials—are your best defense.
Sample Certificate Language And Chain Of Custody Steps
Drafting a clear certificate of destruction feels a lot like setting a ship’s manifest before it sails. You want every item listed, every handoff logged, and no loose ends. This template lays out the core fields—asset IDs, destruction methods, and official attestations—so you can slot it straight into your compliance playbook.
Certificate Template Example
Start with a descriptive title that names the client and includes the destruction date. Right below, add the client’s contact details, physical location, and a unique project reference. Then, in a simple table or list, break out each drive’s serial number, model number, and quantity.
- Certificate Title: Certificate Of Destruction Hard Drive
- Client Details: Organization name, address, point of contact
- Asset Details: Serial numbers, model identifiers, quantity
- Destruction Statement: Method used, technical specifics, date, and time
- Attestation: Operator signature, witness signature, and certification date
“Linking every serial number to a specific destruction method ensures unbroken audit trails,” explains a compliance auditor.
Once you’ve covered the essentials—asset tracking, method description, and provider credentials—you can slip in extra sections for environmental notes or special instructions. Each bullet point can expand into full paragraphs of policy language, tailored to your internal standards.
Chain Of Custody Steps
Imagine a relay race: each runner hands off the baton, and every handoff is timed, witnessed, and recorded. Follow these stages to keep your custody record airtight. Attach logs with timestamps and signatures at each station.
- Collection From Facility
- Secure Transport With Tamper Evidence
- Logged Handoff Between Handlers
- On-Site Or Centralized Destruction
- Issuance Of Final Certificate
By using tamper-evident seals on containers, you cut down the risk of misplaced drives. Add unique barcodes to both seals and documentation so auditors can track each unit from pickup to final certificate. This level of detail checks the boxes for FTC, HIPAA, and PCI DSS.
The following infographic visualizes the disposal methods workflow highlighting wipe, shred, and certify stages.
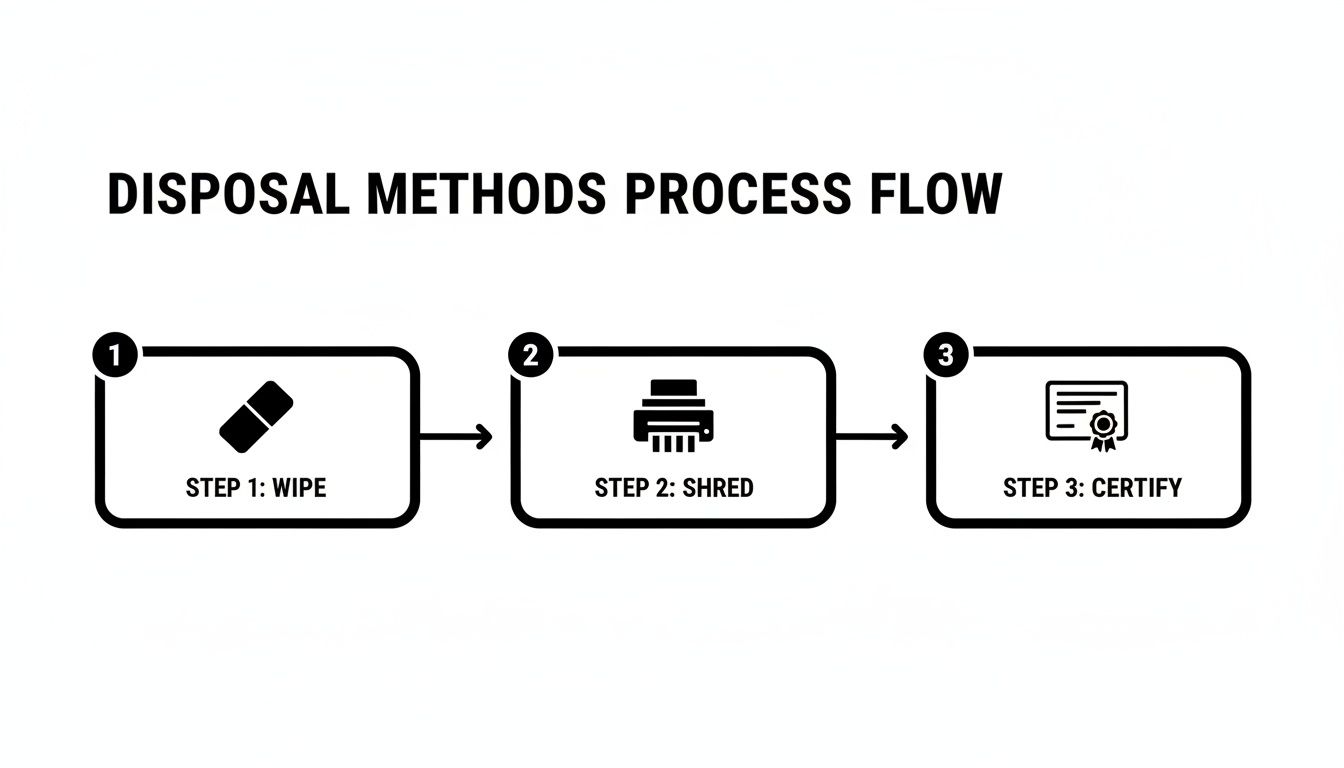
This flowchart lays out wiping, shredding, and certification as a seamless sequence. It drives home the point that certification is your final proof point—your audit defense.
Learn more about our detailed procedures in our hard drive destruction services guide at Beyond Surplus.
Additional Tips And Best Practices
Keep both digital and hard-copy versions of each certificate for at least five years. Store encrypted files in the cloud and lock physical paperwork in a secure cabinet. Run periodic spot-checks to find gaps before an auditor does.
- Use dual signatures on every destruction batch to eliminate single-point failures.
- Archive chain-of-custody logs with operator notes and container IDs for full context.
- Confirm provider credentials and insurance limits before scheduling the service.
A robust chain of custody turns a certificate of destruction hard drive into an invincible audit tool.
Following this template and workflow cements your proof of data elimination. Next, we’ll dive into retention policies and audit drills to keep you audit-ready.
Customizing Certificate Language
Make the template your own by swapping placeholders for project codes, internal order numbers, and department names. Keep the wording active and precise, so there’s no guesswork about what happened, when, and why.
- Insert ISO or NIST standard citations to show strict compliance.
These tweaks guarantee your certificate of destruction hard drive aligns with both legal and corporate reporting standards.
Roles And Responsibilities
Think of this as an instruction manual for your team. Clear role definitions ensure every person knows their part in securing assets and signing off.
- Handler: Collects, seals, and labels containers.
- Operator: Executes destruction and logs all parameters.
- Witness: Verifies procedures and co-signs the certificate.
- Auditor: Reviews logs, certificates, and closes the loop.
When each stakeholder knows their assignment, errors fade away and accountability rises.
FAQ
In this section, we tackle the most frequent questions about Hard Drive Certificates of Destruction. You’ll discover clear insights on retention periods, compliance obligations, and how Beyond Surplus delivers certified documentation.
What Is a Hard Drive Certificate of Destruction?
Think of it as a certified receipt for every storage device you retire. It logs the serial number, the destruction method, and an exact timestamp—proof that your data has been erased beyond recovery.
How Long Should I Keep These Certificates?
Regulators such as the FTC, HIPAA, and PCI DSS expect you to hold onto records for three to seven years. Treat these certificates like tax files—you never know when an auditor might ask to see them.
Can Software Wiping Cover All Regulatory Bases?
In some scenarios, wiping can satisfy specific requirements. But many auditors favor physical destruction proof. Much like scrubbing a tough stain, software erases can leave digital residue that isn’t obvious at first glance.
How Do I Obtain a Certificate from Beyond Surplus?
It’s straightforward. Contact Beyond Surplus to arrange an onsite service or schedule a nationwide pickup. Once we securely destroy your drives, you’ll receive a certificate that aligns with every compliance standard. Reach out via our contact page.
Tips for Bulletproof Certificates
To strengthen your compliance posture, implement these best practices:
- Apply tamper-evident seals on storage containers to secure drives before destruction.
- Require dual signatures—one for the technician and one for the witness.
- Archive digital records in encrypted storage for swift retrieval during audits.
“A trusted certificate of destruction for hard drives is your strongest defense against audit penalties.”
Accurate destruction certificates—and rock-solid document control—act as your audit shield, helping you satisfy inspections, avoid fines, and prove due diligence to stakeholders.
Contact Beyond Surplus for certified electronics recycling and secure IT asset disposal in Birmingham, AL: Contact us.